- Preface
- Using the Command-Line Interface
-
- Configuring Spanning Tree Protocol
- Configuring Multiple Spanning-Tree Protocol
- Configuring Optional Spanning-Tree Features
- Configuring EtherChannels
- Configuring Link-State Tracking
- Configuring Flex Links and the MAC Address-Table Move Update Feature
- Configuring UniDirectional Link Detection
- Configuring Resilient Ethernet Protocol
-
- Security Features Overview
- Preventing Unauthorized Access
- Controlling Switch Access with Passwords and Privilege Levels
- Configuring TACACS+
- Configuring RADIUS
- Configuring Kerberos
- Configuring Local Authentication and Authorization
- Configuring Secure Shell (SSH)
- Configuring Secure Socket Layer HTTP
- Configuring IPv4 ACLs
- Configuring IPv6 ACLs
- Configuring DHCP
- Configuring IP Source Guard
- Configuring Dynamic ARP Inspection
- Configuring IEEE 802.1x Port-Based Authentication
- Configuring Web-Based Authentication
- Configuring Port-Based Traffic Control
- Configuring IPv6 First Hop Security
- Configuring Cisco TrustSec
- Configuring FIPS
- Index
Consolidated Platform Configuration Guide, Cisco IOS XE 15.2(2)E (Catalyst 2960-XR Switch)
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
- Updated:
- July 23, 2014
Chapter: Configuring QoS
- Finding Feature Information
- Prerequisites for QoS
- Restrictions for QoS
- Information About QoS
- Enabling QoS Globally
- Enabling VLAN-Based QoS on Physical Ports
- Configuring Classification Using Port Trust States
- Configuring a QoS Policy
- Classifying Traffic by Using ACLs
- Classifying Traffic by Using Class Maps
- Classifying Traffic by Using Class Maps and Filtering IPv6 Traffic
- Classifying, Policing, and Marking Traffic on Physical Ports by Using Policy Maps
- Classifying, Policing, and Marking Traffic on SVIs by Using Hierarchical Policy Maps
- Classifying, Policing, and Marking Traffic by Using Aggregate Policers
- Configuring DSCP Maps
- Configuring Egress Queue Characteristics
- Configuration Guidelines
- Allocating Buffer Space to and Setting WTD Thresholds for an Egress Queue Set
- Mapping DSCP or CoS Values to an Egress Queue and to a Threshold ID
- Configuring SRR Shaped Weights on Egress Queues
- Configuring SRR Shared Weights on Egress Queues
- Configuring the Egress Expedite Queue
- Limiting the Bandwidth on an Egress Interface
- Example: Configuring Port to the DSCP-Trusted State and Modifying the DSCP-to-DSCP-Mutation Map
- Examples: Classifying Traffic by Using ACLs
- Examples: Classifying Traffic by Using Class Maps
- Examples: Classifying, Policing, and Marking Traffic on Physical Ports Using Policy Maps
- Examples: Classifying, Policing, and Marking Traffic on SVIs by Using Hierarchical Policy Maps
- Examples: Classifying, Policing, and Marking Traffic by Using Aggregate Policers
- Examples: Configuring DSCP Maps
- Examples: Configuring Egress Queue Characteristics
Configuring QoS
- Finding Feature Information
- Prerequisites for QoS
- Restrictions for QoS
- Information About QoS
- How to Configure QoS
- Monitoring Standard QoS
- Configuration Examples for QoS
- Where to Go Next
- Additional References
- Feature History and Information for QoS
Finding Feature Information
Your software release may not support all the features documented in this module. For the latest caveats and feature information, see Bug Search Tool and the release notes for your platform and software release. To find information about the features documented in this module, and to see a list of the releases in which each feature is supported, see the feature information table at the end of this module.
Use Cisco Feature Navigator to find information about platform support and Cisco software image support. To access Cisco Feature Navigator, go to http://www.cisco.com/go/cfn. An account on Cisco.com is not required.
Prerequisites for QoS
Before configuring standard QoS, you must have a thorough understanding of these items:
The types of applications used and the traffic patterns on your network.
Traffic characteristics and needs of your network. For example, is the traffic on your network bursty? Do you need to reserve bandwidth for voice and video streams?
You can configure QoS on physical ports and on switch virtual interfaces (SVIs). Other than to apply policy maps, you configure the QoS settings, such as classification, queueing, and scheduling, the same way on physical ports and SVIs. When configuring QoS on a physical port, you apply a nonhierarchical policy map. When configuring QoS on an SVI, you apply a nonhierarchical or a hierarchical policy map.
QoS ACL Guidelines
Follow these guidelines when configuring QoS with access control lists (ACLs):
It is not possible to match IP fragments against configured IP extended ACLs to enforce QoS. IP fragments are sent as best-effort. IP fragments are denoted by fields in the IP header.
Only one ACL per class map and only one match class-map configuration command per class map are supported. The ACL can have multiple ACEs, which match fields against the contents of the packet.
A trust statement in a policy map requires multiple hardware entries per ACL line. If an input service policy map contains a trust statement in an ACL, the access list might be too large to fit into the available QoS hardware memory, and an error can occur when you apply the policy map to a port. Whenever possible, you should minimize the number of lines is a QoS ACL.
Applying QoS on Interfaces Guidelines
These are the guidelines for configuring QoS on physical ports and SVIs (Layer 3 VLAN interfaces):
You can configure QoS on physical ports and SVIs. When configuring QoS on physical ports, you create and apply nonhierarchical policy maps. When configuring QoS on SVIs, you can create and apply nonhierarchical and hierarchical policy maps.
Incoming traffic is classified, policed, and marked down (if configured) regardless of whether the traffic is bridged, routed, or sent to the CPU. It is possible for bridged frames to be dropped or to have their DSCP and CoS values modified.
Follow these guidelines when configuring policy maps on physical ports or SVIs:
You cannot apply the same policy map to a physical port and to an SVI.
If VLAN-based QoS is configured on a physical port, the switch removes all the port-based policy maps on the port. The traffic on this physical port is now affected by the policy map attached to the SVI to which the physical port belongs.
In a hierarchical policy map attached to an SVI, you can only configure an individual policer at the interface level on a physical port to specify the bandwidth limits for the traffic on the port. The ingress port must be configured as a trunk or as a static-access port. You cannot configure policers at the VLAN level of the hierarchical policy map.
The switch does not support aggregate policers in hierarchical policy maps.
After the hierarchical policy map is attached to an SVI, the interface-level policy map cannot be modified or removed from the hierarchical policy map. A new interface-level policy map also cannot be added to the hierarchical policy map. If you want these changes to occur, the hierarchical policy map must first be removed from the SVI. You also cannot add or remove a class map specified in the hierarchical policy map.
Policing Guidelines
-
The port ASIC device, which controls more than one physical port, supports 256 policers (255 user-configurable policers plus 1 policer reserved for system internal use). The maximum number of user-configurable policers supported per port is 63. Policers are allocated on demand by the software and are constrained by the hardware and ASIC boundaries.
For example, you could configure 32 policers on a Gigabit Ethernet port and 7 policers on a 10-Gigabit Ethernet port, or you could configure 64 policers on a Gigabit Ethernet port and 4 policers on a 10-Gigabit Ethernet port. Policers are allocated on demand by the software and are constrained by the hardware and ASIC boundaries.
You cannot reserve policers per port; there is no guarantee that a port will be assigned to any policer.
-
Only one policer is applied to a packet on an ingress port. Only the average rate and committed burst parameters are configurable.
-
You can create an aggregate policer that is shared by multiple traffic classes within the same nonhierarchical policy map. However, you cannot use the aggregate policer across different policy maps.
-
On a port configured for QoS, all traffic received through the port is classified, policed, and marked according to the policy map attached to the port. On a trunk port configured for QoS, traffic in all VLANs received through the port is classified, policed, and marked according to the policy map attached to the port.
-
If you have EtherChannel ports configured on your switch, you must configure QoS classification, policing, mapping, and queueing on the individual physical ports that comprise the EtherChannel. You must decide whether the QoS configuration should match on all ports in the EtherChannel.
-
If you need to modify a policy map of an existing QoS policy, first remove the policy map from all interfaces, and then modify or copy the policy map. After you finish the modification, apply the modified policy map to the interfaces. If you do not first remove the policy map from all interfaces, high CPU usage can occur, which, in turn, can cause the console to pause for a very long time.
General QoS Guidelines
Control traffic (such as spanning-tree bridge protocol data units [BPDUs] and routing update packets) received by the switch are subject to all ingress QoS processing.
You are likely to lose data when you change queue settings; therefore, try to make changes when traffic is at a minimum.
A switch that is running the IP services feature set supports QoS DSCP and IP precedence matching in policy-based routing (PBR) route maps with these limitations:
Restrictions for QoS
The following are the restrictions for QoS:
Ingress queueing and scheduling are not supported on the switch.
IPv6 QoS is not supported on switches running the LAN base feature set.
IPv6 ACLs are not supported on switches running the LAN base feature set.
The switch supports 3 templates: default, vlan, and IPv4. Both the default and vlan templates support IPv6. The IPv4 template does not support IPv6.
You can configure only individual policers on an SVI.
For the class-map [match-all | match-any] class-map-name global configuration command, because only one match command per class map is supported, the match-all and match-any keywords function the same.
Information About QoS
QoS Implementation
Typically, networks operate on a best-effort delivery basis, which means that all traffic has equal priority and an equal chance of being delivered in a timely manner. When congestion occurs, all traffic has an equal chance of being dropped.
When you configure the QoS feature, you can select specific network traffic, prioritize it according to its relative importance, and use congestion-management and congestion-avoidance techniques to provide preferential treatment. Implementing QoS in your network makes network performance more predictable and bandwidth utilization more effective.
The QoS implementation is based on the Differentiated Services (Diff-Serv) architecture, a standard from the Internet Engineering Task Force (IETF). This architecture specifies that each packet is classified upon entry into the network.
The classification is carried in the IP packet header, using 6 bits from the deprecated IP type of service (ToS) field to carry the classification (class) information. Classification can also be carried in the Layer 2 frame.

- Layer 2 Frame Prioritization Bits
- Layer 3 Packet Prioritization Bits
- End-to-End QoS Solution Using Classification
Layer 2 Frame Prioritization Bits
Layer 2 Inter-Switch Link (ISL) frame headers have a 1-byte User field that carries an IEEE 802.1p class of service (CoS) value in the three least-significant bits. On ports configured as Layer 2 ISL trunks, all traffic is in ISL frames.
Layer 2 802.1Q frame headers have a 2-byte Tag Control Information field that carries the CoS value in the three most-significant bits, which are called the User Priority bits. On ports configured as Layer 2 802.1Q trunks, all traffic is in 802.1Q frames except for traffic in the native VLAN.
Other frame types cannot carry Layer 2 CoS values.
Layer 2 CoS values range from 0 for low priority to 7 for high priority.
Layer 3 Packet Prioritization Bits
Layer 3 IP packets can carry either an IP precedence value or a Differentiated Services Code Point (DSCP) value. QoS supports the use of either value because DSCP values are backward-compatible with IP precedence values.
IP precedence values range from 0 to 7. DSCP values range from 0 to 63.
End-to-End QoS Solution Using Classification
All switches and routers that access the Internet rely on the class information to provide the same forwarding treatment to packets with the same class information and different treatment to packets with different class information. The class information in the packet can be assigned by end hosts or by switches or routers along the way, based on a configured policy, detailed examination of the packet, or both. Detailed examination of the packet is expected to occur closer to the edge of the network, so that the core switches and routers are not overloaded with this task.
Switches and routers along the path can use the class information to limit the amount of resources allocated per traffic class. The behavior of an individual device when handling traffic in the Diff-Serv architecture is called per-hop behavior. If all devices along a path provide a consistent per-hop behavior, you can construct an end-to-end QoS solution.
Implementing QoS in your network can be a simple task or complex task and depends on the QoS features offered by your internetworking devices, the traffic types and patterns in your network, and the granularity of control that you need over incoming and outgoing traffic.
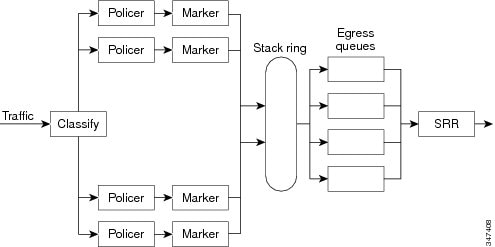
QoS Basic Model
To implement QoS, the switch must distinguish packets or flows from one another (classify), assign a label to indicate the given quality of service as the packets move through the switch, make the packets comply with the configured resource usage limits (police and mark), and provide different treatment (queue and schedule) in all situations where resource contention exists. The switch also needs to ensure that traffic sent from it meets a specific traffic profile (shape).
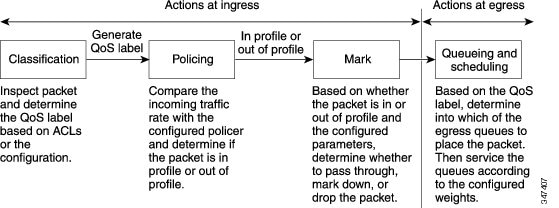
- Actions at Ingress Port
- Actions at Egress Port
- Classification Overview
- Policing and Marking Overview
- Mapping Tables Overview
- Queueing and Scheduling Overview
- Queueing and Scheduling on Egress Queues
- Packet Modification
Actions at Ingress Port
Actions at the ingress port include classifying traffic, policing, marking, and scheduling:
Classifying a distinct path for a packet by associating it with a QoS label. The switch maps the CoS or DSCP in the packet to a QoS label to distinguish one kind of traffic from another. The QoS label that is generated identifies all future QoS actions to be performed on this packet.
Policing determines whether a packet is in or out of profile by comparing the rate of the incoming traffic to the configured policer. The policer limits the bandwidth consumed by a flow of traffic. The result is passed to the marker.
Marking evaluates the policer and configuration information for the action to be taken when a packet is out of profile and determines what to do with the packet (pass through a packet without modification, marking down the QoS label in the packet, or dropping the packet).
 Note | Queueing and scheduling are only supported at egress and not at ingress on the switch. |
Actions at Egress Port
Actions at the egress port include queueing and scheduling:
Queueing evaluates the QoS packet label and the corresponding DSCP or CoS value before selecting which of the four egress queues to use. Because congestion can occur when multiple ingress ports simultaneously send data to an egress port, WTD differentiates traffic classes and subjects the packets to different thresholds based on the QoS label. If the threshold is exceeded, the packet is dropped.
Scheduling services the four egress queues based on their configured SRR shared or shaped weights. One of the queues (queue 1) can be the expedited queue, which is serviced until empty before the other queues are serviced.
Classification Overview
Classification is the process of distinguishing one kind of traffic from another by examining the fields in the packet. Classification is enabled only if QoS is globally enabled on the switch. By default, QoS is globally disabled, so no classification occurs.
During classification, the switch performs a lookup and assigns a QoS label to the packet. The QoS label identifies all QoS actions to be performed on the packet and from which queue the packet is sent.
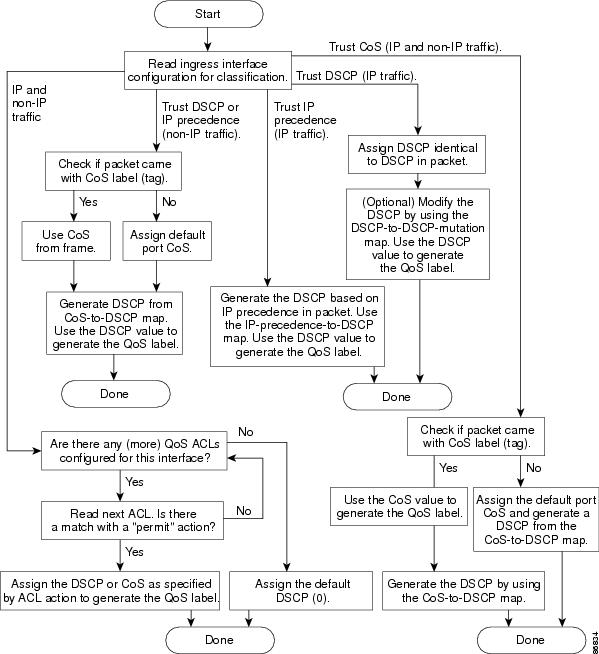
The QoS label is based on the DSCP or the CoS value in the packet and decides the queueing and scheduling actions to perform on the packet. The label is mapped according to the trust setting and the packet type as shown in Classification Flowchart.
You specify which fields in the frame or packet that you want to use to classify incoming traffic.
- Non-IP Traffic Classification
- IP Traffic Classification
- Classification Flowchart
- Access Control Lists
- Classification Based on Class Maps and Policy Maps
Non-IP Traffic Classification
After classification, the packet is sent to the policing and marking stages.
IP Traffic Classification
IP Traffic Classification |
Description |
|---|---|
Trust the DSCP value |
Trust the DSCP value in the incoming packet (configure the port to trust DSCP), and assign the same DSCP value to the packet. The IETF defines the 6 most-significant bits of the 1-byte ToS field as the DSCP. The priority represented by a particular DSCP value is configurable. DSCP values range from 0 to 63. You can also classify IP traffic based on IPv6 DSCP. For ports that are on the boundary between two QoS administrative domains, you can modify the DSCP to another value by using the configurable DSCP-to-DSCP-mutation map. |
Trust the IP precedence value |
Trust the IP precedence value in the incoming packet (configure the port to trust IP precedence), and generate a DSCP value for the packet by using the configurable IP-precedence-to-DSCP map. The IP Version 4 specification defines the 3 most-significant bits of the 1-byte ToS field as the IP precedence. IP precedence values range from 0 for low priority to 7 for high priority. You can also classify IP traffic based on IPv6 precedence. |
Trust the CoS value |
Trust the CoS value (if present) in the incoming packet, and generate a DSCP value for the packet by using the CoS-to-DSCP map. If the CoS value is not present, use the default port CoS value. |
IP standard or an extended ACL |
Perform the classification based on a configured IP standard or an extended ACL, which examines various fields in the IP header. If no ACL is configured, the packet is assigned 0 as the DSCP and CoS values, which means best-effort traffic. Otherwise, the policy-map action specifies a DSCP or CoS value to assign to the incoming frame. |
Override configured CoS |
Override the configured CoS of incoming packets, and apply the default port CoS value to them. For IPv6 packets, the DSCP value is rewritten by using the CoS-to-DSCP map and by using the default CoS of the port. You can do this for both IPv4 and IPv6 traffic. |
After classification, the packet is sent to the policing and marking stages.
Classification Flowchart
Access Control Lists
You can use IP standard, IP extended, or Layer 2 MAC ACLs to define a group of packets with the same characteristics (class). You can also classify IP traffic based on IPv6 ACLs.
In the QoS context, the permit and deny actions in the access control entries (ACEs) have different meanings from security ACLs:
If a match with a permit action is encountered (first-match principle), the specified QoS-related action is taken.
If a match with a deny action is encountered, the ACL being processed is skipped, and the next ACL is processed.
If no match with a permit action is encountered and all the ACEs have been examined, no QoS processing occurs on the packet, and the switch offers best-effort service to the packet.
If multiple ACLs are configured on a port, the lookup stops after the packet matches the first ACL with a permit action, and QoS processing begins.

NoteWhen creating an access list, note that by default the end of the access list contains an implicit deny statement for everything if it did not find a match before reaching the end.
After a traffic class has been defined with the ACL, you can attach a policy to it. A policy might contain multiple classes with actions specified for each one of them. A policy might include commands to classify the class as a particular aggregate (for example, assign a DSCP) or rate-limit the class. This policy is then attached to a particular port on which it becomes effective.
You implement IP ACLs to classify IP traffic by using the access-list global configuration command; you implement Layer 2 MAC ACLs to classify non-IP traffic by using the mac access-list extended global configuration command.
Classification Based on Class Maps and Policy Maps
A class map is a mechanism that you use to name a specific traffic flow (or class) and to isolate it from all other traffic. The class map defines the criteria used to match against a specific traffic flow to further classify it. The criteria can include matching the access group defined by the ACL or matching a specific list of DSCP or IP precedence values. If you have more than one type of traffic that you want to classify, you can create another class map and use a different name. After a packet is matched against the class-map criteria, you further classify it through the use of a policy map.
A policy map specifies which traffic class to act on. Actions can include trusting the CoS, DSCP, or IP precedence values in the traffic class; setting a specific DSCP or IP precedence value in the traffic class; or specifying the traffic bandwidth limitations and the action to take when the traffic is out of profile. Before a policy map can be effective, you must attach it to a port.
You create a class map by using the class-map global configuration command or the class policy-map configuration command. You should use the class-map command when the map is shared among many ports. When you enter the class-map command, the switch enters the class-map configuration mode. In this mode, you define the match criterion for the traffic by using the match class-map configuration command.
You can configure a default class by using the class class-default policy-map configuration command. Unclassified traffic (traffic specified in the other traffic classes configured on the policy-map) is treated as default traffic.
You create and name a policy map by using the policy-map global configuration command. When you enter this command, the switch enters the policy-map configuration mode. In this mode, you specify the actions to take on a specific traffic class by using the class, trust, or set policy-map configuration and policy-map class configuration commands.
The policy map can contain the police and police aggregate policy-map class configuration commands, which define the policer, the bandwidth limitations of the traffic, and the action to take if the limits are exceeded.
To enable the policy map, you attach it to a port by using the service-policy interface configuration command.
You can apply a nonhierarchical policy map to a physical port or an SVI. However, a hierarchical policy map can only be applied to an SVI. A hierarchical policy map contains two levels. The first level, the VLAN level, specifies the actions to be taken against a traffic flow on the SVI. The second level, the interface level, specifies the actions to be taken against the traffic on the physical ports that belong to the SVI. The interface-level actions are specified in the interface-level policy map.
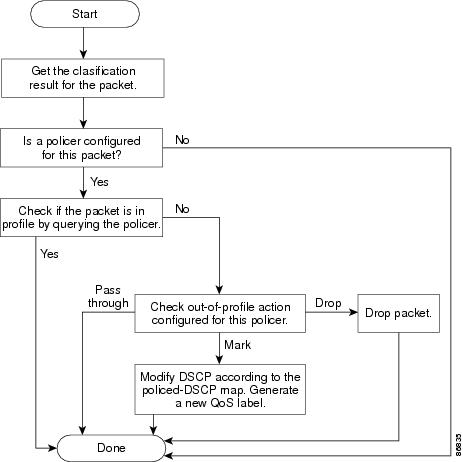
Policing and Marking Overview
After a packet is classified and has a DSCP-based or CoS-based QoS label assigned to it, the policing and marking process can begin.
Policing involves creating a policer that specifies the bandwidth limits for the traffic. Packets that exceed the limits are out of profile or nonconforming. Each policer decides on a packet-by-packet basis whether the packet is in or out of profile and specifies the actions on the packet. These actions, carried out by the marker, include passing through the packet without modification, dropping the packet, or modifying (marking down) the assigned DSCP of the packet and allowing the packet to pass through. The configurable policed-DSCP map provides the packet with a new DSCP-based QoS label. Marked-down packets use the same queues as the original QoS label to prevent packets in a flow from getting out of order.
Physical Port Policing
In policy maps on physical ports, you can create the following types of policers:
Individual—QoS applies the bandwidth limits specified in the policer separately to each matched traffic class. You configure this type of policer within a policy map by using the police policy-map class configuration command.
Aggregate—QoS applies the bandwidth limits specified in an aggregate policer cumulatively to all matched traffic flows. You configure this type of policer by specifying the aggregate policer name within a policy map by using the police aggregate policy-map class configuration command. You specify the bandwidth limits of the policer by using the mls qos aggregate-policer global configuration command. In this way, the aggregate policer is shared by multiple classes of traffic within a policy map.
 Note | You can configure only individual policers on an SVI. |
Policing uses a token-bucket algorithm. As each frame is received by the switch, a token is added to the bucket. The bucket has a hole in it and leaks at a rate that you specify as the average traffic rate in bits per second. Each time a token is added to the bucket, the switch verifies that there is enough room in the bucket. If there is not enough room, the packet is marked as nonconforming, and the specified policer action is taken (dropped or marked down).
How quickly the bucket fills is a function of the bucket depth (burst-byte), the rate at which the tokens are removed (rate-bps), and the duration of the burst above the average rate. The size of the bucket imposes an upper limit on the burst length and limits the number of frames that can be transmitted back-to-back. If the burst is short, the bucket does not overflow, and no action is taken against the traffic flow. However, if a burst is long and at a higher rate, the bucket overflows, and the policing actions are taken against the frames in that burst.
You configure the bucket depth (the maximum burst that is tolerated before the bucket overflows) by using the burst-byte option of the police policy-map class configuration command or the mls qos aggregate-policer global configuration command. You configure how fast (the average rate) that the tokens are removed from the bucket by using the rate-bps option of the police policy-map class configuration command or the mls qos aggregate-policer global configuration command.
The following figure shows the policing and marking process when these types of policy maps are configured:
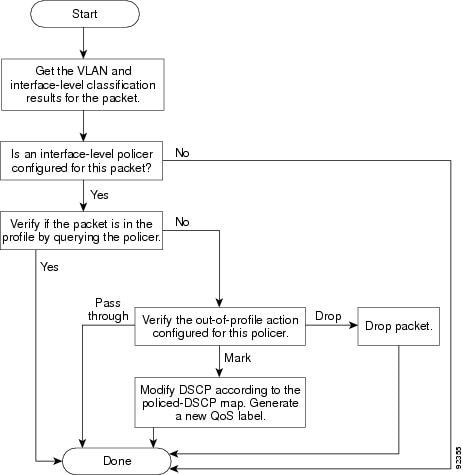
SVI Policing
A hierarchical policy map has two levels. The first level, the VLAN level, specifies the actions to be taken against a traffic flow on an SVI. The second level, the interface level, specifies the actions to be taken against the traffic on the physical ports that belong to the SVI and are specified in the interface-level policy map.
When configuring policing on an SVI, you can create and configure a hierarchical policy map with these two levels:
VLAN level—Create this primary level by configuring class maps and classes that specify the port trust state or set a new DSCP or IP precedence value in the packet. The VLAN-level policy map applies only to the VLAN in an SVI and does not support policers.
Interface level—Create this secondary level by configuring class maps and classes that specify the individual policers on physical ports the belong to the SVI. The interface-level policy map only supports individual policers and does not support aggregate policers. You can configure different interface-level policy maps for each class defined in the VLAN-level policy map.
Mapping Tables Overview
During QoS processing, the switch represents the priority of all traffic (including non-IP traffic) with a QoS label based on the DSCP or CoS value from the classification stage.
The CoS-to-DSCP, DSCP-to-CoS, and the IP-precedence-to-DSCP maps have default values that might or might not be appropriate for your network.
The default DSCP-to-DSCP-mutation map and the default policed-DSCP map are null maps; they map an incoming DSCP value to the same DSCP value. The DSCP-to-DSCP-mutation map is the only map you apply to a specific port. All other maps apply to the entire switch.
Queueing and Scheduling Overview
The switch has queues at specific points to help prevent congestion.
Weighted Tail Drop
As a frame is enqueued to a particular queue, WTD uses the frame’s assigned QoS label to subject it to different thresholds. If the threshold is exceeded for that QoS label (the space available in the destination queue is less than the size of the frame), the switch drops the frame.
Each queue has three threshold values. The QoS label determines which of the three threshold values is subjected to the frame. Of the three thresholds, two are configurable (explicit) and one is not (implicit).
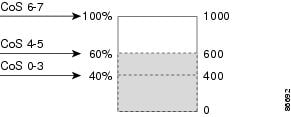
In the example, CoS values 6 and 7 have a greater importance than the other CoS values, and they are assigned to the 100-percent drop threshold (queue-full state). CoS values 4 and 5 are assigned to the 60-percent threshold, and CoS values 0 to 3 are assigned to the 40-percent threshold.
Suppose the queue is already filled with 600 frames, and a new frame arrives. It contains CoS values 4 and 5 and is subjected to the 60-percent threshold. If this frame is added to the queue, the threshold will be exceeded, so the switch drops it.
SRR Shaping and Sharing
You can configure SRR on egress queues for sharing or for shaping.
In shaped mode, the egress queues are guaranteed a percentage of the bandwidth, and they are rate-limited to that amount. Shaped traffic does not use more than the allocated bandwidth even if the link is idle. Shaping provides a more even flow of traffic over time and reduces the peaks and valleys of bursty traffic. With shaping, the absolute value of each weight is used to compute the bandwidth available for the queues.
In shared mode, the queues share the bandwidth among them according to the configured weights. The bandwidth is guaranteed at this level but not limited to it. For example, if a queue is empty and no longer requires a share of the link, the remaining queues can expand into the unused bandwidth and share it among them. With sharing, the ratio of the weights controls the frequency of dequeuing; the absolute values are meaningless. Shaping and sharing is configured per interface. Each interface can be uniquely configured.
Queueing and Scheduling on Egress Queues
The following figure shows queueing and scheduling flowcharts for egress ports on the switch.
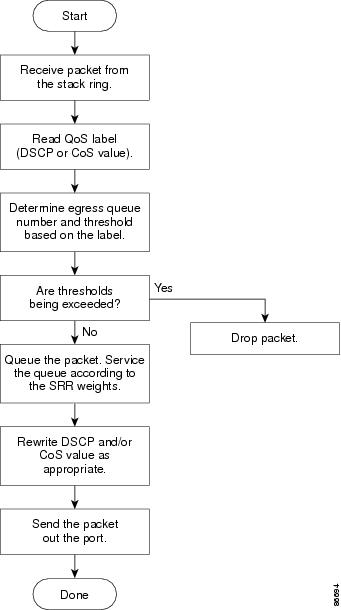
 Note | If the expedite queue is enabled, SRR services it until it is empty before servicing the other three queues. |
- Egress Expedite Queue
- Egress Queue Buffer Allocation
- Buffer and Memory Allocation
- Queues and WTD Thresholds
- Shaped or Shared Mode
Egress Expedite Queue
Each port supports four egress queues, one of which (queue 1) can be the egress expedite queue. These queues are assigned to a queue-set. All traffic exiting the switch flows through one of these four queues and is subjected to a threshold based on the QoS label assigned to the packet.
 Note | If the expedite queue is enabled, SRR services it until it is empty before servicing the other three queues. |
Egress Queue Buffer Allocation
The following figure shows the egress queue buffer.
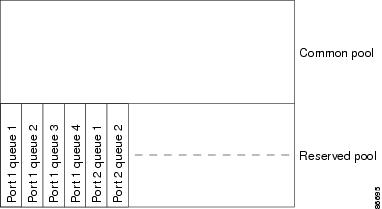
Buffer and Memory Allocation
You guarantee the availability of buffers, set drop thresholds, and configure the maximum memory allocation for a queue-set by using the mls qos queue-set output qset-id threshold queue-id drop-threshold1 drop-threshold2 reserved-threshold maximum-threshold global configuration command. Each threshold value is a percentage of the queue’s allocated memory, which you specify by using the mls qos queue-set output qset-id buffers allocation1 ... allocation4 global configuration command. The sum of all the allocated buffers represents the reserved pool, and the remaining buffers are part of the common pool.
Through buffer allocation, you can ensure that high-priority traffic is buffered. For example, if the buffer space is 400, you can allocate 70 percent of it to queue 1 and 10 percent to queues 2 through 4. Queue 1 then has 280 buffers allocated to it, and queues 2 through 4 each have 40 buffers allocated to them.
You can guarantee that the allocated buffers are reserved for a specific queue in a queue-set. For example, if there are 100 buffers for a queue, you can reserve 50 percent (50 buffers). The switch returns the remaining 50 buffers to the common pool. You also can enable a queue in the full condition to obtain more buffers than are reserved for it by setting a maximum threshold. The switch can allocate the needed buffers from the common pool if the common pool is not empty.
Queues and WTD Thresholds
You can assign each packet that flows through the switch to a queue and to a threshold.
Specifically, you map DSCP or CoS values to an egress queue and map DSCP or CoS values to a threshold ID. You use the mls qos srr-queue output dscp-map queue queue-id {dscp1...dscp8 | threshold threshold-id dscp1...dscp8} or the mls qos srr-queue output cos-map queue queue-id {cos1...cos8 | threshold threshold-id cos1...cos8} global configuration command. You can display the DSCP output queue threshold map and the CoS output queue threshold map by using the show mls qos maps privileged EXEC command.
The queues use WTD to support distinct drop percentages for different traffic classes. Each queue has three drop thresholds: two configurable (explicit) WTD thresholds and one nonconfigurable (implicit) threshold preset to the queue-full state. You assign the two WTD threshold percentages for threshold ID 1 and ID 2. The drop threshold for threshold ID 3 is preset to the queue-full state, and you cannot modify it. You map a port to queue-set by using the queue-set qset-id interface configuration command. Modify the queue-set configuration to change the WTD threshold percentages.
Shaped or Shared Mode
SRR services each queue-set in shared or shaped mode. You map a port to a queue-set by using the queue-set qset-id interface configuration command. You assign shared or shaped weights to the port by using the srr-queue bandwidth share weight1 weight2 weight3 weight4 or the srr-queue bandwidth shape weight1 weight2 weight3 weight4 interface configuration command.
The buffer allocation together with the SRR weight ratios control how much data can be buffered and sent before packets are dropped. The weight ratio is the ratio of the frequency in which the SRR scheduler sends packets from each queue.
All four queues participate in the SRR unless the expedite queue is enabled, in which case the first bandwidth weight is ignored and is not used in the ratio calculation. The expedite queue is a priority queue, and it is serviced until empty before the other queues are serviced. You enable the expedite queue by using the priority-queue out interface configuration command.
You can combine the commands described in this section to prioritize traffic by placing packets with particular DSCPs or CoSs into certain queues, by allocating a large queue size or by servicing the queue more frequently, and by adjusting queue thresholds so that packets with lower priorities are dropped.
Packet Modification
A packet is classified, policed, and queued to provide QoS. The following packet modifications can occur during the process to provide QoS:
For IP and non-IP packets, classification involves assigning a QoS label to a packet based on the DSCP or CoS of the received packet. However, the packet is not modified at this stage; only an indication of the assigned DSCP or CoS value is carried along.
During policing, IP and non-IP packets can have another DSCP assigned to them (if they are out of profile and the policer specifies a markdown DSCP). Once again, the DSCP in the packet is not modified, but an indication of the marked-down value is carried along. For IP packets, the packet modification occurs at a later stage; for non-IP packets the DSCP is converted to CoS and used for queueing and scheduling decisions.
Depending on the QoS label assigned to a frame and the mutation chosen, the DSCP and CoS values of the frame are rewritten. If you do not configure a table map and if you configure the port to trust the DSCP of the incoming frame, the DSCP value in the frame is not changed, but the CoS is rewritten according to the DSCP-to-CoS map. If you configure the port to trust the CoS of the incoming frame and it is an IP packet, the CoS value in the frame is not changed, but the DSCP might be changed according to the CoS-to-DSCP map.
The input mutation causes the DSCP to be rewritten depending on the new value of DSCP chosen. The set action in a policy map also causes the DSCP to be rewritten.
Standard QoS Default Configuration
Standard QoS is disabled by default.
There is no concept of trusted or untrusted ports because the packets are not modified. The CoS, DSCP, and IP precedence values in the packet are not changed.
Traffic is switched in pass-through mode. The packets are switched without any rewrites and classified as best effort without any policing.
When QoS is enabled using the mls qos global configuration command and all other QoS settings are at their defaults, traffic is classified as best effort (the DSCP and CoS value is set to 0) without any policing. No policy maps are configured. The default port trust state on all ports is untrusted.
Default Egress Queue Configuration
The following tables describe the default egress queue configurations.
Default Mapping Table Configuration
The default DSCP-to-DSCP-mutation map is a null map, which maps an incoming DSCP value to the same DSCP value.
The default policed-DSCP map is a null map, which maps an incoming DSCP value to the same DSCP value (no markdown).
DSCP Maps
Default CoS-to-DSCP Map
Default IP-Precedence-to-DSCP Map
Default DSCP-to-CoS Map
How to Configure QoS
Enabling QoS Globally
By default, QoS is disabled on the switch.
The following procedure to enable QoS globally is required.
DETAILED STEPS
Enabling VLAN-Based QoS on Physical Ports
By default, VLAN-based QoS is disabled on all physical switch ports. The switch applies QoS, including class maps and policy maps, only on a physical-port basis. You can enable VLAN-based QoS on a switch port.
The following procedure is required on physical ports that are specified in the interface level of a hierarchical policy map on a Switch Virtual Interface (SVI).
DETAILED STEPS
| Command or Action | Purpose | |||
|---|---|---|---|---|
| Step 1 | configure terminal Example: Switch# configure terminal | |||
| Step 2 | interface interface-id Example: Switch(config)# interface gigabitethernet 1/0/1 | Specifies the physical port, and enter interface configuration mode. | ||
| Step 3 | mls qos vlan-based Example: Switch(config-if)# mls qos vlan-based | Enables VLAN-based QoS on the port.
| ||
| Step 4 | end Example: Switch(config-if)# end | |||
| Step 5 | show mls qos interface interface-id Example: Switch# show mls qos interface gigabitethernet 1/0/1 | |||
| Step 6 | copy running-config startup-config Example: Switch# copy running-config startup-config |
Configuring Classification Using Port Trust States
These sections describe how to classify incoming traffic by using port trust states.
 Note | Depending on your network configuration, you must perform one or more of these tasks in this module or one or more of the tasks in the “QoS Policy Configuration” section on page 37-47. |
- Configuring the Trust State on Ports Within the QoS Domain
- Configuring the CoS Value for an Interface
- Configuring a Trusted Boundary to Ensure Port Security
- Enabling DSCP Transparency Mode
- Configuring the DSCP Trust State on a Port Bordering Another QoS Domain
Configuring the Trust State on Ports Within the QoS Domain
Packets entering a QoS domain are classified at the edge of the QoS domain. When the packets are classified at the edge, the switch port within the QoS domain can be configured to one of the trusted states because there is no need to classify the packets at every switch within the QoS domain.
DETAILED STEPS
| Command or Action | Purpose | |
|---|---|---|
| Step 1 | configure terminal Example: Switch# configure terminal | |
| Step 2 | interface interface-id Example: Switch(config)# interface gigabitethernet 1/0/2 | Specifies the port to be trusted, and enters interface configuration mode. Valid interfaces are physical ports. |
| Step 3 | mls qos trust [cos | dscp | ip-precedence] Example: Switch(config-if)# mls qos trust cos | Configures the port trust state. By default, the port is not trusted. If no keyword is specified, the default is dscp. The keywords have these meanings:
To return a port to its untrusted state, use the no mls qos trust interface configuration command. |
| Step 4 | end Example: Switch(config-if)# end | |
| Step 5 | show mls qos interface Example: Switch# show mls qos interface | |
| Step 6 | copy running-config startup-config Example: Switch# copy running-config startup-config |
Configuring the CoS Value for an Interface
QoS assigns the CoS value specified with the mls qos cos interface configuration command to untagged frames received on trusted and untrusted ports.
Beginning in privileged EXEC mode, follow these steps to define the default CoS value of a port or to assign the default CoS to all incoming packets on the port.
DETAILED STEPS
| Command or Action | Purpose | |||
|---|---|---|---|---|
| Step 1 | configure
terminal
Example: Switch# configure terminal | |||
| Step 2 | interface interface-id Example: Switch(config)# interface gigabitethernet 1/1/1 | Specifies the port to be configured, and enters interface configuration mode. | ||
| Step 3 | mls qos cos {default-cos | override} Example: Switch(config-if)# mls qos override | Configures the default CoS value for the port.
| ||
| Step 4 | end Example: Switch(config-if)# end | |||
| Step 5 | show mls qos interface Example: Switch# show mls qos interface | |||
| Step 6 | copy running-config startup-config Example: Switch# copy running-config startup-config |
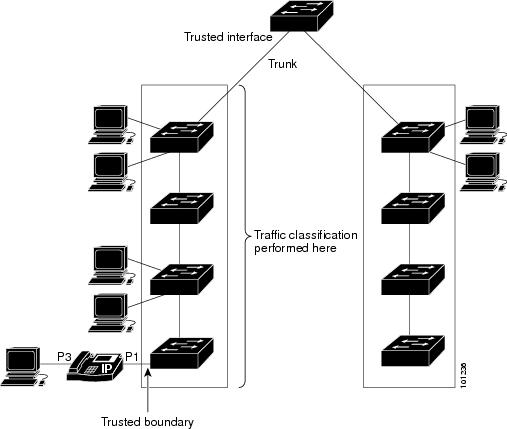
Configuring a Trusted Boundary to Ensure Port Security
In a typical network, you connect a Cisco IP Phone to a switch port and cascade devices that generate data packets from the back of the telephone. The Cisco IP Phone guarantees the voice quality through a shared data link by marking the CoS level of the voice packets as high priority (CoS = 5) and by marking the data packets as low priority (CoS = 0). Traffic sent from the telephone to the switch is typically marked with a tag that uses the 802.1Q header. The header contains the VLAN information and the class of service (CoS) 3-bit field, which is the priority of the packet.
For most Cisco IP Phone configurations, the traffic sent from the telephone to the switch should be trusted to ensure that voice traffic is properly prioritized over other types of traffic in the network. By using the mls qos trust cos interface configuration command, you configure the switch port to which the telephone is connected to trust the CoS labels of all traffic received on that port. Use the mls qos trust dscp interface configuration command to configure a routed port to which the telephone is connected to trust the DSCP labels of all traffic received on that port.
With the trusted setting, you also can use the trusted boundary feature to prevent misuse of a high-priority queue if a user bypasses the telephone and connects the PC directly to the switch. Without trusted boundary, the CoS labels generated by the PC are trusted by the switch (because of the trusted CoS setting). By contrast, trusted boundary uses CDP to detect the presence of a Cisco IP Phone (such as the Cisco IP Phone 7910, 7935, 7940, and 7960) on a switch port. If the telephone is not detected, the trusted boundary feature disables the trusted setting on the switch port and prevents misuse of a high-priority queue. Note that the trusted boundary feature is not effective if the PC and Cisco IP Phone are connected to a hub that is connected to the switch.
In some situations, you can prevent a PC connected to the Cisco IP Phone from taking advantage of a high-priority data queue. You can use the switchport priority extend cos interface configuration command to configure the telephone through the switch CLI to override the priority of the traffic received from the PC.
DETAILED STEPS
| Command or Action | Purpose | |||
|---|---|---|---|---|
| Step 1 | configure
terminal
Example: Switch# configure terminal | |||
| Step 2 | cdp run Example: Switch(config)# cdp run | |||
| Step 3 | interface interface-id Example: Switch(config)# interface gigabitethernet 2/1/1 | Specifies the port connected to the Cisco IP Phone, and enters interface configuration mode. | ||
| Step 4 | cdp enable Example: Switch(config-if)# cdp enable | |||
| Step 5 | Use one of the following:
Example: Switch(config-if)# mls qos trust cos | Configures the switch port to trust the CoS value in traffic received from the Cisco IP Phone. Configures the routed port to trust the DSCP value in traffic received from the Cisco IP Phone. | ||
| Step 6 | mls qos trust device cisco-phone Example: Switch(config-if)# mls qos trust device cisco-phone | Specifies that the Cisco IP Phone is a trusted device. You cannot enable both trusted boundary and auto-QoS (auto qos voip interface configuration command) at the same time; they are mutually exclusive.
| ||
| Step 7 | end Example: Switch(config-if)# end | |||
| Step 8 | show mls qos interface Example: Switch# show mls qos interface | |||
| Step 9 | copy running-config startup-config Example: Switch# copy running-config startup-config |
Enabling DSCP Transparency Mode
The switch supports the DSCP transparency feature. It affects only the DSCP field of a packet at egress. By default, DSCP transparency is disabled. The switch modifies the DSCP field in an incoming packet, and the DSCP field in the outgoing packet is based on the quality of service (QoS) configuration, including the port trust setting, policing and marking, and the DSCP-to-DSCP mutation map.
If DSCP transparency is enabled by using the no mls qos rewrite ip dscp command, the switch does not modify the DSCP field in the incoming packet, and the DSCP field in the outgoing packet is the same as that in the incoming packet.
Regardless of the DSCP transparency configuration, the switch modifies the internal DSCP value of the packet, which the switch uses to generate a class of service (CoS) value that represents the priority of the traffic. The switch also uses the internal DSCP value to select an egress queue and threshold.
DETAILED STEPS
| Command or Action | Purpose | |
|---|---|---|
| Step 1 | configure terminal Example: Switch# configure terminal | |
| Step 2 | mls qos Example: Switch(config)# mls qos | |
| Step 3 | no mls qos rewrite ip dscp Example: Switch(config)# no mls qos rewrite ip dscp | Enables DSCP transparency. The switch is configured to not modify the DSCP field of the IP packet. |
| Step 4 | end Example: Switch(config)# end | |
| Step 5 | show mls qos interface [interface-id] Example: Switch# show mls qos interface gigabitethernet 2/1/1 | |
| Step 6 | copy running-config startup-config Example: Switch# copy running-config startup-config |
DSCP Transparency Mode
To configure the switch to modify the DSCP value based on the trust setting or on an ACL by disabling DSCP transparency, use the mls qos rewrite ip dscp global configuration command.
If you disable QoS by using the no mls qos global configuration command, the CoS and DSCP values are not changed (the default QoS setting).
If you enter the no mls qos rewrite ip dscp global configuration command to enable DSCP transparency and then enter the mls qos trust [cos | dscp] interface configuration command, DSCP transparency is still enabled.
Configuring the DSCP Trust State on a Port Bordering Another QoS Domain
If you are administering two separate QoS domains between which you want to implement QoS features for IP traffic, you can configure the switch ports bordering the domains to a DSCP-trusted state. The receiving port accepts the DSCP-trusted value and avoids the classification stage of QoS. If the two domains use different DSCP values, you can configure the DSCP-to-DSCP-mutation map to translate a set of DSCP values to match the definition in the other domain.
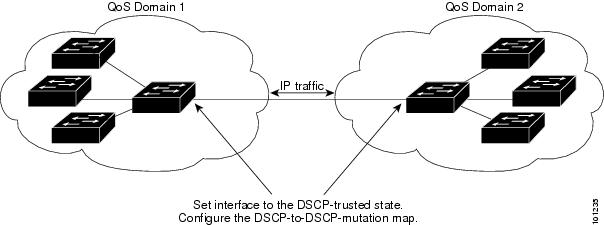
Beginning in privileged EXEC mode, follow these steps to configure the DSCP-trusted state on a port and modify the DSCP-to-DSCP-mutation map. To ensure a consistent mapping strategy across both QoS domains, you must perform this procedure on the ports in both domains.
2.
mls qos map dscp-mutation dscp-mutation-name in-dscp to out-dscp
5.
mls qos dscp-mutation dscp-mutation-name
DETAILED STEPS
| Command or Action | Purpose | |||
|---|---|---|---|---|
| Step 1 | configure
terminal
Example: Switch# configure terminal | |||
| Step 2 | mls qos map dscp-mutation dscp-mutation-name in-dscp to out-dscp Example: Switch(config)# mls qos map dscp-mutation gigabitethernet1/0/2-mutation 10 11 12 13 to 30 | Modifies the DSCP-to-DSCP-mutation map. The default DSCP-to-DSCP-mutation map is a null map, which maps an incoming DSCP value to the same DSCP value. | ||
| Step 3 | interface interface-id Example: Switch(config)# interface gigabitethernet1/0/2 | Specifies the port to be trusted, and enter interface configuration mode. | ||
| Step 4 | mls qos trust dscp Example: Switch(config-if)# mls qos trust dscp | Configures the ingress port as a DSCP-trusted port. By default, the port is not trusted.
| ||
| Step 5 | mls qos dscp-mutation dscp-mutation-name Example: Switch(config-if)# mls qos dscp-mutation gigabitethernet1/0/2-mutation | Applies the map to the specified ingress DSCP-trusted port. For dscp-mutation-name, specify the mutation map name created in Step 2. You can configure multiple DSCP-to-DSCP-mutation maps on an ingress port.
| ||
| Step 6 | end Example: Switch(config-if)# end | |||
| Step 7 | show mls qos maps dscp-mutation Example: Switch# show mls qos maps dscp-mutation | |||
| Step 8 | copy running-config startup-config Example: Switch# copy-running-config startup-config | (Optional) Saves your entries in the configuration file.
|
Configuring a QoS Policy
Configuring a QoS policy typically requires the following tasks:
Classifying traffic into classes
Configuring policies applied to those traffic classes
Attaching policies to ports
These sections describe how to classify, police, and mark traffic. Depending on your network configuration, you must perform one or more of the modules in this section.
- Classifying Traffic by Using ACLs
- Classifying Traffic by Using Class Maps
- Classifying Traffic by Using Class Maps and Filtering IPv6 Traffic
- Classifying, Policing, and Marking Traffic on Physical Ports by Using Policy Maps
- Classifying, Policing, and Marking Traffic on SVIs by Using Hierarchical Policy Maps
- Classifying, Policing, and Marking Traffic by Using Aggregate Policers
Classifying Traffic by Using ACLs
You can classify IP traffic by using IPv4 standard ACLS, IPv4 extended ACLs, or IPv6 ACLs.
You can classify non-IP traffic by using Layer 2 MAC ACLs.
- Creating an IP Standard ACL for IPv4 Traffic
- Creating an IP Extended ACL for IPv4 Traffic
- Creating an IPv6 ACL for IPv6 Traffic
- Creating a Layer 2 MAC ACL for Non-IP Traffic
Creating an IP Standard ACL for IPv4 Traffic
Before you perform this task, determine which access lists you will be using for your QoS configuration.
DETAILED STEPS
| Command or Action | Purpose | |||
|---|---|---|---|---|
| Step 1 | configure terminal Example: Switch# configure terminal | |||
| Step 2 | access-list access-list-number {deny | permit} source [source-wildcard] Example: Switch(config)# access-list 1 permit 192.2.255.0 1.1.1.255 | Creates an IP standard ACL, repeating the command as many times as necessary.
When you create an access list, remember that by default the end of the access list contains an implicit deny statement for everything if it did not find a match before reaching the end.
| ||
| Step 3 | end Example: Switch(config)# end | |||
| Step 4 | show access-lists Example: Switch# show access-lists
| |||
| Step 5 | copy running-config startup-config Example: Switch# copy-running-config startup-config |
Creating an IP Extended ACL for IPv4 Traffic
Before you perform this task, determine which access lists you will be using for your QoS configuration.
2.
access-list
access-list-number
{deny |
permit}
protocol source
source-wildcard destination destination-wildcard
DETAILED STEPS
| Command or Action | Purpose | |||
|---|---|---|---|---|
| Step 1 | configure
terminal
Example: Switch# configure terminal | |||
| Step 2 | access-list
access-list-number
{deny |
permit}
protocol source
source-wildcard destination destination-wildcard
Example: Switch(config)# access-list 100 permit ip any any dscp 32 |
Creates an IP extended ACL, repeating the command as many times as necessary.
When creating an access list, remember that, by default, the end of the access list contains an implicit deny statement for everything if it did not find a match before reaching the end.
| ||
| Step 3 | end
Example: Switch(config)# end | |||
| Step 4 | show
access-lists
Example: Switch# show access-lists
| |||
| Step 5 | copy
running-config startup-config
Example: Switch# copy-running-config
startup-config
|
Creating an IPv6 ACL for IPv6 Traffic
Before you perform this task, determine which access lists you will be using for your QoS configuration.
2.
ipv6 access-list access-list-name
3. {deny | permit} protocol {source-ipv6-prefix/prefix-length | any | host source-ipv6-address} [operator [port-number]] {destination-ipv6-prefix/ prefix-length | any | host destination-ipv6-address} [operator [port-number]] [dscp value] [fragments] [log] [log-input] [routing] [sequence value] [time-range name]
DETAILED STEPS
| Command or Action | Purpose | |||
|---|---|---|---|---|
| Step 1 | configure terminal Example: Switch# configure terminal | |||
| Step 2 | ipv6 access-list access-list-name Example: Switch(config)# ipv6 access-list ipv6_Name_ACL | Creates an IPv6 ACL and enters IPv6 access-list configuration mode. Accesses list names cannot contain a space or quotation mark or begin with a numeric.
| ||
| Step 3 | {deny | permit} protocol
{source-ipv6-prefix/prefix-length | any | host source-ipv6-address}
[operator [port-number]] {destination-ipv6-prefix/ prefix-length | any | host destination-ipv6-address} [operator [port-number]]
[dscp value] [fragments] [log] [log-input] [routing] [sequence value] [time-range name] Example: Switch(config-ipv6-acl)# permit ip host 10::1 host 11::2 host | Enters deny or permit to specify whether to deny or permit the packet if conditions are matched. These are the conditions: For protocol, enter the name or number of an Internet protocol: ahp, esp, icmp, ipv6, pcp, stcp, tcp, or udp, or an integer in the range 0 to 255 representing an IPv6 protocol number.
| ||
| Step 4 | end Example: Switch(config-ipv6-acl)# end | |||
| Step 5 | show ipv6 access-list Example: Switch# show ipv6 access-list | |||
| Step 6 | copy running-config startup-config Example: Switch# copy-running-config startup-config |
Creating a Layer 2 MAC ACL for Non-IP Traffic
Before you perform this task, determine that Layer 2 MAC access lists are required for your QoS configuration.
2.
mac access-list extended name
3. {permit | deny} {host src-MAC-addr mask | any | host dst-MAC-addr | dst-MAC-addr mask} [type mask]
5.
show access-lists [access-list-number | access-list-name]
DETAILED STEPS
| Command or Action | Purpose | |||
|---|---|---|---|---|
| Step 1 | configure terminal Example: Switch# configure terminal | |||
| Step 2 | mac access-list extended name Example: Switch(config)# mac access-list extended maclist1 | Creates a Layer 2 MAC ACL by specifying the name of the list. After entering this command, the mode changes to extended MAC ACL configuration.
| ||
| Step 3 | {permit | deny} {host src-MAC-addr mask | any | host dst-MAC-addr | dst-MAC-addr mask} [type mask] Example: Switch(config-ext-mac1) # permit 0001.0000.0001 0.0.0 0002.0000.0001 0.0.0 Switch(config-ext-mac1) # permit 0001.0000.0002 0.0.0 0002.0000.0002 0.0.0 xns-idp | Specifies the type of traffic to permit or deny if the conditions are matched, entering the command as many times as necessary.
When creating an access list, remember that, by default, the end of the access list contains an implicit deny statement for everything if it did not find a match before reaching the end. | ||
| Step 4 | end Example: Switch(config-ext-mac1)# end | |||
| Step 5 | show access-lists [access-list-number | access-list-name] Example: Switch# show access-lists | |||
| Step 6 | copy running-config startup-config Example: Switch# copy-running-config startup-config |
Classifying Traffic by Using Class Maps
You use the class-map global configuration command to name and to isolate a specific traffic flow (or class) from all other traffic. The class map defines the criteria to use to match against a specific traffic flow to further classify it. Match statements can include criteria such as an ACL, IP precedence values, or DSCP values. The match criterion is defined with one match statement entered within the class-map configuration mode.
 Note | You can also create class maps during policy map creation by using the class policy-map configuration command. |
- access-list access-list-number {deny | permit} source [source-wildcard]
- access-list access-list-number {deny | permit} protocol source [source-wildcard] destination [destination-wildcard]
- ipv6 access-list access-list-name {deny | permit} protocol {source-ipv6-prefix/prefix-length | any | host source-ipv6-address} [operator [port-number]] {destination-ipv6-prefix/ prefix-length | any | host destination-ipv6-address} [operator [port-number]] [dscp value] [fragments] [log] [log-input] [routing] [sequence value] [time-range name]
- mac access-list extended name {permit | deny} {host src-MAC-addr mask | any | host dst-MAC-addr | dst-MAC-addr mask} [type mask]
2.
Use one of the
following:
3.
class-map [match-all |
match-any]
class-map-name
4.
match {access-group
acl-index-or-name |
ip dscp
dscp-list |
ip precedence
ip-precedence-list}
DETAILED STEPS
| Command or Action | Purpose | |||
|---|---|---|---|---|
| Step 1 | configure
terminal
Example: Switch# configure terminal | |||
| Step 2 | Use one of the
following:
Example: Switch(config)# access-list 103 permit ip any any dscp 10 |
Creates an IP standard or extended ACL, an IPv6 ACL for IP traffic, or a Layer 2 MAC ACL for non-IP traffic, repeating the command as many times as necessary. When creating an access list, remember that, by default, the end of the access list contains an implicit deny statement for everything if it did not find a match before reaching the end. | ||
| Step 3 | class-map [match-all |
match-any]
class-map-name
Example: Switch(config)# class-map class1 |
Creates a class map, and enters class-map configuration mode. By default, no class maps are defined.
If neither the match-all or match-any keyword is specified, the default is match-all.
| ||
| Step 4 | match {access-group
acl-index-or-name |
ip dscp
dscp-list |
ip precedence
ip-precedence-list}
Example: Switch(config-cmap)# match ip dscp 10 11 12 |
Defines the match criterion to classify traffic. By default, no match criterion is defined. Only one match criterion per class map is supported, and only one ACL per class map is supported.
| ||
| Step 5 | end
Example: Switch(config-cmap)# end | |||
| Step 6 | show
class-map
Example: Switch# show class-map | |||
| Step 7 | copy
running-config startup-config
Example: Switch# copy-running-config startup-config |
Classifying Traffic by Using Class Maps and Filtering IPv6 Traffic
 Note | IPv6 QoS is not supported on switches running the LAN base feature set. |
To apply the primary match criteria to only IPv4 traffic, use the match protocol command with the ip keyword. To apply the primary match criteria to only IPv6 traffic, use the match protocol command with the ipv6 keyword.
2.
class-map {match-all}
class-map-name
4.
match {ip dscp
dscp-list |
ip precedence
ip-precedence-list}
DETAILED STEPS
| Command or Action | Purpose | |||
|---|---|---|---|---|
| Step 1 | configure
terminal
Example: Switch# configure terminal | |||
| Step 2 | class-map {match-all}
class-map-name
Example: Switch(config)# class-map cm-1 |
Creates a class map, and enters class-map configuration mode. By default, no class maps are defined. When you use the match protocol command, only the match-all keyword is supported. If neither the match-all or match-any keyword is specified, the default is match-all.
| ||
| Step 3 | match protocol [ip
|
ipv6]
Example: Switch(config-cmap)# match protocol ip |
(Optional) Specifies the IP protocol to which the class map applies:
| ||
| Step 4 | match {ip dscp
dscp-list |
ip precedence
ip-precedence-list}
Example: Switch(config-cmap)# match ip dscp 10 |
Defines the match criterion to classify traffic. By default, no match criterion is defined.
| ||
| Step 5 | end
Example: Switch(config-cmap)# end | |||
| Step 6 | show
class-map
Example: Switch# show class-map | |||
| Step 7 | copy
running-config startup-config
Example: Switch# copy-running-config startup-config |
Classifying, Policing, and Marking Traffic on Physical Ports by Using Policy Maps
You can configure a policy map on a physical port that specifies which traffic class to act on. Actions can include trusting the CoS, DSCP, or IP precedence values in the traffic class; setting a specific DSCP or IP precedence value in the traffic class; and specifying the traffic bandwidth limitations for each matched traffic class (policer) and the action to take when the traffic is out of profile (marking).
A policy map also has these characteristics:
-
A policy map can contain multiple class statements, each with different match criteria and policers.
-
A policy map can contain a predefined default traffic class explicitly placed at the end of the map.
-
A separate policy-map class can exist for each type of traffic received through a port.
Follow these guidelines when configuring policy maps on physical ports:
-
You can attach only one policy map per ingress port.
-
If you configure the IP-precedence-to-DSCP map by using the mls qos map ip-prec-dscp dscp1...dscp8 global configuration command, the settings only affect packets on ingress interfaces that are configured to trust the IP precedence value. In a policy map, if you set the packet IP precedence value to a new value by using the set ip precedence new-precedence policy-map class configuration command, the egress DSCP value is not affected by the IP-precedence-to-DSCP map. If you want the egress DSCP value to be different than the ingress value, use the set dscp new-dscp policy-map class configuration command.
-
If you enter or have used the set ip dscp command, the switch changes this command to set dscp in its configuration.
-
You can use the set ip precedence or the set precedence policy-map class configuration command to change the packet IP precedence value. This setting appears as set ip precedence in the switch configuration.
-
You can configure a separate second-level policy map for each class defined for the port. The second-level policy map specifies the police action to take for each traffic class.
-
A policy-map and a port trust state can both run on a physical interface. The policy-map is applied before the port trust state.
-
When you configure a default traffic class by using the class class-default policy-map configuration command, unclassified traffic (traffic that does not meet the match criteria specified in the traffic classes) is treated as the default traffic class (class-default).
2.
class-map [match-all |
match-any]
class-map-name
4.
class [class-map-name |
class-default]
5.
trust [cos |
dscp |
ip-precedence]
6.
set {dscp
new-dscp |
ip precedence
new-precedence}
7.
police
rate-bps burst-byte
[exceed-action {drop |
policed-dscp-transmit}]
11.
service-policy
input
policy-map-name
13.
show policy-map [policy-map-name [class
class-map-name]]
DETAILED STEPS
| Command or Action | Purpose | |||
|---|---|---|---|---|
| Step 1 | configure
terminal
Example: Switch# configure terminal | |||
| Step 2 | class-map [match-all |
match-any]
class-map-name
Example: Switch(config)# class-map ipclass1 |
Creates a class map, and enters class-map configuration mode. By default, no class maps are defined.
If neither the match-all or match-any keyword is specified, the default is match-all. | ||
| Step 3 | policy-map
policy-map-name
Example: Switch(config-cmap)# policy-map flowit |
Creates a policy map by entering the policy map name, and enters policy-map configuration mode. By default, no policy maps are defined. The default behavior of a policy map is to set the DSCP to 0 if the packet is an IP packet and to set the CoS to 0 if the packet is tagged. No policing is performed.
| ||
| Step 4 | class [class-map-name |
class-default]
Example: Switch(config-pmap)# class ipclass1 |
Defines a traffic classification, and enters policy-map class configuration mode. By default, no policy map class-maps are defined. If a traffic class has already been defined by using the class-map global configuration command, specify its name for class-map-name in this command. A class-default traffic class is pre-defined and can be added to any policy. It is always placed at the end of a policy map. With an implied match any included in the class-default class, all packets that have not already matched the other traffic classes will match class-default.
| ||
| Step 5 | trust [cos |
dscp |
ip-precedence]
Example: Switch(config-pmap-c)# trust dscp |
Configures the trust state, which QoS uses to generate a CoS-based or DSCP-based QoS label. This command is mutually exclusive with the set command within the same policy map. If you enter the trust command, go to Step 6. By default, the port is not trusted. If no keyword is specified when the command is entered, the default is dscp. The keywords have these meanings:
| ||
| Step 6 | set {dscp
new-dscp |
ip precedence
new-precedence}
Example: Switch(config-pmap-c)# set dscp 45 |
Classifies IP traffic by setting a new value in the packet.
| ||
| Step 7 | police
rate-bps burst-byte
[exceed-action {drop |
policed-dscp-transmit}]
Example: Switch(config-pmap-c)# police 100000 80000 drop |
Defines a policer for the classified traffic. By default, no policer is defined.
| ||
| Step 8 | exit
Example: Switch(config-pmap-c)# exit | |||
| Step 9 | exit
Example: Switch(config-pmap)# exit | |||
| Step 10 | interface
interface-id
Example: Switch(config)# interface gigabitethernet 2/0/1 |
Specifies the port to attach to the policy map, and enters interface configuration mode. | ||
| Step 11 | service-policy
input
policy-map-name
Example: Switch(config-if)# service-policy input flowit |
Specifies the policy-map name, and applies it to an ingress port. Only one policy map per ingress port is supported.
| ||
| Step 12 | end
Example: Switch(config-if)# end | |||
| Step 13 | show policy-map [policy-map-name [class
class-map-name]]
Example: Switch# show policy-map | |||
| Step 14 | copy
running-config startup-config
Example: Switch# copy-running-config startup-config |
Classifying, Policing, and Marking Traffic on SVIs by Using Hierarchical Policy Maps
You can configure hierarchical policy maps on SVIs, but not on other types of interfaces. Hierarchical policing combines the VLAN- and interface-level policy maps to create a single policy map.
You can configure hierarchical policy maps on SVIs, but not on other types of interfaces. Hierarchical policing combines the VLAN- and interface-level policy maps to create a single policy map.
On an SVI, the VLAN-level policy map specifies which traffic class to act on. Actions can include trusting the CoS, DSCP, or IP precedence values or setting a specific DSCP or IP precedence value in the traffic class. Use the interface-level policy map to specify the physical ports that are affected by individual policers.
You can configure hierarchical policy maps that filter IPv4 and IPv6 traffic.
Follow these guidelines when configuring hierarchical policy maps:
Before configuring a hierarchical policy map, you must enable VLAN-based QoS on the physical ports that are to be specified at the interface level of the policy map.
You can attach only one policy map per ingress port or SVI.
A policy map can contain multiple class statements, each with different match criteria and actions.
A separate policy-map class can exist for each type of traffic received on the SVI.
In a switch stack, you cannot use the match input-interface class-map configuration command to specify interfaces across stack members in a policy-map class.
A policy-map and a port trust state can both run on a physical interface. The policy-map is applied before the port trust state.
If you configure the IP-precedence-to-DSCP map by using the mls qos map ip-prec-dscp dscp1...dscp8 global configuration command, the settings only affect packets on ingress interfaces that are configured to trust the IP precedence value. In a policy map, if you set the packet IP precedence value to a new value by using the set ip precedence new-precedence policy-map class configuration command, the egress DSCP value is not affected by the IP-precedence-to-DSCP map. If you want the egress DSCP value to be different than the ingress value, use the set dscp new-dscp policy-map class configuration command.
If you enter or have used the set ip dscp command, the switch changes this command to set dscp in its configuration. If you enter the set ip dscp command, this setting appears as set dscp in the switch configuration.
You can use the set ip precedence or the set precedence policy-map class configuration command to change the packet IP precedence value. This setting appears as set ip precedence in the switch configuration.
If VLAN-based QoS is enabled, the hierarchical policy map supersedes the previously configured port-based policy map.
The hierarchical policy map is attached to the SVI and affects all traffic in the VLAN. The actions specified in the VLAN-level policy map affect the traffic belonging to the SVI. The police action on the port-level policy map affects the ingress traffic on the affected physical interfaces.
When configuring a hierarchical policy map on trunk ports, the VLAN ranges must not overlap. If the ranges overlap, the actions specified in the policy map affect the incoming and outgoing traffic on the overlapped VLANs.
Aggregate policers are not supported in hierarchical policy maps.
When VLAN-based QoS is enabled, the switch supports VLAN-based features, such as the VLAN map.
You can configure a hierarchical policy map only on the primary VLAN of a private VLAN.
When you enable VLAN-based QoS and configure a hierarchical policy map in a switch stack, these automatic actions occur when the stack configuration changes:
When a new stack master is selected, the stack master reenables and reconfigures these features on all applicable interfaces on the stack master.
When a stack member is added, the stack master reenables and reconfigures these features on all applicable ports on the stack member.
When you merge switch stacks, the new stack master reenables and reconfigures these features on the switches in the new stack.
When the switch stack divides into two or more switch stacks, the stack master in each switch stack re-enables and reconfigures these features on all applicable interfaces on the stack members, including the stack master.
When you configure a default traffic class by using the class class-default policy-map configuration command, unclassified traffic (traffic that does not meet the match criteria specified in the traffic classes) is treated as default traffic class (class-default).
2.
class-map [match-all | match-any] class-map-name
3.
match {access-group acl-index-or-name | ip dscp dscp-list | ip precedence ip-precedence-list}
7.
class-map [match-all | match-any] class-map-name
8.
match input-interface interface-id-list
11.
policy-map policy-map-name
13.
police rate-bps burst-byte [exceed-action {drop | policed-dscp-transmit}]
16.
policy-map policy-map-name
17.
class [class-map-name | class-default]
18.
trust [cos | dscp | ip-precedence]
19.
set {dscp new-dscp | ip precedence new-precedence}
20.
service-policy policy-map-name
24.
service-policy input policy-map-name
26. show policy-map [policy-map-name [class class-map-name]] or show mls qos vlan-based
DETAILED STEPS
| Command or Action | Purpose | |||
|---|---|---|---|---|
| Step 1 | configure
terminal
Example: Switch# configure terminal | |||
| Step 2 | class-map [match-all | match-any] class-map-name Example: Switch(config)# class-map cm-1 | Creates a VLAN-level class map, and enters class-map configuration mode. By default, no class maps are defined.
If neither the match-all or match-any keyword is specified, the default is match-all. Because only one match command per class map is supported, the match-all and match-any keywords function the same. | ||
| Step 3 | match {access-group acl-index-or-name | ip dscp dscp-list | ip precedence ip-precedence-list} Example: Switch(config-cmap)# match ip dscp 10 | Defines the match criterion to classify traffic. By default, no match criterion is defined. Only one match criterion per class map is supported, and only one ACL per class map is supported.
| ||
| Step 4 | match protocol [ip | ipv6] Example: Switch(config-cmap)# match protocol ipv6 | (Optional) Specifies the IP protocol to which the class map applies.
You can use the match protocol command with the match ip dscp or match precedence commands, but not with the match access-group command. | ||
| Step 5 | exit Example: Switch(config-cmap)# exit | |||
| Step 6 | exit Example: Switch(config)# exit | |||
| Step 7 | class-map [match-all | match-any] class-map-name Example: Switch(config)# class-map match-all cm-2 | Creates an interface-level class map, and enters class-map configuration mode. By default, no class maps are defined.
If neither the match-all or match-any keyword is specified, the default is match-all. Because only one match command per class map is supported, the match-all and match-any keywords function the same. | ||
| Step 8 | match input-interface interface-id-list Example: Switch(config-cmap)# match input-interface gigabitethernet 3/0/1-3/0/2 | Specifies the physical ports on which the interface-level class map acts. You can specify up to six ports as follows:
This command can only be used in the child-level policy map and must be the only match condition in the child-level policy map. | ||
| Step 9 | exit Example: Switch(config-cmap)# exit | |||
| Step 10 | exit Example: Switch(config)# exit | |||
| Step 11 | policy-map policy-map-name Example: Switch# policy-map port-plcmap | Creates an interface-level policy map by entering the policy-map name, and enters policy-map configuration mode. By default, no policy maps are defined, and no policing is performed. To delete an existing policy map, use the no policy-map policy-map-name global configuration command. To delete an existing class map, use the no class class-map-name policy-map configuration command. To return to the untrusted state in a policy map, use the no trust policy-map configuration command. To remove an assigned DSCP or IP precedence value, use the no set {dscp new-dscp | ip precedence new-precedence} policy-map configuration command. | ||
| Step 12 | class-map class-map-name Example: Switch(config-pmap)# class cm-interface-1 | Defines an interface-level traffic classification, and enters policy-map configuration mode. By default, no policy-map class-maps are defined. If a traffic class has already been defined by using the class-map global configuration command, specify its name for class-map-name in this command. | ||
| Step 13 | police rate-bps burst-byte [exceed-action {drop | policed-dscp-transmit}] Example: Switch(config-pmap-c)# police 900000 9000 exceed-action policed-dscp-transmit | Defines an individual policer for the classified traffic. By default, no policer is defined.
To remove an existing policer in an interface-level policy map, use the no police rate-bps burst-byte [exceed-action {drop | policed-dscp-transmit}] policy-map configuration command. To remove the hierarchical policy map and port associations, use the no service-policy input policy-map-name interface configuration command. | ||
| Step 14 | exit Example: Switch(config-pmap-c)# exit | |||
| Step 15 | exit Example: Switch(config-pmap)# exit | |||
| Step 16 | policy-map policy-map-name Example: Switch(config)# policy-map vlan-plcmap | Creates a VLAN-level policy map by entering the policy-map name, and enters policy-map configuration mode. By default, no policy maps are defined. The default behavior of a policy map is to set the DSCP to 0 if the packet is an IP packet and to set the CoS to 0 if the packet is tagged. No policing is performed. | ||
| Step 17 | class [class-map-name | class-default] Example: Switch(config-pmap)# class cm-1 | Defines a VLAN-level traffic classification, and enters policy-map class configuration mode. By default, no policy-map class-maps are defined. If a traffic class has already been defined by using the class-map global configuration command, specify its name for class-map-name in this command. A class-default traffic class is pre-defined and can be added to any policy. It is always placed at the end of a policy map. With an implied match any included in the class-default class, all packets that have not already matched the other traffic classes will match class-default. | ||
| Step 18 | trust [cos | dscp | ip-precedence] Example: Switch(config-pmap-c)# trust dscp | Configures the trust state, which QoS uses to generate a CoS-based or DSCP-based QoS label. This command is mutually exclusive with the set command within the same policy map. If you enter the trust command, omit Step 18. By default, the port is not trusted. If no keyword is specified when the command is entered, the default is dscp. The keywords have these meanings:
| ||
| Step 19 | set {dscp new-dscp | ip precedence new-precedence} Example: Switch(config-pmap-c)# set dscp 10 | |||
| Step 20 | service-policy policy-map-name Example: Switch(config-pmap-c)# service-policy port-plcmap-1 | Specifies the interface-level policy-map name (from Step 10) and associate it with the VLAN-level policy map. If the VLAN-level policy map specifies more than one class, each class can have a different service-policy policy-map-name command. | ||
| Step 21 | exit Example: Switch(config-pmap-c)# exit | |||
| Step 22 | exit Example: Switch(config-pmap)# exit | |||
| Step 23 | interface interface-id Example: Switch(config)# interface vlan 10 | Specifies the SVI to which to attach the hierarchical policy map, and enters interface configuration mode. | ||
| Step 24 | service-policy input policy-map-name Example: Switch(config-if)# service-policy input vlan-plcmap | Specifies the VLAN-level policy-map name, and applies it to the SVI. Repeat the previous step and this command to apply the policy map to other SVIs. If the hierarchical VLAN-level policy map has more than one interface-level policy map, all class maps must be configured to the same VLAN-level policy map specified in the service-policy policy-map-name command.
| ||
| Step 25 | end Example: Switch(config-if)# end | |||
| Step 26 | show policy-map [policy-map-name [class class-map-name]]
or
show mls qos vlan-based Example: Switch# show mls qos vlan-based | |||
| Step 27 | copy running-config startup-config Example: Switch# copy-running-config startup-config |
Classifying, Policing, and Marking Traffic by Using Aggregate Policers
By using an aggregate policer, you can create a policer that is shared by multiple traffic classes within the same policy map. However, you cannot use the aggregate policer across different policy maps or ports.
You can configure aggregate policers only in nonhierarchical policy maps on physical ports.
2.
mls qos aggregate-policer aggregate-policer-name rate-bps burst-byte exceed-action {drop | policed-dscp-transmit}
3.
class-map [match-all | match-any] class-map-name
5.
class [class-map-name | class-default]
6.
police aggregate aggregate-policer-name
9.
service-policy input policy-map-name
DETAILED STEPS
| Command or Action | Purpose | |
|---|---|---|
| Step 1 | configure
terminal
Example: Switch# configure terminal | |
| Step 2 | mls qos aggregate-policer aggregate-policer-name rate-bps burst-byte exceed-action {drop | policed-dscp-transmit} Example: Switch(config)# mls qos aggregate-police transmit1 48000 8000 exceed-action policed-dscp-transmit | Defines the policer parameters that can be applied to multiple traffic classes within the same policy map. By default, no aggregate policer is defined.
|
| Step 3 | class-map [match-all | match-any] class-map-name Example: Switch(config)# class-map ipclass1 | |
| Step 4 | policy-map policy-map-name Example: Switch(config-cmap)# policy-map aggflow1 | Creates a policy map by entering the policy map name, and enters policy-map configuration mode. |
| Step 5 | class [class-map-name | class-default] Example: Switch(config-cmap-p)# class ipclass1 | Defines a traffic classification, and enters policy-map class configuration mode. |
| Step 6 | police aggregate aggregate-policer-name Example: Switch(configure-cmap-p)# police aggregate transmit1 | Applies an aggregate policer to multiple classes in the same policy map. For aggregate-policer-name, enter the name specified in Step 2. To remove the specified aggregate policer from a policy map, use the no police aggregate aggregate-policer-name policy map configuration command. To delete an aggregate policer and its parameters, use the no mls qos aggregate-policer aggregate-policer-name global configuration command. |
| Step 7 | exit Example: Switch(configure-cmap-p)# exit | |
| Step 8 | interface interface-id Example: Switch(config)# interface gigabitethernet 2/0/1 | Specifies the port to attach to the policy map, and enters interface configuration mode. |
| Step 9 | service-policy input policy-map-name Example: Switch(config-if)# service-policy input aggflow1 | Specifies the policy-map name, and applies it to an ingress port. |
| Step 10 | end Example: Switch(configure-if)# end | |
| Step 11 | show mls qos aggregate-policer [aggregate-policer-name] Example: Switch# show mls qos aggregate-policer transmit1 | |
| Step 12 | copy running-config startup-config Example: Switch# copy-running-config startup-config |
Configuring DSCP Maps
Configuring the CoS-to-DSCP Map
You use the CoS-to-DSCP map to map CoS values in incoming packets to a DSCP value that QoS uses internally to represent the priority of the traffic.
Beginning in privileged EXEC mode, follow these steps to modify the CoS-to-DSCP map. This procedure is optional.
DETAILED STEPS
| Command or Action | Purpose | |||
|---|---|---|---|---|
| Step 1 | configure
terminal
Example: Switch# configure terminal | |||
| Step 2 | mls qos map
cos-dscp
dscp1...dscp8
Example: Switch(config)# mls qos map cos-dscp 10 15 20 25 30 35 40 45 |
For dscp1...dscp8, enter eight DSCP values that correspond to CoS values 0 to 7. Separate each DSCP value with a space.
| ||
| Step 3 | end
Example: Switch(config)# end | |||
| Step 4 | show mls qos maps
cos-dscp
Example: Switch# show mls qos maps cos-dscp | |||
| Step 5 | copy
running-config startup-config
Example: Switch# copy-running-config startup-config |
Configuring the IP-Precedence-to-DSCP Map
You use the IP-precedence-to-DSCP map to map IP precedence values in incoming packets to a DSCP value that QoS uses internally to represent the priority of the traffic.
Beginning in privileged EXEC mode, follow these steps to modify the IP-precedence-to-DSCP map. This procedure is optional.
DETAILED STEPS
| Command or Action | Purpose | |||
|---|---|---|---|---|
| Step 1 | configure
terminal
Example: Switch# configure terminal | |||
| Step 2 | mls qos map
ip-prec-dscp
dscp1...dscp8
Example: Switch(config)# mls qos map ip-prec-dscp 10 15 20 25 30 35 40 45 |
Modifies the IP-precedence-to-DSCP map. For dscp1...dscp8, enter eight DSCP values that correspond to the IP precedence values 0 to 7. Separate each DSCP value with a space.
| ||
| Step 3 | end
Example: Switch(config)# end | |||
| Step 4 | show mls qos maps
ip-prec-dscp
Example: Switch# show mls qos maps ip-prec-dscp
| |||
| Step 5 | copy
running-config startup-config
Example: Switch# copy-running-config startup-config |
Configuring the Policed-DSCP Map
You use the policed-DSCP map to mark down a DSCP value to a new value as the result of a policing and marking action.
The default policed-DSCP map is a null map, which maps an incoming DSCP value to the same DSCP value.
Beginning in privileged EXEC mode, follow these steps to modify the policed-DSCP map. This procedure is optional.
DETAILED STEPS
| Command or Action | Purpose | |||
|---|---|---|---|---|
| Step 1 | configure terminal Example: Switch# configure terminal | |||
| Step 2 | mls qos map policed-dscp dscp-list to mark-down-dscp Example: Switch(config)# mls qos map policed-dscp 50 51 52 53 54 55 56 57 to 0 | Modifies the policed-DSCP map.
| ||
| Step 3 | end Example: Switch(config)# end | |||
| Step 4 | show mls qos maps policed-dscp Example: Switch(config)# show mls qos maps policed-dscp | |||
| Step 5 | copy running-config startup-config Example: Switch# |
Configuring the DSCP-to-CoS Map
You use the DSCP-to-CoS map to generate a CoS value, which is used to select one of the four egress queues.
Beginning in privileged EXEC mode, follow these steps to modify the DSCP-to-CoS map. This procedure is optional.
DETAILED STEPS
| Command or Action | Purpose | |||
|---|---|---|---|---|
| Step 1 | configure
terminal
Example: Switch# configure terminal | |||
| Step 2 | mls qos map
dscp-cos
dscp-list
to
cos
Example: Switch# mls qos map dscp-cos 0 8 16 24 32 40 48 50 to 0 |
The DSCP range is 0 to 63; the CoS range is 0 to 7.
| ||
| Step 3 | end
Example: Switch(config)# end | |||
| Step 4 | show mls qos maps
dscp-to-cos
Example: Switch# show mls qos maps dscp-to-cos | |||
| Step 5 | copy
running-config startup-config
Example: Switch# copy-running-config startup-config |
Configuring the DSCP-to-DSCP-Mutation Map
If two QoS domains have different DSCP definitions, use the DSCP-to-DSCP-mutation map to translate one set of DSCP values to match the definition of another domain. You apply the DSCP-to-DSCP-mutation map to the receiving port (ingress mutation) at the boundary of a QoS administrative domain.
With ingress mutation, the new DSCP value overwrites the one in the packet, and QoS applies the new value to the packet. The switch sends the packet out the port with the new DSCP value.
You can configure multiple DSCP-to-DSCP-mutation maps on an ingress port. The default DSCP-to-DSCP-mutation map is a null map, which maps an incoming DSCP value to the same DSCP value.
Beginning in privileged EXEC mode, follow these steps to modify the DSCP-to-DSCP-mutation map. This procedure is optional.
2.
mls qos map dscp-mutation dscp-mutation-name in-dscp to out-dscp
5.
mls qos dscp-mutation dscp-mutation-name
DETAILED STEPS
| Command or Action | Purpose | |||
|---|---|---|---|---|
| Step 1 | configure
terminal
Example: Switch# configure terminal | |||
| Step 2 | mls qos map dscp-mutation dscp-mutation-name in-dscp to out-dscp Example: Switch(config)# mls qos map dscp-mutation mutation1 1 2 3 4 5 6 7 to 0 | Modifies the DSCP-to-DSCP-mutation map.
| ||
| Step 3 | interface interface-id Example: Switch(config)# interface gigabitethernet1/0/1 | Specifies the port to which to attach the map, and enters interface configuration mode. | ||
| Step 4 | mls qos trust dscp Example: Switch(config-if)# mls qos trust dscp | Configures the ingress port as a DSCP-trusted port. By default, the port is not trusted. | ||
| Step 5 | mls qos dscp-mutation dscp-mutation-name Example: Switch(config-if)# mls qos dscp-mutation mutation1 | Applies the map to the specified ingress DSCP-trusted port. For dscp-mutation-name, enter the mutation map name specified in Step 2. | ||
| Step 6 | end Example: Switch(config-if)# end | |||
| Step 7 | show mls qos maps dscp-mutation Example: Switch# show mls qos maps dscp-mutation | |||
| Step 8 | copy running-config startup-config Example: Switch# copy-running-config startup-config |
Configuring Egress Queue Characteristics
Depending on the complexity of your network and your QoS solution, you might need to perform all of the tasks in the following modules. You need to make decisions about these characteristics:
Which packets are mapped by DSCP or CoS value to each queue and threshold ID?
What drop percentage thresholds apply to the queue-set (four egress queues per port), and how much reserved and maximum memory is needed for the traffic type?
How much of the fixed buffer space is allocated to the queue-set?
How often should the egress queues be serviced and which technique (shaped, shared, or both) should be used?
- Configuration Guidelines
- Allocating Buffer Space to and Setting WTD Thresholds for an Egress Queue Set
- Mapping DSCP or CoS Values to an Egress Queue and to a Threshold ID
- Configuring SRR Shaped Weights on Egress Queues
- Configuring SRR Shared Weights on Egress Queues
- Configuring the Egress Expedite Queue
- Limiting the Bandwidth on an Egress Interface
Configuration Guidelines
Follow these guidelines when the expedite queue is enabled or the egress queues are serviced based on their SRR weights:
If the egress expedite queue is enabled, it overrides the SRR shaped and shared weights for queue 1.
If the egress expedite queue is disabled and the SRR shaped and shared weights are configured, the shaped mode overrides the shared mode for queue 1, and SRR services this queue in shaped mode.
If the egress expedite queue is disabled and the SRR shaped weights are not configured, SRR services this queue in shared mode.
Allocating Buffer Space to and Setting WTD Thresholds for an Egress Queue Set
You can guarantee the availability of buffers, set WTD thresholds, and configure the maximum allocation for a queue set by using the mls qos queue-set output qset-id threshold queue-id drop-threshold1 drop-threshold2 reserved-threshold maximum-threshold global configuration command.
Each threshold value is a percentage of the queue’s allocated buffers, which you specify by using the mls qos queue-set output qset-id buffers allocation1 ... allocation4 global configuration command. The queues use WTD to support distinct drop percentages for different traffic classes.
 Note | The egress queue default settings are suitable for most situations. You should change them only when you have a thorough understanding of the egress queues and if these settings do not meet your QoS solution. |
Beginning in privileged EXEC mode, follow these steps to configure the memory allocation and to drop thresholds for a queue set. This procedure is optional.
2.
mls qos srr-queue output queues 8
3.
mls qos queue-set output qset-id buffers allocation1 ... allocation8
4.
mls qos queue-set output qset-id threshold queue-id drop-threshold1 drop-threshold2 reserved-threshold maximum-threshold
DETAILED STEPS
| Command or Action | Purpose | |||
|---|---|---|---|---|
| Step 1 | configure
terminal
Example: Switch# configure terminal | |||
| Step 2 | mls qos srr-queue output queues 8 Example:
Switch(config)# mls qos srr-queue output queues 8
| (Optional) The switch supports 4 egress queues by default, although you can enable a total of 8 egress queues. Use the optional mls qos srr-queue output queues 8 command to enable the additional 4 egress queues. Once 8 queue support is enabled, you can then proceed to configure the additional 4 queues. Any existing egress queue configuration commands are then modified to support the additional queue parameters.
| ||
| Step 3 | mls qos queue-set output qset-id buffers allocation1 ... allocation8 Example: Switch(config)# mls qos queue-set output 2 buffers 40 20 20 20 10 10 10 10 | Allocates buffers to a queue set. By default, all allocation values are equally mapped among the four queues (25, 25, 25, 25). Each queue has 1/4 of the buffer space. When eight egress queues are configured, then by default 30 percent of the total buffer space is allocated to queue 2 and 10 percent (each) to queues 1,3,4,5,6,7, and 8. If you enabled 8 egress queues as described in Step 2 above, then the following applies:
Allocate buffers according to the importance of the traffic; for example, give a large percentage of the buffer to the queue with the highest-priority traffic.
| ||
| Step 4 | mls qos queue-set output qset-id threshold queue-id drop-threshold1 drop-threshold2 reserved-threshold maximum-threshold Example: Switch(config)# mls qos queue-set output 2 threshold 2 40 60 80 200 | Configures the WTD thresholds, guarantee the availability of buffers, and configures the maximum memory allocation for the queue set (four egress queues per port). By default, the WTD thresholds for queues 1, 3, and 4 are set to 100 percent. The thresholds for queue 2 are set to 200 percent. The reserved thresholds for queues 1, 2, 3, and 4 are set to 50 percent. The maximum thresholds for all queues are set to 400 percent by default. If you enabled 8 egress queues as described in Step 2 above, then the following applies:
| ||
| Step 5 | interface interface-id Example: Switch(config)# interface gigabitethernet1/0/1 | Specifies the port of the outbound traffic, and enters interface configuration mode. | ||
| Step 6 | queue-set qset-id Example: Switch(config-id)# queue-set 2 |
For qset-id, enter the ID of the queue set specified in Step 2. The range is 1 to 2. The default is 1. | ||
| Step 7 | end Example: Switch(config-id)# end | |||
| Step 8 | show mls qos interface [interface-id] buffers Example: Switch# show mls qos interface buffers | |||
| Step 9 | copy running-config startup-config Example: Switch# copy-running-config startup-config | (Optional) Saves your entries in the configuration file. To return to the default setting, use the no mls qos queue-set output qset-id buffers global configuration command. To return to the default WTD threshold percentages, use the no mls qos queue-set output qset-id threshold [queue-id] global configuration command. |
Mapping DSCP or CoS Values to an Egress Queue and to a Threshold ID
You can prioritize traffic by placing packets with particular DSCPs or costs of service into certain queues and adjusting the queue thresholds so that packets with lower priorities are dropped.
 Note | The egress queue default settings are suitable for most situations. You should change them only when you have a thorough understanding of egress queues and if these settings do not meet your QoS solution. |
Beginning in privileged EXEC mode, follow these steps to map DSCP or CoS values to an egress queue and to a threshold ID. This procedure is optional.
DETAILED STEPS
| Command or Action | Purpose | |||
|---|---|---|---|---|
| Step 1 | configure terminal Example: Switch# configure terminal | |||
| Step 2 | Use one of the following:
Example: Switch(config)# mls qos srr-queue output dscp-map queue 1 threshold 2 10 11 | Maps DSCP or CoS values to an egress queue and to a threshold ID. By default, DSCP values 0–15 are mapped to queue 2 and threshold 1. DSCP values 16–31 are mapped to queue 3 and threshold 1. DSCP values 32–39 and 48–63 are mapped to queue 4 and threshold 1. DSCP values 40–47 are mapped to queue 1 and threshold 1. By default, CoS values 0 and 1 are mapped to queue 2 and threshold 1. CoS values 2 and 3 are mapped to queue 3 and threshold 1. CoS values 4, 6, and 7 are mapped to queue 4 and threshold 1. CoS value 5 is mapped to queue 1 and threshold 1.
| ||
| Step 3 | end Example: Switch(config)# end | |||
| Step 4 | show mls qos maps Example: Switch# show mls qos maps |
The DSCP output queue threshold map appears as a matrix. The d1 column specifies the most-significant digit of the DSCP number; the d2 row specifies the least-significant digit in the DSCP number. The intersection of the d1 and the d2 values provides the queue ID and threshold ID; for example, queue 2 and threshold 1 (02-01). The CoS output queue threshold map shows the CoS value in the top row and the corresponding queue ID and threshold ID in the second row; for example, queue 2 and threshold 2 (2-2). | ||
| Step 5 | copy running-config startup-config Example: Switch# copy-running-config startup-config | (Optional) Saves your entries in the configuration file. To return to the default DSCP output queue threshold map or the default CoS output queue threshold map, use the no mls qos srr-queue output dscp-map or the no mls qos srr-queue output cos-map global configuration command. |
Configuring SRR Shaped Weights on Egress Queues
You can specify how much of the available bandwidth is allocated to each queue. The ratio of the weights is the ratio of frequency in which the SRR scheduler sends packets from each queue.
You can configure the egress queues for shaped or shared weights, or both. Use shaping to smooth bursty traffic or to provide a smoother output over time.
Beginning in privileged EXEC mode, follow these steps to assign the shaped weights and to enable bandwidth shaping on the four egress queues mapped to a port. This procedure is optional.
3.
srr-queue bandwidth shape weight1 weight2 weight3 weight4
DETAILED STEPS
| Command or Action | Purpose | |
|---|---|---|
| Step 1 | configure
terminal
Example: Switch# configure terminal | |
| Step 2 | interface interface-id Example: Switch(config)# interface gigabitethernet2/0/1 | Specifies the port of the outbound traffic, and enters interface configuration mode. |
| Step 3 | srr-queue bandwidth shape weight1 weight2 weight3 weight4 Example: Switch(config-if)# srr-queue bandwidth shape 8 0 0 0 | Assigns SRR weights to the egress queues. By default, weight1 is set to 25; weight2, weight3, and weight4 are set to 0, and these queues are in shared mode. For weight1 weight2 weight3 weight4, enter the weights to control the percentage of the port that is shaped. The inverse ratio (1/weight) controls the shaping bandwidth for this queue. Separate each value with a space. The range is 0 to 65535. If you configure a weight of 0, the corresponding queue operates in shared mode. The weight specified with the srr-queue bandwidth shape command is ignored, and the weights specified with the srr-queue bandwidth share interface configuration command for a queue come into effect. When configuring queues in the same queue-set for both shaping and sharing, make sure that you configure the lowest number queue for shaping. The shaped mode overrides the shared mode. To return to the default setting, use the no srr-queue bandwidth shape interface configuration command. |
| Step 4 | end Example: Switch(config-if)# end | |
| Step 5 | show mls qos interface interface-id queueing Example: Switch# show mls qos interface interface-id queuing | |
| Step 6 | copy running-config startup-config Example: Switch# copy running-config startup-config | (Optional) Saves your entries in the configuration file. To return to the default setting, use the no srr-queue bandwidth shape interface configuration command. |
Configuring SRR Shared Weights on Egress Queues
In shared mode, the queues share the bandwidth among them according to the configured weights. The bandwidth is guaranteed at this level but not limited to it. For example, if a queue empties and does not require a share of the link, the remaining queues can expand into the unused bandwidth and share it among them. With sharing, the ratio of the weights controls the frequency of dequeuing; the absolute values are meaningless.
 Note | The egress queue default settings are suitable for most situations. You should change them only when you have a thorough understanding of the egress queues and if these settings do not meet your QoS solution. |
Beginning in privileged EXEC mode, follow these steps to assign the shared weights and to enable bandwidth sharing on the four egress queues mapped to a port. This procedure is optional.
3.
srr-queue bandwidth share weight1 weight2 weight3 weight4
DETAILED STEPS
| Command or Action | Purpose | |
|---|---|---|
| Step 1 | configure terminal Example: Switch# configure terminal | |
| Step 2 | interface interface-id Example: Switch(config)# interface gigabitethernet2/0/1 | Specifies the port of the outbound traffic, and enters interface configuration mode. |
| Step 3 | srr-queue bandwidth share weight1 weight2 weight3 weight4 Example: Switch(config-id)# srr-queue bandwidth share 1 2 3 4 | Assigns SRR weights to the egress queues. By default, all four weights are 25 (1/4 of the bandwidth is allocated to each queue). For weight1 weight2 weight3 weight4, enter the weights to control the ratio of the frequency in which the SRR scheduler sends packets. Separate each value with a space. The range is 1 to 255. To return to the default setting, use the no srr-queue bandwidth share interface configuration command. |
| Step 4 | end Example: Switch(config-id)# end | |
| Step 5 | show mls qos interface interface-id queueing Example: Switch# show mls qos interface interface_id queuing | |
| Step 6 | copy running-config startup-config Example: Switch# copy-running-config startup-config | (Optional) Saves your entries in the configuration file. To return to the default setting, use the no srr-queue bandwidth share interface configuration command. |
Configuring the Egress Expedite Queue
You can ensure that certain packets have priority over all others by queuing them in the egress expedite queue. SRR services this queue until it is empty before servicing the other queues.
Beginning in privileged EXEC mode, follow these steps to enable the egress expedite queue. This procedure is optional.
DETAILED STEPS
| Command or Action | Purpose | |||
|---|---|---|---|---|
| Step 1 | configure terminal Example: Switch# configure terminal | |||
| Step 2 | mls qos Example: Switch(config)# mls qos | |||
| Step 3 | interface interface-id Example: Switch(config)# interface gigabitethernet1/0/1 | Specifies the egress port, and enters interface configuration mode. | ||
| Step 4 | priority-queue out Example: Switch(config-if)# priority-queue out | Enables the egress expedite queue, which is disabled by default. When you configure this command, the SRR weight and queue size ratios are affected because there is one fewer queue participating in SRR. This means that weight1 in the srr-queue bandwidth shape or the srr-queue bandwidth share command is ignored (not used in the ratio calculation).
| ||
| Step 5 | end Example: Switch(config-if)# end | |||
| Step 6 | show running-config Example: Switch# show running-config | |||
| Step 7 | copy running-config startup-config Example: Switch# copy running-config startup-config | (Optional) Saves your entries in the configuration file. To disable the egress expedite queue, use the no priority-queue out interface configuration command. |
Limiting the Bandwidth on an Egress Interface
You can limit the bandwidth on an egress port. For example, if a customer pays only for a small percentage of a high-speed link, you can limit the bandwidth to that amount.
 Note | The egress queue default settings are suitable for most situations. You should change them only when you have a thorough understanding of the egress queues and if these settings do not meet your QoS solution. |
Beginning in privileged EXEC mode, follow these steps to limit the bandwidth on an egress port. This procedure is optional.
DETAILED STEPS
| Command or Action | Purpose | |||
|---|---|---|---|---|
| Step 1 | configure terminal Example: Switch# configure terminal | |||
| Step 2 | interface interface-id Example: Switch(config)# interface gigabitethernet2/0/1 | Specifies the port to be rate-limited, and enters interface configuration mode. | ||
| Step 3 | srr-queue bandwidth limit weight1 Example: Switch(config-if)# srr-queue bandwidth limit 80 | Specifies the percentage of the port speed to which the port should be limited. The range is 10 to 90. By default, the port is not rate-limited and is set to 100 percent.
| ||
| Step 4 | end Example: Switch(config-if)# end | |||
| Step 5 | show mls qos interface [interface-id] queueing Example: Switch# show mls qos interface interface_id queueing | |||
| Step 6 | copy running-config startup-config Example: Switch# copy-running-config startup-config | (Optional) Saves your entries in the configuration file. To return to the default setting, use the no srr-queue bandwidth limit interface configuration command. |
Monitoring Standard QoS
Command |
Description |
|---|---|
Displays QoS class maps, which define the match criteria to classify traffic. |
|
show mls qos interface [interface-id] [buffers | policers | queueing | statistics] |
Displays QoS information at the port level, including the buffer allocation, which ports have configured policers, the queueing strategy, and the ingress and egress statistics. |
show mls qos maps [cos-dscp | |cos-output-q | dscp-cos | |dscp-mutation dscp-mutation-name | dscp-output-q | ip-prec-dscp | policed-dscp] |
|
Displays QoS policy maps, which define classification criteria for incoming traffic. Do not use the show policy-map interface privileged EXEC command to display classification information for incoming traffic. The control-plane and interface keywords are not supported, and the statistics shown in the display should be ignored. |
|
Configuration Examples for QoS
Example: Configuring Port to the DSCP-Trusted State and Modifying the DSCP-to-DSCP-Mutation Map
This example shows how to configure a port to the DSCP-trusted state and to modify the DSCP-to-DSCP-mutation map (named gi1/0/2-mutation) so that incoming DSCP values 10 to 13 are mapped to DSCP 30:
Switch(config)# mls qos map dscp-mutation gigabitethernet1/0/2-mutation 10 11 12 13 to 30 Switch(config)# interface gigabitethernet1/0/2 Switch(config-if)# mls qos trust dscp Switch(config-if)# mls qos dscp-mutation gigabitethernet1/0/2-mutation Switch(config-if)# end
Examples: Classifying Traffic by Using ACLs
This example shows how to allow access for only those hosts on the three specified networks. The wildcard bits apply to the host portions of the network addresses. Any host with a source address that does not match the access list statements is rejected.
Switch(config)# access-list 1 permit 192.5.255.0 0.0.0.255 Switch(config)# access-list 1 permit 128.88.0.0 0.0.255.255 Switch(config)# access-list 1 permit 36.0.0.0 0.0.0.255 ! (Note: all other access implicitly denied)
This example shows how to create an ACL that permits IP traffic from any source to any destination that has the DSCP value set to 32:
Switch(config)# access-list 100 permit ip any any dscp 32
This example shows how to create an ACL that permits IP traffic from a source host at 10.1.1.1 to a destination host at 10.1.1.2 with a precedence value of 5:
Switch(config)# access-list 100 permit ip host 10.1.1.1 host 10.1.1.2 precedence 5
This example shows how to create an ACL that permits PIM traffic from any source to a destination group address of 224.0.0.2 with a DSCP set to 32:
Switch(config)# access-list 102 permit pim any 224.0.0.2 dscp 32
This example shows how to create an ACL that permits IPv6 traffic from any source to any destination that has the DSCP value set to 32:
Switch(config)# ipv6 access-list 100 permit ip any any dscp 32
This example shows how to create an ACL that permits IPv6 traffic from a source host at 10.1.1.1 to a destination host at 10.1.1.2 with a precedence value of 5:
Switch(config)# ipv6 access-list ipv6_Name_ACL permit ip host 10::1 host 10.1.1.2 precedence 5
This example shows how to create a Layer 2 MAC ACL with two permit statements. The first statement allows traffic from the host with MAC address 0001.0000.0001 to the host with MAC address 0002.0000.0001. The second statement allows only Ethertype XNS-IDP traffic from the host with MAC address 0001.0000.0002 to the host with MAC address 0002.0000.0002.
Switch(config)# mac access-list extended maclist1 Switch(config-ext-macl)# permit 0001.0000.0001 0.0.0 0002.0000.0001 0.0.0 Switch(config-ext-macl)# permit 0001.0000.0002 0.0.0 0002.0000.0002 0.0.0 xns-idp ! (Note: all other access implicitly denied)
Examples: Classifying Traffic by Using Class Maps
This example shows how to configure the class map called class1. The class1 has one match criterion, which is access list 103. It permits traffic from any host to any destination that matches a DSCP value of 10.
Switch(config)# access-list 103 permit ip any any dscp 10 Switch(config)# class-map class1 Switch(config-cmap)# match access-group 103 Switch(config-cmap)# end Switch#
This example shows how to create a class map called class2, which matches incoming traffic with DSCP values of 10, 11, and 12.
Switch(config)# class-map class2 Switch(config-cmap)# match ip dscp 10 11 12 Switch(config-cmap)# end Switch#
This example shows how to create a class map called class3, which matches incoming traffic with IP-precedence values of 5, 6, and 7:
Switch(config)# class-map class3 Switch(config-cmap)# match ip precedence 5 6 7 Switch(config-cmap)# end Switch#
This example shows how to configure a class map to match IP DSCP and IPv6:
Switch(config)# Class-map cm-1 Switch(config-cmap)# match ip dscp 10 Switch(config-cmap)# match protocol ipv6 Switch(config-cmap)# exit Switch(config)# Class-map cm-2 Switch(config-cmap)# match ip dscp 20 Switch(config-cmap)# match protocol ip Switch(config-cmap)# exit Switch(config)# Policy-map pm1 Switch(config-pmap)# class cm-1 Switch(config-pmap-c)# set dscp 4 Switch(config-pmap-c)# exit Switch(config-pmap)# class cm-2 Switch(config-pmap-c)# set dscp 6 Switch(config-pmap-c)# exit Switch(config-pmap)# exit Switch(config)# interface G1/0/1 Switch(config-if)# service-policy input pm1
This example shows how to configure a class map that applies to both IPv4 and IPv6 traffic:
Switch(config)# ip access-list 101 permit ip any any Switch(config)# ipv6 access-list ipv6-any permit ip any any Switch(config)# Class-map cm-1 Switch(config-cmap)# match access-group 101 Switch(config-cmap)# exit Switch(config)# class-map cm-2 Switch(config-cmap)# match access-group name ipv6-any Switch(config-cmap)# exit Switch(config)# Policy-map pm1 Switch(config-pmap)# class cm-1 Switch(config-pmap-c)# set dscp 4 Switch(config-pmap-c)# exit Switch(config-pmap)# class cm-2 Switch(config-pmap-c)# set dscp 6 Switch(config-pmap-c)# exit Switch(config-pmap)# exit Switch(config)# interface G0/1 Switch(config-if)# switch mode access Switch(config-if)# service-policy input pm1
Examples: Classifying, Policing, and Marking Traffic on Physical Ports Using Policy Maps
This example shows how to create a policy map and attach it to an ingress port. In the configuration, the IP standard ACL permits traffic from network 10.1.0.0. For traffic matching this classification, the DSCP value in the incoming packet is trusted. If the matched traffic exceeds an average traffic rate of 48000 b/s and a normal burst size of 8000 bytes, its DSCP is marked down (based on the policed-DSCP map) and sent:
Switch(config)# access-list 1 permit 10.1.0.0 0.0.255.255 Switch(config)# class-map ipclass1 Switch(config-cmap)# match access-group 1 Switch(config-cmap)# exit Switch(config)# policy-map flow1t Switch(config-pmap)# class ipclass1 Switch(config-pmap-c)# trust dscp Switch(config-pmap-c)# police 1000000 8000 exceed-action policed-dscp-transmit Switch(config-pmap-c)# exit Switch(config-pmap)# exit Switch(config)# interface gigabitethernet2/0/1 Switch(config-if)# service-policy input flow1t
This example shows how to create a Layer 2 MAC ACL with two permit statements and attach it to an ingress port. The first permit statement allows traffic from the host with MAC address 0001.0000.0001 destined for the host with MAC address 0002.0000.0001. The second permit statement allows only Ethertype XNS-IDP traffic from the host with MAC address 0001.0000.0002 destined for the host with MAC address 0002.0000.0002.
Switch(config)# mac access-list extended maclist1 Switch(config-ext-mac)# permit 0001.0000.0001 0.0.0 0002.0000.0001 0.0.0 Switch(config-ext-mac)# permit 0001.0000.0002 0.0.0 0002.0000.0002 0.0.0 xns-idp Switch(config-ext-mac)# exit Switch(config)# mac access-list extended maclist2 Switch(config-ext-mac)# permit 0001.0000.0003 0.0.0 0002.0000.0003 0.0.0 Switch(config-ext-mac)# permit 0001.0000.0004 0.0.0 0002.0000.0004 0.0.0 aarp Switch(config-ext-mac)# exit Switch(config)# class-map macclass1 Switch(config-cmap)# match access-group maclist1 Switch(config-cmap)# exit Switch(config)# policy-map macpolicy1 Switch(config-pmap)# class macclass1 Switch(config-pmap-c)# set dscp 63 Switch(config-pmap-c)# exit Switch(config-pmap)# class macclass2 maclist2 Switch(config-pmap-c)# set dscp 45 Switch(config-pmap-c)# exit Switch(config-pmap)# exit Switch(config)# interface gigabitethernet1/0/1 Switch(config-if)# mls qos trust cos Switch(config-if)# service-policy input macpolicy1
This example shows how to create a class map that applies to both IPv4 and IPv6 traffic with the default class applied to unclassified traffic:
Switch(config)# ip access-list 101 permit ip any any Switch(config)# ipv6 access-list ipv6-any permit ip any any Switch(config)# class-map cm-1 Switch(config-cmap)# match access-group 101 Switch(config-cmap)# exit Switch(config)# class-map cm-2 Switch(config-cmap)# match access-group name ipv6-any Switch(config-cmap)# exit Switch(config)# policy-map pm1 Switch(config-pmap)# class cm-1 Switch(config-pmap-c)# set dscp 4 Switch(config-pmap-c)# exit Switch(config-pmap)# class cm-2 Switch(config-pmap-c)# set dscp 6 Switch(config-pmap-c)# exit Switch(config-pmap)# class class-default Switch(config-pmap-c)# set dscp 10 Switch(config-pmap-c)# exit Switch(config-pmap)# exit Switch(config)# interface G0/1 Switch(config-if)# switch mode access Switch(config-if)# service-policy input pm1
Examples: Classifying, Policing, and Marking Traffic on SVIs by Using Hierarchical Policy Maps
This example shows how to create a hierarchical policy map:
Switch> enable Switch# configure terminal Enter configuration commands, one per line. End with CNTL/Z. Switch(config)# access-list 101 permit ip any any Switch(config)# class-map cm-1 Switch(config-cmap)# match access 101 Switch(config-cmap)# exit Switch(config)# exit Switch# Switch#
This example shows how to attach the new map to an SVI:
Switch# configure terminal Enter configuration commands, one per line. End with CNTL/Z. Switch(config)# class-map cm-interface-1 Switch(config-cmap)# match input gigabitethernet3/0/1 - gigabitethernet3/0/2 Switch(config-cmap)# exit Switch(config)# policy-map port-plcmap Switch(config-pmap)# class cm-interface-1 Switch(config-pmap-c)# police 900000 9000 exc policed-dscp-transmit Switch(config-pmap-c)# exit Switch(config-pmap)# exit Switch(config)# policy-map vlan-plcmap Switch(config-pmap)# class cm-1 Switch(config-pmap-c)# set dscp 7 Switch(config-pmap-c)# service-policy port-plcmap-1 Switch(config-pmap-c)# exit Switch(config-pmap)# class cm-2 Switch(config-pmap-c)# service-policy port-plcmap-1 Switch(config-pmap-c)# set dscp 10 Switch(config-pmap)# exit Switch(config-pmap)# class cm-3 Switch(config-pmap-c)# service-policy port-plcmap-2 Switch(config-pmap-c)# set dscp 20 Switch(config-pmap)# exit Switch(config-pmap)# class cm-4 Switch(config-pmap-c)# trust dscp Switch(config-pmap)# exit Switch(config)# interface vlan 10 Switch(config-if)# service-policy input vlan-plcmap Switch(config-if)# exit Switch(config)# exit Switch#
This example shows that when a child-level policy map is attached below a class, an action must be specified for the class:
Switch(config)# policy-map vlan-plcmap Switch(config-pmap)# class cm-5 Switch(config-pmap-c)# set dscp 7 Switch(config-pmap-c)# service-policy port-plcmap-1
This example shows how to configure a class map to match IP DSCP and IPv6:
Switch(config)# class-map cm-1 Switch(config-cmap)# match ip dscp 10 Switch(config-cmap)# match protocol ipv6 Switch(config-cmap)# exit Switch(config)# class-map cm-2 Switch(config-cmap)# match ip dscp 20 Switch(config-cmap)# match protocol ip Switch(config-cmap)# exit Switch(config)# policy-map pm1 Switch(config-pmap)# class cm-1 Switch(config-pmap-c)# set dscp 4 Switch(config-pmap-c)# exit Switch(config-pmap)# class cm-2 Switch(config-pmap-c)# set dscp 6 Switch(config-pmap-c)# exit Switch(config-pmap)# exit Switch(config)# interface G1/0/1 Switch(config-if)# service-policy input pm1
This example shows how to configure default traffic class to a policy map:
Switch# configure terminal Switch(config)# class-map cm-3 Switch(config-cmap)# match ip dscp 30 Switch(config-cmap)# match protocol ipv6 Switch(config-cmap)# exit Switch(config)# class-map cm-4 Switch(config-cmap)# match ip dscp 40 Switch(config-cmap)# match protocol ip Switch(config-cmap)# exit Switch(config)# policy-map pm3 Switch(config-pmap)# class class-default Switch(config-pmap)# set dscp 10 Switch(config-pmap-c)# exit Switch(config-pmap)# class cm-3 Switch(config-pmap-c) set dscp 4 Switch(config-pmap-c)# exit Switch(config-pmap)# class cm-4 Switch(config-pmap-c)# trust cos Switch(config-pmap-c)# exit Switch(config-pmap)# exit
This example shows how the default traffic class is automatically placed at the end of policy-map pm3 even though class-default was configured first:
Switch# show policy-map pm3 Policy Map pm3 Class cm-3 set dscp 4 Class cm-4 trust cos Class class-default police 8000 80000 exceed-action drop Switch#
Examples: Classifying, Policing, and Marking Traffic by Using Aggregate Policers
This example shows how to create an aggregate policer and attach it to multiple classes within a policy map. In the configuration, the IP ACLs permit traffic from network 10.1.0.0 and from host 11.3.1.1. For traffic coming from network 10.1.0.0, the DSCP in the incoming packets is trusted. For traffic coming from host 11.3.1.1, the DSCP in the packet is changed to 56. The traffic rate from the 10.1.0.0 network and from host 11.3.1.1 is policed. If the traffic exceeds an average rate of 48000 b/s and a normal burst size of 8000 bytes, its DSCP is marked down (based on the policed-DSCP map) and sent. The policy map is attached to an ingress port.
Switch(config)# access-list 1 permit 10.1.0.0 0.0.255.255 Switch(config)# access-list 2 permit 11.3.1.1 Switch(config)# mls qos aggregate-police transmit1 48000 8000 exceed-action policed-dscp-transmit Switch(config)# class-map ipclass1 Switch(config-cmap)# match access-group 1 Switch(config-cmap)# exit Switch(config)# class-map ipclass2 Switch(config-cmap)# match access-group 2 Switch(config-cmap)# exit Switch(config)# policy-map aggflow1 Switch(config-pmap)# class ipclass1 Switch(config-pmap-c)# trust dscp Switch(config-pmap-c)# police aggregate transmit1 Switch(config-pmap-c)# exit Switch(config-pmap)# class ipclass2 Switch(config-pmap-c)# set dscp 56 Switch(config-pmap-c)# police aggregate transmit1 Switch(config-pmap-c)# exit Switch(config-pmap)# class class-default Switch(config-pmap-c)# set dscp 10 Switch(config-pmap-c)# exit Switch(config-pmap)# exit Switch(config)# interface gigabitethernet2/0/1 Switch(config-if)# service-policy input aggflow1 Switch(config-if)# exit
Examples: Configuring DSCP Maps
This example shows how to modify and display the CoS-to-DSCP map:
Switch(config)# mls qos map cos-dscp 10 15 20 25 30 35 40 45 Switch(config)# end Switch# show mls qos maps cos-dscp Cos-dscp map: cos: 0 1 2 3 4 5 6 7 -------------------------------- dscp: 10 15 20 25 30 35 40 45
This example shows how to modify and display the IP-precedence-to-DSCP map:
Switch(config)# mls qos map ip-prec-dscp 10 15 20 25 30 35 40 45 Switch(config)# end Switch# show mls qos maps ip-prec-dscp IpPrecedence-dscp map: ipprec: 0 1 2 3 4 5 6 7 -------------------------------- dscp: 10 15 20 25 30 35 40 45
This example shows how to map DSCP 50 to 57 to a marked-down DSCP value of 0:
Switch(config)# mls qos map policed-dscp 50 51 52 53 54 55 56 57 to 0 Switch(config)# end Switch# show mls qos maps policed-dscp Policed-dscp map: d1 : d2 0 1 2 3 4 5 6 7 8 9 --------------------------------------- 0 : 00 01 02 03 04 05 06 07 08 09 1 : 10 11 12 13 14 15 16 17 18 19 2 : 20 21 22 23 24 25 26 27 28 29 3 : 30 31 32 33 34 35 36 37 38 39 4 : 40 41 42 43 44 45 46 47 48 49 5 : 00 00 00 00 00 00 00 00 58 59 6 : 60 61 62 63
 Note | In this policed-DSCP map, the marked-down DSCP values are shown in the body of the matrix. The d1 column specifies the most-significant digit of the original DSCP; the d2 row specifies the least-significant digit of the original DSCP. The intersection of the d1 and d2 values provides the marked-down value. For example, an original DSCP value of 53 corresponds to a marked-down DSCP value of 0. |
This example shows how to map DSCP values 0, 8, 16, 24, 32, 40, 48, and 50 to CoS value 0 and to display the map:
Switch(config)# mls qos map dscp-cos 0 8 16 24 32 40 48 50 to 0 Switch(config)# end Switch# show mls qos maps dscp-cos Dscp-cos map: d1 : d2 0 1 2 3 4 5 6 7 8 9 --------------------------------------- 0 : 00 00 00 00 00 00 00 00 00 01 1 : 01 01 01 01 01 01 00 02 02 02 2 : 02 02 02 02 00 03 03 03 03 03 3 : 03 03 00 04 04 04 04 04 04 04 4 : 00 05 05 05 05 05 05 05 00 06 5 : 00 06 06 06 06 06 07 07 07 07 6 : 07 07 07 07
 Note | In the above DSCP-to-CoS map, the CoS values are shown in the body of the matrix. The d1 column specifies the most-significant digit of the DSCP; the d2 row specifies the least-significant digit of the DSCP. The intersection of the d1 and d2 values provides the CoS value. For example, in the DSCP-to-CoS map, a DSCP value of 08 corresponds to a CoS value of 0. |
This example shows how to define the DSCP-to-DSCP-mutation map. All the entries that are not explicitly configured are not modified (remains as specified in the null map):
Switch(config)# mls qos map dscp-mutation mutation1 1 2 3 4 5 6 7 to 0 Switch(config)# mls qos map dscp-mutation mutation1 8 9 10 11 12 13 to 10 Switch(config)# mls qos map dscp-mutation mutation1 20 21 22 to 20 Switch(config)# mls qos map dscp-mutation mutation1 30 31 32 33 34 to 30 Switch(config)# interface gigabitethernet1/0/1 Switch(config-if)# mls qos trust dscp Switch(config-if)# mls qos dscp-mutation mutation1 Switch(config-if)# end Switch# show mls qos maps dscp-mutation mutation1 Dscp-dscp mutation map: mutation1: d1 : d2 0 1 2 3 4 5 6 7 8 9 --------------------------------------- 0 : 00 00 00 00 00 00 00 00 10 10 1 : 10 10 10 10 14 15 16 17 18 19 2 : 20 20 20 23 24 25 26 27 28 29 3 : 30 30 30 30 30 35 36 37 38 39 4 : 40 41 42 43 44 45 46 47 48 49 5 : 50 51 52 53 54 55 56 57 58 59 6 : 60 61 62 63
 Note | In the above DSCP-to-DSCP-mutation map, the mutated values are shown in the body of the matrix. The d1 column specifies the most-significant digit of the original DSCP; the d2 row specifies the least-significant digit of the original DSCP. The intersection of the d1 and d2 values provides the mutated value. For example, a DSCP value of 12 corresponds to a mutated value of 10. |
Examples: Configuring Egress Queue Characteristics
This example shows how to map a port to queue-set 2. It allocates 40 percent of the buffer space to egress queue 1 and 20 percent to egress queues 2, 3, and 4. It configures the drop thresholds for queue 2 to 40 and 60 percent of the allocated memory, guarantees (reserves) 100 percent of the allocated memory, and configures 200 percent as the maximum memory that this queue can have before packets are dropped:
Switch(config)# mls qos queue-set output 2 buffers 40 20 20 20 Switch(config)# mls qos queue-set output 2 threshold 2 40 60 100 200 Switch(config)# interface gigabitethernet1/0/1 Switch(config-if)# queue-set 2
This example shows how to map DSCP values 10 and 11 to egress queue 1 and to threshold 2:
Switch(config)# mls qos srr-queue output dscp-map queue 1 threshold 2 10 11
This example shows how to configure bandwidth shaping on queue 1. Because the weight ratios for queues 2, 3, and 4 are set to 0, these queues operate in shared mode. The bandwidth weight for queue 1 is 1/8, which is 12.5 percent:
Switch(config)# interface gigabitethernet2/0/1 Switch(config-if)# srr-queue bandwidth shape 8 0 0 0
This example shows how to configure the weight ratio of the SRR scheduler running on an egress port. Four queues are used, and the bandwidth ratio allocated for each queue in shared mode is 1/(1+2+3+4), 2/(1+2+3+4), 3/(1+2+3+4), and 4/(1+2+3+4), which is 10 percent, 20 percent, 30 percent, and 40 percent for queues 1, 2, 3, and 4. This means that queue 4 has four times the bandwidth of queue 1, twice the bandwidth of queue 2, and one-and-a-third times the bandwidth of queue 3.
Switch(config)# interface gigabitethernet2/0/1 Switch(config-if)# srr-queue bandwidth share 1 2 3 4
This example shows how to enable the egress expedite queue when the SRR weights are configured. The egress expedite queue overrides the configured SRR weights.
Switch(config)# interface gigabitethernet1/0/1 Switch(config-if)# srr-queue bandwidth shape 25 0 0 0 Switch(config-if)# srr-queue bandwidth share 30 20 25 25 Switch(config-if)# priority-queue out Switch(config-if)# end
This example shows how to limit the bandwidth on a port to 80 percent:
Switch(config)# interface gigabitethernet2/0/1 Switch(config-if)# srr-queue bandwidth limit 80
When you configure this command to 80 percent, the port is idle 20 percent of the time. The line rate drops to 80 percent of the connected speed, which is 800 Mb/s. These values are not exact because the hardware adjusts the line rate in increments of six.
Where to Go Next
Review the auto-QoS documentation to see if you can use these automated capabilities for your QoS configuration.
Additional References
Related Documents
| Related Topic | Document Title |
|---|---|
For complete syntax and usage information for the commands used in this book. |
Catalyst 2960-XR Switch Quality of Service Command Reference |
Standards and RFCs
| Standard/RFC | Title |
|---|---|
— |
— |
MIBs
| MIB | MIBs Link |
|---|---|
All supported MIBs for this release. |
To locate and download MIBs for selected platforms, Cisco IOS releases, and feature sets, use Cisco MIB Locator found at the following URL: |
Technical Assistance
| Description | Link |
|---|---|
|
The Cisco Support website provides extensive online resources, including documentation and tools for troubleshooting and resolving technical issues with Cisco products and technologies. To receive security and technical information about your products, you can subscribe to various services, such as the Product Alert Tool (accessed from Field Notices), the Cisco Technical Services Newsletter, and Really Simple Syndication (RSS) Feeds. Access to most tools on the Cisco Support website requires a Cisco.com user ID and password. |
Feature History and Information for QoS
| Release | Modification |
|---|---|
| Cisco IOS 15.0(2)EX1 |
This feature was introduced. |
 Feedback
Feedback