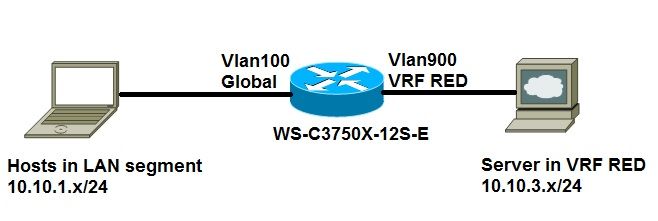
Configure Route Leak Between Global and VRF Routing Table without Next-Hop
Available Languages
Revision History
| Revision | Publish Date | Comments |
|---|---|---|
5.0 |
12-Nov-2024
|
Recertification, formatting. |
4.0 |
09-Aug-2023
|
Recertification |
3.0 |
13-Jul-2022
|
Updates |
2.0 |
06-Jun-2022
|
minor HTML changes |
1.0 |
17-Sep-2015
|
Initial Release |
Contact Cisco
- Open a Support Case

- (Requires a Cisco Service Contract)
 Feedback
Feedback