Traffic storm control has the following configuration guidelines and limitations:
-
The storm control feature does not work if you enable storm control on an interface where sFlow is also enabled.
-
Storm control PPS option was supported only on Cisco Nexus 9300-FX2 platform switches. Beginning with Cisco NX-OS Release
10.3(2)F, it is also supported on Cisco Nexus 9300-FX3, 9300-GX, and 9300-GX2 platform switches.
-
For Cisco Nexus NFE2-enabled devices, you can use the storm control-cpu to control the number of ARP packets sent to the CPU.
-
Storm control can be configured on physical, port-channel, and breakout interfaces.
-
Specify the traffic storm control level as a percentage of the total interface bandwidth:
-
The pps range can be from 0 to 200000000.
-
The optional fraction of a level can be from 0 to 99.
-
100 percent means no traffic storm control.
-
0.0 percent suppresses all traffic.
-
For Cisco Nexus 9500 Series switches with 9400 Series line cards, and Cisco Nexus 9300 Series switches, you can use the storm control CLI to specify bandwidth level either as a percentage of port
capacity or packets-per-second.
-
Beginning with Cisco Nexus Release 9.2(1), the error margin is greater than 1% when you configure the storm control packets-per-seconds
as follows:
-
Traffic period < 60 s
-
Storm control pps <1000
-
Storm control pps <5 is not supported
-
For 5-1000 pps, 20 additional pps is required to hit storm control in <60 s
-
For >1000 pps, 2.5-3 % additional pps is required to hit storm control in <60 s
-
Beginning with Cisco Nexus Release 9.2(1), you can use the percentage of port capacity or packets-per-second for the Cisco
Nexus 9336C-FX2, Cisco Nexus 93300YC-FX2, and Cisco Nexus 93240YC-FX2-Z switches.
-
If you have configured an SVI for the VLAN on Cisco Nexus 9200, 9300-EX platform switches, or on the N9K-X9700-FX3 line cards, storm control broadcast does not work for ARP traffic (ARP request).
-
Local link and hardware limitations prevent storm-control drops from being counted separately. Instead, storm-control drops
are counted with other drops in the discards counter.
-
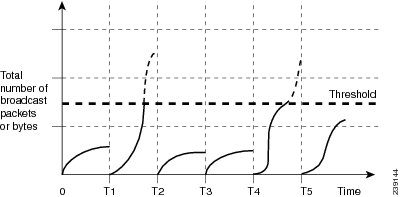
Because of hardware limitations and the method by which packets of different sizes are counted, the traffic storm control
level percentage is an approximation. Depending on the sizes of the frames that make up the incoming traffic, the actual enforced
level might differ from the configured level by several percentage points.
-
Due to a hardware limitation, the output for the show interface counters storm-control command does not show ARP suppression when storm control is configured and the interface is actually suppressing ARP broadcast
traffic. This limitation can lead to the configured action not being triggered but the incoming ARP broadcast traffic being
correctly storm suppressed.
-
Due to a hardware limitation, storm control is not supported for 400G ports beyond 70% of the port bandwidth in Cisco Nexus
GX series platform switches.
-
Due to a hardware limitation, the packet drop counter cannot distinguish between packet drops caused by a traffic storm and
packet drops caused by other discarded input frames. This limitation can lead to the configured action being triggered even
in the absence of a traffic storm.
-
Due to a hardware limitation, storm suppression packet statistics are not supported on uplink ports.
-
Due to a hardware limitation, storm suppression packet statistics do not include broadcast traffic on VLANs with an active
switched virtual interface (SVI).
-
Due to a design limitation, storm suppression packet statistics do not work if the configured level is 0.0, which is meant
to suppress all incoming storm packets.
-
Traffic storm control is supported on the Cisco Nexus 9300 Series switches and the Cisco Nexus 9500 Series switches with the
9700-EX/FX line card.
-
Traffic storm control is not supported on Cisco N9K-M4PC-CFP2.
-
Traffic storm control is not supported on either Host Interface (HIF) or Network Interface (NIF) FEX interfaces.
-
When an interface is shut down (either as a result of storm-control errdisable or due to an administrative shutdown)the Rx
storm suppression drop count may appear slightly lower than the actual number of packets dropped in hardware. This discrepancy
can occur if the last update from the hardware or from internal system processes (such as the tahusd daemon, which relays
hardware statistics to the system) is missed as the interface goes down. The suppressed packet count is fully updated once
the interface returns to the up state.
-
Traffic storm control is only for ingress traffic, specifically for unknown unicast, unknown multicast, and broadcast traffic.

Note
|
On Cisco Nexus 9000 Series switches, traffic storm control applies to unknown unicast traffic and not known unicast traffic
|
-
When port channel members are error disabled due to a configured action, all individual member ports should be flapped to
recover from the error disabled state.
-
Cisco Nexus Release 9.2(1) the traffic storm control feature is not supported on Cisco Nexus 9500 platform switches with the
N9K-X96136YC-R line card and N9K-C9504-FM-R fabric module.
-
Beginning with Cisco Nexus Release 9.2(4), the traffic storm control feature is supported on Cisco Nexus 9500 platform switches
with the N9K-X96136YC-R line card and N9K-C9504-FM-R fabric module. Traffic storm control counters do not increment when the
interface is flooded with the broadcast traffic.
-
Beginning with Cisco Nexus Release 9.3(2), the traffic storm control feature with only rate-limiting is supported on Cisco
Nexus 9500 platform switches with the N9K-X96136YC-R, N9K-X9636C-R, N9K-X9636Q-R, N9K-X9636C-RX line cards, and N9K-C9504-FM-R
and N9K-C9508-FM-R fabric modules. Traffic storm control counters and storm-control action are not supported.
-
The following guidelines and limitations apply to Cisco Nexus 9200 Series switches:
-
Traffic storm control with unknown multicast traffic is not supported.
-
Packet-based statistics are not supported for traffic storm control as the policer supports only byte-based statistics.
-
Traffic storm control is not supported for copy-to-CPU packets.
-
Beginning with Cisco NX-OS Release 10.1(2), Storm Control feature is supported on the N9K-X9624D-R2 and N9K-C9508-FM-R2 platform
switches.
-
Beginning with Cisco Nexus Release 10.1(2), for Cisco Nexus N9300-FX and N9300-FX2 series switches, you can configure a two-level
threshold and logging support for Broadcast, Unknown Unicast, and Multicast (BUM) traffic, and also set trap or shutdown action
for each threshold level. The existing storm control configuration is now used only for one-level threshold.
-
The following guidelines and limitations apply to the two-level threshold and logging support for BUM traffic feature for
Cisco Nexus 10.1(2) release:
-
The new traffic storm control feature in Cisco Nexus Release 10.1(2) supports a maximum of 62 ports (as a single slice) on
Cisco Nexus N9300-FX and a total of 124 ports (as two slices) on Cisco Nexus N9300-FX2.
-
Traffic storm control supports devices that are only in one storm control mode at a time, either one-level or two-level threshold.
It does not support a mix of one-level threshold and two-level threshold storm control mode across ports at a time.
-
Traffic storm control monitors traffic statistics and generates system log for each level (lower and higher) and traffic type
(unknown unicast, multicast, and broadcast) from Cisco Nexus Release 10.1(2).
-
The two-level threshold traffic storm control feature requires carving of a new Ternary Content Addressable Memory (TCAM)
region with a fixed size of 512, and a reload of the device.
-
Traffic storm control for two-level threshold cannot coexist with the L2 Netflow feature, that is, presence of config layer2-switched
flow monitor CLI, because of TCAM resource limitation.
-
The two-level threshold feature for traffic storm control does not support non-IP MC flood traffic (packet without an IP header)
and packets-per-second mode.
-
Traffic storm control is not supported on Generic Online Diagnostics (GOLD) packets and sub-interface level.
-
If you were on a prior release, have upgraded to 10.1(2), and want to use the two-level storm control feature, then make sure
that you configure the switch with the new storm control commands.
-
If you have configured the two-level storm control feature in version 10.1(2), and you want to downgrade to a previous version,
then the new feature does not support downgrade. To downgrade, remove the configuration.
-
Beginning from Cisco Nexus Release 10.2(1), Storm control does not allow to have multiple action configurations on an interface.
If the previous action value is overwritten, then it considers the latest action value that is configured.
-
Beginning with Cisco NX-OS Release 10.2(2)F, the storm control feature is supported on Cisco N9K-9332D-GX2B platform switches.
-
Beginning with Cisco NX-OS Release 10.3(2)F, Traffic Storm Control is supported on Layer 3 interfaces, and the following guidelines
and limitations are applicable:
-
Traffic storm control supports devices that are only on one-level threshold storm control mode.
-
Layer 3 packets destined for the control plane such as ARP broadcast are not suppressed by storm control and are policed by
the CoPP policer. However, storm control violation actions are triggered.
-
This feature is supported only on Cisco Nexus 9300-FX, 9300-FX2, 9300-FX3, 9300-GX, and 9300-GX2 platform switches, and Cisco
Nexus 9500 Series switches with FX and GX line cards.
-
Beginning with Cisco NX-OS Release 10.3(3)F, the system storm-control priority-policy drop-l3 command is introduced to prioritize storm control drop over the CoPP policer, and the following guidelines and limitations
are applicable:
-
This feature applies to Layer 3 control frames.
-
This feature is supported only on Cisco Nexus 9300-FX, 9300-FX2, 9300-FX3, 9300-GX, and 9300-GX2 platform switches, and Cisco
Nexus 9500 Series switches with FX and GX line cards.
-
This feature is applicable only for one-level threshold traffic storm control.

 Feedback
Feedback