Field Notice: FN74392 - Cisco Identity Services Engine: Impact on Secure Communications from Public CA Client Authentication EKU Changes Starting in May 2026 - Workaround Provided
Available Languages
Notice
THIS FIELD NOTICE IS PROVIDED ON AN "AS IS" BASIS AND DOES NOT IMPLY ANY KIND OF GUARANTEE OR WARRANTY, INCLUDING THE WARRANTY OF MERCHANTABILITY. YOUR USE OF THE INFORMATION ON THE FIELD NOTICE OR MATERIALS LINKED FROM THE FIELD NOTICE IS AT YOUR OWN RISK. CISCO RESERVES THE RIGHT TO CHANGE OR UPDATE THIS FIELD NOTICE AT ANY TIME.
Products Affected
| Affected Software Product | Affected Release | Affected Release Number | Comments |
|---|---|---|---|
| Identity Services Engine System Software | 3.1 | 3.1 P1, 3.1 P10, 3.1 P2, 3.1 P3, 3.1 P4, 3.1 P5, 3.1 P6, 3.1 P7, 3.1 P8, 3.1 P9, 3.1.0 | ISE 3.1 Patch 10 and earlier are affected. |
| Identity Services Engine System Software | 3.2 | 3.2 P1, 3.2 P2, 3.2 P3, 3.2 P4, 3.2 P5, 3.2 P6, 3.2 P7, 3.2 P8, 3.2 P9, 3.2.0 | ISE 3.2 Patch 9 and earlier are affected. |
| Identity Services Engine System Software | 3.3 | 3.3 P1, 3.3 P10, 3.3 P2, 3.3 P3, 3.3 P4, 3.3 P5, 3.3 P6, 3.3 P7, 3.3 P8, 3.3 P9, 3.3.0 | ISE 3.3 Patch 10 and earlier are affected. |
| Identity Services Engine System Software | 3.4 | 3.4 P1, 3.4 P2, 3.4 P3, 3.4 P4, 3.4 P5, 3.4.0 | ISE 3.4 Patch 5 and earlier are affected. |
| Identity Services Engine System Software | 3.5 | 3.5 P1, 3.5 P2, 3.5.0 | ISE 3.5 Patch 2 and earlier are affected. |
Defect Information
| Defect ID | Headline |
| CSCws83036 | Impact assesment of ClientAuth EKU enforcement in ISE |
Problem Description
Beginning in May 2026, many public certificate authorities (CAs) will stop issuing Transport Layer Security (TLS) certificates that include the Client Authentication Extended Key Usage (EKU). Newly issued certificates will typically include Server Authentication EKU only.
As a result, if certificates issued by a public CA are renewed under the updated CA policies and then deployed in Cisco Identity Services Engine (ISE), services where Client Authentication EKU is required will fail. The specific services being impacted are: pxGrid, ISE Messaging Service (IMS), and TC-NAC (Threat Centric Network Access Control).
Background
Publicly trusted TLS certificates are issued by CAs that must comply with industry policies governing certificate issuance and usage.
The Chrome Root Program Policy, operated by Google, defines requirements that CAs must follow for their certificates to be trusted by the Google Chrome browser. These requirements influence how publicly trusted certificates are issued across the industry. As part of evolving security practices, the Chrome Root Program is introducing stricter guidance around certificate usage.
Many public CAs are therefore moving away from issuing certificates that include Client Authentication EKU and are transitioning toward issuing certificates intended only for server authentication. As a result, newly issued certificates from many public CAs are expected to include Server Authentication EKU only.
Services Impacted on Cisco ISE
Cisco ISE uses TLS certificates for several services. Services listed in the following table expect certificates that include both Server Authentication EKU and Client Authentication EKU. As a result, if certificates that are issued by a public CA are renewed under the updated CA policies and then deployed in Cisco ISE, affected services may fail where Client Authentication EKU is still required.
This notice applies to customers who use public CA-issued certificates for the services listed in the table, unless their private or enterprise CA enforces similar Client Authentication EKU restrictions.
| Service | Impact |
|---|---|
| pxGrid | Certificate renewed by a public or enterprise CA that includes only the Server Authentication EKU will not be accepted for import or bind into Cisco ISE. |
| ISE Messaging Service (IMS) | |
| TC-NAC (Threat Centric Network Access Control) | If the Admin certificate includes Server Authentication EKU only and Tenable VA is configured with strict mTLS, then certificate-based authentication for TC-NAC will be impacted. |
Note: The solution in this Field Notice is limited to the pxGrid and IMS services. Cisco ISE may also act as a TLS client for other services (TC-NAC, LDAPS, Secure Syslog, Radius DTLS). For additional details, see the Prepare Identity Services Engine for Extended Key Usage Restrictions in Certificates Issued by Public Certification Authorities TechNote.
Problem Symptom
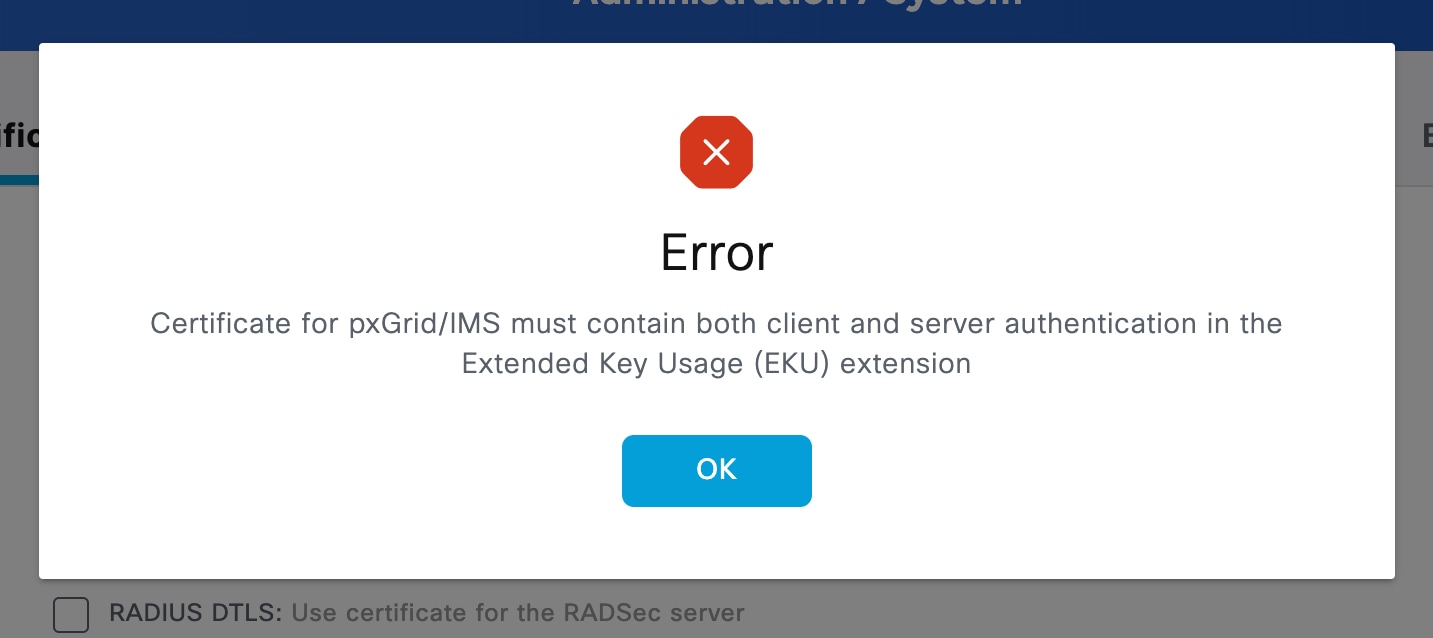
After deploying Server Authentication EKU-only certificates, customers will observe certificate import or bind failures in the Cisco ISE GUI when attempting to upload pxGrid or IMS certificates that do not meet the current EKU requirements for the selected service.
The following image shows an example of the error message that will display.
Services that rely on these certificates may become partially or fully unavailable until the required actions that are described in this notice are completed.
Workaround/Solution
Before considering workaround and solution options, audit current certificates. Prepare an inventory of all public TLS certificates to identify which certificates contain the Client Authentication EKU.
Workaround
Administrators can choose from one of the following workaround options.
Option 1: Switch to public root CAs that provide combined EKU certificates
Some public root CAs, such as DigiCert and IdenTrust, issue certificates with combined EKU types (server and client certificates) from an alternative root, which may not be included in the Chrome Root Store. Coordinate with the CA provider to check the availability of such certificates, and, before deploying them, ensure that both the server presenting the certificate and the clients consuming it trust the corresponding root CA.
This approach alleviates the need to upgrade server software to mitigate sunsetting of Client Authentication EKU enforced by the Chrome Root Program Policy.
The following table, which shows examples of public root CAs and EKU types, is not an exhaustive list and is for illustrative purposes only.
CA Vendor EKU Type Root CA Issuing/Sub CA IdenTrust clientAuth + serverAuth IdenTrust Public Sector Root CA 1 IdenTrust Public Sector Server CA 1 IdenTrust clientAuth IdenTrust Public Sector Root CA 1 TrustID RSA ClientAuth CA 2 IdenTrust serverAuth (browser trusted) IdenTrust Commercial Root CA 1 HydrantID Server CA O1 DigiCert clientAuth + serverAuth DigiCert Assured ID Root G2 DigiCert Assured ID CA G2 DigiCert clientAuth DigiCert Assured ID Root G2 DigiCert Assured ID Client CA G2 DigiCert serverAuth (browser trusted) DigiCert Global Root G2 DigiCert Global G2 TLS RSA SHA256 Option 2: Renew current certificates to extend validity
Certificates that are issued by public root CAs before May 2026 that have both Server and Client Authentication EKU will continue to be honored until their term expires. However, it is best to renew combined EKU certificates before the policy sunsetting occurs.
Public CA policy and implementation dates may vary by vendor. Check with the CA and plan certificate renewal accordingly.
Option 3: Migrate to private PKI
Evaluate the feasibility of transitioning to a private Public Key Infrastructure (PKI) and then set up a private CA to issue single certificates with combined EKU (Server and Client certificates with the required EKUs).
Before issuing or deploying a certificate, ensure that both the server presenting the certificate and all clients consuming it trust the corresponding root CA. Using this approach will alleviate the urgency to patch the Cisco ISE system software to mitigate sunsetting of Client Authentication EKU enforced by the Google Chrome Root Policy.
Solution
Upgrade Cisco ISE system software to a patch release that introduces updated certificate handling for certificates issued under the new CA policies. The following patches will be released starting mid-April 2026:
| Cisco ISE Release | Patch |
|---|---|
| 3.1 | Patch 11 |
| 3.2 | Patch 10 |
| 3.3 | Patch 11 |
| 3.4 | Patch 6 |
| 3.5 | Patch 3 |
After upgrading Cisco ISE, do the following:
pxGrid Certificate (ISE)
Cisco ISE will allow the import or bind of pxGrid certificates that contain Server Authentication EKU. In addition, Cisco ISE will continue to accept certificates that contain both Server Authentication and Client Authentication EKU.
Note: Verify the certificate type used by any external pxGrid clients. Upon renewal, public CA-signed certificates may no longer include Client Authentication EKU. External pxGrid client integrations must include the Client Authentication EKU when communicating with Cisco ISE or the connection will be rejected resulting in a non-functional integration.
IMS Certificate
For Cisco ISE releases 3.1, 3.2, and 3.3, there is no change in behavior after installing the patch. IMS will continue to require a certificate with both Client and Server EKU. Customers should plan to use an ISE Internal CA certificate after the current certificate expires.
To renew the IMS certificate with a Cisco ISE internal CA certificate, complete the following steps:
- Choose Administration > System > Certificates > Certificate Management > Certificate Signing Request.
- Choose Generate Certificate Signing Request (CSR).
- In the Usage section, choose ISE Messaging Service.
- Choose the radio button for Regenerate ISE Messaging Service Certificate.
- In the Node(s) section, check the boxes of all the Cisco ISE nodes in the deployment.
- Click Generate ISE Messaging Service Certificate.
No service restart is required.
For Cisco ISE releases 3.4 and 3.5, after installing the patch, Cisco ISE will allow the import or bind of IMS certificates that contain Server Authentication EKU. In addition, Cisco ISE will continue to accept certificates that contain both Server Authentication and Client Authentication EKU. However, because IMS is used only for internal Cisco ISE communication, Cisco recommends using the Cisco ISE internal CA certificate when the certificate is renewed.
Revision History
| Version | Description | Section | Date |
| 1.1 | Updated pxGrid Certificate and IMS Certificate information. | Background and Workaround/Solution | 2026-APR-06 |
| 1.0 | Initial Release | — | 2026-MAR-18 |
For More Information
For further assistance or for more information about this field notice, contact the Cisco Technical Assistance Center (TAC) using one of the following methods:
Receive Email Notification About New Field Notices
To receive email updates about Field Notices (reliability and safety issues), Security Advisories (network security issues), and end-of-life announcements for specific Cisco products, set up a profile in My Notifications.
Unleash the Power of TAC's Virtual Assistance
 Feedback
Feedback