URL Filtering Overview
Use the URL filtering feature to control the websites that users on your network can access:
-
Category and reputation-based URL filtering—With a URL Filtering license, you can control access to websites based on the URL’s general classification (category) and risk level (reputation). This is the recommended option.
-
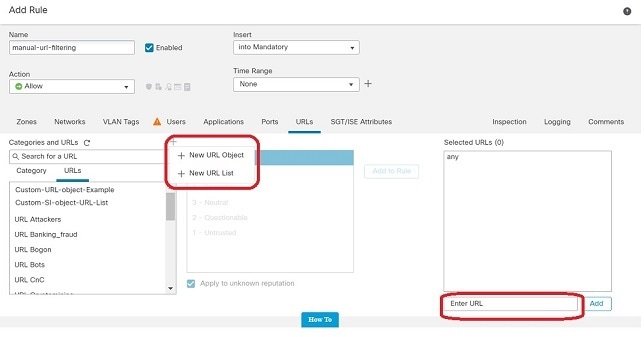
Manual URL filtering—With any license, you can manually specify individual URLs, groups of URLs, and URL lists and feeds to achieve granular, custom control over web traffic. For more information, see Manual URL Filtering.
See also Blocking Traffic with Security Intelligence, a similar but different feature for blocking malicious URLs, domains, and IP addresses.
About URL Filtering with Category and Reputation
With a URL Filtering license, you can control access to websites based on the category and reputation of requested URLs:
-
Category—A general classification for the URL. For example, ebay.com belongs to the Auctions category, and monster.com belongs to the Job Search category.
A URL can belong to more than one category.
-
Reputation—How likely the URL is to be used for purposes that might be against your organization’s security policy. Reputations range from Unknown risk (level 0) or Untrusted (level 1) to Trusted (level 5).
Benefits of Category and Reputation-Based URL Filtering
URL categories and reputations help you quickly configure URL filtering. For example, you can use access control to block untrusted URLs in the Hacking category. Or, you can use QoS to rate limit traffic from sites in the Streaming Video category. There are also categories for types of threats, such as a Spyware and Adware category.
Using category and reputation data simplifies policy creation and administration. It grants you assurance that the system controls web traffic as expected. Because Cisco continually updates its threat intelligence with new URLs, as well as new categories and risks for existing URLs, the system uses up-to-date information to filter requested URLs. Sites that (for example) represent security threats, or that serve undesirable content, may appear and disappear faster than you can update and deploy new policies.
Some examples of how the system can adapt include:
-
If an access control rule blocks all gaming sites, as new domains get registered and classified as Games, the system can block those sites automatically. Similarly, if a QoS rule rate limits all streaming video sites, the system can automatically limit traffic to new Streaming Video sites.
-
If an access control rule blocks all malware sites and a shopping page gets infected with malware, the system can recategorize the URL from Shopping to Malware Sites and block that site.
-
If an access control rule blocks untrusted social networking sites and somebody posts a link on their profile page that contains links to malicious payloads, the system can change the reputation of that page from Favorable to Untrusted and block it.
URL Category and Reputation Descriptions
Category Descriptions
A description of each URL category is available from https://www.talosintelligence.com/categories.
Be sure to click Threat Categories to see those categories.
Reputation Level Descriptions
Go to https://talosintelligence.com/reputation_center/support and look in the Common Questions section.
URL Filtering Data from the Cisco Cloud
URL filtering based on category and reputation requires a data set provided by the Cisco cloud.
Generally, by default, when a valid URL Filtering license is applied to an active device, the URL category and reputation data set is downloaded from the Cisco cloud to the Firepower Management Center and pushed to devices. This locally stored data set is updated periodically.
When a user on the network accesses a URL, the system looks for a match in the local (downloaded) data set. If there is no match, the system checks a cache of results that the system previously looked up in the Cisco cloud. If there is still no match, the system looks up the URL in the Cisco cloud and adds the result to the cache.
The set of URL categories may change periodically. When you receive notification of such changes, you should review the URL rules in your policies to see if you need to make changes. For more information, see If the URL Category Set Changes, Take Action.



 Feedback
Feedback