The following is sample output from the C9610R-SUP-3 and SUP-3-XL bootup in SVL mode:
Switch# show module
Chassis Type: C9610R
Switch Number 1
Mod Ports Card Type Model Serial No.
---+-----+--------------------------------------+--------------+--------------
1 44 40x1/10/25/50GE + 2x200GE + 2x400GE C9600-LC-40YL4CD FDO253602CE
2 44 40x1/10/25/50GE + 2x200GE + 2x400GE C9600-LC-40YL4CD FDO251809YJ
3 32 30x40/100GE + 2x40/100/400GE C9600X-LC-32CD FDO253205BS
4 60 56x1/10/25/50GE + 4x40/100GE C9600X-LC-56YL4C FDO27080QKZ
5 0 Supervisor 3 Module C9610-SUP-3 FDO28160V76
6 0 Supervisor 3 Module
7 48 48-Port 10GE and MGIG COPPER C9600-LC-48TX CAT2308L2G9
8 44 40x1/10/25/50GE + 2x200GE + 2x400GE C9610-LC-40YL4CD FDO283807D8
9 32 30x40/100GE + 2x40/100/400GE C9600X-LC-32CD FDO254907VU
10 32 30x40/100GE + 2x40/100/400GE C9600X-LC-32CD FDO26030AA5
Mod MAC addresses Hw Fw Sw Status
---+--------------------------------+----+------------+------------------+--------
1 A478.06EC.7000 to A478.06EC.707F 1.0 17.18.1r BLD_V1718_THROTTLE_ ok
2 BCD2.9513.D400 to BCD2.9513.D47F 0.2 17.18.1r BLD_V1718_THROTTLE_ ok
3 A478.0633.F800 to A478.0633.F81F 0.2 17.18.1r BLD_V1718_THROTTLE_ ok
4 C02C.178D.4480 to C02C.178D.44FF 0.2 17.18.1r BLD_V1718_THROTTLE_ ok
5 24D5.E4D1.E480 to 24D5.E4D1.E4FF 0.9 17.18.1r BLD_V1718_THROTTLE_ ok
6 N/A N/A N/A N/A other
7 6C8B.D3F4.7E00 to 6C8B.D3F4.7E7F 0.4 17.18.1r BLD_V1718_THROTTLE_ ok
8 286B.5C1A.8400 to 286B.5C1A.847F 0.3 17.18.1r BLD_V1718_THROTTLE_ ok
9 E069.BA16.1180 to E069.BA16.119F 0.2 17.18.1r BLD_V1718_THROTTLE_ ok
10 E069.BADA.4000 to E069.BADA.401F 0.2 17.18.1r BLD_V1718_THROTTLE_ ok
Mod Redundancy Role Operating Redundancy Mode Configured Redundancy Mode
---+-------------------+-------------------------+---------------------------
5 Standby sso sso
6 Standby sso sso
Switch Number 2
Mod Ports Card Type Model Serial No.
---+-----+--------------------------------------+--------------+--------------
1 32 30x40/100GE + 2x40/100/400GE C9600X-LC-32CD FDO254907W3
2 44 40x1/10/25/50GE + 2x200GE + 2x400GE C9600-LC-40YL4CD FDO2512144G
3 44 40x1/10/25/50GE + 2x200GE + 2x400GE C9610-LC-40YL4CD FDO283807CX
4 32 30x40/100GE + 2x40/100/400GE C9600X-LC-32CD FDO254907VX
5 0 Supervisor 3 Module C9610-SUP-3 FDO28160V74
7 32 30x40/100GE + 2x40/100/400GE C9600X-LC-32CD FDO261800XK
8 32 30x40/100GE + 2x40/100/400GE C9600X-LC-32CD FDO254909K3
9 60 56x1/10/25/50GE + 4x40/100GE C9600X-LC-56YL4C FDO27130Q65
10 32 30x40/100GE + 2x40/100/400GE C9610-LC-32CD FDO28390S8J
Mod MAC addresses Hw Fw Sw Status
---+--------------------------------+----+------------+------------------+--------
1 E069.BA16.1400 to E069.BA16.141F 0.2 17.18.1r BLD_V1718_THROTTLE_ ok
2 6C03.090E.DF00 to 6C03.090E.DF7F 0.2 17.18.1r BLD_V1718_THROTTLE_ ok
3 286B.5C1A.6400 to 286B.5C1A.647F 0.3 17.18.1r BLD_V1718_THROTTLE_ ok
4 E069.BA16.2780 to E069.BA16.279F 0.2 17.18.1r BLD_V1718_THROTTLE_ ok
5 8C44.A586.6280 to 8C44.A586.62FF 0.9 17.18.1r BLD_V1718_THROTTLE_ ok
7 806A.000F.D300 to 806A.000F.D31F 0.2 17.18.1r BLD_V1718_THROTTLE_ ok
8 E069.BA16.1E00 to E069.BA16.1E1F 0.2 17.18.1r BLD_V1718_THROTTLE_ ok
9 6C29.D2B7.EF00 to 6C29.D2B7.EF7F 0.2 17.18.1r BLD_V1718_THROTTLE_ ok
10 286B.5C1A.D880 to 286B.5C1A.D89F 0.3 17.18.1r BLD_V1718_THROTTLE_ ok
Mod Redundancy Role Operating Redundancy Mode Configured Redundancy Mode
---+-------------------+-------------------------+---------------------------
5 Active sso sso
Chassis 1 MAC address range: 64 addresses from b08d.57ac.bf00 to b08d.57ac.bf3f
Chassis 2 MAC address range: 64 addresses from b08d.57ac.be00 to b08d.57ac.be3f
Switch#
rommon 1 > boot
boot: attempting to boot from [bootflash:packages.conf]
boot: reading file packages.conf
#
##########################################################################################
Image validated
*Dec 19 05:24:01.719: %IOSXEBOOT-4-SMART_LOG: (local/local):
Fri Dec 19 05:24:01 Universal 2025 INFO: Starting SMART daemon
Restricted Rights Legend
Use, duplication, or disclosure by the Government is
subject to restrictions as set forth in subparagraph
(c) of the Commercial Computer Software - Restricted
Rights clause at FAR sec. 52.227-19 and subparagraph
(c) (1) (ii) of the Rights in Technical Data and Computer
Software clause at DFARS sec. 252.227-7013.
Cisco Systems, Inc.
170 West Tasman Drive
San Jose, California 95134-1706
Cisco IOS Software [IOSXE], Cisco L3 Switch Software (CISCO9K_IOSXE),
Version 17.18.2, RELEASE SOFTWARE (fc3)
Technical Support: http://www.cisco.com/techsupport
Copyright (c) 1986-2025 by Cisco Systems, Inc.
Compiled Fri 19-Dec-25 03:36 by mcpr
This software version supports only Smart Licensing as the software
licensing mechanism.
Please read the following carefully before proceeding. By downloading,
installing, and/or using any Cisco software product, application, feature,
license, or license key (collectively, the "Software"), you accept and
agree to the following terms. If you do not agree, do not proceed and
do not use this Software.
This Software and its use are governed by Cisco's General Terms and any
relevant supplemental terms found at
https://www.cisco.com/site/us/en/about/legal/contract-experience/index.html.
If you have a negotiated agreement with Cisco that includes this Software, the
terms of that agreement apply as well. In the event of a conflict, the order
of precedence stated in your negotiated agreement controls.
Cisco Software is licensed on a term and/or subscription-basis. The license to
the Software is valid only for the duration of the specified term, or in the
case of a subscription-based license, only so long as all required subscription
payments are current and fully paid-up. While Cisco may provide you
licensing-related alerts, it is your sole responsibility to monitor your usage.
Using Cisco Software without a valid license is not permitted and may result in
fees charged to your account. Cisco reserves the right to terminate access to,
or restrict the functionality of, any Cisco Software, or any features thereof,
that are being used without a valid license.
ROMMON variable 'MCP_STARTUP_DEBUG': debugging enabled
ROMMON variable 'MCP_STARTUP_DEBUG_CMD0': debug cwan oir
FIPS: Crimson DB Key Check : Key Not Found, FIPS Mode Not Enabled
cisco C9610R (X86) processor (revision V00) with 239563K bytes of memory.
CMD: debug cwan oir
Processor board ID FOX2814P8MX
0 Virtual Ethernet interface
154 Forty/Hundred Gigabit Ethernet interfaces
136 One/Ten/TwentyFive/Fifty Gigabit Ethernet interfaces
4 Forty/Hundred/TwoHundred Gigabit Ethernet interfaces
14 Forty/Hundred/FourHundred Gigabit Ethernet interfaces
8192K bytes of non-volatile configuration memory.
33554432K bytes of physical memory.
24190976K bytes of Bootflash at bootflash:.
3276800K bytes of Crash Files at crashinfo:.
468850503K bytes of SATA hard disk at disk0:.
Base Ethernet MAC Address : b0:8d:57:ac:be:00
Motherboard Assembly Number : 53A3
Motherboard Serial Number : FOX2814P8MX
Model Revision Number : V02
Motherboard Revision Number : 2
Model Number : C9610R
System Serial Number : FOX2814P8MX
Warning: When Cisco determines that a fault or defect can be traced to
the use of third-party transceivers installed by a customer or reseller,
then, at Cisco's discretion, Cisco may withhold support under warranty or
a Cisco support program. In the course of providing support for a Cisco
networking product Cisco may require that the end user install Cisco
transceivers if Cisco determines that removing third-party parts will
assist Cisco in diagnosing the cause of a support issue.
Press RETURN to get started!
*Dec 19 05:25:07.905: %CRYPTO-5-SELF_TEST_START: Crypto algorithms release (Rel5b), Entropy release (3.4.1)
begin Crypto Module self-tests
*Dec 19 05:25:07.905: %CRYPTO-5-SELF_TEST_START: Crypto algorithms release (Rel5b), Entropy release (3.4.1)
begin Crypto Module Integrity Test
*Dec 19 05:25:07.942: %CRYPTO-5-SELF_TEST_END: Crypto Integrity self-test completed successfully
All tests passed.
*Dec 19 05:25:08.234: %CRYPTO-5-SELF_TEST_END: Crypto Algorithm self-test completed successfully
All tests passed.
*Dec 19 05:25:09.025: %IOSD_INFRA-6-IFS_DEVICE_OIR: Device disk0 added
*Dec 19 05:25:10.958: %CRYPTO-4-AUDITWARN: Encryption audit check could not be performed
*Dec 19 05:25:10.958: %CRYPTO_ENGINE-4-CSDL_COMPLIANCE_DISABLED: Cisco PSB security compliance
has been disabled by configuration
*Dec 19 05:25:12.131: %LINK-3-UPDOWN: Interface LIIN49/2, changed state to up
*Dec 19 05:25:12.796: %LINEPROTO-5-UPDOWN: Line protocol on Interface Loopback999999,
changed state to up
*Dec 19 05:25:13.009: %CLNS-6-DFT_OPT: Protocol timers for fast convergence are Enabled.
*Dec 19 05:25:13.248: %LINEPROTO-5-UPDOWN: Line protocol on Interface LIIN49/2,
changed state to up
*Dec 19 05:25:14.136: %LINK-3-UPDOWN: Interface uds_punject49/3, changed state to up
*Dec 19 05:25:14.143: %SYS-7-NVRAM_INIT_WAIT_TIME: Waited 0 seconds for NVRAM to be available
*Dec 19 05:25:15.141: %LINEPROTO-5-UPDOWN: Line protocol on Interface uds_punject49/3,
changed state to up
*Dec 19 05:27:08.540: %SPA_OIR-6-ONLINECARD: SPA (C9600X-LC-56YL4C) online in subslot 9/0
*Dec 19 05:27:16.341: %LINK-3-UPDOWN: Interface FiftyGigE9/0/48, changed state to up
*Dec 19 05:27:18.333: %LINK-3-UPDOWN: Interface Port-channel241, changed state to up
*Dec 19 05:27:19.332: %LINEPROTO-5-UPDOWN: Line protocol on Interface FiftyGigE9/0/48,
changed state to up
*Dec 19 05:27:19.344: %LINEPROTO-5-UPDOWN: Line protocol on Interface Port-channel241,
changed state to up
*Dec 19 05:27:20.374: %CLNS-5-ADJCHANGE: ISIS: Adjacency to 0871.7219.1000 (Port-channel241) Up,
new adjacency
*Dec 19 05:27:21.344: %CLNS-5-ADJCHANGE: ISIS: Adjacency to sw.B08D57ACBF00 (Port-channel241)
Up, new adjacency
Restricted Rights Legend
Use, duplication, or disclosure by the Government is
subject to restrictions as set forth in subparagraph
(c) of the Commercial Computer Software - Restricted
Rights clause at FAR sec. 52.227-19 and subparagraph
(c) (1) (ii) of the Rights in Technical Data and Computer
Software clause at DFARS sec. 252.227-7013.
Cisco Systems, Inc.
170 West Tasman Drive
San Jose, California 95134-1706
Cisco IOS XE Software, Version 17.18.02
Cisco IOS Software [IOSXE], Cisco L3 Switch Software (CISCO9K_IOSXE),
Version 17.18.2, RELEASE SOFTWARE (fc3)
Technical Support: http://www.cisco.com/techsupport
Copyright (c) 1986-2025 by Cisco Systems, Inc.
Compiled Fri 19-Dec-25 03:36 by mcpre
This software version supports only Smart Licensing as the software licensing
mechanism.
Please read the following carefully before proceeding. By downloading,
installing, and/or using any Cisco software product, application, feature,
license, or license key (collectively, the "Software"), you accept and
agree to the following terms. If you do not agree, do not proceed and do not
use this Software.
This Software and its use are governed by Cisco's General Terms and any
relevant supplemental terms found at
https://www.cisco.com/site/us/en/about/legal/contract-experience/index.html.
If you have a negotiated agreement with Cisco that includes this Software, the
terms of that agreement apply as well. In the event of a conflict, the order
of precedence stated in your negotiated agreement controls.
Cisco Software is licensed on a term and/or subscription-basis. The license to
the Software is valid only for the duration of the specified term, or in the
case of a subscription-based license, only so long as all required subscription
payments are current and fully paid-up. While Cisco may provide you
licensing-related alerts, it is your sole responsibility to monitor your usage.
Using Cisco Software without a valid license is not permitted and may result in
fees charged to your account. Cisco reserves the right to terminate access to,
or restrict the functionality of, any Cisco Software, or any features thereof,
that are being used without a valid license.
ROMMON variable 'MCP_STARTUP_DEBUG': debugging enabled
ROMMON variable 'MCP_STARTUP_DEBUG_CMD0': debug cwan oir
Unable to obtain tty for signal, defaulting to console
CMD: debug cwan oir
debug cwan oir
^
% Invalid input detected at '^' marker.
FIPS: Crimson DB Key Check : Key Not Found, FIPS Mode Not Enabled
*Dec 19 05:27:39.780: ISIS-GRACEFUL-RELOAD: Init State GR_NOT_SUPPORTED
*Dec 19 05:27:40.081: Default mpls label mode set to "per-vrf"
cisco C9610R (X86) processor (revision V00) with 5763019K/6147K bytes of memory.
CMD: debug cwan oir
Processor board ID FOX2814P8MX
0 Virtual Ethernet interface
154 Forty/Hundred Gigabit Ethernet interfaces
136 One/Ten/TwentyFive/Fifty Gigabit Ethernet interfaces
4 Forty/Hundred/TwoHundred Gigabit Ethernet interfaces
14 Forty/Hundred/FourHundred Gigabit Ethernet interfaces
32768K bytes of non-volatile configuration memory.
33554432K bytes of physical memory.
24190976K bytes of Bootflash at bootflash:.
3276800K bytes of Crash Files at crashinfo:.
468850503K bytes of SATA hard disk at disk0:.
Base Ethernet MAC Address : b0:8d:57:ac:be:00
Motherboard Assembly Number : 53A3
Motherboard Serial Number : FOX2814P8MX
Model Revision Number : V02
Motherboard Revision Number : 2
Model Number : C9610R
System Serial Number : FOX2814P8MX
ConstWan OIR debug debugging is on
*Dec 19 05:27:47.030: Master key is already set, not generating new key
Warning: When Cisco determines that a fault or defect can be traced to
the use of third-party transceivers installed by a customer or reseller,
then, at Cisco's discretion, Cisco may withhold support under warranty or
a Cisco support program. In the course of providing support for a Cisco
networking product Cisco may require that the end user install Cisco
transceivers if Cisco determines that removing third-party parts will
assist Cisco in diagnosing the cause of a support issue.
*Dec 19 05:27:47.088: %CNS IQ:0.1 ID:0 Changed:[Switch]
*Dec 19 05:27:47.088: %CNS IQ:0.2 ID:1 Changed:[Switch]
*Dec 19 05:27:47.088: %CNS IQ:0.3 ID:2 Changed:[Switch]
*Dec 19 05:27:47.091: Power redundancy mode changed to: Combined
*Dec 19 05:27:47.092: Power redundancy mode changed to: Combined
login on-success log 14400
^
% Invalid input detected at '^' marker.
*Dec 19 05:27:56.548: yang-infra: self-signed cert inserted(TP-self-signed-1944634332)
*Dec 19 05:27:56.563: AAA CC: AAA CC Default Policy Validation: AAA Default policy is
not available, creating one
% Password has less than number of numeric characters configured
% Warning: Password/key validation failed against default policy
INSECURE DYNAMIC WARNING - Module: AAA, Command: username admin privilege 15 password 6 *,
Reason: Configuration employs a weak password or key, Remediation:
Configure a strong password or key meeting security complexity requirements,
Submode: configure, Parent CLI: configure
INSECURE DYNAMIC WARNING - Module: IP, Command: ip forward-protocol udp tftp,
Reason: Legacy protocol poses data confidentiality and integrity risks due to
lack of encryption and authentication, Remediation: This is a legacy feature,
please consider disabling it, Submode: configure, Parent CLI: Not Applicable
INSECURE DYNAMIC WARNING - Module: TELNET, Command: ip telnet comport enable,
Reason: IP traffic is not encrypted, Remediation: Migrate to secure SSH-based remote access,
Submode: configure, Parent CLI: Not Applicable
SECURITY WARNING - Module: TFTP, Command: ip tftp source-interface GigabitEthernet0/0 ,
Reason: Legacy protocol poses data confidentiality and integrity risks due to lack of encryption
and authentication, Description: TFTP service enabled - unencrypted file transfer protocol
vulnerable to eavesdropping and tampering, Remediation: Transition to secure file transfer
methods using SCP, SFTP, HTTPS protocols
INSECURE DYNAMIC WARNING - Module: RCMD, Command: ip rcmd domain-lookup,
Reason: No encryption is configured, Remediation: This is a legacy feature,
please consider disabling it,
Submode: configure, Parent CLI: Not Applicable
SECURITY WARNING - Module: LINE, Command: transport input all ,
Reason: Legacy protocol poses data confidentiality and integrity risks due to
lack of encryption and authentication, Description: Line transport
configured with unencrypted protocols - allows plaintext transmission of sensitive
data, Remediation: Migrate to secure SSH-based remote access
Press RETURN to get started!
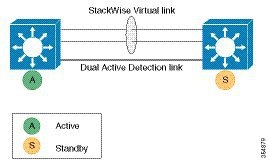
Enabling 400G SVL on the C9600X-LC-32CD and C9610-LC-32CD Line Card
SVL and DAD link configurations on the QSFP-DD interfaces (400G Ethernet ports 27 and 31) of the C9600X-LC-32CD and C9610-LC-32CD
line card are not supported when the ports are operating in non-SVL mode. To enable the SVL links on ports 27 and 31, you
must first enable StackWise Virtual on both the switches without configuring any links as SVL or DAD.
After both the switches are up in StackWise Virtual mode after reload, execute the hw-module switch {1 | 2} slot
number
port-group
range
mode
400G command to enable the 400G interface. After the hw-module configuration is complete, you can configure the linked 400G interfaces (FourHundredGigabitEthernet 27 and FourHundredGigabitEthernet
31) as SVL links and run the write memory command to save the configuration.
The switches then auto-detect the SVL links, and one of the switches restarts because of stack merge. In the next restart
cycle, the same switch restarts again to set switch number 2. In subsequent restart cycles, the device joins the SVL stack
as standby, and the entire SVL system reaches SSO state. You can use the show stackwise-virtual link and show switch commands to verify whether the switch is operating in SVL mode in SSO state.

 Feedback
Feedback