Threat Intelligence Director Overview
The Threat Intelligence Director operationalizes threat intelligence data, helping you aggregate intelligence data, configure defensive actions, and analyze threats in your environment. This feature is intended to supplement other Firepower functionality, offering an additional line of defense against threats.
When configured on your hosting platform, TID ingests data from threat intelligence sources and publishes the data to all configured managed devices (elements.) For more information about the hosting platforms and elements supported in this release, see Platform, Element, and License Requirements.
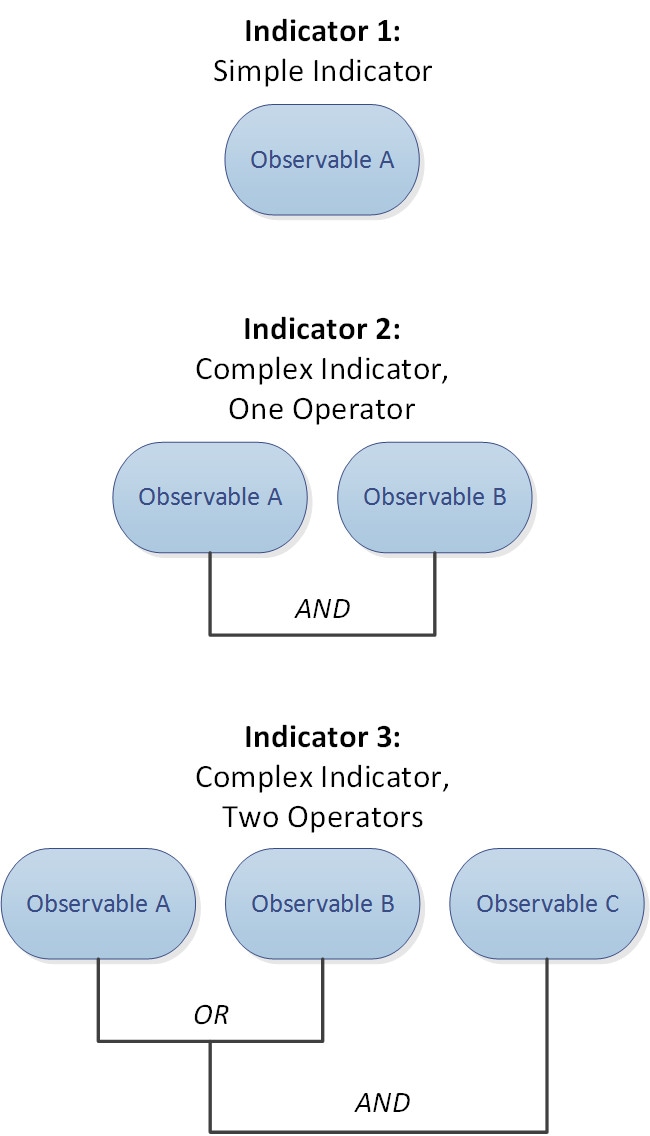
Sources contain indicators, which contain observables. An indicator conveys all of the characteristics associated with a threat, and individual observables represent individual characteristics (e.g. a SHA-256 value) associated with the threat. Simple indicators contain a single observable, and complex indicators contain two or more observables.
Observables and the AND/OR operators between them form an indicator's pattern, as illustrated in the following examples.
After the observables are published to the elements, the elements monitor traffic and report observations to the Firepower Management Center when the system identifies observables in traffic.
The Firepower Management Center collects observations from all elements, evaluates the observations against TID indicators, and generates or updates incidents associated with the observable's parent indicator(s).
An incident is fully realized when an indicator's pattern is fulfilled. An incident is partially realized if traffic matches one or more observables in the indicator but not the entire pattern. For more information, see Observation and Incident Generation.
The following diagram shows data flow in a sample Firepower System configuration.
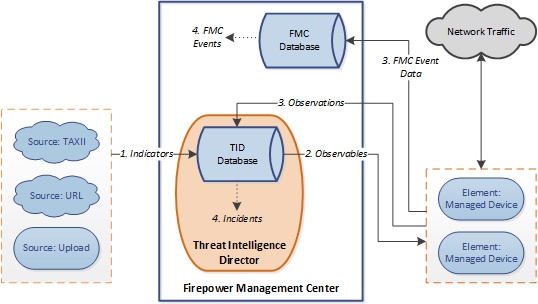
When a TID incident is fully or partially realized, the system takes the configured action (monitor, block, partially block, or no action). For details, see Factors That Affect the Action Taken.
TID and Security Intelligence
As part of your access control policy, Security Intelligence uses reputation intelligence to quickly block connections to or from IP addresses, URLs, and domains. Security Intelligence uniquely provides access to industry-leading threat intelligence from Cisco Talos Intelligence Group (Talos). For more information on Security Intelligence, see About Security Intelligence.
TID enhances the system's ability to block connections based on security intelligence from third-party sources as follows:
-
TID supports additional traffic filtering criteria—Security Intelligence allows you to filter traffic based on IP address, URL, and (if DNS policy is enabled) domain name. TID also supports filtering by these criteria and adds support for filtering on SHA-256 hash values.
-
TID supports additional intelligence ingestion methods—With both Security Intelligence and TID, you can import threat intelligence into the system by either manually uploading flat files or configuring the system to retrieve flat files from a third-party host. TID provides increased flexibility in managing those flat files. In addition, TID can retrieve and ingest intelligence provided in Structured Threat Information eXpression (STIX™) format.
-
TID provides granular control of filtering actions—With Security Intelligence, you can specify filtering criteria by network, URL, or DNS object. Security Intelligence objects, especially list and feeds, can contain multiple IP addresses, URLs, or DNS domain names, but you can only block or not block based on entire objects, not based on individual components of an object. With TID, you can configure filtering actions for individual criteria (that is, simple indicators or individual observables).
-
TID configuration changes do not require redeployment—After you modify Security Intelligence settings in the access control policy, you must redeploy the changed configuration to managed devices. With TID, after initial deployment of the access control policy to the managed devices, you can configure sources, indicators, and observables without redeploying, and the system automatically publishes new TID data to the elements.
For information about what the system does when either Security Intelligence or TID could handle a particular incident, see TID-Firepower Management Center Action Prioritization.
Performance Impact of Threat Intelligence Director
Firepower Management Center
In some cases, you may notice the following:
-
The system may experience minor performance issues while ingesting particularly large STIX sources, and ingestion may take longer than expected to finish.
-
The system may take up to 15 minutes to publish new or modified TID data down to elements.
Managed Device
There is no exceptional performance impact. TID impacts performance identically to the Firepower Management Center Security Intelligence feature.
Threat Intelligence Director and High Availability Configurations
If you host TID on the active Firepower Management Center in a high availability configuration, the system does not synchronize TID configurations and TID data to the standby Firepower Management Center. We recommend performing regular backups of TID data on your active Firepower Management Center so that you can restore the data after failover.
For details, see About Backing Up and Restoring TID Data.

 )
) )
) )
) )
) )
) )
) )
) )
)

 Feedback
Feedback