Prerequisites to Install Linux Agents
-
For platform requirements, see Supported Platforms and Requirements.
-
To install and execute the agent services, you require root or administrator privileges.
-
The agent and log file require 1 GB of storage space.
-
Configure security exclusions on the security applications that are monitoring the host. This action prevents these applications from blocking agent installation or agent activity. For more information, see Security Exclusions.
-
The system creates a special user, tet-sensor, in the host where the agent is installed. If Pluggable Authentication Modules (PAM) or Security-Enhanced Linux (SELinux) is configured on the host, then grant the tet-sensor user with appropriate privileges. These privileges are necessary to execute the tet-sensor process and make connections to collectors. If you provide an alternative install directory and Security-Enhanced Linux (SELinux) is configured, ensure that you allow execution for that location.
-
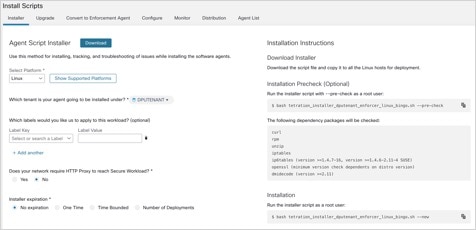
If you install the agent using the AutoInstall (installer script) method, you must be able to use the unzip command.

 Feedback
Feedback