- Preface
- Product Overview
- Basic Router Configuration
- Configuring Ethernet CFM and Y.1731 Performance Monitoring on Layer 3 Interfaces
- Configuring Power Management
- Configuring Security Features
- Configuring Secure Storage
- Configuring Backup Data Lines and Remote Management
- Configuring Ethernet Switches
- Configuring Voice Functionality
- Configuring the Serial Interface
- Configuring Wireless Devices
- Configuring PPP over Ethernet with NAT
- Configuring PPP over ATM with NAT
- Environmental and Power Management
- Configuring a LAN with DHCP and VLANs
- Configuring a VPN Using Easy VPN and an IPSec Tunnel
- Configuring Cisco Multimode G.SHDSL EFM/ATM
- Configuring VDSL2 Bonding and Single-Wire Pair
- Configuring Cisco IOx
- Deployment Scenarios
- Troubleshooting Cisco 800 Series Routers
- Cisco IOS Software Basic Skills
- Concepts
- ROM Monitor
- Index
- Authentication, Authorization, and Accounting
- Configuring AutoSecure
- Configuring Access Lists
- Configuring Cisco IOS Firewall
- Configuring Cisco IOS IPS
- URL Filtering
- Configuring VPN
- Cisco ScanSafe
Configuring Security Features
This chapter provides an overview of authentication, authorization, and accounting (AAA), which is the primary Cisco framework for implementing selected security features that can be configured on the Cisco 860 and Cisco 880 series Integrated Services Routers (ISRs).
This chapter contains the following sections:
- Authentication, Authorization, and Accounting
- Configuring AutoSecure
- Configuring Access Lists
- Configuring Cisco IOS Firewall
- Configuring Cisco IOS IPS
- URL Filtering
- Configuring VPN
- Cisco ScanSafe
Authentication, Authorization, and Accounting
AAA network security services provide the primary framework through which you set up access control on your router. Authentication provides the method of identifying users, including login and password dialog, challenge and response, messaging support, and depending on the security protocol you choose, encryption. Authorization provides the method for remote access control, including one-time authorization or authorization for each service; per-user account list and profile; user group support; and support of IP, Internetwork Packet Exchange (IPX), AppleTalk Remote Access (ARA), and Telnet. Accounting provides the method for collecting and sending security server information used for billing, auditing, and reporting, such as user identities, start and stop times, executed commands (such as PPP), number of packets, and number of bytes.
AAA uses protocols such as RADIUS, TACACS+, or Kerberos to administer its security functions. If your router is acting as a network access server, AAA is the means through which you establish communication between your network access server and your RADIUS, TACACS+, or Kerberos security server.
For information about configuring AAA services and supported security protocols, see the following sections of http://www.cisco.com/en/US/docs/ios/sec_user_services/configuration/guide/12_4T/sec_securing_user_services_12.4t_book.html Cisco IOS Security Configuration Guide: Securing User Services, Release 12.4T :
- Configuring Authentication
- Configuring Authorization
- Configuring Accounting
- RADIUS and TACACS + Attributes
- Configuring Kerberos
Configuring AutoSecure
The AutoSecure feature disables common IP services that can be exploited for network attacks and enables IP services and features that can aid in the defense of a network when under attack. These IP services are all disabled and enabled simultaneously with a single command, which simplifies security configuration on your router. For a complete description of the AutoSecure feature, see AutoSecure .
Configuring Access Lists
Access lists permit or deny network traffic over an interface based on source IP address, destination IP address, or protocol. Access lists are configured as standard or extended. A standard access list either permits or denies passage of packets from a designated source. An extended access list allows designation of both the destination and the source, and it allows designation of individual protocols to be permitted or denied passage.
For more complete information on creating access lists, see the “Access Control Lists (ACLs)” section in http://www.cisco.com/en/US/docs/ios/sec_data_plane/configuration/guide/12_4t/sec_data_plane_12_4t_book.html Cisco IOS Security Configuration Guide: Securing the Data Plane, Release 12.4T.
An access list is a series of commands with a common tag to bind them together. The tag is either a number or a name. Table below lists the commands used to configure access lists.
|
ACL Type |
Configuration Commands |
|---|---|
|
Numbered |
|
|
Standard |
access-list 1-99}{permit | deny} source-addr [source-mask] |
|
Extended |
access-list 100-199}{permit | deny} protocol source-addr [source-mask] destination-addr [destination-mask] |
|
Named |
|
|
Standard |
ip access-list standard name deny {source | source-wildcard | any} |
|
Extended |
ip access-list extended name {permit | deny} protocol {source-addr[source-mask] | any}{destination-addr [destination-mask] | any} |
To create, refine, and manage access lists, see the “Access Control Lists (ACLs)” section in http://www.cisco.com/en/US/docs/ios/sec_data_plane/configuration/guide/12_4t/sec_data_plane_12_4t_book.html Cisco IOS Security Configuration Guide: Securing the Data Plane, Release 12.4T :
Access Groups
An access group is a sequence of access list definitions bound together with a common name or number. This group is enabled for an interface during interface configuration. Use the following guidelines when creating access groups.
- The order of access list definitions is significant. A packet is compared against the first access list in the sequence. If there is no match (that is, if neither a permit nor a deny occurs), the packet is compared with the next access list, and so on.
- All parameters must match the access list before the packet is permitted or denied.
- There is an implicit “deny all” at the end of all sequences.
For information on configuring and managing access groups, see http://www.cisco.com/en/US/docs/ios/sec_data_plane/configuration/guide/12_4t/sec_data_plane_12_4t_book.html Cisco IOS Security Configuration Guide: Securing the Data Plane, Release 12.4T.
Configuring Cisco IOS Firewall
The Cisco IOS Firewall lets you configure a stateful firewall in which packets are inspected internally and the state of network connections is monitored. A stateful firewall is superior to static access lists because access lists can only permit or deny traffic based on individual packets, not based on streams of packets. Also, because Cisco IOS Firewall inspects the packets, decisions to permit or deny traffic can be made by examining application layer data, which static access lists cannot examine.
To configure a Cisco IOS Firewall, specify which protocols to examine by using the following command in interface configuration mode:
ip inspect name inspection-name protocol timeout seconds
When inspection detects that the specified protocol is passing through the firewall, a dynamic access list is created to allow the passage of return traffic. The timeout parameter specifies the length of time the dynamic access list remains active without return traffic passing through the router. When the timeout value is reached, the dynamic access list is removed, and subsequent packets (possibly valid ones) are not permitted.
Use the same inspection name in multiple statements to group them into one set of rules. This set of rules can be activated elsewhere in the configuration by using the ip inspect inspection-name {in | out} command when you configure an interface at the firewall.
For additional information about configuring a Cisco IOS Firewall, see http://www.cisco.com/en/US/docs/ios/sec_data_plane/configuration/guide/12_4t/sec_data_plane_12_4t_book.html Cisco IOS Security Configuration Guide: Securing the Data Plane, Release 12.4T .
The Cisco IOS Firewall may also be configured to provide voice security in Session Initiated Protocol (SIP) applications. SIP inspection provides basic inspect functionality (SIP packet inspection and detection of pin-hole openings), as well protocol conformance and application security. For more information, see Cisco IOS Firewall: SIP Enhancements: ALG and AIC .
Configuring Cisco IOS IPS
Cisco IOS Intrusion Prevention System (IPS) technology is available on Cisco 880 series ISRs and enhances perimeter firewall protection by taking appropriate action on packets and flows that violate the security policy or represent malicious network activity.
Cisco IOS IPS identifies attacks using “signatures” to detect patterns of misuse in network traffic. Cisco IOS IPS acts as an in-line intrusion detection sensor, watching packets and sessions as they flow through the router, scanning each to match known IPS signatures. When Cisco IOS IPS detects suspicious activity, it responds before network security can be compromised, it logs the event, and, depending on configuration, it does one of the following:
- Sends an alarm
- Drops suspicious packets
- Resets the connection
- Denies traffic from the source IP address of the attacker for a specified amount of time
- Denies traffic on the connection for which the signature was seen for a specified amount of time
For additional information about configuring Cisco IOS IPS, see http://www.cisco.com/en/US/docs/ios/sec_data_plane/configuration/guide/12_4t/sec_data_plane_12_4t_book.html Cisco IOS Security Configuration Guide: Securing the Data Plane, Release 12.4T .
URL Filtering
Cisco 860 series and Cisco 880 series ISRs provide category based URL filtering. The user provisions URL filtering on the ISR by selecting categories of websites to be permitted or blocked. An external server, maintained by a third party, is used to check for URLs in each category. Permit and deny policies are maintained on the ISR. The service is subscription based, and the URLs in each category are maintained by the third-party vendor.
For additional information about configuring URL filtering, see http://www.cisco.com/en/US/docs/ios/sec_data_plane/configuration/guide/sec_url_filtering.html Subscription-based Cisco IOS Content Filtering guide .
Configuring VPN
A VPN connection provides a secure connection between two networks over a public network such as the Internet. Cisco 860 and Cisco 880 series ISRs support two types of VPNs; site-to-site and remote access. Site-to-site VPNs are used to connect branch offices to corporate offices, for example. Remote access VPNs are used by remote clients to log into a corporate network. Two examples are given in this section: remote access VPN and site-to-site VPN.
Remote Access VPN
The configuration of a remote access VPN uses Cisco Easy VPN and an IP Security (IPSec) tunnel to configure and secure the connection between the remote client and the corporate network. Figure below shows a typical deployment scenario.
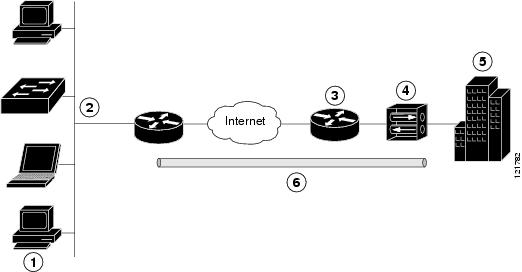
|
1 |
Remote networked users |
|
2 |
VPN client—Cisco 880 series access router |
|
3 |
Router—Providing the corporate office network access |
|
4 |
VPN server—Easy VPN server; for example, a Cisco VPN 3000 concentrator with outside interface address 210.110.101.1 |
|
5 |
Corporate office with a network address of 10.1.1.1 |
|
6 |
IPSec tunnel |
The Cisco Easy VPN client feature eliminates much of the tedious configuration work by implementing the Cisco Unity Client protocol. This protocol allows most VPN parameters, such as internal IP addresses, internal subnet masks, DHCP server addresses, Windows Internet Naming Service (WINS) server addresses, and split-tunneling flags to be defined at a VPN server, such as a Cisco VPN 3000 series concentrator that is acting as an IPSec server.
A Cisco Easy VPN server-enabled device can terminate VPN tunnels initiated by mobile and remote workers who are running Cisco Easy VPN Remote software on PCs. Cisco Easy VPN server-enabled devices allow remote routers to act as Cisco Easy VPN Remote nodes.
The Cisco Easy VPN client feature can be configured in one of two modes: client mode or network extension mode. Client mode is the default configuration and allows only devices at the client site to access resources at the central site. Resources at the client site are unavailable to the central site. Network extension mode allows users at the central site (where the VPN 3000 series concentrator is located) to access network resources on the client site.
After the IPSec server has been configured, a VPN connection can be created with minimal configuration on an IPSec client, such as a supported Cisco 880 series ISR. When the IPSec client initiates the VPN tunnel connection, the IPSec server pushes the IPSec policies to the IPSec client and creates the corresponding VPN tunnel connection.
 Note | The Cisco Easy VPN client feature supports configuration of only one destination peer. If your application requires creation of multiple VPN tunnels, you must manually configure the IPSec VPN and Network Address Translation/Peer Address Translation (NAT/PAT) parameters on both the client and the server. |
Cisco 860 and Cisco 880 series ISRs can also be configured to act as Cisco Easy VPN servers, letting authorized Cisco Easy VPN clients establish dynamic VPN tunnels to the connected network. For information on the configuration of Cisco Easy VPN servers see http://www.cisco.com/c/en/us/support/docs/cloud-systems-management/configuration-professional/112037-easyvpn-router-config-ccp-00.html.
Site-to-Site VPN
The configuration of a site-to-site VPN uses IPSec and the generic routing encapsulation (GRE) protocol to secure the connection between the branch office and the corporate network. Figure below shows a typical deployment scenario.
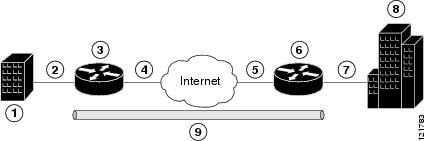
|
1 |
Branch office containing multiple LANs and VLANs |
|
2 |
Fast Ethernet LAN interface—With address 192.165.0.0/16 (also the inside interface for NAT) |
|
3 |
VPN client—Cisco 860 or Cisco 880 series ISR |
|
4 |
Fast Ethernet or ATM interface—With address 200.1.1.1 (also the outside interface for NAT) |
|
5 |
LAN interface—Connects to the Internet; with outside interface address of 210.110.101.1 |
|
6 |
VPN client—Another router, which controls access to the corporate network |
|
7 |
LAN interface—Connects to the corporate network, with inside interface address of 10.1.1.1 |
|
8 |
Corporate office network |
|
9 |
IPSec tunnel with GRE |
For more information about IPSec and GRE configuration, see http://www.cisco.com/c/en/us/td/docs/ios-xml/ios/security/config_library/12-4t/secon-12-4t-library.html Cisco IOS Security Configuration Guide: Secure Connectivity, Release 12.4T .
Configuration Examples
Each example configures a VPN over an IPSec tunnel, using the procedure given in the Configuring a VPN over an IPSec Tunnel. The specific procedure for a remote access configuration is given, followed by the specific procedure for a site-to-site configuration.
The examples shown in this chapter apply only to the endpoint configuration on the Cisco 860 and Cisco 880 ISRs. Any VPN connection requires both endpoints be configured properly to function. See the software configuration documentation as needed to configure the VPN for other router models.
VPN configuration information must be configured on both endpoints. You must specify parameters, such as internal IP addresses, internal subnet masks, DHCP server addresses, and Network Address Translation (NAT).
- Configuring a VPN over an IPSec Tunnel
- Creating a Cisco Easy VPN Remote Configuration
- Configuring a Site-to-Site GRE Tunnel
Configuring a VPN over an IPSec Tunnel
Perform the following tasks to configure a VPN over an IPSec tunnel:
- Configuring the IKE Policy
- Configuring Group Policy Information
- Applying Mode Configuration to the Crypto Map
- Enabling Policy Lookup
- Configuring IPSec Transforms and Protocols
- Configuring the IPSec Crypto Method and Parameters
- Applying the Crypto Map to the Physical Interface
Configuring the IKE Policy
To configure the Internet Key Exchange (IKE) policy, perform these steps, beginning in global configuration mode:
1.
crypto
isakmp
policy
priority
2.
encryption
{des
|
3des
|
aes
|
aes
192
|
aes
256}
3.
hash
{md5
|
sha}
4. authentication {rsa-sig | rsa-encr | pre-share}
5. group {1 | 2 | 5}
6. lifetime seconds
7. exit
DETAILED STEPS
Configuring Group Policy Information
To configure the group policy, perform these steps, beginning in global configuration mode:
1. crypto isakmp client configuration group {group-name | default}
2.
key
name
3.
dns
primary-server
4.
domain
name
5.
exit
6. ip local pool {default | poolname} [low-ip-address [high-ip-address]]
DETAILED STEPS
| Command or Action | Purpose | |||
|---|---|---|---|---|
| Step 1 | crypto
isakmp
client
configuration
group {group-name
|
default}
Example: Router(config)# crypto isakmp client configuration group rtr-remote |
Creates an IKE policy group containing attributes to be downloaded to the remote client. Also enters the Internet Security Association Key and Management Protocol (ISAKMP) group policy configuration mode. | ||
| Step 2 | key
name
Example: Router(config-isakmp-group)# key secret-password |
Specifies the IKE pre-shared key for the group policy. | ||
| Step 3 | dns
primary-server
Example: Router(config-isakmp-group)# dns 10.50.10.1 |
Specifies the primary Domain Name System (DNS) server for the group.
| ||
| Step 4 | domain
name
Example: Router(config-isakmp-group)# domain company.com |
Specifies group domain membership. | ||
| Step 5 | exit
Example: Router(config-isakmp-group)# exit Router(config)# |
Exits ISAKMP group policy configuration mode and returns to global configuration mode. | ||
| Step 6 | ip
local
pool
{default |
poolname}
[low-ip-address
[high-ip-address]]
Example: Router(config)# ip local pool dynpool 30.30.30.20 30.30.30.30 |
Specifies a local address pool for the group. For details about this command and additional parameters that can be set, see Cisco IOS Dial Technologies Command Reference . |
Applying Mode Configuration to the Crypto Map
To apply mode configuration to the crypto map, perform these steps, beginning in global configuration mode:
1.
crypto
map
map-name
isakmp
authorization
list
list-name
2.
crypto
map
tag
client
configuration
address
[initiate
|
respond]
DETAILED STEPS
Enabling Policy Lookup
To enable policy lookup through AAA, perform these steps, beginning in global configuration mode:
1.
aaa
new-model
2.
aaa
authentication
login
{default
|
list-name}
method1
[method2...]
3.
aaa
authorization
{network
|
exec
|
commands
level
|
reverse-access
|
configuration}
{default
|
list-name}
[method1
[method2...]]
4.
username
name
{nopassword
|
password
password
|
password
encryption-type
encrypted-password}
DETAILED STEPS
| Command or Action | Purpose | |||
|---|---|---|---|---|
| Step 1 | aaa
new-model
Example: Router(config)# aaa new-model |
Enables the AAA access control model. | ||
| Step 2 | aaa
authentication
login
{default
|
list-name}
method1
[method2...]
Example: Router(config)# aaa authentication login rtr-remote local |
Specifies AAA authentication of selected users at login, and specifies the method used.
| ||
| Step 3 | aaa
authorization
{network
|
exec
|
commands
level
|
reverse-access
|
configuration}
{default
|
list-name}
[method1
[method2...]]
Example: Router(config)# aaa authorization network rtr-remote local |
Specifies AAA authorization of all network-related service requests, including PPP, and specifies the method of authorization.
| ||
| Step 4 | username
name
{nopassword
|
password
password
|
password
encryption-type
encrypted-password}
Example: Router(config)# username username1 password 0 password1 |
Establishes a username-based authentication system. |
Configuring IPSec Transforms and Protocols
A transform set represents a certain combination of security protocols and algorithms. During IKE negotiation, the peers agree to use a particular transform set for protecting data flow.
During IKE negotiations, the peers search in multiple transform sets for a transform that is the same at both peers. When a transform set is found that contains such a transform, it is selected and applied to the protected traffic as a part of both configurations.
To specify the IPSec transform set and protocols, perform these steps, beginning in global configuration mode:
1.
crypto
ipsec
profile
profile-name
2.
crypto
ipsec
transform-set
transform-set-name
transform1
[transform2]
[transform3]
[transform4]
3.
crypto
ipsec
security-association
lifetime
{seconds
seconds
|
kilobytes
kilobytes}
DETAILED STEPS
| Command or Action | Purpose | |
|---|---|---|
| Step 1 | crypto
ipsec
profile
profile-name
Example: Router(config)# crypto ipsec profile pro1 |
Configures IPSec profile to apply protection on the tunnel for encryption. |
| Step 2 | crypto
ipsec
transform-set
transform-set-name
transform1
[transform2]
[transform3]
[transform4]
Example: Router(config)# crypto ipsec transform-set vpn1 esp-3des esp-sha-hmac |
Defines a transform set—an acceptable combination of IPSec security protocols and algorithms. See Cisco IOS Security Configuration Guide: Secure Connectivity, Release 12.4T for details about the valid transforms and combinations. |
| Step 3 | crypto
ipsec
security-association
lifetime
{seconds
seconds
|
kilobytes
kilobytes}
Example: Router(config)# crypto ipsec security-association lifetime seconds 86400 |
Specifies global lifetime values used when IPSec security associations are negotiated. |
Configuring the IPSec Crypto Method and Parameters
A dynamic crypto map policy processes negotiation requests for new security associations from remote IPSec peers, even if the router does not know all the crypto map parameters (for example, IP address).
To configure the IPSec crypto method, perform these steps, beginning in global configuration mode:
1.
crypto
dynamic-map
dynamic-map-name
dynamic-seq-num
2.
set
transform-set
transform-set-name
[transform-set-name2...transform-set-name6]
3.
reverse-route
4.
exit
5.
crypto
map
map-name
seq-num
[ipsec-isakmp]
[dynamic
dynamic-map-name]
[discover]
[profile
profile-name]
DETAILED STEPS
| Command or Action | Purpose | |
|---|---|---|
| Step 1 | crypto
dynamic-map
dynamic-map-name
dynamic-seq-num
Example: Router(config)# crypto dynamic-map dynmap 1 |
Creates a dynamic crypto map entry and enters crypto map configuration mode. See Cisco IOS Security Command Reference for more details about this command. |
| Step 2 | set
transform-set
transform-set-name
[transform-set-name2...transform-set-name6]
Example: Router(config-crypto-map)# set transform-set vpn1 |
Specifies which transform sets can be used with the crypto map entry. |
| Step 3 | reverse-route
Example: Router(config-crypto-map)# reverse-route |
Creates source proxy information for the crypto map entry. See Cisco IOS Security Command Reference for details. |
| Step 4 | exit
Example: Router(config-crypto-map)# exit |
Exits crypto map configuration mode and returns to global configuration mode. |
| Step 5 | crypto
map
map-name
seq-num
[ipsec-isakmp]
[dynamic
dynamic-map-name]
[discover]
[profile
profile-name]
Example: Router(config)# crypto map static-map 1 ipsec-isakmp dynamic dynmap |
Creates a crypto map profile. |
Applying the Crypto Map to the Physical Interface
The crypto maps must be applied to each interface through which IPSec traffic flows. Applying the crypto map to the physical interface instructs the router to evaluate all the traffic against the security associations database. With the default configurations, the router provides secure connectivity by encrypting the traffic sent between remote sites. However, the public interface still allows the rest of the traffic to pass and provides connectivity to the Internet.
To apply a crypto map to an interface, perform these steps, beginning in global configuration mode:
1.
interface
type
number
2.
crypto
map
map-name
3.
exit
DETAILED STEPS
| Command or Action | Purpose | |
|---|---|---|
| Step 1 | interface
type
number
Example: Router(config)# interface fastethernet 4 |
Enters the interface configuration mode for the interface to which the crypto map will be applied. |
| Step 2 | crypto
map
map-name
Example: Router(config-if)# crypto map static-map |
Applies the crypto map to the interface.
|
| Step 3 | exit
Example: Router(config-crypto-map)# exit Router(config)# |
Exits interface configuration mode and returns to global configuration mode. |
Where to Go Next
If you are creating a Cisco Easy VPN remote configuration, go to the Creating a Cisco Easy VPN Remote Configuration.
If you are creating a site-to-site VPN using IPSec tunnels and GRE, go to the Configuring a Site-to-Site GRE Tunnel.
Creating a Cisco Easy VPN Remote Configuration
The router acting as the Cisco Easy VPN client must create a Cisco Easy VPN remote configuration and assign it to the outgoing interface.
To create the remote configuration, perform these steps, beginning in global configuration mode:
1.
crypto
ipsec
client
ezvpn
name
2.
group
group-name
key
group-key
3.
peer
{ipaddress
|
hostname}
4. mode {client | network-extension | network extension plus}
5.
exit
6.
crypto
isakmp
keepalive
seconds
7.
interface
type
number
8.
crypto
ipsec
client
ezvpn
name
[outside
|
inside]
9.
exit
DETAILED STEPS
Configuration Example
The following configuration example shows a portion of the configuration file for the VPN and IPSec tunnel described in this chapter.
! aaa new-model ! aaa authentication login rtr-remote local aaa authorization network rtr-remote local aaa session-id common ! username Cisco password 0 Cisco ! crypto isakmp policy 1 encryption 3des authentication pre-share group 2 lifetime 480 ! crypto isakmp client configuration group rtr-remote key secret-password dns 10.50.10.1 10.60.10.1 domain company.com pool dynpool ! crypto ipsec transform-set vpn1 esp-3des esp-sha-hmac ! crypto ipsec security-association lifetime seconds 86400 ! crypto dynamic-map dynmap 1 set transform-set vpn1 reverse-route ! crypto map static-map 1 ipsec-isakmp dynamic dynmap crypto map dynmap isakmp authorization list rtr-remote crypto map dynmap client configuration address respond crypto ipsec client ezvpn ezvpnclient connect auto group 2 key secret-password mode client peer 192.168.100.1 ! interface fastethernet 4 crypto ipsec client ezvpn ezvpnclient outside crypto map static-map ! interface vlan 1 crypto ipsec client ezvpn ezvpnclient inside !
Configuring a Site-to-Site GRE Tunnel
To configure a GRE tunnel, perform these steps, beginning in global configuration mode:
1.
interface
type
number
2.
ip
address
ip-address
mask
3.
tunnel
source
interface-type
number
4.
tunnel
destination
default-gateway-ip-address
5.
crypto
map
map-name
6.
exit
7. ip access-list {standard | extended}access-list-name
8.
permit
protocol
source
source-wildcard
destination
destination-wildcard
9.
exit
DETAILED STEPS
| Command or Action | Purpose | |||
|---|---|---|---|---|
| Step 1 | interface
type
number
Example: Router(config)# interface tunnel 1 |
Creates a tunnel interface and enters interface configuration mode. | ||
| Step 2 | ip
address
ip-address
mask
Example: Router(config-if)# 10.62.1.193 255.255.255.252 |
Assigns an address to the tunnel. | ||
| Step 3 | tunnel
source
interface-type
number
Example: Router(config-if)# tunnel source fastethernet 0 |
Specifies the source endpoint of the router for the GRE tunnel. | ||
| Step 4 | tunnel
destination
default-gateway-ip-address
Example: Router(config-if)# tunnel destination 192.168.101.1 |
Specifies the destination endpoint of the router for the GRE tunnel. | ||
| Step 5 | crypto
map
map-name
Example: Router(config-if)# crypto map static-map |
Assigns a crypto map to the tunnel.
| ||
| Step 6 | exit
Example: Router(config-if)# exit |
Exits interface configuration mode, and returns to global configuration mode. | ||
| Step 7 | ip
access-list
{standard
|
extended}access-list-name
Example: Router(config)# ip access-list extended vpnstatic1 |
Enters ACL configuration mode for the named ACL that is used by the crypto map. | ||
| Step 8 | permit
protocol
source
source-wildcard
destination
destination-wildcard
Example: Router(config-acl)# permit gre host 192.168.100.1 host 192.168.101.1 |
Specifies that only GRE traffic is permitted on the outbound interface. | ||
| Step 9 | exit
Example: Router(config-acl)# exit Router(config)# |
Exits ACL configuration mode and returns to global configuration mode. |
Configuration Example
The following configuration example shows a portion of the configuration file for a VPN using a GRE tunnel scenario described in the preceding sections.
! aaa new-model ! aaa authentication login rtr-remote local aaa authorization network rtr-remote local aaa session-id common ! username cisco password 0 cisco ! interface tunnel 1 ip address 10.62.1.193 255.255.255.252 tunnel source fastethernet 0 tunnel destination interface 192.168.101.1 ip route 20.20.20.0 255.255.255.0 tunnel 1 crypto isakmp policy 1 encryption 3des authentication pre-share group 2 ! crypto isakmp client configuration group rtr-remote key secret-password dns 10.50.10.1 10.60.10.1 domain company.com pool dynpool ! crypto ipsec transform-set vpn1 esp-3des esp-sha-hmac ! crypto ipsec security-association lifetime seconds 86400 ! crypto dynamic-map dynmap 1 set transform-set vpn1 reverse-route ! crypto map static-map 1 ipsec-isakmp dynamic dynmap crypto map dynmap isakmp authorization list rtr-remote crypto map dynmap client configuration address respond ! ! Defines the key association and authentication for IPsec tunnel. crypto isakmp policy 1 hash md5 authentication pre-share crypto isakmp key cisco123 address 200.1.1.1 ! ! ! Defines encryption and transform set for the IPsec tunnel. crypto ipsec transform-set set1 esp-3des esp-md5-hmac ! ! Associates all crypto values and peering address for the IPsec tunnel. crypto map to_corporate 1 ipsec-isakmp set peer 200.1.1.1 set transform-set set1 match address 105 ! ! ! VLAN 1 is the internal home network. interface vlan 1 ip address 10.1.1.1 255.255.255.0 ip nat inside ip inspect firewall in ! Inspection examines outbound traffic. crypto map static-map no cdp enable ! ! FE4 is the outside or Internet-exposed interface interface fastethernet 4 ip address 210.110.101.21 255.255.255.0 ! acl 103 permits IPsec traffic from the corp. router as well as ! denies Internet-initiated traffic inbound. ip access-group 103 in ip nat outside no cdp enable crypto map to_corporate ! Applies the IPsec tunnel to the outside interface. ! ! Utilize NAT overload in order to make best use of the ! single address provided by the ISP. ip nat inside source list 102 interface Ethernet1 overload ip classless ip route 0.0.0.0 0.0.0.0 210.110.101.1 no ip http server ! ! ! acl 102 associated addresses used for NAT. access-list 102 permit ip 10.1.1.0 0.0.0.255 any ! acl 103 defines traffic allowed from the peer for the IPsec tunnel. access-list 103 permit udp host 200.1.1.1 any eq isakmp access-list 103 permit udp host 200.1.1.1 eq isakmp any access-list 103 permit esp host 200.1.1.1 any ! Allow ICMP for debugging but should be disabled because of security implications. access-list 103 permit icmp any any access-list 103 deny ip any any ! Prevents Internet-initiated traffic inbound. ! acl 105 matches addresses for the IPsec tunnel to or from the corporate network. access-list 105 permit ip 10.1.1.0 0.0.0.255 192.168.0.0 0.0.255.255 no cdp run
Cisco ScanSafe
The Cisco Integrated Services Router G2 (ISR G2) family delivers numerous security services, including firewall, intrusion prevention, and VPN. These security capabilities have been extended with Cisco ISR Web Security with Cisco ScanSafe for a web security and web filtering solution that requires no additional hardware or client software.
Cisco ISR Web Security with Cisco ScanSafe enables branch offices to intelligently redirect web traffic to the cloud to enforce granular security and acceptable use policies over user web traffic. With this solution, you can deploy market-leading web security quickly and can easily protect branch office users from web-based threats, such as viruses, while saving bandwidth, money, and resources.
For more information, see Cisco ISR Web Security with Cisco ScanSafe Solution Guide.
 Feedback
Feedback