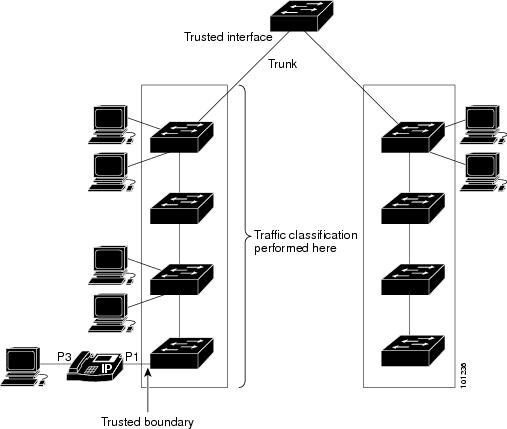
In a typical network, you connect a Cisco IP Phone to a switch port and cascade devices that generate data packets from the back of the telephone. The Cisco IP Phone guarantees the voice
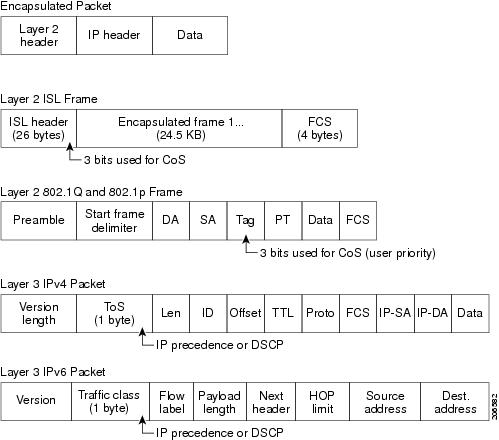
quality through a shared data link by marking the CoS level of the voice packets as high priority (CoS = 5) and by marking
the data packets as low priority (CoS = 0). Traffic sent from the telephone to the switch is typically marked with a tag that uses the 802.1Q header. The header contains the VLAN information and the class of service
(CoS) 3-bit field, which is the priority of the packet.
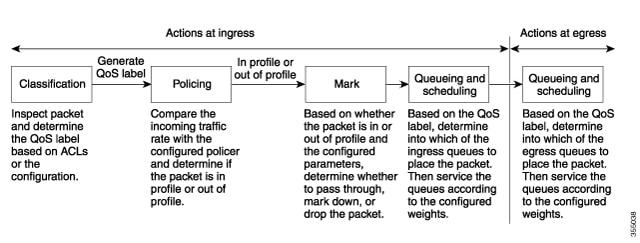
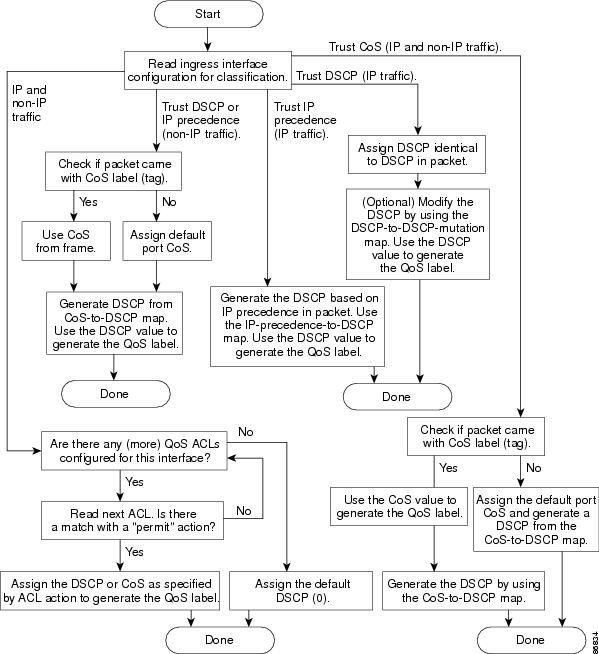
For most Cisco IP Phone configurations, the traffic sent from the telephone to the switch should be trusted to ensure that voice traffic is properly prioritized over other types of traffic in the network. By using
the mls qos trust cos interface configuration command, you configure the switch port to which the telephone is connected to trust the CoS labels of all traffic received on that port. Use the mls qos trust dscp interface configuration command to configure a routed port to which the telephone is connected to trust the DSCP labels of
all traffic received on that port.
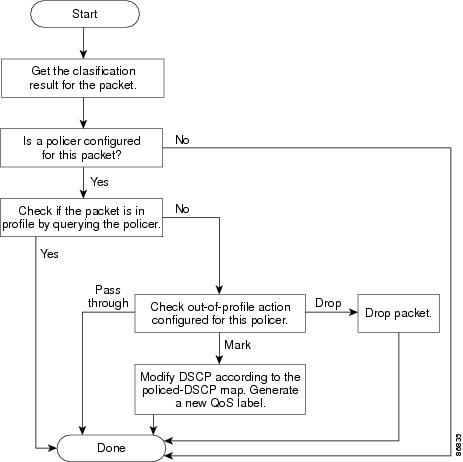
With the trusted setting, you also can use the trusted boundary feature to prevent misuse of a high-priority queue if a user
bypasses the telephone and connects the PC directly to the switch. Without trusted boundary, the CoS labels generated by the PC are trusted by the switch (because of the trusted CoS setting). By contrast, trusted boundary uses CDP to detect the presence of a Cisco IP Phone (such
as the Cisco IP Phone 7910, 7935, 7940, and 7960) on a switch port. If the telephone is not detected, the trusted boundary feature disables the trusted setting on the switch port and prevents misuse of a high-priority queue. Note that the trusted boundary feature is not effective if the PC and
Cisco IP Phone are connected to a hub that is connected to the switch.

 Feedback
Feedback