Information About the TR-069 Agent
Limitations for the TR-069 Agent
The following table provide the limitations of the parameters in TR-069.
|
TR-069 Parameter |
Expected Value |
Supported on Cisco ISR G2 |
Supported on Cisco 4451 |
|---|---|---|---|
|
InternetGatewayDevice. WANDevice.2. WANConnectionDevice.1.WANIPConnection.1.Uptime |
Time |
No |
No |
|
Internet gatewy device. WAN device2. WAN common interface config enabled. For Internet registration entry for Internet gateway device. WAN device. WAN common Interface configuration does not include the parameter enabled for Internet. |
True or Flase |
No |
No |
|
InternetGatewayDevice.DeviceInfo.SoftwareVersionentPhysicalSoftwareRev for the Cisco ISR4451 Chassis is NULL, hence InternetGatewayDevice.DeviceInfo.SoftwareVersion is also NULL |
Version |
Yes |
No |
|
WAN access type is DSL (Internet gateway device. WAN device2. WAN common interface configuration. WAN access type) The WAN DSL interface configuration data is populates when the WAN access type is Ethernet (Internet Gateway device. WAN device. WAN common interface configuration interface config. WAN access type). The WAN Ethernet interface configuration date populates. |
Populate the details |
Yes |
Yes |
|
InternetGatewayDevice.Layer3Forwarding.Forwarding.1.MTUregistration entry for InternetGatewayDevice.Layer3Forwarding.Forwarding. does not include the parameter MTU |
MTU value |
No |
No |
|
Internet gateway device. Layer 3 forwarding. Forwarding 1. MTU registration entry for Internet gateway device. Layer 3 forwarding. Forwarding does not include the parameter MTU. |
MTU value |
No |
No |
|
Set parameter values- Internet gateway device. Time. NTP server 5 in Cisco 4451, config t, archive, path boot flash should be configured to set the value in Cisco ISR G2; only one storage path and it is the flash memory. |
ntp server 100.12.12.1 |
YES (no archive) |
YES (configure archive) |
TR-069 Agent
The TR-069 Agent allows an ACS to provision a CPE or collection of CPEs. The provisioning mechanism includes specific provisioning parameters and a general mechanism for adding vendor-specific provisioning capabilities as needed. The identification mechanisms included in the protocol allow CPE provisioning based either on the requirements of each specific CPE, or on collective criteria such as the CPE vendor, model, software version, or other criteria.
The provisioning mechanism allows CPE provisioning at the time of initial connection to the broadband access network and the ability to reprovision at any subsequent time. This includes support for asynchronous ACS-initiated reprovisioning of a CPE.
The TR-069 Agent also supports image upgrade, configuration application, file downloads, configuration and log file uploads, and CPE monitoring.
 Note |
The TR-069 Agent CPE devices must be set up and enabled for TR-069. An ACS used to communicate with the CPE must be TR-069 compliant in order to enable the TR-069 Agent. |
RPC Support
The following remote procedure calls (RPCs) are supported with the TR-069 Agent:
-
Standard RPCs
-
GetRPCMethods
-
SetParameterValues
-
GetParameterValues
-
GetParameterNames
-
SetParameterAttributes
-
GetParameterAttributes
-
AddObject
-
DeleteObject
-
Reboot
-
Download
-
Upload

Note
In case of the Download operation, the file transfer option is supported only through HTTP.
-
-
Vendor RPCs
-
X_00000C_SetConfiguration
-
X_00000C_ShowStatus
-
CWMP Vendor Profile Schema
The following details the CWMP vendor profile schema:
-
For SetConfiguration,
<cwmp:X_00000C_SetConfiguration>
<ErrorOption> rollback </ErrorOption>
<Target> {running-config | startup-config} </Target>
<ConfigCommandBlock> block of clis separated by newline [\n] character </ConfigCommandBlock>
<ConfigCommandList array of strings[1..unbounded] each of length 256>
<string> IOS Configuration command 1 </string>
<string> IOS Configuration command 2 </string>
</ConfigCommandList>
<ParameterKey> parameterkey </ParameterKey>
</cwmp:X_00000C_SetConfiguration>
ErrorOption => string with length 64
Target => string with length 64
On success,
<X_00000C_SetConfigurationResponse>
<Status>0</Status>
</X_00000C_SetConfigurationResponse>
On failure,
<SOAP:Fault>
<SOAP:faultcode>Client</SOAP:faultcode>
<SOAP:faultstring>CWMP fault</SOAP:faultstring>
<SOAP:detail>
<cwmp:Fault>
<FaultCode></FaultCode>
<FaultString></FaultString>
<cwmp:X_00000C_SetConfigurationFault>
<Command>IOS Configuration command that failed</Command>
<FaultCode>parse_cmd() return value</FaultCode>
</cwmp:X_00000C_SetConfigurationFault>
<cwmp:X_00000C_SetConfigurationFault>
<Command>IOS Configuration command that failed</Command>
<FaultCode>parse_cmd() return value</FaultCode>
</cwmp:X_00000C_SetConfigurationFault>
</cwmp:Fault>
</SOAP:detail>
</SOAP:Fault>
-
For ShowStatus,
<cwmp:X_00000C_ShowStatus>
<ExecCommandList array of strings[1..unbounded] each of length 256 >
<string> IOS Exec command 1 </string>
<string> IOS Exec command 2 </string>
<string> IOS Exec command 3 </string>
</ExecCommandList>
</cwmp:X_00000C_ShowStatus>
On success,
<cwmp:X_00000C_ShowStatusResponse>
<ExecResponseList array of ExecResponseStruct [1..unbounded]>
<ExecResponseStruct>
<Command> IOS Exec command 1 </Command>
<Response> output of command 1</Response>
</ExecResponseStruct>
<ExecResponseStruct>
<Command> IOS Exec command 2 </Command>
<Response> output of command 2 </Response>
</ExecResponseStruct>
<ExecResponseStruct>
<Command> IOS Exec command 3 </Command>
<Response>output of command 3</Response>
</ExecResponseStruct>
</ExecResponseList>
</cwmp:X_00000C_ShowStatusResponse>
On failure,
<SOAP:Fault>
<SOAP:faultcode>Client</SOAP:faultcode>
<SOAP:faultstring>CWMP fault</SOAP:faultstring>
<SOAP:detail>
<cwmp:Fault>
<FaultCode></FaultCode>
<FaultString></FaultString>
</cwmp:Fault>
</SOAP:detail>
</SOAP:Fault>
HTTP Digest Authentication Support
The TR-069 Agent uses HTTP as the transport and needs support for digest authentication from the HTTP client infrastructure.
 Note |
This feature is not a TR-069 Agent-exclusive feature and can be used in other scenarios to configure HTTP Digest Authentication Support. |
HTTP Cookie Support Per RFC2965
A cookie is a piece of HTTP state information generated and sent by an HTTP server in response to an HTTP request. The HTTP client returns the cookie containing the state information back to the HTTP server in its next HTTP request. This scenario is used to create a stateful session with HTTP requests and responses. The TR-069 Agent uses HTTP as the transport and needs support for both Netscape cookies and RFC 2965 in HTTP client infrastructure.
 Note |
This feature is not a TR-069 Agent-exclusive feature and can be used in other scenarios to clear, monitor and troubleshoot HTTP cookies. |
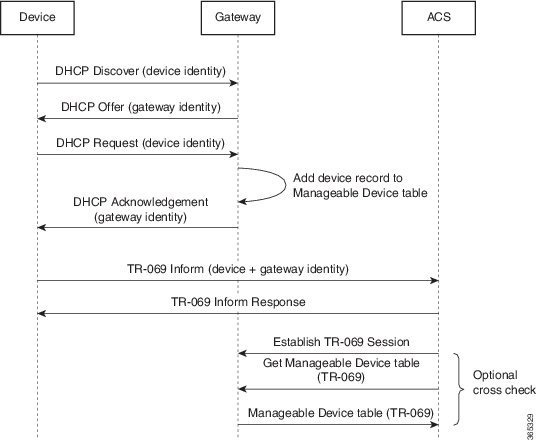
Device Gateway Association
The CPE WAN Management Protocol (CWMP) can be used to remotely manage customer premise equipment (CPE) devices that are connected over a LAN through a gateway. If Auto Configuration Server (ACS) manages both the Device and the Gateway through which the device is connected , ACS determines the identity of the gateway by checking the device gateway association information. The ACS with the device gateway association profile can identify the end devices behind each gateway. The device gateway association constitutes Annex F (previously part of TR-111), part of the TR-069 standard. The mechanism defined for device gateway association relies on the Device’s use of Dynamic Host Configuration Protocol (DHCP) Option 125. The end devices will pass on their identity to the gateway via vendor-specific DHCP option. When the gateway receives this information, the gateway populates the ManageableDevice table containing identity information for each device on its LAN. The parameters, which are supported on the gateway as part of device gateway association is as follows:
-
InternetGatewayDevice.ManagementServer.ManageableDeviceNumberOfEntries
-
InternetGatewayDevice.ManagementServer.ManageableDevice.{i}
-
ManufacturerOUI
-
ProductClass
-
SerialNumber
-
The device gateway association functionality does not support configuring IP addresses manually on the end devices. The IP addresses are assigned to the end devices via DHCP by the gateway. You must configure renew deny unknown command under the DHCP server configuration to initiate the DHCP discovery process for the end devices after a gateway reload.
The following example shows how to set up the Device-Gateway Association and Port Mapping feature via a Dynamic Host Configuration Protocol (DHCP) on VLAN interface:
ip dhcp excluded-address 15.15.15.1
!
ip dhcp pool NET-POOL1
network 15.15.15.0 255.255.255.0
default-router 15.15.15.1
lease 0 0 5
renew deny unknown
end
interface Vlan102
ip address pool NET-POOL1
endPort Mapping Support
The CPE WAN Management Protocol (CWMP) can be used to remotely manage customer premise equipment (CPE) devices that are connected via a LAN through a network address translation (NAT) gateway. This can be achieved by making use of the PortMapping functionality. This feature helps in maintaining the privacy of the IP addresses of the end devices as the communication happens with the auto-configuration server (ACS) in the public domain. The gateway supports the following CWMP parameters:
-
InternetGatewayDevice.WANDevice.{i}.WANConnectionDevice.{i}.WANIPConnection.{i}. PortMappingNumberOfEntries
-
InternetGatewayDevice.WANDevice.{i}.WANConnectionDevice.{i}.WANIPConnection.{i}.Port-Mapping.{i}.
-
PortMappingEnabled
-
PortMappingLeaseDuration
-
RemoteHost
-
ExternalPort
-
InternalPort
-
PortMappingProtocol
-
InternalClient
-
PortMappingDescription
-
-
InternetGatewayDevice.WANDevice.{i}.WANConnectionDevice.{i}.WANPPP-Connection.{i}.PortMappingNumberOfEntries
-
InternetGatewayDevice.WANDevice.{i}.WANConnectionDevice.{i}.WANPPP-Connection.{i}.PortMapping.{i}.
-
PortMappingEnabled
-
PortMappingLeaseDuration
-
RemoteHost
-
ExternalPort
-
InternalPort
-
PortMappingProtocol
-
InternalClient
-
PortMappingDescription
-
 Note |
The ACS must provide values for the mandatory parameters—ExternalPort, InternalPort, PortMappingProtocol, and InternalClient—to the gateway for adding the port mapping for an end device. There is no support to limit the portmapping to a particular host using RemoteHost parameter. |
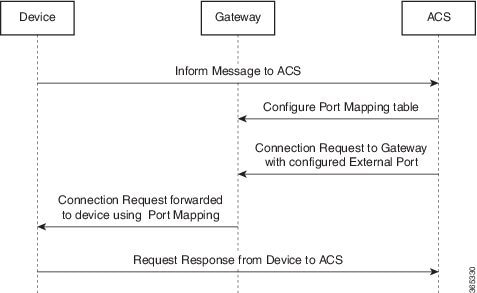
The following is an example Port Mapping Support on a device configured as a gateway and ACS.
For the below parameters configured on ACS,
Destination IP (InternalClient) - 15.15.15.2
Source port (ExternalPort) - 9000
Destination port (InternalPort) - 7547
PortMappingProtocol - TCP
the following NAT command is configured on the gateway:
ip nat inside source static tcp 15.15.15.2 7547 10.194.145.170 9000 extendable10.194.145.170 is the RemoteHost and the IP address of the device or gateway provisioned by ACS. This is the IP address corresponding to the interface with the configuration cwmp wan default command.
VRF Support for CPE WAN Management Protocol
The digital subscriber line (DSL) forum's TR-069 and CPE WAN Management Protocol (CWMP) are used for communications between a customer premise equipment (CPE) and an auto-configuration server (ACS). Virtual Route Forward (VRF) will be supported on TR-069 and TR-111 from Cisco IOS XE Bengaluru 17.4.1 onwards.
This feature supports:
-
TR-069 within a VRF aware interface
-
TR-069 within a VRF aware sub-interface
-
TR-069 within a VRF aware loopback interface
-
Device association profile over VRF
-
Port mapping table over VRF
-
Port forwarding service from ACS
The following are the examples for different scenarios:
interface GigabitEthernet0/0/1
vrf forwarding blue
ip address 11.1.1.1 255.255.255.0
cwmp wan default
interface GigabitEthernet0/0/1.4092
encapsulation dot1Q 4092
vrf forwarding blue
ip address 12.1.1.1 255.255.255.0
cwmp wan default
interface GigabitEthernet0/0/1
vrf forwarding blue
ip address 11.1.1.1 255.255.255.0
interface Loopback0
vrf forwarding blue
ip address 20.1.1.1 255.255.255.0
cwmp wan default
interface GigabitEthernet0/0/1.4092
encapsulation dot1Q 4092
vrf forwarding blue
ip address dhcp
cwmp wan default
On peer end, ip dhcp pool should be configured as follows:
ip dhcp excluded-address 12.1.1.2
ip dhcp pool cwmp-pool
network 12.1.1.0 255.255.255.0
default-router 12.1.1.2
Router#sh ip dhcp binding
Bindings from all pools not associated with VRF:
IP address Client-ID/ Lease expiration Type State Interface
Hardware address/
User name
Bindings from VRF pool blue:
IP address Client-ID/ Lease expiration Type State Interface
Hardware address/
User name
5.6.6.2 0004.137a.1c50 Mar 04 2020 04:33 PM Automatic Active Vlan102
5.6.6.3 0004.137a.1c7a Mar 04 2020 04:33 PM Automatic Active Vlan102
Router#sh ip dhcp binding vrf blue
Bindings from VRF pool blue:
IP address Client-ID/ Lease expiration Type State Interface
Hardware address/
User name
5.6.6.2 0004.137a.1c50 Mar 04 2020 04:33 PM Automatic Active Vlan102
5.6.6.3 0004.137a.1c7a Mar 04 2020 04:33 PM Automatic Active Vlan102
Router#show cwmp map wandevice
CWMP WAN Id Interface
1 GigabitEthernet0/0/1
interface GigabitEthernet0/0/1.4092
encapsulation dot1Q 4092
vrf forwarding blue
ip address 12.1.1.1 255.255.255.0
ip nat outside
cwmp wan default
interface GigabitEthernet0/1/7
switchport access vlan 102
interface Vlan102
vrf forwarding blue
ip address 5.6.6.1 255.255.255.0
ip nat inside
On UUT, NAT should be configured as follows:
ip access-list extended NATLIST
permit ip 5.6.6.0 0.0.0.255 any
ip nat inside source list NATLIST interface GigabitEthernet0/0/1.4092 vrf blue overload
 Feedback
Feedback