Comprehensive, analytics-driven coverage
Pre-emptive threat blocking, insightful machine learning, quicker detection, and industry-leading threat intelligence: Cisco security analytics has all the angles covered.
Secure network and cloud infrastructure
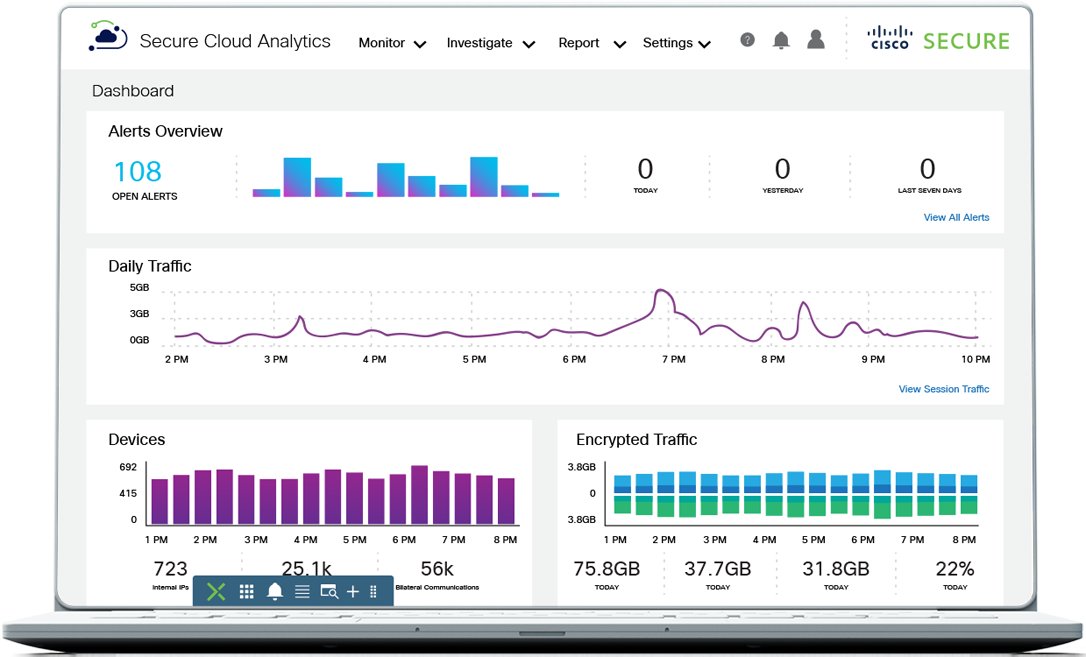
When your security can weather any storm, you can take full advantage of your network and the cloud. Process billions of network sessions, target anomalies, and display critical alerts—even in encrypted traffic.
Secure user access
Work confidently by developing a baseline for normal access, then analyze each new access attempt to spot anomalous behavior. Gain insight into threats such as account takeover, access abuse, and compromised insiders.
Secure applications
Get complete in-depth visibility into application components, communications, and dependencies to enable faster threat detection and consistent network microsegmentation.
Secure endpoints
Handle known and unknown threats. Identify malicious files and activities based on the traits of known malware. Machine learning capabilities help detect never-before-seen malware at the point of entry.
Cisco Secure Endpoint
Establish protection, detection, response, and user access coverage to defend your endpoints.
Cisco Secure Workload
Achieve security in multicloud environments across cloud, application, and workload.
Cisco Duo
Gain complete device visibility and trust to safeguard all users, devices, and applications anywhere.
Cisco Umbrella
Protect users everywhere with lightning fast, flexible, cloud-delivered security.
Add value to security solutions
Cisco Security Enterprise Agreement
Instant savings
Experience security software buying flexibility with one easy-to-manage agreement.
Services for security
Let the experts secure your business
Get more from your investments and enable constant vigilance to protect your organization.