New and Changed Information
The following table provides an overview of the significant changes up to this current release. The table does not provide an exhaustive list of all changes or of the new features up to this release.
| Release Version | Feature | Description |
|---|---|---|
|
Nexus Dashboard 4.2.1 |
Improved image management and switch software update workflow. |
Beginning with Nexus Dashboard 4.2.1, the workflow to update switch software and manage fabric software images in Nexus Dashboard have been enhanced. For more information, see Upgrade or downgrade switches in a fabric under Overview tab. |
|
Nexus Dashboard 4.2.1 |
Support for Cisco Catalyst 8000 switches |
Beginning with Nexus Dashboard 4.2.1, Nexus Dashboard supports software update for Cisco Catalyst 8000 switches. For more information, see Understand the information provided in the Fabric Software page for NX-OS and IOS-XE fabrics. |
Understand Fabric Software for NX-OS and IOS-XE fabrics
This section provides detailed information for the Fabric Software feature in Nexus Dashboard for NX-OS/IOS-XE fabrics.
Fabric Software deploys Cisco software images to switches which allows network stability and feature consistency. Fabric Software workflows provide these benefits:
-
Image staging, validation, and in-service software upgrade (ISSU) operations which are independent, allowing mass updates and downgrades, and the ability to perform staging and validation in a single step
-
You can perform these operations before the maintenance window.
-
Stage image files
This copies the image files to the switch bootflash.
-
Validate Network Operating System (NOS) and electronic programmable logic device (EPLD) compatibility where possible
This checks if the image is complete, if the image is valid for the individual hardware, and if the update can be non-disruptive.
-
Run Update Analysis reports
-
-
-
The ability to run reports and compare the results
-
The View Logs column provides Live log status to monitor each operation
-
Allows you to make use of maintenance mode to minimize the impact of disruptive updates, especially for multi-reload update situations
-
Update groups allow bulk updates and downgrades. Update groups have checks to avoid unnecessary downtime in redundant fabrics in these cases:
-
Switches belonging to different fabrics are not allowed to form an update group.
-
By default, Virtual Port Channel (vPC) peers are placed in different groups as listed:
-
Switches that have even numbers or VPC role of primary
-
Switches that have odd numbers or VPC role of secondary
-
-
-
Provides visibility into previous and current update details as well as high-level summarization
-
Visibility into current NOS, EPLD and patch consistency at a switch, fabric, and group level
Navigate to the Fabric Software page for NX-OS and IOS-XE fabrics
To navigate to the Fabric Software page, click Manage > Fabric Software.
The NX-OS/IOS-XE tab is the default view.
Understand the information provided in the Fabric Software page for NX-OS and IOS-XE fabrics
The Overview tab provides fabric-level update and downgrade options whereas the Devices tab provides these options at the individual device or switch level.
The Overview tab displays the images, platforms, release versions, and fabric information.
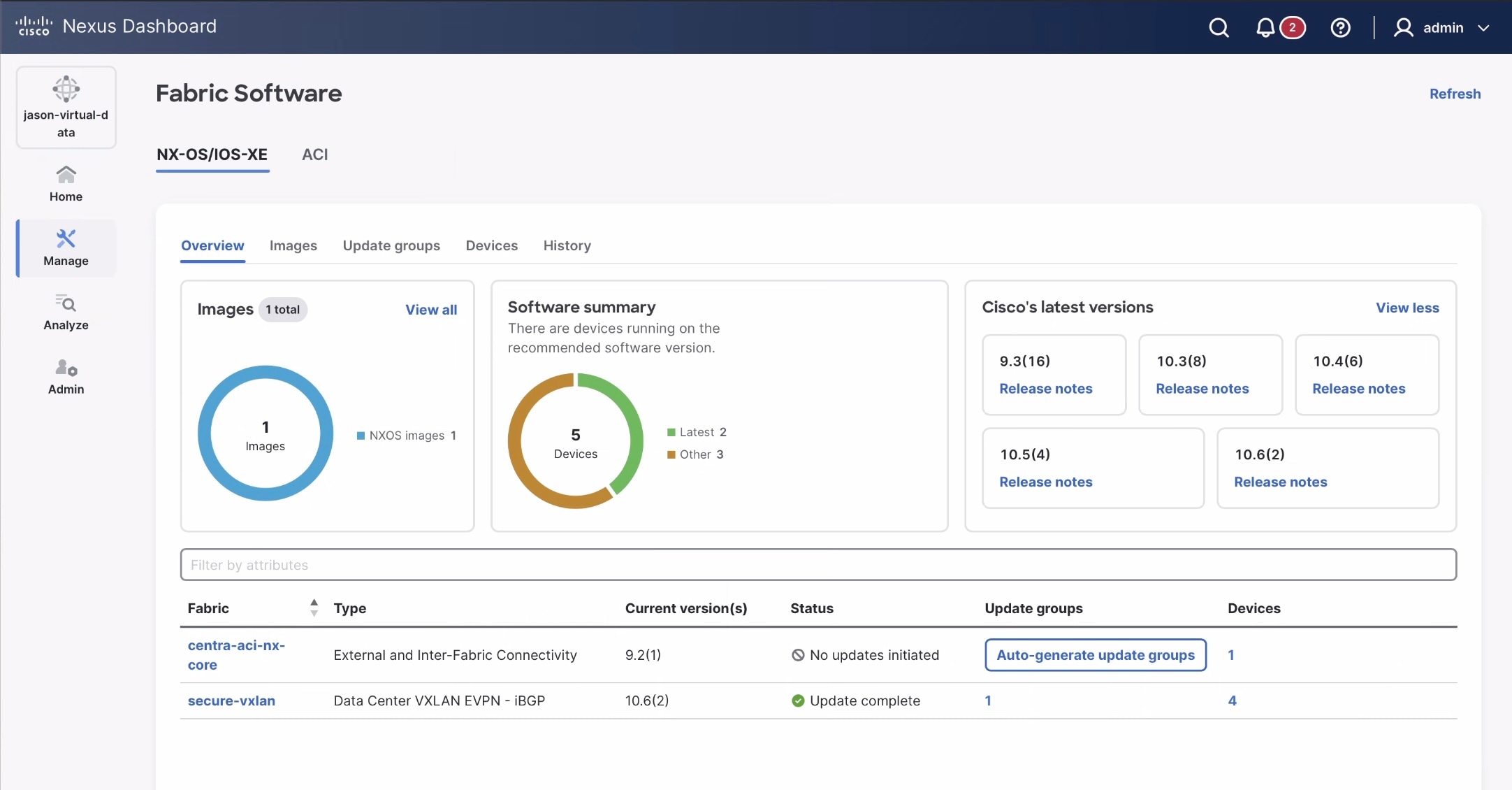
The Fabric Software page has the following functional areas:
-
Overview: This displays the images, platforms, release versions, and fabric information.
-
The Images card displays the number of images and the type of packages or patches. Click View all to see a table with a detailed listing of all the images.
-
The Cisco’s latest versions card displays the latest versions of the switch software that are available, the versions of the switch software that Cisco recommends, and the corresponding release notes.
-
The fabric area displays information about the configured fabrics.
-
|
Field |
Description |
|
Fabric |
The name of the fabric. |
|
Type |
The type of fabric. |
|
Current version(s) |
The current versions of software running on the switches in the fabric. |
|
Status |
The status of the fabric-level software update. The available options are:
|
|
Update groups |
A clickable link to the update groups page for a fabric or an option to Auto-generate update groups, if the update group is not available. |
|
Devices |
A clickable link to the devices page with a detailed listing of the number of switches in a fabric. |
-
Images: This displays the details of the uploaded images on Nexus Dashboard. You can upload or delete images.
|
Field |
Description |
|
Platform |
Specifies the name of the platform. Images, RPMs, or SMUs are categorized as follows:
The images are the same for n9k and n3k platforms. The platform is Other if the uploaded images are not mapped to any of the existing platforms. The platform is n9k/n3k for RPMs. |
|
Bits |
Specifies the bits of the image |
|
Image name |
Specifies the filename of the image, RPM, or SMU that you uploaded. |
|
Image type |
Specifies the file type. The available options are image, EPLD, RPM, and SMU. |
|
Image sub type |
Specifies the file type of the image, EPLD, RPM, or SMU as listed here:
|
|
NOS version |
Specifies the NX-OS or IOS-XE image version for Cisco switches only. |
|
Size (Bytes) |
Specifies the size of the image, RPM, or SMU files in bytes. |
|
Image present |
Determines if the uploaded image is present after a successful Nexus Dashboard restore or update process. Switch firmware images that were uploaded to Nexus Dashboard in release 3.2.x are not carried over when you update to Nexus Dashboard 4.x. These instances are listed as Absent in the Image Present column. After updating to Nexus Dashboard 4.x, re-upload the switch firmware images. However, images uploaded to Nexus Dashboard in release 4.1.1 are carried over when you update to Nexus Dashboard 4.2.1. For more information, see Upload the image to Nexus Dashboard. |
|
Checksum |
Specifies the checksum of the image. The checksum checks if there’s any corruption in the file of the image, RPM, or SMU. You can validate the authenticity by verifying if the checksum value is same for the file you downloaded from the Cisco website and the file you upload in the Image Upload. |
-
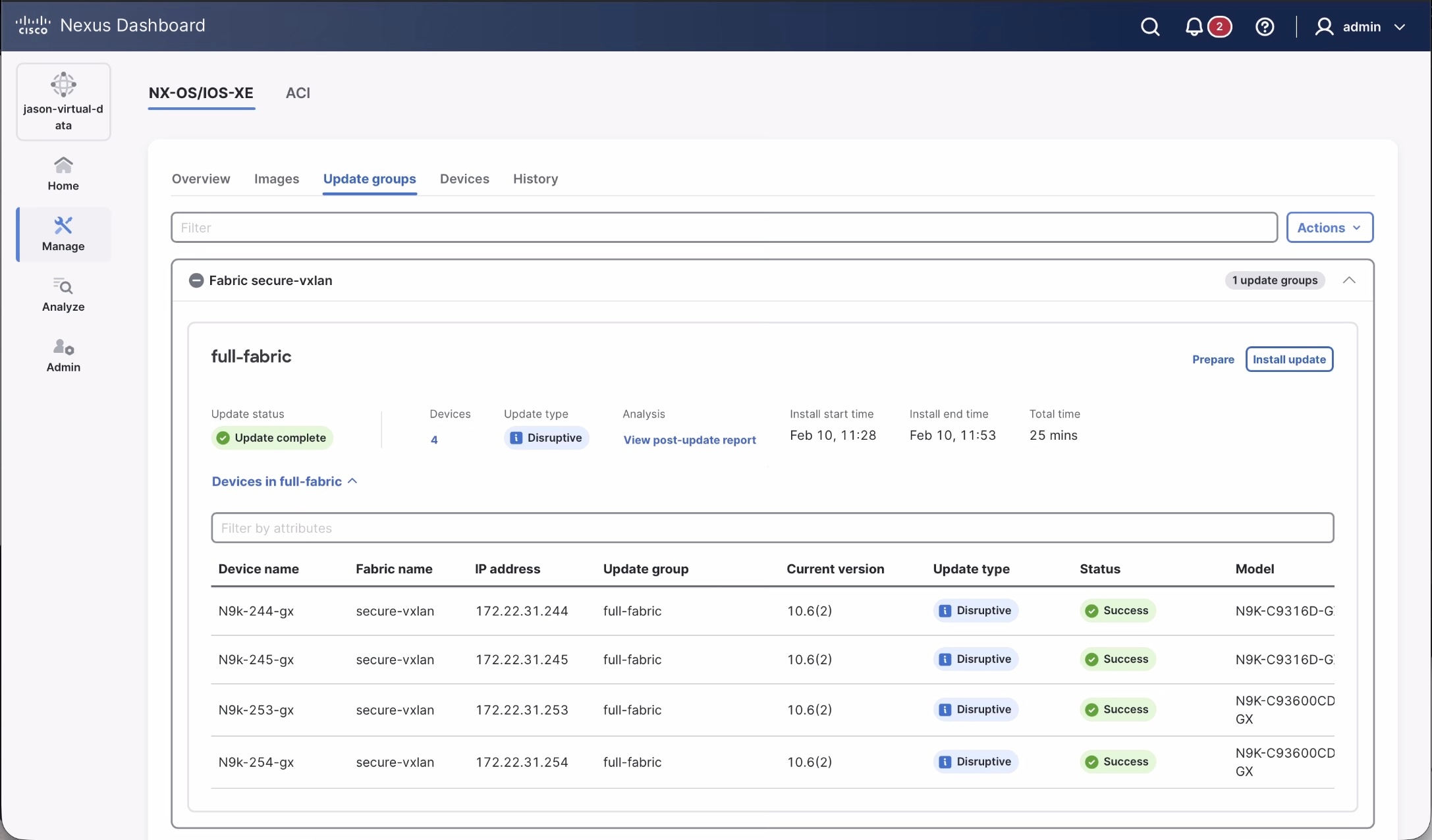
Update groups: This displays switch updates by groups. You can Prepare, Install update, and check Update status. This allows you to easily stage groups in advance and return to the update workflow at any point. You can also:
-
create auto-update groups
-
view pre or post-update reports
-
view update logs, or
-
access switch bootflash or hardware to check or delete images from the switch bootflash.
Devices that are not associated with any update group are listed under None. For information about assigning an update group to a device, see Attach or detach update groups to the switches.
-
-
Review the information provided in the Update groups area.
-
Fabric: The name of the fabric
-
Count of update groups: Next to the fabric name, the number of update groups created for a specific fabric
-
Update group name: The name of the update group where you can install or update the software on the devices in that fabric
-
About <time> minutes: Next to the Update group name, the approximate time needed for the update is listed. This appears only after Prepare.
-
Prepare: To prepare a software update that can be used at the update group level
-
Install update: To initiate software update installation
-
Update status: The status of the update. This can be No status, Update complete, or Update failed.
-
Devices: Shows the number of devices in this update group.
-
Update Type: Shows the nature of the update. This can be either Disruptive or Non-disruptive.
-
Analysis: Shows if any warnings are triggered prior to the update. Click View pre-update report or View post-update report for detailed information.
-
Install start time: Shows the time when the update installation starts.
-
Install end time: Shows the time when the update installation ends.
-
Total time: Shows the total time taken for the update installation.
-
-
Devices: This displays the devices in a fabric-level update group. You can Prepare update group, Install update group, Modify groups, or Resync the software on the selected device(s). Use the gear icon to customize the columns displayed in the table.
|
Field |
Description |
|
Device name |
Specifies the name of the device. |
|
Fabric name |
Specifies the fabric that the device resides in. |
|
Recommended version |
Specifies the Cisco recommended version of NX-OS images for the specific Cisco switch. |
|
Latest version in train |
Specifies the most recent NX-OS image version for the specific Cisco switches on the corresponding release train. |
|
Current version |
Specifies the NX-OS or IOS-XE image version currently running on the corresponding Cisco switch. |
|
Latest version |
Specifies the highest numbered NX-OS image version for the specific Cisco switch on the corresponding release train. |
|
Version status |
Specifies the software status on the device. The available options listed in descending order of priority are:
The version status column displays None for the non-n9k devices. |
|
IP address |
Specifies the IP address of the device. |
|
Update Type |
Shows the nature of update. This can be either Disruptive or Non-disruptive. |
|
Status |
Specifies the configuration status. These include:
|
|
System mode |
Specifies the mode of the switch at a given instant. These include:
|
|
Role |
Specifies the role for the switch. |
|
Analysis |
Provides an analysis of the update if the pre or post-update report are generated. |
|
Model |
Specifies the switch model. |
|
Update group |
Specifies the name of the upgrade group. |
|
Logs |
Provides a link to View logs. |
|
VPC Role |
Specifies the VPC role, if applicable (Primary or Secondary). |
|
VPC Peer |
Specifies which switch is the VPC peer with this switch, if applicable. |
-
History: This displays the history of all the operations performed on the switches.
|
Field |
Description |
|
ID |
Specifies the ID number. |
|
Device Name |
Specifies the device name. |
|
Version |
Specifies the version of the image on the device. |
|
Status |
Displays if the operation was a success or failure. |
|
Operation Type |
Specifies the type of operation performed. |
|
Fabric Name |
Specifies the name of the Fabric. |
|
Created By |
Specifies the user name who performed the operation. |
|
Timestamp |
Specifies the time when the operation was performed. |
Terminology
This describes the terms that you must be familiar with:
|
Term |
Acronym |
Description |
|
Electronic Programmable Logic Device |
EPLD |
The EPLD image upgrades to enhance hardware functionality or to resolve known issues. |
|
In-Service Software Upgrade |
ISSU |
ISSU allows you to upgrade the software version of the release on a chassis device with no network downtime. |
|
Local Area Network |
LAN |
LAN consists of a series of computers linked together to form a network in a circumscribed location. |
|
Network Operating System |
NOS |
A specialized operating system designed for a network device such as a router, switch or firewall. Some examples include NX-OS for Nexus switches, IOS XE for Cisco Catalyst switches and so on. |
|
Rendezvous Points |
RP |
RP is a router that acts as the place where sources and receivers of multicast data can find each other. |
|
Route Reflector |
RR |
Route Reflector is a router that acts as a routing information exchange server for all other iBGP routers. |
|
Storage Area Network |
SAN |
SAN refers to the Storage Area Network management and analytics capabilities provided by the SAN Controller persona in Nexus Dashboard. This includes comprehensive management, monitoring, and visualization of SAN fabrics, typically composed of Cisco MDS switches supporting Fibre Channel SAN traffic. |
|
Secure Copy |
SCP |
SCP is used by fabric software to transfer files between devices. |
|
Secure File Transfer Protocol |
SFTP |
SFTP is a network protocol that allows you to securely access, transfer, and manage large files and sensitive data. |
Required software versions
For Cisco Nexus Dashboard services compatibility information, see the Cisco Data Center Networking Applications Compatibility Matrix.
Prerequisites
This section describes the prerequisites. This document assumes that the reader has a fundamental knowledge of Nexus Dashboard.
-
For remote image upload, you can import an image from an SCP or SFTP server.
-
To upload images from a remote location, specify the storage location or path in the System Settings page to configure remote storage settings.
-
Ensure that your user role is super-admin or fabric-admin.
-
Ensure that there is a fabric, its Deployment Enabled flag is set, and the switches are managed by the Nexus Dashboard in this fabric.
-
Ensure you have per-user device credentials set.
Guidelines and limitations
This section describes the guidelines and limitations.
-
Update group name character limit: The Nexus Dashboard UI limits update group names to 128 characters. Although the
attachGroupAPI allows names to exceed this limit to maintain backward compatibility for existing groups, you must shorten names to 128 characters or fewer to edit them in the UI.
-
Nexus Dashboard has these limitations for image management images stored under Manage > Fabric Software > Images, as described in Upload the image to Nexus Dashboard:
-
12 GB limitation for virtual Nexus Dashboards (vNDs), and physical Nexus Dashboards (pNDs) other than the ND-NODE-G5L (UCS-C225-M8)
-
36 GB limitation for the ND-NODE-G5L (UCS-C225-M8)
-
If you reach the space limit for images in Nexus Dashboard, navigate to Manage > Fabric Software > Images, choose the images that are no longer needed and click Actions > Delete.
-
Nexus Dashboard supports software updates on Cisco Catalyst devices in install mode only not in bundle mode.
-
There is a known issue where Nexus Dashboard is not able to stage or copy an IOS-XE image to Catalyst 9000 switches running IOS-XE 17.12.2 or later, where the image upgrade fails at the SCP image copy point of the process with this error:
Error opening scp://<ND-IP-address>/scp_data/<bin> (Undefined error)
This issue occurs because IOS-XE 17.10.x and later enables ETM (Encrypt-then-MAC) SSH algorithms only by default, whereas the Nexus Dashboard SCP client will attempt the upgrade using non-ETM MAC algorithms, leading to a
no matching mac foundfailure.The workaround for this issue is to push the following configuration to the switch using the freeform configuration in Nexus Dashboard:
ip ssh client algorithm mac hmac-sha2-256 hmac-sha2-256-etm@openssh.com hmac-sha2-512 hmac-sha2-512-etm@openssh.com
For more information on freeform configurations, see "Deploy freeform CLIs on a specific switch" in Configuring Switches for LAN and IPFM Fabrics
Upgrade or downgrade switches in a fabric under Overview tab
You can perform switch upgrades or downgrades at the fabric level.
This feature applies only to LAN and IPFM fabrics.
Prepare a fabric software update
This section describes how to prepare a software update that can be used at the fabric level.
-
Navigate to the Fabric Software page for NX-OS and IOS-XE fabrics.
-
In the Fabric Software page, click the Update groups tab.
See Understand Fabric Software for NX-OS and IOS-XE fabrics for more information on the Overview tab and the other tabs in the Fabric Software page.
-
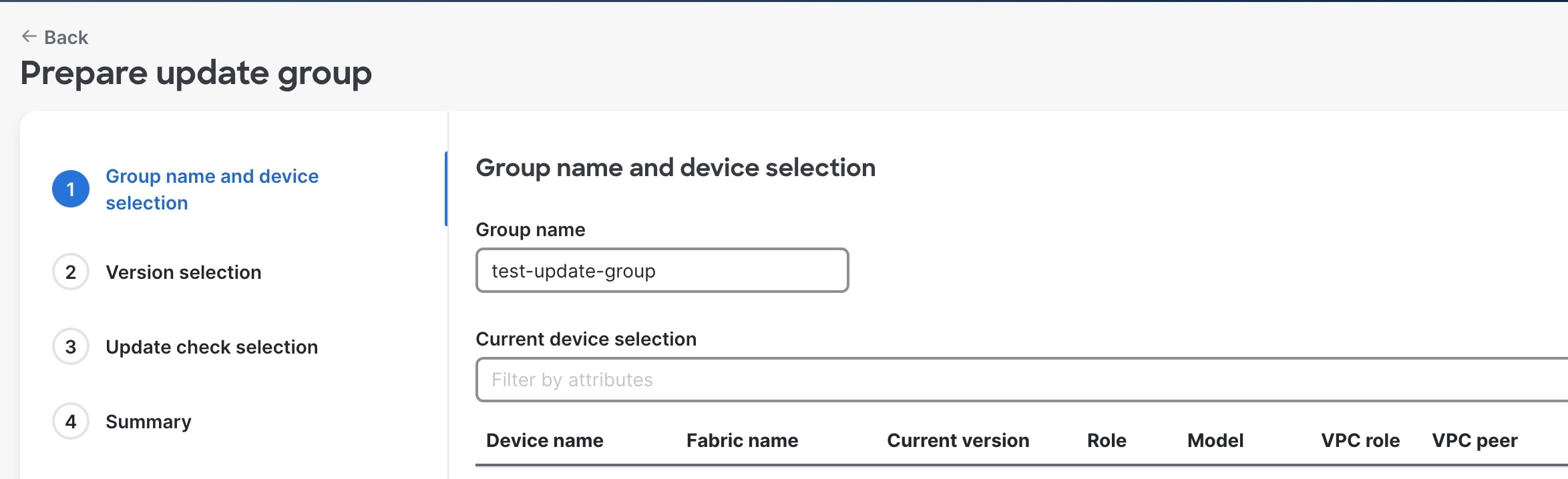
In the list of fabric-level update groups shown here, locate the update group for which you want to prepare a software update.
-
Click Prepare for the selected update group.
The Prepare update group wizard appears.
-
In the Group name and device selection area, make the appropriate configurations for this update group and click Next.
-
Review the types of devices listed in the devices area.
The list consists of device types that are detected in this fabric. Use this list to verify that the software update that you select in the next step aligns with the type of devices that you have in this fabric.
VPC peers are allowed in the same group. However, if both the VPC peers are part of an update, then a Warning message is displayed. This is applicable to both prepare & install flows.
For example, if you see
CAT8K,N9Klisted in the Devices area, when you select the version in the next step, verify that the image you select aligns with either Catalyst 8000 or Nexus 9000 series switches. -
-
In the Version selection area, choose between Non-disruptive or Disruptive and Select from uploaded images.
You can also choose to upload an image at this stage instead of using a previously uploaded image.
If the device is N9k, then Advanced options such as Select an EPLD and Select RPM(s) are enabled. Advanced options are not available for Cat8k devices.
If you choose the Non-disruptive update type, then Advanced options > Select an EPLD is disabled.
-
In the Update check selection area, choose the Type of report from No report, Basic or Custom report. However, if the device is Cat8k, No report is listed. NOTE: If No report is selected, then the Use existing pre report option is disabled during the Install flow. All other report options continue to be available for selection during the install flow. .
-
Review the configured details in the Summary area and click Stage and validate.
The Preparing update group message is displayed with a progress bar.
If you do not navigate away from this page, you can proceed to Install update once software preparation is completed. Also, the View pre-update report link is displayed during software preparation.
Alternatively, you can click Close to exit this wizard since software preparation for the update group continues to run in the background.
Create a report
As you go through the procedures in Prepare a fabric software update or [Install or upgrade software on devices in a fabric], you can create a basic or custom report with required checks.
The basic report contains fundamental checks to ensure switches meet the minimum requirements for a software update.
The basic checks are listed below:
-
Diag_module: Executes the
show diagnostic result module <module-number>command for each installed module. It then parses the detailed test results for each diagnostic test and confirms that all tests show a Pass status, which is indicated by aPin the output. -
All filesystem free space: Executes
show system internal flashcommand to retrieve detailed information about all storage partitions, analyzes every active filesystem (such as bootflash, logflash, etc.), calculates the usage percentage for each filesystem, and verifies that no filesystem exceeds the 85% usage threshold. This value is configurable. It excludes the read-only filesystems (ending with_ro). -
General log messages: Executes the
show logging logfile start-time <date>command to retrieve log entries from the past 30 days. It filters log messages with severity levels 1, 2, and 3. are found. -
Management console: Executes the
show line consolecommand and examines the Register Bits section in the output to verify if these three critical control signals are active:-
Request To send (RTS): Indicates the device is ready to send data.
-
Data terminal ready (DTR): Indicates the terminal is connected and ready.
-
Data set ready(DSR): Indicates the serial device is powered on and ready.
-
-
vPC state
-
BGP state
-
Module status
-
Modules health and backup power
-
Interface status
-
vPC sticky bit
-
NVRAM log messages
-
vPC secondary role
-
OSPF state
The custom report allows you to turn checks on or off or even add your own command-line checks to build a report tailored to your needs.
In addition to the basic checks listed above, other checks available for a custom report include: * BGP stability * HSRP mgo state active * Modules health and backup power * OSPF stability * HSRP mgo state standby
Data is available for telemetry-enabled fabrics.
For the pre-report, this includes: * Forecasted cleared anomalies and advisories * Potentially affected endpoints
For the post-report, this includes: * Cleared anomalies and advisories * 13 delta tables that include endpoints, protocol, interface, and hardware-related details similar to telemetry reports in Nexus Dashboard 4.1.1.
Change number of concurrent switches for staging/validating/updating
As you go through the procedures in [Install or upgrade software on devices in a fabric], there are points during the staging/validating or updating processes where you might be taking actions on a group of switches concurrently. Following are the default values for the number of switches that are grouped together when you are taking an action on a group of switches concurrently:
-
Staging/validating: Default number of switches is 10
-
Updating: Default number of switches is 20
Follow these procedures if you want to change these default values.
-
Navigate to Admin > System Settings > Fabric management.
-
In the Advanced Settings area, click the Admin tab.
-
Modify the values in the following fields, if necessary:
-
Image update thread pool size: The number of switches that can be updated concurrently.
Default value is 20. Valid range is 10-200.
-
Image stage/validate thread pool size: The number of switches that can be staged and validated concurrently.
Default value is 10. Valid range is 5-200.
-
-
Click Save when you have completed any configuration changes on this page.
Install or update software on devices in a fabric
This section describes how to install or update software on the devices in a fabric through update groups.
-
Navigate to the Fabric Software page for NX-OS and IOS-XE fabrics.
-
In Fabric Software, click the Update groups tab.
You can also select Prepare from the Devices tab.
-
In the list of fabric-level update groups shown here, locate the update group for which you want to install a software update.
-
In the update group area corresponding to the desired fabric, click Install update.
The Install update group wizard is displayed.
-
In the Group name and device selection area, verify the devices for this update group and click Next.
-
Review the types of devices listed in the devices area.
The list consists of device types that are detected in this fabric. Use this list to verify that the software update that you select in the next step aligns with the type of devices that you have in this fabric.
VPC peers are allowed in the same group. However, if both the VPC peers are part of an update, then a Warning message is displayed. This is applicable to both prepare & install flows.
-
-
In the Update options area, verify the configurations and click Next.
-
Select the type of update by choosing between Non-disruptive or Disruptive.
For Catalyst devices, only Disruptive update is supported.
-
Choose between Disruptive or Non-Disruptive.
If you choose Non-Disruptive, then the Use Maintenance Mode checkbox will be cleared. Refer to [Understanding In-Service Software Upgrades] for more information about this option.
-
If the device is N9k, you can choose between Yes or No to isolate the switches prior to update using maintenance mode. For Cat8k devices, this option is set to No.
Maintenance mode along with normal mode is part of Graceful Insertion and Removal (GIR). When the Maintenance Mode option is enabled, Nexus Dashboard places the switches in the update group. This occurs during the update process in the maintenance mode, where all configured Layer 3 control-plane protocols are isolated from the network. The switches return to normal mode after the update process is completed. Refer to [Configuring Graceful Insertion and Removal] for more information on GIR.
-
Choose between Serial or Parallel for the Execution Paradigm.
In the Execution Paradigm field, choose between Serial or Parallel execution:
-
Serial: Switches are updated one at a time, serially, where the update process must fully complete on one switch before it begins on the next switch in the update group.
-
Parallel: Switches are updated all at one time, depending on the number of switches that can be updated concurrently. For example, if you have 40 switches in the update group but 20 switches are updated at a time concurrently, then a Parallel setting results in the first set of 20 switches going through the update process, simultaneously, and then the second set of 20 switches going through the same concurrent update process after the update process has completed for the first set.
-
-
Verify the devices listed under Current device selection.
-
For Error handling, choose between Pause or Continue from the On failure drop-down menu.
In the Error handling/On failure field, determine if the installation needs to Continue or Pause if a failure occurs during the update.
A failure might occur for various reasons, such as a switch failing to come back online or a failure to successfully establish an ssh session between Nexus Dashboard and the switch.
The actions taken with this setting may also be affected by settings in other areas.
For example, if the Error handling/On failure field is set to Pause and the Execution Paradigm field is set to Serial. If a set of 20 switches in an update group are undergoing a serial update but an issue arises with the sixth switch in the set. Then, the update pauses at the update process for the sixth switch. This pauses proceed the update process for the remaining 14 switches in the set until the update process is manually initiated.
However, if the Execution Paradigm field is set to Parallel and there is an issue with the sixth switch in a set in the update group. Then, the update process continues for the other 14 switches in the set that are being updated concurrently. In this scenario, the update process pauses before moving to the update process for the next set of switches in the update group.
-
-
In the Update check selection area, choose the Type of report from No report, Basic or Custom report. However, if the device is Cat8k, No report is the only option available.
If the No report option is selected during the Prepare Update flow, then you can select all other report options except the Use existing pre report option which gets disabled.
-
Review the configured details in the Summary area and click Install update.
The Installing update group message is displayed with a progress bar. The software preparation for the update group continues to run in the background. Click Close to exit this wizard.
Also, the View the post-update report link is displayed during software preparation.
Update or downgrade switches
This section describes both the disruptive and non-disruptive method of upgrading or downgrading a group of switches.
During disruptive update, the switches go down temporarily. This results in a disruption in your fabric traffic.
During non-disruptive update, the switches run without disruption in your fabric traffic.
Guidelines and limitations: Disruptive update
-
If you are downgrading a group of switches, the process is identical to the process for updating a group of switches, except that the target image that you choose will be earlier than the currently installed image. The text for dialogs, fields, buttons, and other controls in the UI specify “upgrade” even though you are downgrading the software.
EPLD downgrades are not supported and EPLD upgrades are always disruptive.
-
For switches running on NX-OS 9.3(11), there is an issue when upgrading the EPLD along with NX-OS using the
install alloption. This is not an issue with switches running on a release after NX-OS 9.3(11).To resolve this issue, follow these steps for an upgrade in this situation:
-
Install the NX-OS image from 9.3(11) to the destination version.
-
After the NX-OS upgrade, install the EPLD image.
-
Guidelines and limitations: Non-disruptive upgrade
-
Non-Disruptive update is not supported on Catalyst devices.
-
An EPLD upgrade using the
install allcommand when upgrading switches using the non-disruptive option is not supported on these switch platforms on the NX-OS 10.5.3 version for the bundled image:-
N9K-C93180YC-FX
-
N9K-C93108TC-FX
-
N9K-C9348GC-FXP
-
N9K-C93240YC-FX2
-
N9K-C9336C-FX2
-
N9K-C9364C
-
N9K-C9332C
-
N9K-C9232C
-
N9K-SUP-A+
-
N9K-SUP-B+
-
N3K-C36180YC-R
-
N3K-C3636C-R
-
N9K-SUP-A
-
N9K-SUP-B
In these cases, use the
install epldcommand separately to update the EPLD. -
Download an image from the Software Download website
This section describes how to download an image from the software download website.
-
Go to the Software Download Website.
-
Log in with your credentials.
You need to be logged in to download the software.
-
Navigate to Switches, choose a series and a switch.
-
Choose a software type:
-
For Nexus switches:
-
NX-OS EPLD Updates
-
NX-OS Firmware
-
NX-OS Patch Release
-
NX-OS Software Maintenance Upgrades (SMU)
-
NX-OS System Software
-
-
For Cisco Catalyst switches: IOS XE Software
For Cisco Catalyst switches, Nexus Dashboard provides support for software upgrade using CAT9K and CAT9K_LITE image types.
-
-
Choose the software file you want to download and click the download icon.
Upload the image to Nexus Dashboard
This section describes how to upload the image.
-
In some cases, you can download an SMU image from the Software Download website wherein multiple RPMs are bundled together as a .tar file, and Nexus Dashboard allows you to upload this type of bundled .tar file to Nexus Dashboard. However, Nexus Dashboard normally does not allow you to upload any other type of bundled .tar file, so if you try to upload a bundled .tar file and you see an error message, use a .zip format instead for the bundle.
-
If you are about to upload a compacted NX-OS image to the Nexus Dashboard image repository and another NX-OS image with the same name is currently in the repository, you might overwrite the existing (older) NX-OS image with the newer NX-OS image that you are about to upload. You can avoid overwriting the existing image using the following method:
-
Upgrade the switches that can use normal NX-OS image first.
-
Delete the normal NX-OS image from the Nexus Dashboard repository using the Image Upload screen.
-
Upload the compact image and upgrade the other set of switches.
-
-
Nexus Dashboard has these limitations for image management images stored under Images:
-
12 GB limitation for virtual Nexus Dashboards (vNDs), and physical Nexus Dashboards (pNDs) other than the ND-NODE-G5L (UCS-C225-M8)
-
36 GB limitation for the ND-NODE-G5L (UCS-C225-M8)
-
-
You can upload up to three images simultaneously.
-
Navigate to the Fabric Software page for NX-OS and IOS-XE fabrics.
-
In the Fabric Software page, choose Images.
-
From the Actions drop-down list, select Upload.
-
In the Upload Image dialog box, either upload the file from a local device or import it from SCP or SFTP.
-
For Import from SCP/SFTP, choose pre-defined remote servers from the Remote server name drop-down list.
-
Uploading an image to SCP or SFTP server from a non-Unix based device is not supported.
-
-
Click Verify.
Now, the uploaded image is validated, downloaded and copied, and then verified.
Attach or detach update groups to the switches
This section describes how to attach or detach switches to or from an update group. Grouping allows you to track upgrades for a set of switches. You can create several groups and select a switch regardless of the group, role, or type of switch.
We recommend that you create update groups based on the roles of the switches. For example, if a fabric has multiple switches with different roles, such as Leaf, Spine, Border, and more, creating groups based on different roles is recommended. This clearly separates roles and responsibilities during switch image management operations. Switches with different roles perform critical functionality and respond differently based on the control plane, data plane, and system-level convergence.
A user with admin role can create multiple groups as listed:
-
Group-Leaf-Even for Leaf switches that have even numbers or VPC role of primary
-
Group-Leaf-Odd for Leaf switches that have odd numbers or VPC role of secondary
You can automatically assign groups based on these criteria:
-
Role-based: All switches of a given role for a fabric in the same group
-
Even-odd: Switches that are grouped in odd or even groups:
-
Switches that have even numbers or vPC role of primary
-
Switches that have odd numbers or vPC role of secondary
-
Update groups have checks to avoid unnecessary downtime in redundant fabrics in these cases:
-
Switches belonging to different fabrics are not allowed to form an update group.
-
Virtual Port Channel (vPC) peers are placed in different groups by defaul
Typically, Spine and Border devices are limited to fabric, while the role of the Leaf is the most common one. Therefore, users with the admin role can upgrade individual Spines followed by Individual Borders, or create different groups for Spines and Borders. Users with the admin role can still leverage groups to divide the Leaf role switches and perform bulk actions.
-
Navigate to the Fabric Software page for NX-OS and IOS-XE fabrics.
-
In the Fabric Software page, choose Devices.
-
In the Devices page, place a checkmark in the checkbox for the devices you want to group.
-
From the Actions drop-down list, select Modify groups.
-
In the Modify groups dialog box, click the radio button to either Attach Group or Detach Group.
-
Select Attach Group and choose Create Group to create a new group or select an existing group from the Group drop-down list.
-
To create a group, enter a group name in the Modify groups dialog box.
-
Click Save.
-
-
Select Detach Group and click Detach to detach the devices from a group. This deletes the Update group, if it is not assigned to any switches.
-
Update group name character limit: Limit update group names to 128 characters. Although the API allows longer names for backward compatibility, the Nexus Dashboard UI prevents you from saving names that exceed this limit.
Auto-generate update groups
This section describes how to auto-generate update groups from the Update groups tab. Devices that are not associated with any update group are listed under None.
For a given fabric, you can create update groups either based on role or odd-even grouping. Creating update groups based on the roles, such as Leaf, Spine, Border, and more, clearly separates roles and responsibilities during switch image management operations. Switches with different roles perform critical functionality and respond differently based on the control plane, data plane, and system-level convergence.
For the odd-even auto-grouping mechanism, devices within each role are assigned to the odd or even group alternately. This ensures that route reflectors and rendezvous are not placed in the same group thereby enabling redundancy.
All vPC primary devices are placed in even groups while all vPC secondary are placed in odd groups.
-
Navigate to the Fabric Software page for NX-OS and IOS-XE fabrics.
-
In the Fabric Software page, choose Update Groups.
-
From the Actions drop-down list, select Auto-generate groups.
-
In the Auto-generate update groups dialog box, choose the Fabric and Type.
-
For Type, choose between Role-based or Even odd.
-
-
Click Save.
Change mode for a switch
This section describes how to change mode for a switch.
-
Navigate to the Fabric Software page for NX-OS and IOS-XE fabrics.
-
In the Fabric Software page, choose Devices.
-
In the Devices page, place a checkmark in the checkbox for the device you want.
-
From the Actions drop-down list, select Change Mode.
-
In the Change Mode dialog box, choose either Normal or Maintenance mode.
-
Click Deploy Now or Deploy Later.
Understand Fabric Software for ACI fabrics
This section provides detailed information for the Fabric Software feature in Nexus Dashboard for ACI fabrics.
Navigate to the Fabric Software page for ACI fabrics
To navigate to the Fabric Software page:
-
Click Manage > Fabric Software.
-
Click the ACI tab.
-
Cisco’s recommended versions: The software versions that Cisco recommends. These are the latest versions available for upgrade or for running an analysis.
-
Current version: This is the software version that the fabric is currently running.
-
Recommended: Displays the recommended software version to upgrade to. This version is determined based on the current version the fabric is running on.
For example, if the fabric is currently on version 6.0(3d), then the Recommended version indicates 6.0(3d). However, if the Current version is newer than the recommended versions, then this field will be blank.
-
NOTE:
-
Delta analysis is no longer a part of the post-upgrade assist workflow. In Delta analysis, you can only run an analysis per fabric unlike Upgrade assist, where you can choose a subset of devices to analyse.
-
When you initially run an analysis, you can Rerun the report from the Pre-update analysis drawer to collect fresh data. Once your devices are upgraded, you can run a post-upgrade analysis. However, this disables the Rerun the report button in the pre-update analysis drawer.
Understand the information provided in the Fabric Software page for ACI fabrics
-
Connect to Intersight if you are not connected already.
Hover over the link icon in the Sofware Versions area to see if you are connected to Intersight. Intersight connectivity is required for Nexus Dashboard to automatically check for recommended software versions for the ACI fabrics. See Working with Intersight for more information.
-
Review the information in the Software Versions area.
The Software Versions area provides information on recommended software releases for your ACI fabrics and links to the Release Notes for those software releases.
Copyright
THE SPECIFICATIONS AND INFORMATION REGARDING THE PRODUCTS IN THIS MANUAL ARE SUBJECT TO CHANGE WITHOUT NOTICE. ALL STATEMENTS, INFORMATION, AND RECOMMENDATIONS IN THIS MANUAL ARE BELIEVED TO BE ACCURATE BUT ARE PRESENTED WITHOUT WARRANTY OF ANY KIND, EXPRESS OR IMPLIED. USERS MUST TAKE FULL RESPONSIBILITY FOR THEIR APPLICATION OF ANY PRODUCTS.
THE SOFTWARE LICENSE AND LIMITED WARRANTY FOR THE ACCOMPANYING PRODUCT ARE SET FORTH IN THE INFORMATION PACKET THAT SHIPPED WITH THE PRODUCT AND ARE INCORPORATED HEREIN BY THIS REFERENCE. IF YOU ARE UNABLE TO LOCATE THE SOFTWARE LICENSE OR LIMITED WARRANTY, CONTACT YOUR CISCO REPRESENTATIVE FOR A COPY.
The Cisco implementation of TCP header compression is an adaptation of a program developed by the University of California, Berkeley (UCB) as part of UCB’s public domain version of the UNIX operating system. All rights reserved. Copyright © 1981, Regents of the University of California.
NOTWITHSTANDING ANY OTHER WARRANTY HEREIN, ALL DOCUMENT FILES AND SOFTWARE OF THESE SUPPLIERS ARE PROVIDED “AS IS" WITH ALL FAULTS. CISCO AND THE ABOVE-NAMED SUPPLIERS DISCLAIM ALL WARRANTIES, EXPRESSED OR IMPLIED, INCLUDING, WITHOUT LIMITATION, THOSE OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT OR ARISING FROM A COURSE OF DEALING, USAGE, OR TRADE PRACTICE.
IN NO EVENT SHALL CISCO OR ITS SUPPLIERS BE LIABLE FOR ANY INDIRECT, SPECIAL, CONSEQUENTIAL, OR INCIDENTAL DAMAGES, INCLUDING, WITHOUT LIMITATION, LOST PROFITS OR LOSS OR DAMAGE TO DATA ARISING OUT OF THE USE OR INABILITY TO USE THIS MANUAL, EVEN IF CISCO OR ITS SUPPLIERS HAVE BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES.
Any Internet Protocol (IP) addresses and phone numbers used in this document are not intended to be actual addresses and phone numbers. Any examples, command display output, network topology diagrams, and other figures included in the document are shown for illustrative purposes only. Any use of actual IP addresses or phone numbers in illustrative content is unintentional and coincidental.
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product.
Cisco and the Cisco logo are trademarks or registered trademarks of Cisco and/or its affiliates in the U.S. and other countries. To view a list of Cisco trademarks, go to this URL: https://www.cisco.com/go/trademarks. Third-party trademarks mentioned are the property of their respective owners. The use of the word partner does not imply a partnership relationship between Cisco and any other company. (1110R)
© 2017-2026 Cisco Systems, Inc. All rights reserved.
Americas Headquarters
Cisco Systems, Inc.
170 West Tasman Drive
San Jose, CA 95134-1706
USA
https://www.cisco.com
Tel: 408 526-4000
800 553-NETS (6387)
Fax: 408 527-0883