Overview
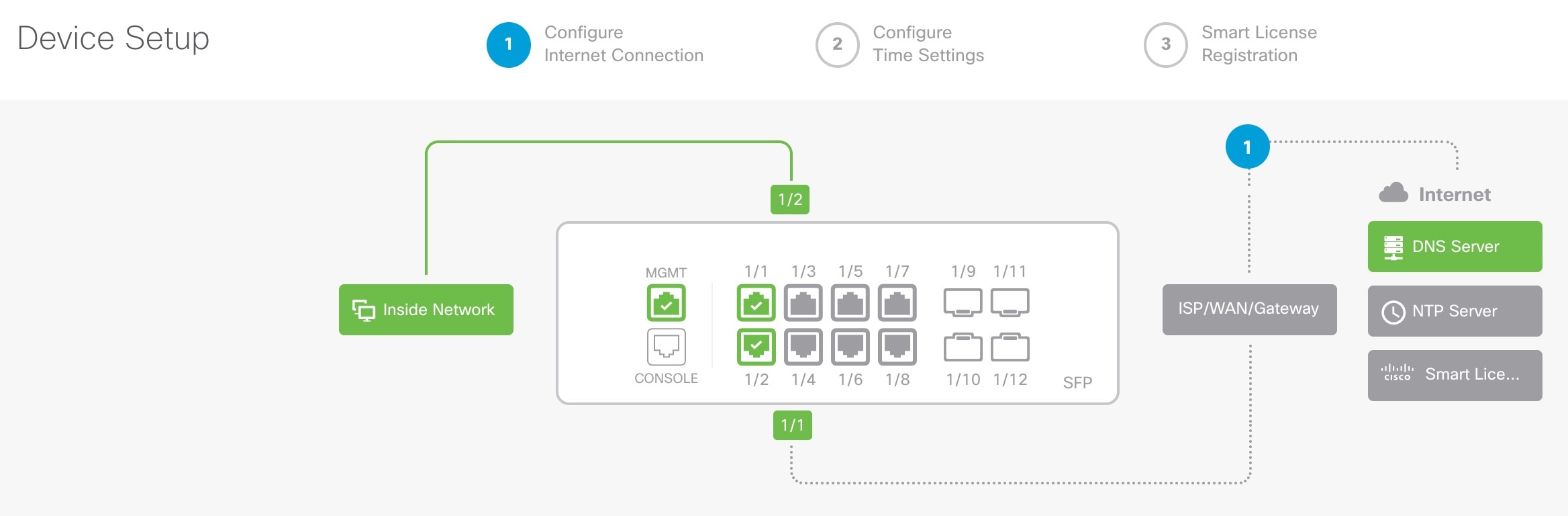
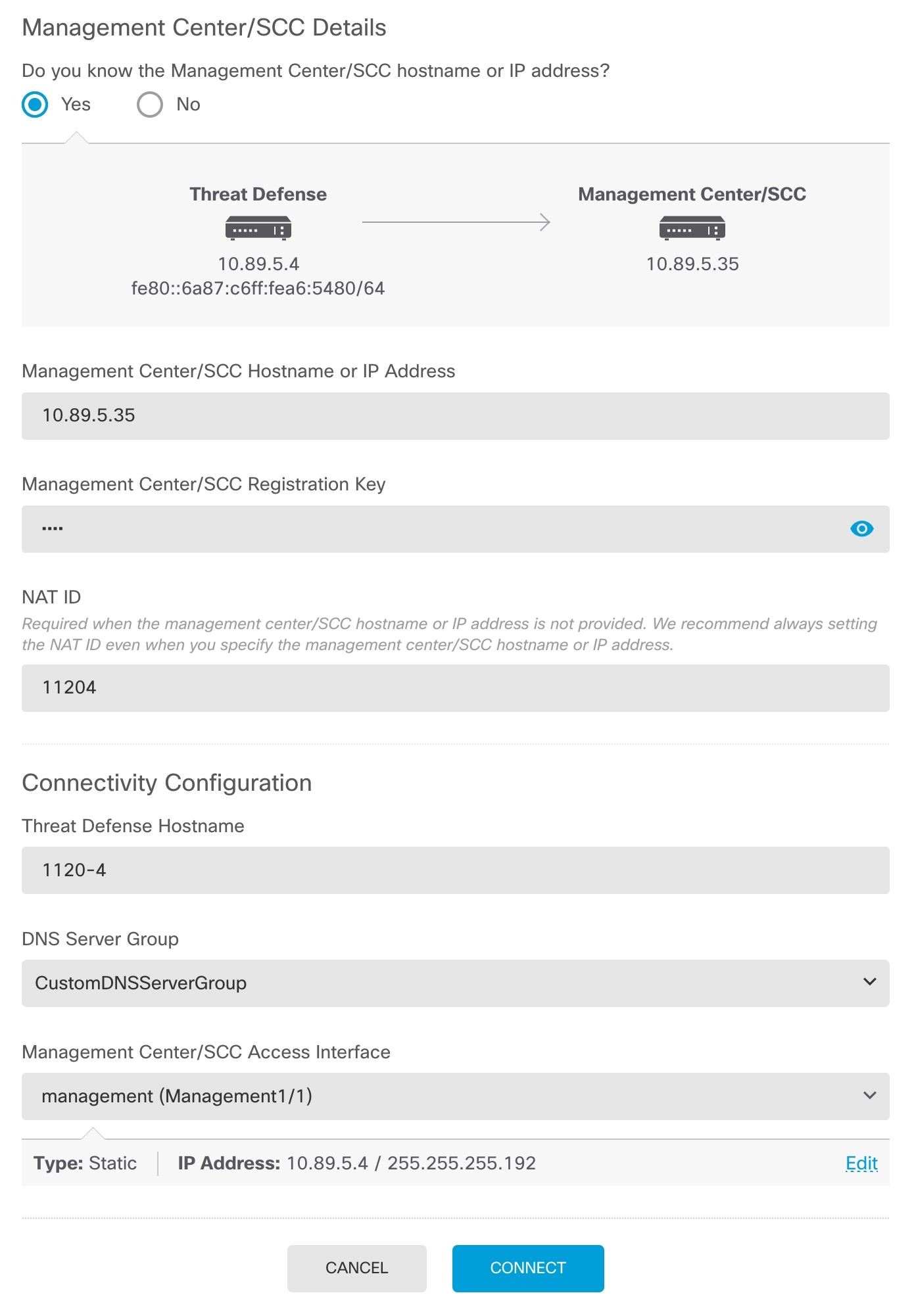
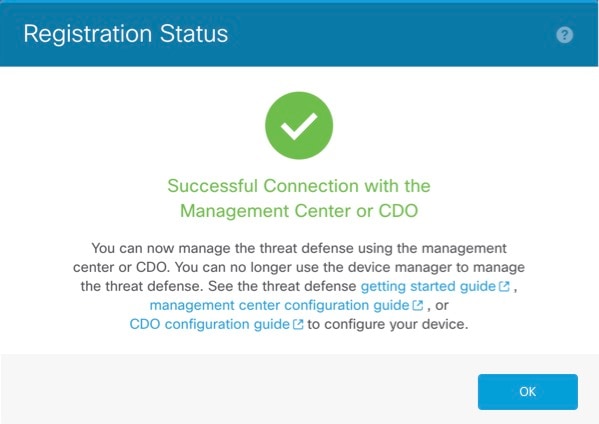
How to complete initial Secure Firewall 3100 setup for manual provisioning so the device has basic network settings and is ready to register to the Firewall Management Center.
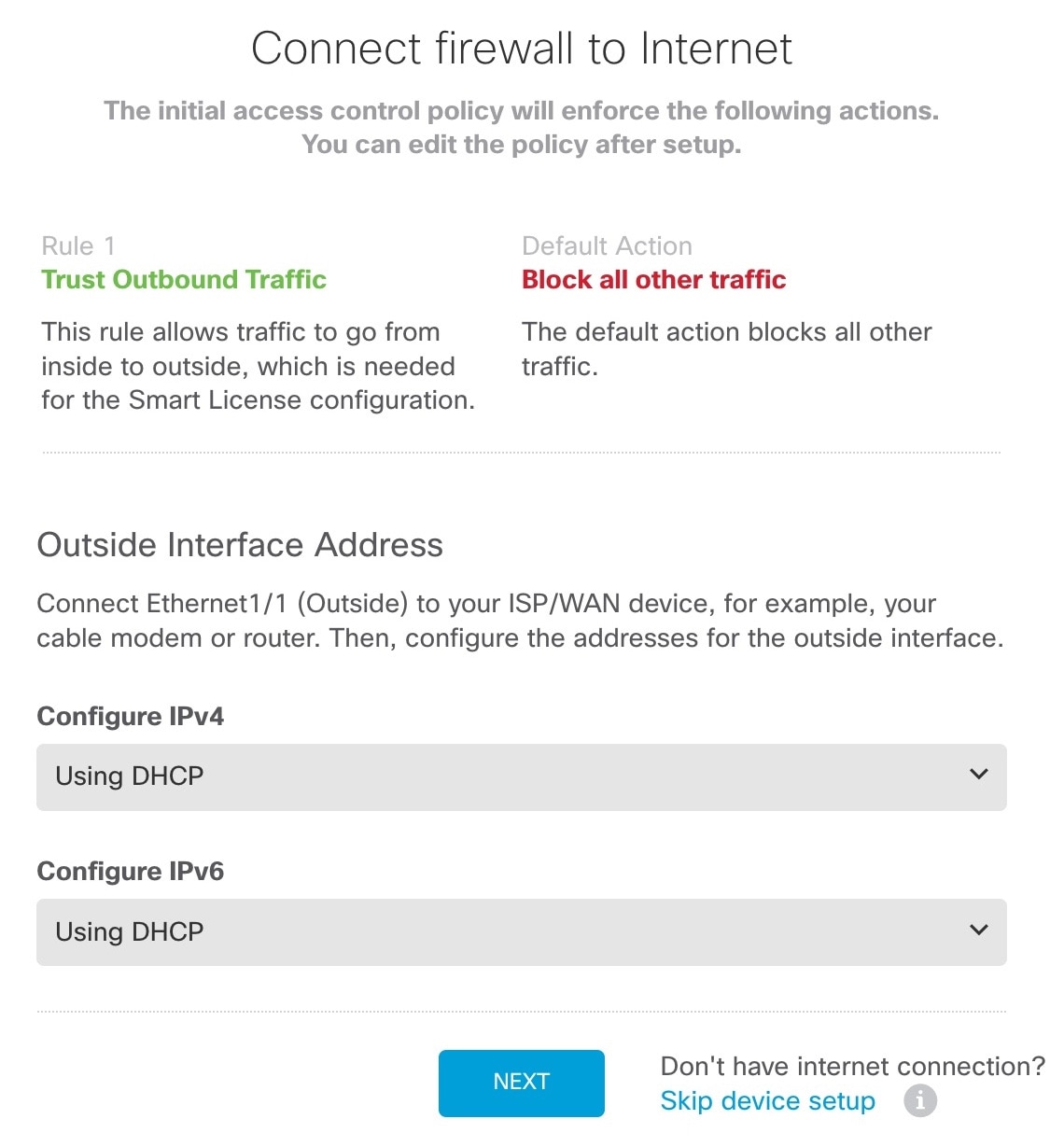
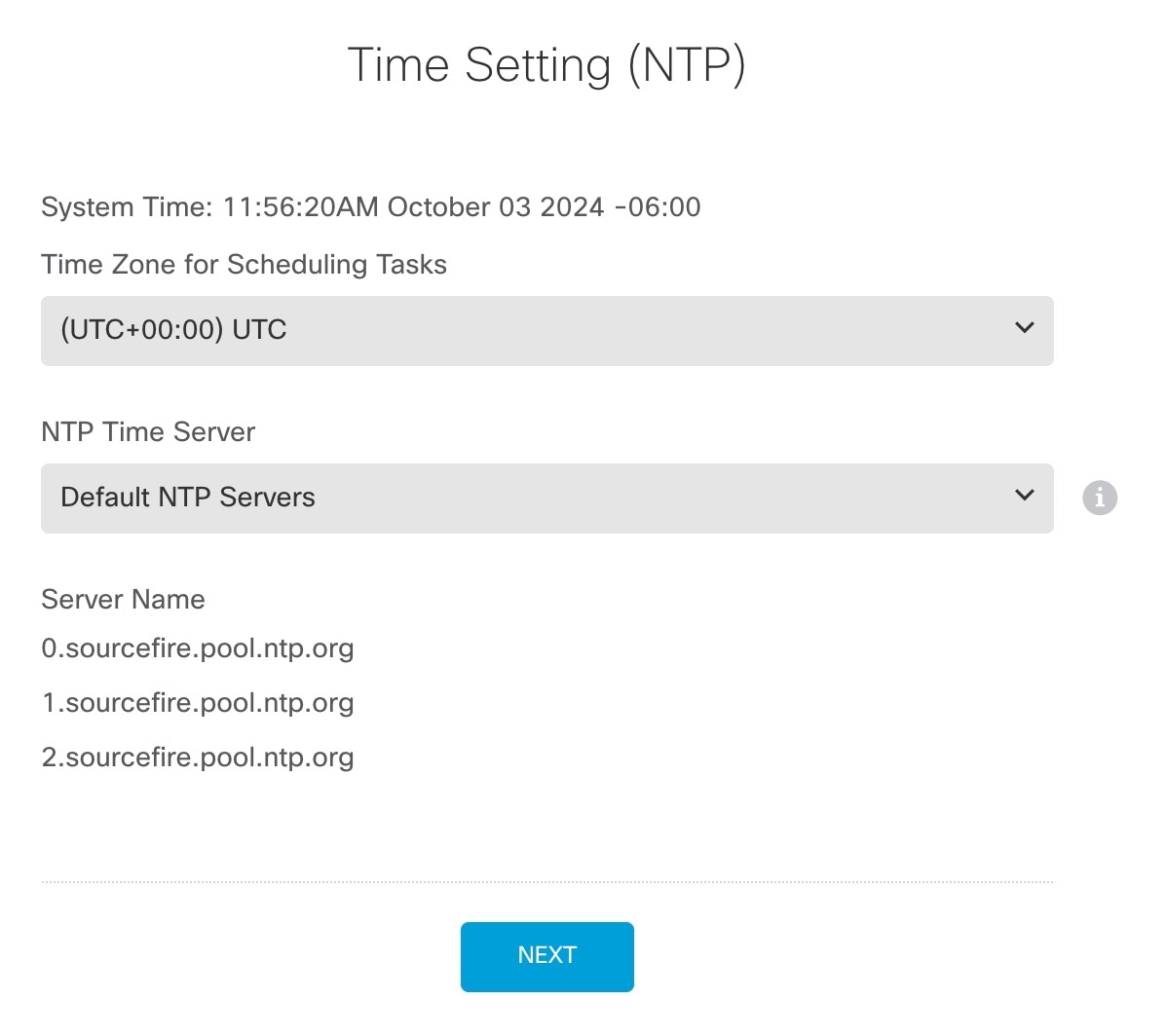
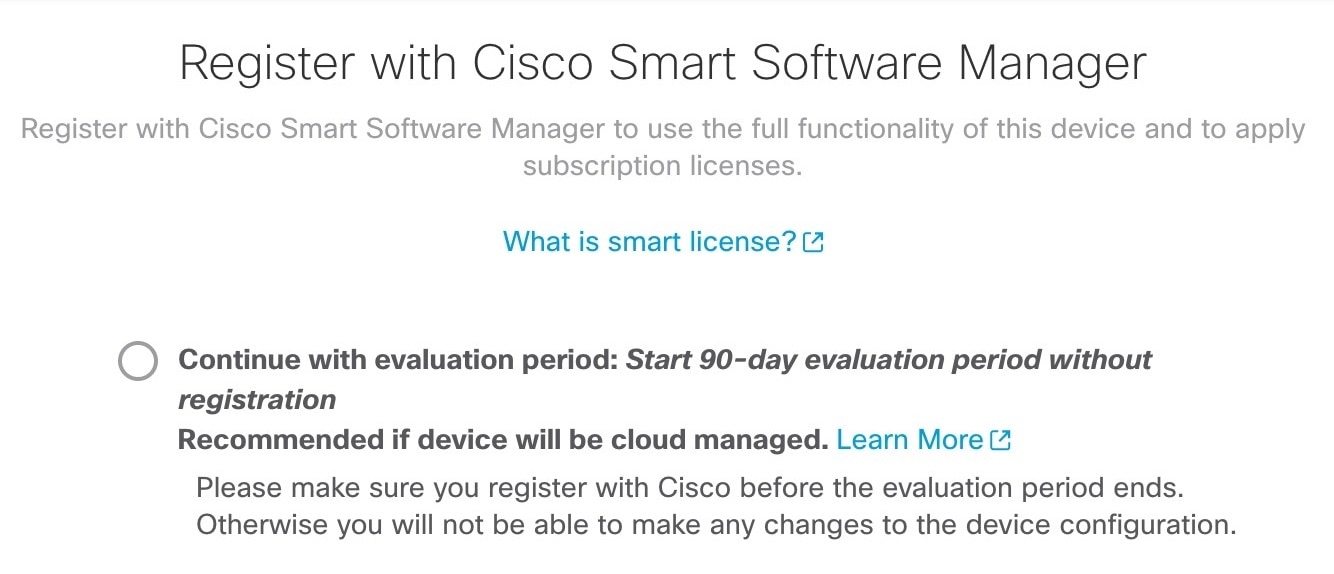
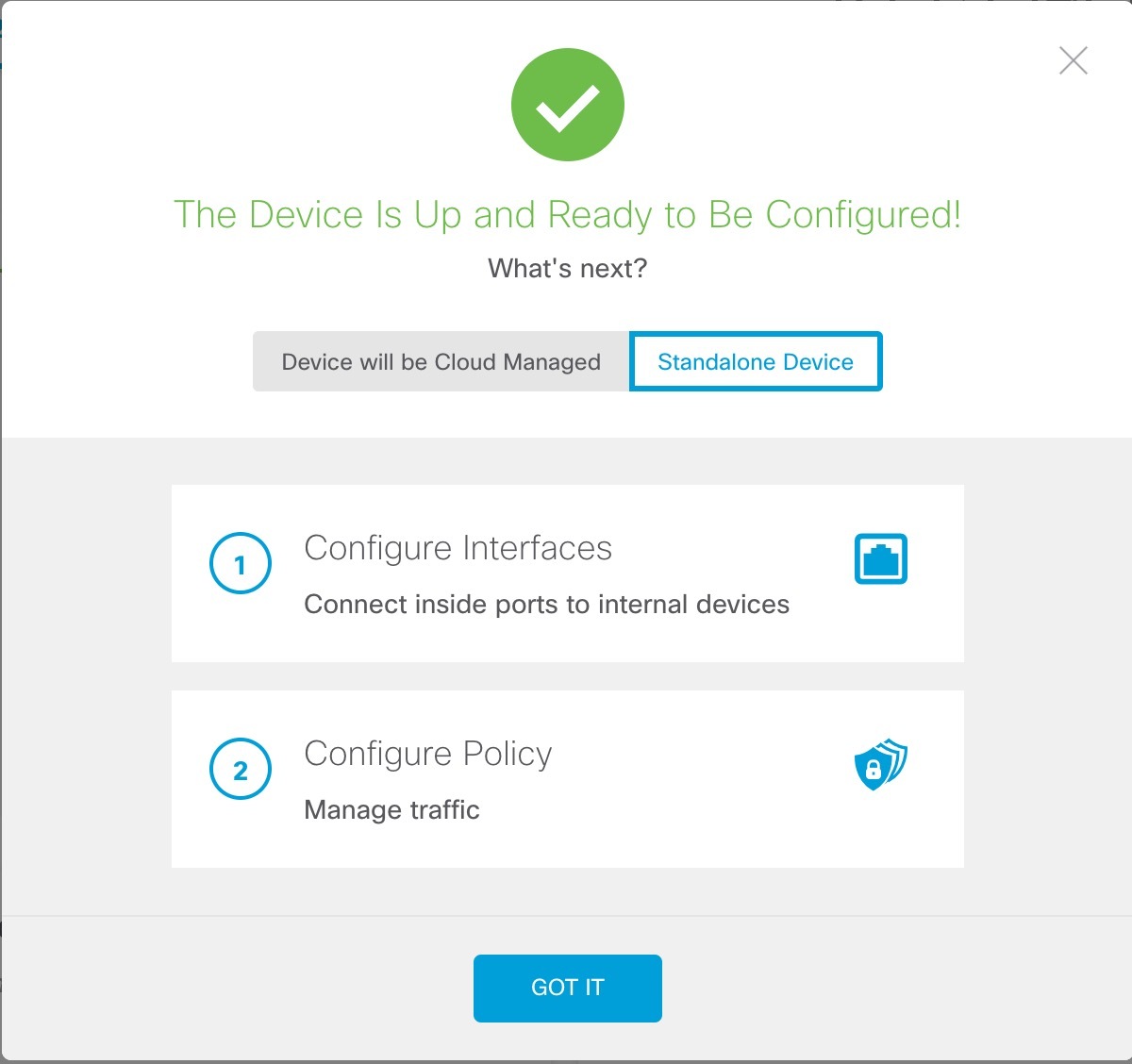
Perfom initial configuration of the firewall using the Secure Firewall Device Manager or using the CLI.