Cisco Workgroup Bridges
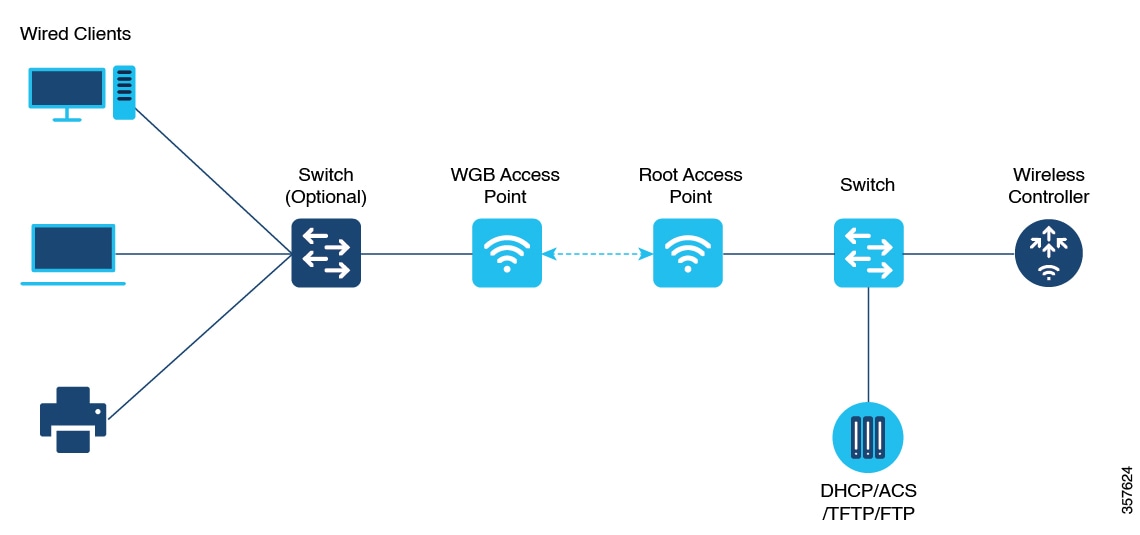
A workgroup bridge (WGB) is an Access Point (AP) mode to provide wireless connectivity to wired clients that are connected to the Ethernet port of the WGB AP. A WGB connects a wired network over a single wireless segment by learning the MAC addresses of its wired clients on the Ethernet interface and reporting them to the WLC through infrastructure AP using Internet Access Point Protocol (IAPP) messaging. The WGB establishes a single wireless connection to the root AP, which in turn, treats the WGB as a wireless client.
Starting from Cisco IOS XE Cupertino 17.8.1, WGB is supported on the following Cisco Catalyst 9100 Series Access Points.
-
Cisco Catalyst 9105
-
Cisco Catalyst 9115
-
Cisco Catalyst 9120
Starting from Cisco IOS XE Dublin 17.10.1, WGB is supported on the following Cisco Catalyst 9100 Series Access Points.
-
Cisco Catalyst 9124
-
Cisco Catalyst 9130
From Cisco IOS XE Cupertino 17.9.1 onwards, WGB supports one radio for uplink (backhaul) connectivity and another radio for serving wireless clients. This feature is supported on the Cisco 11AX APs such as Cisco Catalyst 9105 APs, Cisco Catalyst 9115 APs, Cisco Catalyst 9120 APs.
OPEN and PSK security (WPA2 Personal) based wireless clients can be associated to WGB independent of its uplink connectivity, but they will not be able to pass traffic unless WGB has uplink connectivity. Radius server must be configured and the WGB should have uplink connectivity for authentication of wireless clients to 802.1x security (WPA2 Enterprise) WLAN. Both IPv4 and IPv6 traffic forwarding is supported for wireless clients. Static IP and Passive Client support is enabled by default on these WLANs.
The following features are supported for use with a WGB:
|
Feature |
Cisco Wave 2 APs |
Cisco 11AX APs |
|---|---|---|
|
802.11r |
Supported |
Supported |
|
QOS |
Supported |
Supported |
|
UWGB mode |
Supported |
Not supported |
|
IGMP Snooping or Multicast |
Supported |
Supported |
|
802.11w |
Supported |
Supported |
|
PI support (without SNMP) |
Not supported |
Not supported |
|
IPv6 |
Supported |
Supported |
|
VLAN |
Supported |
Supported |
|
802.11i (WPAv2) |
Supported |
Supported |
|
Broadcast tagging/replicate |
Supported |
Supported |
|
Unified VLAN client |
Supported |
Supported |
|
WGB client |
Supported |
Supported |
|
802.1x – PEAP, EAP-FAST, EAP-TLS |
Supported |
Supported |
|
NTP |
Supported |
Supported |
|
Wired client support on all LAN ports |
Supported in all Wired-0, 1 and LAN ports 1, 2, and 3 |
Supported in all Wired-0, 1 and LAN ports 1, 2, and 3 |
|
Second radio wireless client support |
Not supported |
Supported |
The following table shows the supported and unsupported authentication and switching modes for Cisco APs when connecting to a WGB.
 Note |
Workgroup Bridge mode is supported on the WiFi6 Pluggable Module from Cisco IOS XE Bengaluru 17.6.1. |
|
Access Points |
Requirements |
|---|---|
|
Cisco Aironet 2800, 3800, 4800, 1562, and Cisco Catalyst 9105, 9115, 9120, 9124, and 9130, IW6300 and ESW6300 Series |
CAPWAP image starting from Cisco AireOS 8.8 release. |
-
MAC filtering is not supported for wired clients.
-
Idle timeout is not supported for both WGB and wired clients.
-
Session timeout is not applicable for wired clients.
-
Web authentication is not supported.
-
The total number of clients supported by WGB (wired + wireless) is limited to 20 clients.
-
If you want to use a chain of certificates, copy all the CA certificates to a file and install it under a trust point on the WGB, else server certificate validation may fail.
-
Wired clients connected to a WGB inherit the WGB's QoS and AAA override attributes.
-
To enable the WGB to communicate with the root AP, create a WLAN and make sure that Aironet IE is enabled under the Advanced settings.
-
WPA2 Enterprise security works only if the uplink WLAN is enabled for FlexConnect local switching or Fabric enabled WLAN.
-
Radius override is not supported for wireless clients that are associated with WGB WLANs.
-
WGB does not support 802.1X wired client authentication when used with power injector.
The power-injector drops all EAPOL packets received from the wired client and does not forward it to the WGB's wired0 interface. In such cases, use PoE plus hub behind the wired0 interface and connect the wired clients to the hub.
-
After WGB reload, the WGB 802.1X wired clients behind a hub do not trigger authentication automatically, unless done manually.
After WGB is reloaded the WGB dot1x wired clients which are behind a hub remain authenticated or connected on their side and do not get notified that the WGB is reloaded. Clients are also not shown on the WGB bridge table. The client interfaces must be manually disabled and enabled back to trigger authentication.
-
When the 802.1X wired client Ethernet interface is disabled and then enabled again, client authentication might fail for some of dot1x wired clients, at times.
 Feedback
Feedback