Cyber Vision New UI
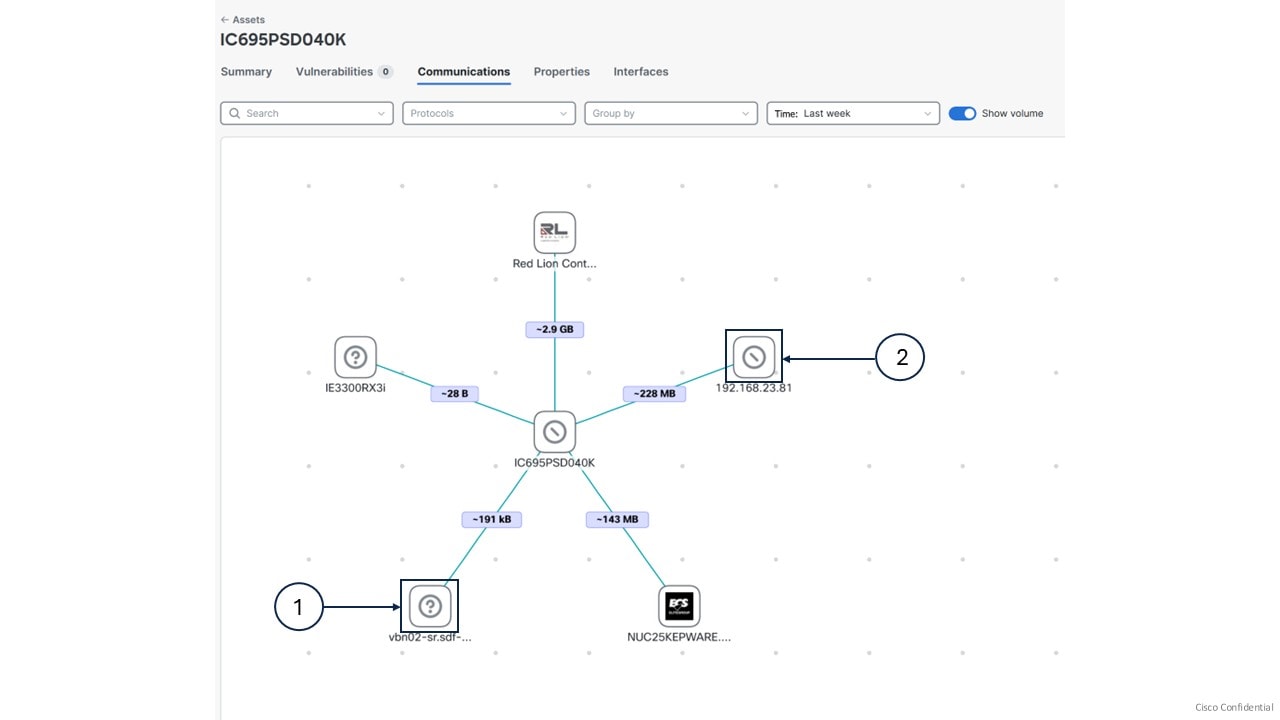
A Cyber Vision New UI is an asset-based user interface that
-
organizes information around assets, which is a clearer representation of physical equipment, instead of discrete components or device entries,
-
aggregates multiple network identities (including interfaces, IP addresses, and MAC addresses) that belong to the same physical equipment, and
-
prioritizes the most relevant information, such as asset name, type, and version, to help users stay focused and reduce clutter.
|
Feature |
Release Information |
Feature Description |
|---|---|---|
|
New UI |
Release 5.3.x |
Cisco Cyber Vision Center offers New UI that comprises simplified, structured views of assets, vulnerabilities, and alerts. The New UI includes a new method for automatically grouping assets using AI-based clustering. Click Go to Cyber Vision New UI in the top banner of your Center to get started. |
Key differences between Classic UI and New UI
The Classic UI focuses on technical entities such as components and devices. Users need to manually define presets, such as baselines or monitoring sets. They often manage separate entries for each network identity, which results in complexity and confusion.
The Cyber Vision New UI connects the physical industrial environment and its digital representation. It visually groups all elements associated with a single physical equipment. Examples include production line equipment or customer installations.
|
Feature |
Classic UI |
New UI |
|---|---|---|
|
Entity focus |
Components, devices |
Assets—representation of physical equipment |
|
Information grouping |
Each network identity shown as a separate item |
Multiple identities grouped by asset |
|
User effort |
Requires manual preset definitions |
Provides automatic aggregation to improve clarity |
|
Information display |
Shows all details, often overwhelming |
Displays only the most relevant attributes of each asset. |

 Feedback
Feedback