About 802.1X
802.1X is a client-server based access control and authentication protocol that restricts unauthorized clients from connecting to a LAN through publicly accessible ports.
-
Authenticates each client connected to a Cisco NX-OS device port using an authentication server.
-
Allows only Extensible Authentication Protocol over LAN (EAPOL) traffic until authentication is successful.
-
Permits normal traffic through the port after successful authentication.
Device Roles
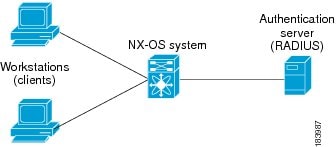
Device roles in 802.1X define the responsibilities of network devices in port-based authentication, including the supplicant, authenticator, and authentication server.
-
Supplicant : The client device that requests access to the LAN and responds to requests from the Cisco NX-OS device, requiring 802.1X-compliant client software.
-
Authentication server : Performs the actual authentication of the supplicant, validates its identity, and notifies the Cisco NX-OS device about authorization. RADIUS with EAP extensions is the only supported authentication server.
-
Authenticator : Controls physical access to the network based on the supplicant's authentication status, acts as an intermediary between the supplicant and authentication server, and includes the RADIUS client for EAP frame handling.
Details of Device Roles in 802.1X Authentication
With 802.1X port-based authentication, devices in the network have specific roles that determine how access is granted and managed.
-
The supplicant is typically a workstation or client device running 802.1X-compliant software, such as Microsoft Windows XP.
-
The authentication server is usually a RADIUS server with EAP extensions, such as Cisco Secure Access Control Server, version 3.0.
-
The authenticator is the Cisco NX-OS device, which acts as a proxy between the supplicant and the authentication server.
-
When the authenticator receives EAPOL frames from the supplicant, it strips the Ethernet header and encapsulates the EAP frame in RADIUS format for the authentication server.
-
The authentication server processes the EAP frame and sends a response back to the authenticator.
-
The authenticator removes the server’s frame header, encapsulates the EAP frame for Ethernet, and sends it to the supplicant.
 Note |
The Cisco NX-OS device can only be an 802.1X authenticator. |
Example of Device Roles in 802.1X
For example, when a user connects a workstation (supplicant) to a network port, the Cisco NX-OS device (authenticator) requests identity information. The authentication server (RADIUS) validates the credentials and authorizes access if the supplicant is verified.
Authentication Initiation and Message Exchange
Authentication initiation and message exchange describe the process by which either the authenticator (Cisco NX-OS device) or the supplicant (client) starts the authentication process, and how EAP frames are exchanged to establish network access.
-
Authentication can be initiated by either the authenticator or the supplicant.
-
The authenticator sends EAP-request/identity frames when a port transitions from down to up.
-
The supplicant responds with EAP-response/identity frames or can initiate authentication with an EAPOL-start frame if no request is received.
Details of Authentication Initiation and Message Exchange
Authentication on Cisco NX-OS devices can be initiated by either the authenticator or the supplicant. When authentication is enabled on a port and the link state transitions from down to up, the authenticator sends an EAP-request/identity frame to the supplicant. The supplicant responds with an EAP-response/identity frame. If the supplicant does not receive a request, it can initiate authentication by sending an EAPOL-start frame. The authenticator then acts as an intermediary, passing EAP frames between the supplicant and the authentication server until authentication succeeds or fails. If authentication is successful, the port becomes authorized.
 Note |
If 802.1X is not enabled or supported on the network access device, the Cisco NX-OS device drops any EAPOL frames from the supplicant. If the supplicant does not receive an EAP-request/identity frame after three attempts to start authentication, the supplicant transmits data as if the port is in the authorized state. A port in the authorized state means that the supplicant has been successfully authenticated. |
The specific exchange of EAP frames depends on the authentication method being used.
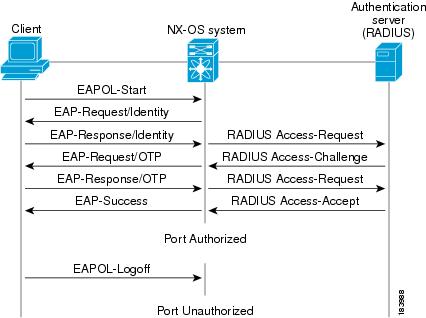
The user’s secret pass-phrase never crosses the network at any time such as during authentication or during pass-phrase changes.
Example of Authentication Message Exchange
This example shows a message exchange initiated by the supplicant using the One-Time-Password (OTP) authentication method with a RADIUS server. The OTP authentication device uses a secret pass-phrase to generate a sequence of one-time (single use) passwords.
Authenticator PAE Status for Interfaces
An authenticator PAE (Port Access Entity) is a protocol entity that supports authentication on an interface when 802.1X is enabled.
-
Created automatically when 802.1X is enabled on an interface.
-
Not automatically cleared when 802.1X is disabled on the interface.
-
Can be explicitly removed and reapplied as needed.
Authenticator PAE Management on Interfaces
When 802.1X is enabled on an interface, the Cisco NX-OS software creates an authenticator PAE instance to support authentication. Disabling 802.1X does not automatically remove the PAE instance; manual removal and reapplication may be required.
Example: Managing Authenticator PAE Instances
For example, after disabling 802.1X on an interface, you may need to explicitly remove the authenticator PAE before re-enabling it to ensure proper authentication behavior.
Ports in Authorized and Unauthorized States
The port authorization state determines whether a supplicant is granted access to the network. Ports can be in authorized or unauthorized states, which control the flow of network traffic based on authentication status.
-
In the unauthorized state, the port blocks all ingress and egress traffic except for 802.1X protocol packets.
-
When a supplicant is successfully authenticated, the port transitions to the authorized state, allowing all traffic for the supplicant.
-
Ports support three authorization states: Force authorized, Force unauthorized, and Auto.
Authorization States and Port Behavior
Ports can operate in different authorization states, each affecting how authentication and network access are managed.
-
Force authorized : Disables 802.1X port-based authentication and transitions to the authorized state without requiring any authentication exchange. The port transmits and receives normal traffic without 802.1X-based authentication of the client. This authorization state is the default.
-
Force unauthorized : Causes the port to remain in the unauthorized state, ignoring all attempts by the client to authenticate. The authenticator cannot provide authentication services to the client through the interface.
-
Auto : Enables 802.1X port-based authentication and causes the port to begin in the unauthorized state, allowing only EAPOL frames to be sent and received through the port. The authentication process begins when the link state of the port transitions from down to up or when an EAPOL-start frame is received from the supplicant. The authenticator requests the identity of the client and begins relaying authentication messages between the client and the authentication server. Each supplicant that attempts to access the network is uniquely identified by the authenticator by using the supplicant’s MAC address.
When a client that does not support 802.1X is connected to an unauthorized 802.1X port, the authenticator requests the client’s identity. If the client does not respond, the port remains in the unauthorized state and the client is not granted access to the network.
When an 802.1X-enabled client connects to a port that is not running the 802.1X protocol, the client initiates the authentication process by sending the EAPOL-start frame. If no response is received, the client retries a fixed number of times and then begins sending frames as if the port is in the authorized state.
If the supplicant is successfully authenticated (receives an Accept frame from the authentication server), the port state changes to authorized, and all frames from the authenticated supplicant are allowed through the port. If authentication fails, the port remains in the unauthorized state, but authentication can be retried. If the authentication server cannot be reached, the authenticator can retransmit the request. If no response is received from the server after the specified number of attempts, authentication fails, and the supplicant is not granted network access.
When a supplicant logs off, it sends an EAPOL-logoff message, which causes the authenticator port to transition to the unauthorized state. If the link state of a port transitions from up to down, or if an EAPOL-logoff frame is received, the port returns to the unauthorized state.
Example: Port State Transitions
For example, if a supplicant is authenticated successfully, the port transitions to the authorized state and allows all traffic. If authentication fails or the supplicant logs off, the port returns to the unauthorized state, restricting network access.
Counter-Example: Non-802.1X Client on Unauthorized Port
If a non-802.1X client is connected to an unauthorized port, it does not respond to identity requests, and the port remains unauthorized, denying network access.
Analogy: Security Checkpoint
Port authorization states are like a security checkpoint: only authenticated individuals (supplicants) are allowed through (authorized state), while others are stopped at the gate (unauthorized state).
Single Host and Multiple Hosts Support
Single-host and multiple-host support in 802.1X define how many endpoint devices can access a port and how authentication and security violations are handled.
-
Single-host mode restricts port access to only one authenticated endpoint device.
-
Multiple-host mode allows multiple endpoint devices to access a port after the first device is authenticated.
-
Security violations are handled differently in each mode, with stricter enforcement in single-host mode.
Details of Single Host and Multiple Hosts Support in 802.1X
The 802.1X feature can restrict traffic on a port to only one endpoint device (single-host mode) or allow traffic from multiple endpoint devices on a port (multi-host mode).
-
Single-host mode: Only one endpoint device is allowed on the port. After authentication, the port is authorized. If the device leaves, the port becomes unauthorized. Any traffic from a different MAC address triggers a security violation, disabling the interface. This mode is used for host-to-switch topologies and applies to both Layer 2 and Layer 3 ports.
-
Multiple-host mode: Only the first host must be authenticated. Once authorized, additional hosts can access the network without separate authentication. If the port becomes unauthorized, all hosts lose access. Security violation shutdown is disabled in this mode. It is applicable to both switch-to-switch and host-to-switch topologies.
Example of Single Host and Multiple Hosts Support
For example, in single-host mode, a single computer connected to a switch port must authenticate before gaining network access. In multiple-host mode, once the first device authenticates, other devices connected to the same port can access the network without additional authentication.
Supported Topology
Supported topology for 802.1X port-based authentication refers to the network configuration in which the authentication protocol operates.
-
Supports point-to-point topology.
-
Only one supplicant (client) can connect to the 802.1X-enabled authenticator port at a time.
-
The authenticator detects the supplicant when the port link state changes to up, and returns to unauthorized state if the supplicant leaves or is replaced.
Reference Information for Supported Topology
The 802.1X port-based authentication is designed for point-to-point topologies, ensuring that only a single client is authenticated per port.
Example of Supported Topology
For example, when a client device connects to a Cisco NX-OS device port configured for 802.1X, the device authenticates the client. If the client disconnects and another device connects, the port transitions to the unauthorized state until the new device is authenticated.
 Feedback
Feedback