Understanding SNMP
SNMP (Simple Network Management Protocol) is a standard protocol used for monitoring and managing devices on IP networks.
What is SNMP?
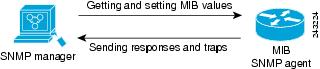
Simple Network Management Protocol (SNMP) is an application-layer protocol for communication between managers and agents. An SNMP system consists of an SNMP manager, an SNMP agent, and a Management Information Base (MIB).
The SNMP manager can be part of a network management system (NMS), such as Cisco Prime Infrastructure. The agent and MIB reside on the device. To configure SNMP on the device, you define the relationship between the manager and the agent.
The SNMP agent contains MIB variables whose values the SNMP manager can request or change. A manager can get a value from an agent or store a value into the agent. The agent gathers data from the MIB, the repository for information about device parameters and network data. The agent can also respond to a manager's requests to get or set data.
An agent can send unsolicited traps to the manager. Traps are messages alerting the SNMP manager to a condition on the network. Traps can indicate improper user authentication, restarts, link status (up or down), MAC address tracking, closing of a Transmission Control Protocol (TCP) connection, loss of connection to a neighbor, or other significant events.
SNMP Versions
SNMP versions provide different capabilities for managing network devices. This software release supports SNMPv1, SNMPv2C, and SNMPv3.
-
SNMPv1: The Simple Network Management Protocol, is a Full Internet Standard defined in RFC 1157.
-
SNMPv2C: SNMPv2C updates SNMPv2Classic by replacing its Party-based Administrative and Security Framework with a community-string-based framework. It retains SNMPv2Classic's bulk retrieval and improved error handling.
SNMPv2C includes:
-
SNMPv2: Version 2 of the Simple Network Management Protocol, a Draft Internet Standard defined in RFCs 1902 through 1907.
-
SNMPv2C: The community-string-based Administrative Framework for SNMPv2, an Experimental Internet Protocol defined in RFC 1901.
Both SNMPv1 and SNMPv2C use a community-based security model. The community of managers able to access the agent’s Management Information Base (MIB) is defined by an IP address access control list and password.
SNMPv2C includes a bulk retrieval function that retrieves tables and large quantities of information, minimizing the number of required round-trips. It also provides improved error handling with expanded error codes that distinguish different error conditions, which are reported through a single error code in SNMPv1.
-
-
SNMPv3: SNMPv3, Version 3 of the SNMP, is an interoperable standards-based protocol defined in RFCs 2273 to 2275. SNMPv3 provides secure access to devices by authenticating and encrypting packets over the network. It includes these security features:
-
message integrity: Ensures that a packet was not tampered with in transit.
-
authentication: Determines that the message is from a valid source.
-
encryption: Mixes the contents of a package to prevent it from being read by an unauthorized source.

Note
To select encryption, enter the priv keyword.
SNMPv3 provides for both security models and security levels. A security model is an authentication strategy set up for a user and the group within which the user resides. A security level is the permitted level of security within a security model. A combination of the security level and the security model determines which security method is used when handling an SNMP packet. Available security models are SNMPv1, SNMPv2C, and SNMPv3.
-
The following table identifies characteristics and compares different combinations of security models and levels:
| Model | Level | Authentication | Encryption | Result |
|---|---|---|---|---|
| SNMPv1 | noAuthNoPriv | Community string | No | Uses a community string match for authentication. |
| SNMPv2C | noAuthNoPriv | Community string | No | Uses a community string match for authentication. |
| SNMPv3 | noAuthNoPriv | Username | No | Uses a username match for authentication. |
| SNMPv3 | authNoPriv | Message Digest 5 (MD5) or Secure Hash Algorithm (SHA) | No | Provides authentication based on the HMAC-MD5 or HMAC-SHA algorithms. |
| SNMPv3 | authPriv | MD5 or SHA | Data Encryption Standard (DES) or Advanced Encryption Standard (AES) |
Provides authentication based on the HMAC-MD5 or HMAC-SHA algorithms. Allows specifying the User-based Security Model (USM) with these encryption algorithms:
|


 Feedback
Feedback