About Fleet Upgrade
Cisco Crosswork Workflow Manager (CWM) Solutions is a collection of pre-built use cases that offers customers a convenient and efficient way to manage, configure and upgrade their devices. It provides out-the-box use cases that are easy to deploy and ready to use, allowing users to quickly onboard their devices for management.
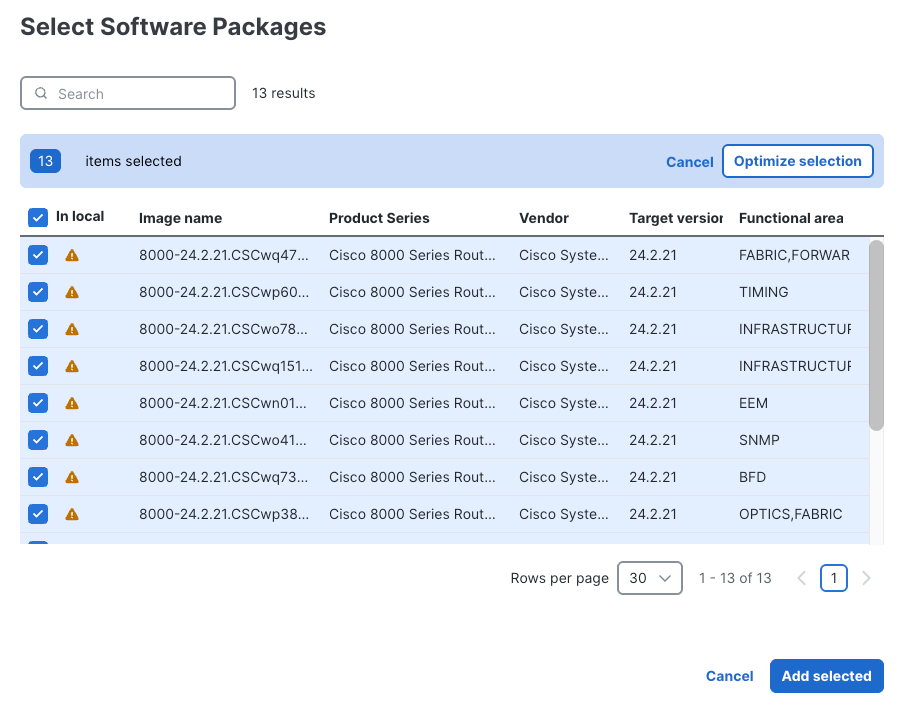
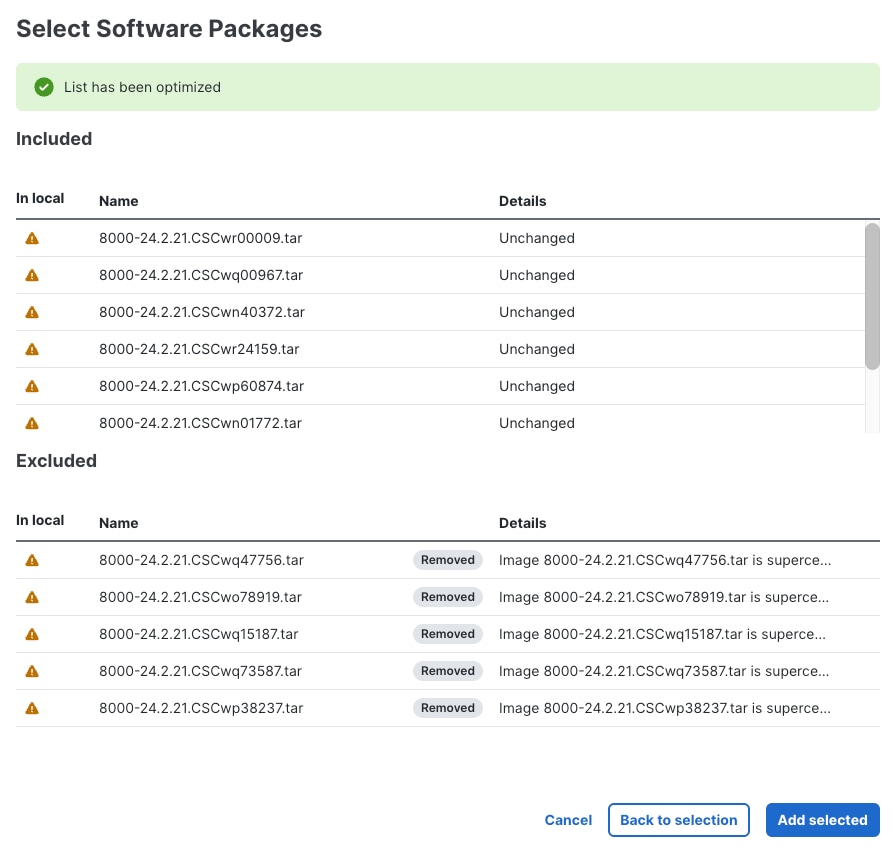
CWM Solutions Fleet Upgrade lets users manage, distribute, and commit software images and image upgrades ato multiple devices at the same time, including to third-party devices.
Fleet Upgrade is automated, customizable, extensible, provides strong error checking, and supports devices from Cisco and other vendors.
To get started using Fleet Upgrade, see the next topic, Onboard devices.
Pre-requisites
This version of Crosswork Workflow Manager Solutions (CWM-S) Fleet Upgrade is part of the Cisco Crosswork Network Controller Advantage tier. You must install the Advantage tier package as a CAPP (Crosswork APPlication) on an SVM (single virtual machine) deployment of Cisco Crosswork Network Controller.
Refer to Cisco Crosswork Network Controller 7.2 Installation Guide for instructions on cluster deployment and installation of the supporting products.


 Feedback
Feedback