Loop Detection Guard
Need for Loop Detection Guard
While Spanning Tree Protocol (STP) is typically used to prevent network loops, loop detection guard is essential in environments with unmanaged switches that do not support STP or where STP is not configured. In such scenarios—especially when edge switches are connected to an unmanaged switch and STP is disabled, a dedicated loop detection mechanism is essential to ensure network stability.
Loop detection mechanism
To detect loops, the system sends loop-detect frames from the interface, at preconfigured intervals. When a loop is detected, the configured action is taken. Loop detection guard is enabled at the interface level.
Supported devices
This feature is available with Network Essential license and is supported on these switches:
-
Cisco Catalyst IE3100 Series Switches
-
Cisco Catalyst IE3200 Series Switches
-
Cisco Catalyst IE3300 Series Switches
-
Cisco Catalyst IE3400 Series Switches
Types of loops
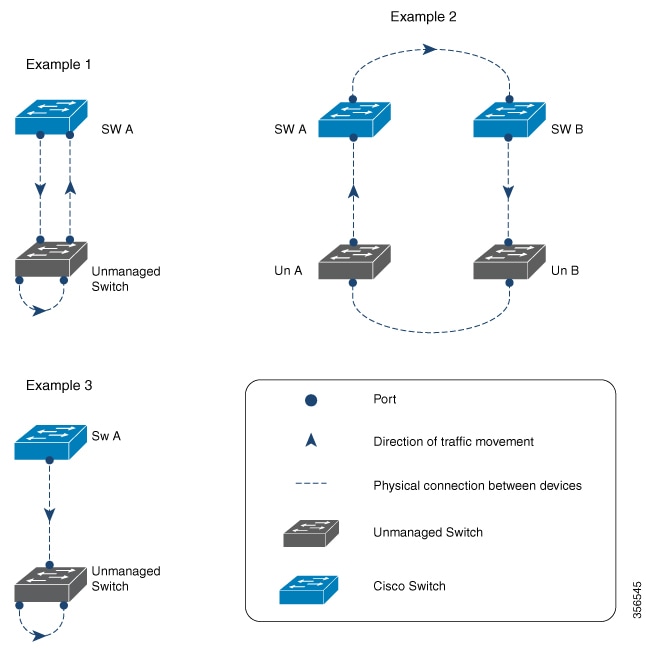
The figure given here illustrates how loops occur.
-
Example 1: A managed switch (SW A) is sending traffic to an unmanaged switch on one port and receiving traffic from the same unmanaged switch, on another port. On the unmanaged switch, the port receiving traffic is connected to the port sending the traffic back to the network. This creates a loop between the managed and unmanaged switches.
-
Example 2: Two managed switches (SW A and SW B) are sending traffic to two unmanaged switches (Un A and Un B). Traffic is moving from SW A to SW B to Un A to Un B and back to SW A, resulting in a network loop.
-
Example 3: A cable connects two ports on the unmanaged switch, resulting in a network loop.
 Feedback
Feedback