Component Assessment
This chapter discusses the function of each component and how it helps to address PCI DSS 2.0 compliance requirements. Each component was assessed by Verizon Business.
This assessment took place at a specific point in time using currently available versions of products and software.
Component Section Overview
Each component section includes the following:
•![]() Description
Description
•![]() PCI assessment summary
PCI assessment summary
•![]() Primary PCI function
Primary PCI function
•![]() Capability assessment
Capability assessment
•![]() Design considerations
Design considerations
PCI Assessment Summary
For each component, the PCI Assessment Summary table (see Table 4-1) lists each of the PCI sub-requirements that were passed, required compensating controls, or failed.
Capability Assessment
Each component requires specific capabilities to be deployable in a compliant environment. Customers and vendors alike have complained that it is difficult to understand what capabilities are required when developing or purchasing equipment for the purpose of compliance. Therefore, Cisco has developed a simplified approach to clarify the scales that are relevant. Sub-requirements have been grouped for ease of assessment, as shown in Table 4-1.
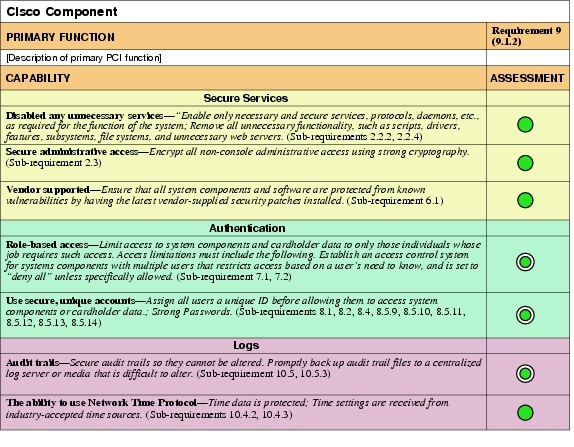
The PCI DSS 2.0 security standard is written from the perspective of helping a merchant become compliant. It is not grouped in a clear manner for the evaluation of hardware or software. The following grouping of sub-requirements is an extrapolation of the standard to simplify the assessment of hardware and software:
•![]() Secure services comprises sub-requirements that affect the secure administration and hardening of the component, and include the following:
Secure services comprises sub-requirements that affect the secure administration and hardening of the component, and include the following:
–![]() Disable any unnecessary services—Enable only necessary and secure services, protocols, daemons, etc., as required for the function of the system; Remove all unnecessary functionality, such as scripts, drivers, features, subsystems, file systems, and unnecessary web servers. (Sub-requirements 2.2.2, 2.2.4)
Disable any unnecessary services—Enable only necessary and secure services, protocols, daemons, etc., as required for the function of the system; Remove all unnecessary functionality, such as scripts, drivers, features, subsystems, file systems, and unnecessary web servers. (Sub-requirements 2.2.2, 2.2.4)
–![]() Secure administrative access—Encrypt all non-console administrative access using strong cryptography. (Sub-requirement 2.3)
Secure administrative access—Encrypt all non-console administrative access using strong cryptography. (Sub-requirement 2.3)
–![]() Vendor supported—Ensure that all system components and software are protected from known vulnerabilities by having the latest vendor-supplied security patches installed. (Sub-requirement 6.1)
Vendor supported—Ensure that all system components and software are protected from known vulnerabilities by having the latest vendor-supplied security patches installed. (Sub-requirement 6.1)
•![]() Authentication comprises sub-requirements that affect the identity of personnel accessing systems in the cardholder data environment, including the following:
Authentication comprises sub-requirements that affect the identity of personnel accessing systems in the cardholder data environment, including the following:
–![]() Role-based access—Limit access to system components and cardholder data to only those individuals whose job requires such access. Access limitations must include the following. Establish an access control system for systems components with multiple users that restricts access based on a user's need to know, and is set to "deny all" unless specifically allowed. (Sub-requirement 7.1, 7.2)
Role-based access—Limit access to system components and cardholder data to only those individuals whose job requires such access. Access limitations must include the following. Establish an access control system for systems components with multiple users that restricts access based on a user's need to know, and is set to "deny all" unless specifically allowed. (Sub-requirement 7.1, 7.2)
–![]() Use secure, unique accounts—Assign all users a unique ID before allowing them to access system components or cardholder data. Strong Passwords. (Sub-requirements 8.1, 8.2, 8.4, 8.5.9, 8.5.10, 8.5.11, 8.5.12, 8.5.13, 8.5.14)
Use secure, unique accounts—Assign all users a unique ID before allowing them to access system components or cardholder data. Strong Passwords. (Sub-requirements 8.1, 8.2, 8.4, 8.5.9, 8.5.10, 8.5.11, 8.5.12, 8.5.13, 8.5.14)
•![]() Logs comprises sub-requirements that affect the forensic analysis capabilities of the cardholder data environment, including the following:
Logs comprises sub-requirements that affect the forensic analysis capabilities of the cardholder data environment, including the following:
–![]() Audit trails—Secure audit trails so they cannot be altered. Promptly back up audit trail files to a centralized log server or media that is difficult to alter. (Sub-requirement 10.5, 10.5.3)
Audit trails—Secure audit trails so they cannot be altered. Promptly back up audit trail files to a centralized log server or media that is difficult to alter. (Sub-requirement 10.5, 10.5.3)
–![]() The ability to use Network Time Protocol—Time data is protected; Time settings are received from industry-accepted time sources. (Sub-requirements 10.4.2, 10.4.3)
The ability to use Network Time Protocol—Time data is protected; Time settings are received from industry-accepted time sources. (Sub-requirements 10.4.2, 10.4.3)
Table 4-3 explains the color-codes icons used in the tables.
Design Considerations
This section provides compliance principles as well as best practices for each technology deployed within a retail business environment.
Endpoints and Applications
The endpoints and applications layer of the solution framework addresses the components such as voice, e-mail, and physical security.
Voice
Cisco Unified Communications Manager and IP Phones
The Cisco Unified Communication Manager is a suite of voice applications, signaling control, and utilities that provide IP communications capabilities using devices such as the IP phones. It is configured as an appliance that is easy to deploy, flexible to manage, and allows robust security.
|
|
|
Cisco Unified Communication Manager 8.5.1 |
|
PCI Sub-Requirements Passed |
|
PCI 2 |
|
PCI 6 |
|
PCI 7 |
|
PCI 8 |
8.1, 8.2, 8.4, 8.5.5, 8.5.9, 8.5.10, 8.5.11, 8.5.12, 8.5.13, 8.5.14, 8.5.15 |
PCI 9 |
|
PCI 10 |
10.1, 10.2.1, 10.2.2,10.2.3, 10.2.4, 10.2.5, 10.2.6, 10.2.7, 10.3.1, 10.3.2, 10.3.3, 10.3.4, 10.3.5, 10.3.6, 10.4.2, 10.4.3, 10.5.1, 10.5.2, 10.5.3, 10.5.5 |
|
|
|
No compensating controls were required to satisfy any sub-requirements. |
|
|
|
|
No sub-requirements were failed. |
|
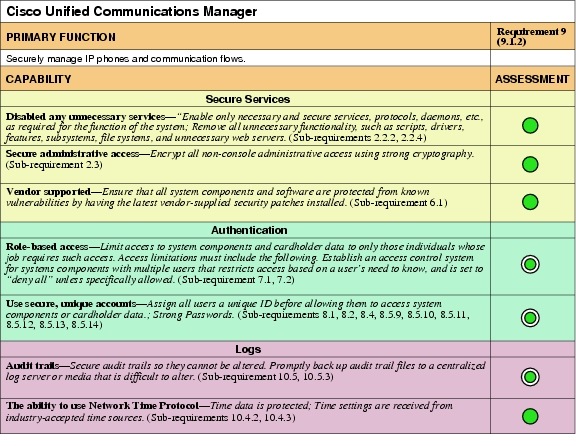
Primary PCI Function
The primary PCI function of Cisco Unified Communications Manager is to securely manage IP phones and communications flows, as well as securing publicly accessible network jacks (9.1.2).
Table 4-4 lists the component assessment details for Cisco Unified Communications Manager.
Design Considerations
The design features for improving security for the Cisco Unified Communications Manager appliance include:
•![]() Deployment as a clustered redundancy model that includes a publisher server and several subscriber servers
Deployment as a clustered redundancy model that includes a publisher server and several subscriber servers
•![]() Downloading and installing security patches when vulnerabilities are announced by the Cisco Product Security Incident Response Team (PSIRT)
Downloading and installing security patches when vulnerabilities are announced by the Cisco Product Security Incident Response Team (PSIRT)
•![]() Implementing Transport Layer Security (TLS) messaging for secure signaling and Secure RTP (SRTP) for encrypted media throughout the enterprise
Implementing Transport Layer Security (TLS) messaging for secure signaling and Secure RTP (SRTP) for encrypted media throughout the enterprise
•![]() Enabling device authentication and communication encryption using X.509 certificates that are signed by the Certificate Authority Proxy Function (CAPF) feature on the server
Enabling device authentication and communication encryption using X.509 certificates that are signed by the Certificate Authority Proxy Function (CAPF) feature on the server
Best practices for Cisco Unified Communications Manager phone security are as follows:
•![]() The Gratuitous ARP setting on the Cisco Unified IP Phones should be disabled.
The Gratuitous ARP setting on the Cisco Unified IP Phones should be disabled.
•![]() Disabling the web access setting prevents the phone from opening the HTTP port 80; this blocks access to the phone's internal web pages.
Disabling the web access setting prevents the phone from opening the HTTP port 80; this blocks access to the phone's internal web pages.
•![]() Disabling the PC Voice VLAN access setting in the phone configuration window prevents the devices connected to the PC port from using the voice VLAN functionality.
Disabling the PC Voice VLAN access setting in the phone configuration window prevents the devices connected to the PC port from using the voice VLAN functionality.
•![]() Disabling the Setting Access option in the phone configuration window prevents users from viewing and changing the phone options, including the Network Configuration options, directly on the phone.
Disabling the Setting Access option in the phone configuration window prevents users from viewing and changing the phone options, including the Network Configuration options, directly on the phone.
•![]() Cisco Unified IP Phones can be configured for authentication and encryption by installing a CTL file on the phones that includes security tokens, trusted server and firewall information, and CAPF.
Cisco Unified IP Phones can be configured for authentication and encryption by installing a CTL file on the phones that includes security tokens, trusted server and firewall information, and CAPF.
Physical Security
Cisco Physical Security solutions provide broad capabilities in video surveillance, IP cameras, electronic access control, and groundbreaking technology that converges voice, data, and physical security in one modular platform. Cisco Physical Security solutions enable customers to use the IP network as an open platform to build more collaborative and integrated physical security systems while preserving their existing investments in analog-based technology. As customers converge physical security infrastructures and operations and begin using the IP network as the platform, they can gain significant value through rapid access to relevant information and interoperability between systems. This creates a higher level of situational awareness and allows intelligent decisions to be made more quickly.
Cisco Video Surveillance
Video surveillance technology provides security monitoring capabilities within a store environment. Video surveillance for loss prevention can now be extended into the area of protecting the cardholder data environment.
As the core component of Cisco's video surveillance software portfolio, the Cisco Video Surveillance Media Server offers the power and flexibility to meet a diverse range of video surveillance requirements. The media server:
•![]() Uses IP technology to provide outstanding scalability in terms of sites, cameras, viewers, and storage
Uses IP technology to provide outstanding scalability in terms of sites, cameras, viewers, and storage
•![]() Delivers low-latency, high-quality, event-tagged video
Delivers low-latency, high-quality, event-tagged video
•![]() Supports a broad range of cameras, codecs (such as JPEG, and MPEG-4, and H.264), viewing platforms, and network topologies
Supports a broad range of cameras, codecs (such as JPEG, and MPEG-4, and H.264), viewing platforms, and network topologies
•![]() Archives at various frame rates, durations, and locations
Archives at various frame rates, durations, and locations
Quickly and effectively configure and manage video throughout your enterprise with the Cisco Video Surveillance Operations Manager (VSOM). Working in conjunction with the Cisco Video Surveillance Media Server and Cisco Video Surveillance Virtual Matrix, the Operations Manager meets the diverse needs of administrators, systems integrators, and operators by providing:
•![]() A web-based toolkit for configuration, management, display, and control of video from a wide variety of both Cisco and third-party surveillance endpoints
A web-based toolkit for configuration, management, display, and control of video from a wide variety of both Cisco and third-party surveillance endpoints
•![]() Management of a large number of Cisco Video Surveillance Media Servers, Virtual Matrixes, cameras, and users
Management of a large number of Cisco Video Surveillance Media Servers, Virtual Matrixes, cameras, and users
•![]() Flexible video recording options including motion-based, scheduled, and event-based
Flexible video recording options including motion-based, scheduled, and event-based
•![]() Comprehensive control of users and user roles including scheduling of operator shifts, event filters, and user-specific video views
Comprehensive control of users and user roles including scheduling of operator shifts, event filters, and user-specific video views
•![]() Detailed activity reports and system audit
Detailed activity reports and system audit
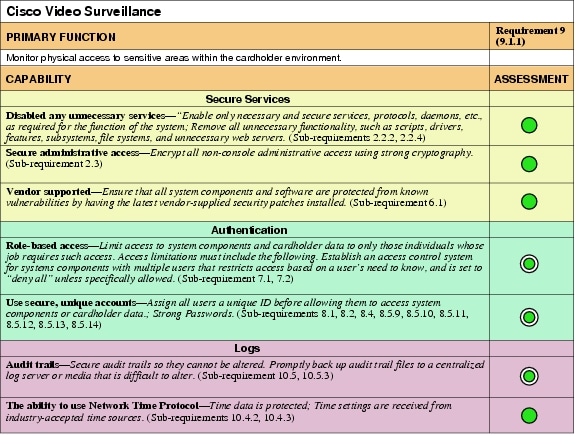
Primary PCI Function
The primary function of video surveillance is to monitor physical access to sensitive areas within the cardholder data environment (9.1.1).
Table 4-6 lists the component assessment details for the Cisco Video Surveillance solution.
Design Considerations
•![]() Ensure that cameras are positioned to monitor servers or systems within the cardholder data environment.
Ensure that cameras are positioned to monitor servers or systems within the cardholder data environment.
•![]() Cameras should be appropriately positioned to identify personnel accessing these systems.
Cameras should be appropriately positioned to identify personnel accessing these systems.
•![]() Ensure adequate storage of video for three months.
Ensure adequate storage of video for three months.
For more information, see the Cisco IP Video Surveillance Guide at the following URL: http://www.cisco.com/en/US/docs/solutions/Enterprise/Video/IPVS/IPVS_DG/IPVSchap4.html
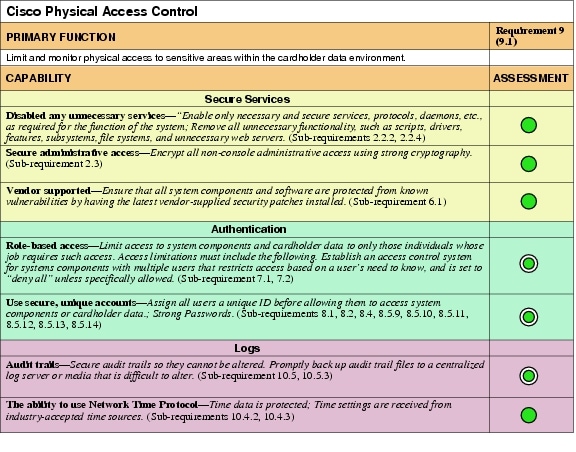
Cisco Physical Access Control
Cisco Physical Access Control allows retailers to secure their physical doors and locations. Cisco Physical Access Control addresses specific PCI requirements by providing:
•![]() Secure access to the server by supporting secure protocols such as HTTPS and also securing the accounts using strong passwords
Secure access to the server by supporting secure protocols such as HTTPS and also securing the accounts using strong passwords
•![]() Role-based access to the system by making use of profiles that can restrict access to the modules, depending on the roles
Role-based access to the system by making use of profiles that can restrict access to the modules, depending on the roles
•![]() Automated backup of events to a centralized server
Automated backup of events to a centralized server
•![]() Ability to archive audit reports on a centralized server
Ability to archive audit reports on a centralized server
Cisco Physical Access Control is a comprehensive IP-based solution that uses the IP network as a platform for integrated security operations (see Figure 4-1). It works with existing card readers, locks, and biometric devices and is integrated with Cisco Video Surveillance Manager (VSM) and with Cisco IP Interoperability and Collaboration System (IPICS).
Figure 4-1 Scalable, Modular Architecture
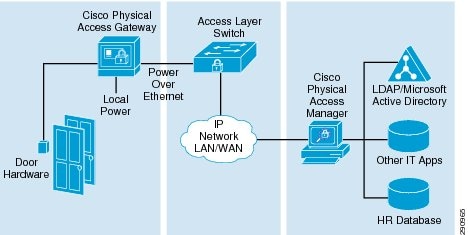
Cisco Physical Access Control has two components:
•![]() The hardware component, Cisco Physical Access Gateway, provides a modular and scalable platform to connect readers, inputs, and outputs to the system. The gateway scales from a single door to thousands of doors at a fixed cost per door.
The hardware component, Cisco Physical Access Gateway, provides a modular and scalable platform to connect readers, inputs, and outputs to the system. The gateway scales from a single door to thousands of doors at a fixed cost per door.
•![]() The software component, Cisco Physical Access Manager, manages the hardware, monitors activity, enrolls users, and integrates with IT applications and data stores.
The software component, Cisco Physical Access Manager, manages the hardware, monitors activity, enrolls users, and integrates with IT applications and data stores.
Primary PCI Function
The primary function of the CPAM appliance is to configure, manage, monitor, and report on the physical doors and door hardware, protecting sensitive areas within the cardholder data environment (9.1).
Table 4-8 lists the component assessment details for Cisco Physical Access Control.
Design Considerations
Best practices are as follows:
•![]() Use high availability for Cisco Physical Access Manager (PAM) servers.
Use high availability for Cisco Physical Access Manager (PAM) servers.
•![]() Map each store location and identify the following:
Map each store location and identify the following:
–![]() Actual doors and modules
Actual doors and modules
–![]() Door devices and module ports
Door devices and module ports
•![]() Use backup power supply for servers, modules, and devices.
Use backup power supply for servers, modules, and devices.
•![]() Cisco PAM was implemented following the Cisco Physical Access Manager Appliance User Guide, Release 1.2.0: http://www.cisco.com/en/US/docs/security/physical_security/access_control/cpam/1_2_0/english/user_guide/cpam_1_2_0.html
Cisco PAM was implemented following the Cisco Physical Access Manager Appliance User Guide, Release 1.2.0: http://www.cisco.com/en/US/docs/security/physical_security/access_control/cpam/1_2_0/english/user_guide/cpam_1_2_0.html
Cisco IronPort Email Security Solution
Cisco IronPort Email Security Solution uses data loss prevention (DLP) technology to block e-mail that is inadvertently sent containing cardholder data information.

Note ![]() The Cisco IronPort Email Security Solution was initially reviewed by Verizon Business and determined to be outside the scope of the PCI Audit. There is no Assessment Summary or Capability Assessment details for this product. However, Cisco IronPort Email Security Solution could potentially store or transmit sensitive cardholder data if used with the default settings for message tracking. Sensitive information in messages would be automatically forwarded in clear text to administrators, and recipients. These same messages would also be stored un-encrypted. The design considerations below detail how to properly configure the Cisco IronPort Email Security Solution to avoid this pitfall.
The Cisco IronPort Email Security Solution was initially reviewed by Verizon Business and determined to be outside the scope of the PCI Audit. There is no Assessment Summary or Capability Assessment details for this product. However, Cisco IronPort Email Security Solution could potentially store or transmit sensitive cardholder data if used with the default settings for message tracking. Sensitive information in messages would be automatically forwarded in clear text to administrators, and recipients. These same messages would also be stored un-encrypted. The design considerations below detail how to properly configure the Cisco IronPort Email Security Solution to avoid this pitfall.
Cisco IronPort Email Security Solution provides sophisticated and scalable mechanisms that help to minimize the downtime associated with e-mail-borne malware and simplify the administration of corporate e-mail systems, while offering insight into the e-mail system operation. Capabilities include the following:
•![]() Spam protection
Spam protection
•![]() Data loss prevention (DLP)
Data loss prevention (DLP)
•![]() Virus defense
Virus defense
•![]() E-mail encryption tracking and reporting tools
E-mail encryption tracking and reporting tools
Primary PCI Function
Although data loss prevention is not covered by a specific PCI requirement, Cisco IronPort Email Security Solution helps in achieving PCI compliance by preventing the transmission of cardholder data over open public networks via e-mail.
Design Considerations
•![]() Do not enable logging, storage, or forwarding messages identified as containing cardholder data.
Do not enable logging, storage, or forwarding messages identified as containing cardholder data.
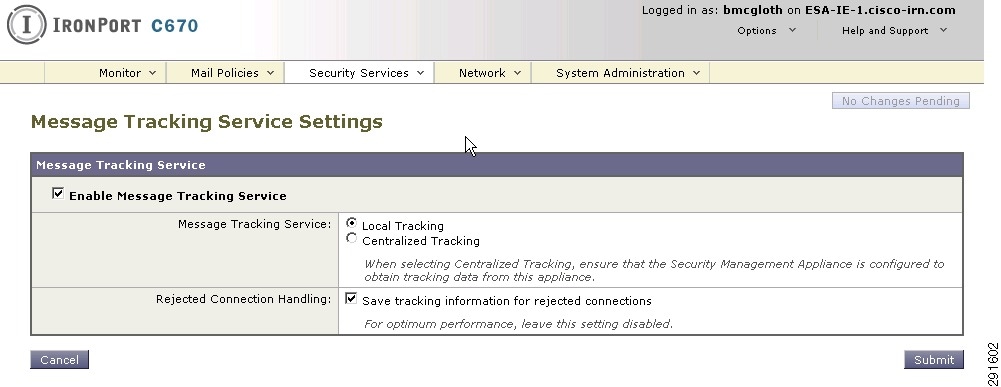
•![]() For IronPort to analyze messages passing through it, message tracking must be enabled, as shown in Figure 4-2.
For IronPort to analyze messages passing through it, message tracking must be enabled, as shown in Figure 4-2.
Figure 4-2 Enable IronPort Message Tracking
•![]() Create policy in IronPort to drop messages containing credit card numbers, but not to forward that message to administrators. Ensure that the "include original message" checkbox is not selected, as shown in Figure 4-3.
Create policy in IronPort to drop messages containing credit card numbers, but not to forward that message to administrators. Ensure that the "include original message" checkbox is not selected, as shown in Figure 4-3.
Figure 4-3 Policy in IronPort Excluding Original Message

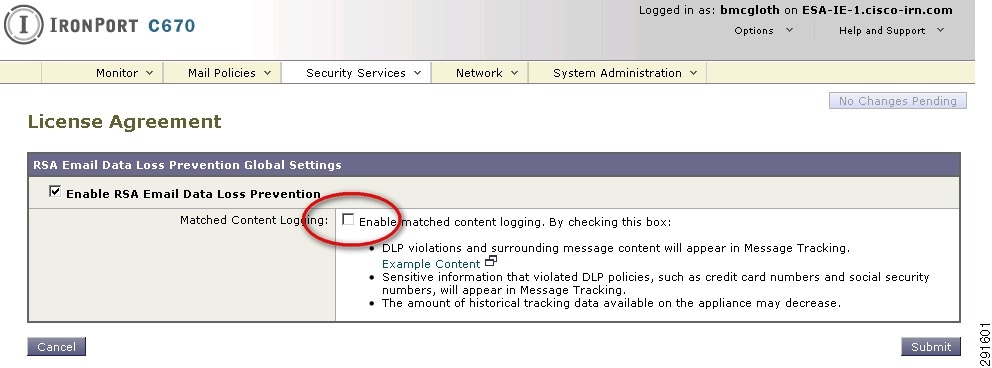
•![]() To ensure that messages identified as containing credit card information are not stored in the local system, you must disable logging of matched content, as shown in Figure 4-4. The local log of the IronPort server is not a safe encrypted place to store cardholder data.
To ensure that messages identified as containing credit card information are not stored in the local system, you must disable logging of matched content, as shown in Figure 4-4. The local log of the IronPort server is not a safe encrypted place to store cardholder data.
Figure 4-4 IronPort DLP—Matched Content Logging Disabled
Hosts
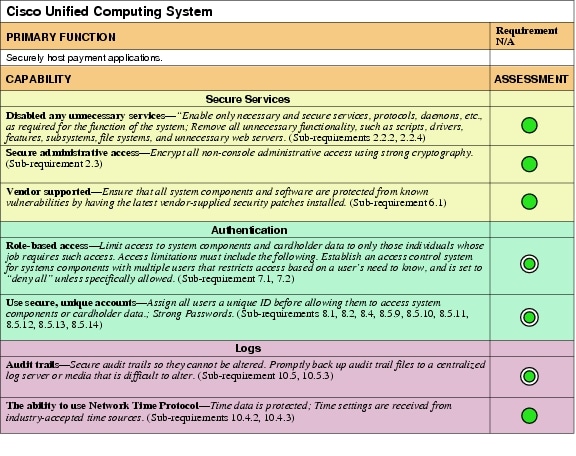
Cisco Unified Computing System
The Cisco Unified Computing System (UCS) is used to securely deploy sensitive and compliance-related applications. Provisioning options, including virtualization technology, allow the mixing of sensitive and non-sensitive applications without compromising scope boundaries.
Improve IT responsiveness to rapidly changing business demands with this next-generation data center platform. Cisco UCS accelerates the delivery of new services simply, reliably, and securely through end-to-end provisioning and migration support.
Benefits include the following:
•![]() Streamlines data center resources to reduce total cost of ownership
Streamlines data center resources to reduce total cost of ownership
•![]() Scales service delivery to increase business agility
Scales service delivery to increase business agility
•![]() Radically reduces the number of devices requiring setup, management, power, cooling, and cabling
Radically reduces the number of devices requiring setup, management, power, cooling, and cabling
|
|
|
Cisco UCS Manager version 1.3(1p) |
|
PCI Sub-Requirements Passed |
|
PCI 2 |
|
PCI 6 |
|
PCI 7 |
|
PCI 8 |
8.1, 8.2, 8.4, 8.5.5, 8.5.9, 8.5.10, 8.5.11, 8.5.12, 8.5.13, 8.5.14, 8.5.15 |
PCI 10 |
10.1, 10.2, 10.2.1, 10.2.2, 10.2.3, 10.2.4, 10.2.5, 10.2.6, 10.2.7, 10.3, 10.3.1, 10.3.2, 10.3.4, 10.3.5, 10.3.6, 10.4.2, 10.4.3, 10.5.1, 10.5.2, 10.5.3, 10.5.5 |
|
|
|
No compensating controls were required to satisfy any sub-requirements. |
|
|
|
|
No sub-requirements were failed. |
|
Primary PCI Function
The main function of Cisco UCS is to securely host one primary compliance-related function per physical or virtual server.
It provides segmentation of sensitive applications from out-of-scope applications via physical and virtualization technology. Although technically, a firewall or ACL is used to enforce PCI Requirement 1, Cisco UCS extends Layer 3 boundaries to virtual network and storage adapters within the chassis. Using VLANs and VSANs, Cisco UCS allows a retailer to separate its payment systems (in-scope) from other non-sensitive data (out-of-scope).
Table 4-10 lists the component assessment details for Cisco UCS.
Design Considerations
•![]() Cisco UCS allows for the provisioning of individual servers on blades. Each blade can host a native operating system such as Windows 2008 server, or a virtualization hypervisor system such as VMware ESX/ESXi. These provisioning options represent a primary function for the server blade. In the lab validation, VMware ESX was installed on each of the Cisco UCS blades, and several VM hosts were then configured, each with one primary function. Each server blade is provisioned via a profile. Profiles can be created locally in Cisco UCS Manager or centrally using the Vblock provisioning utility, Unified Infrastructure Manager (UIM), which provides simplified Vblock management by combining provisioning with configuration, change, and compliance management.
Cisco UCS allows for the provisioning of individual servers on blades. Each blade can host a native operating system such as Windows 2008 server, or a virtualization hypervisor system such as VMware ESX/ESXi. These provisioning options represent a primary function for the server blade. In the lab validation, VMware ESX was installed on each of the Cisco UCS blades, and several VM hosts were then configured, each with one primary function. Each server blade is provisioned via a profile. Profiles can be created locally in Cisco UCS Manager or centrally using the Vblock provisioning utility, Unified Infrastructure Manager (UIM), which provides simplified Vblock management by combining provisioning with configuration, change, and compliance management.
•![]() EMC SAN is a primary component of the VCE architecture for Vblock Infrastructure Platforms. Vblock 1 is designed for medium to high numbers of virtual machines, and is ideally suited to a broad range of usage scenarios, including shared services, e-mail, file and print, virtual desktops, and collaboration.
EMC SAN is a primary component of the VCE architecture for Vblock Infrastructure Platforms. Vblock 1 is designed for medium to high numbers of virtual machines, and is ideally suited to a broad range of usage scenarios, including shared services, e-mail, file and print, virtual desktops, and collaboration.
•![]() Cisco UCS allows for the provisioning of individual servers on blades. Each blade can host a native operating system such as Windows 2008 server, or a virtualization hypervisor system such as VMware ESX/ESXi.
Cisco UCS allows for the provisioning of individual servers on blades. Each blade can host a native operating system such as Windows 2008 server, or a virtualization hypervisor system such as VMware ESX/ESXi.
•![]() Each Cisco UCS server blade is provisioned via a profile. Profiles can be created locally in Cisco UCS Manager or centrally using the Vblock provisioning utility, EMC Unified Infrastructure Manager (UIM), which provides simplified Vblock management by combining provisioning with configuration, change, and compliance management.
Each Cisco UCS server blade is provisioned via a profile. Profiles can be created locally in Cisco UCS Manager or centrally using the Vblock provisioning utility, EMC Unified Infrastructure Manager (UIM), which provides simplified Vblock management by combining provisioning with configuration, change, and compliance management.
•![]() The PCI standard requires one primary function per server. When using virtualization technology, the single primary server function is extended to individual virtual machines.
The PCI standard requires one primary function per server. When using virtualization technology, the single primary server function is extended to individual virtual machines.
•![]() The hypervisor of an individual blade is considered insecure for segmenting scopes of compliance. Therefore, when putting non-sensitive VM servers with sensitive VM servers on the same physical blade, the non-sensitive would be included in the scope of the audit.
The hypervisor of an individual blade is considered insecure for segmenting scopes of compliance. Therefore, when putting non-sensitive VM servers with sensitive VM servers on the same physical blade, the non-sensitive would be included in the scope of the audit.
•![]() The UCS system securely segments network and storage to each blade, which allows mixing of sensitive and non-sensitive applications across different physical blades of the chassis.
The UCS system securely segments network and storage to each blade, which allows mixing of sensitive and non-sensitive applications across different physical blades of the chassis.
•![]() PCI requires a 15-minute timeout for administrative functions. Cisco UCS does not feature an explicit session timeout. Administration time limits would need to be enabled systemically through active directory policy to the admin workstation desktops, locking them when there is no activity.
PCI requires a 15-minute timeout for administrative functions. Cisco UCS does not feature an explicit session timeout. Administration time limits would need to be enabled systemically through active directory policy to the admin workstation desktops, locking them when there is no activity.
Cisco UCS was implemented using the Cisco UCS installation guides: http://www.cisco.com/en/US/products/ps10276/prod_installation_guides_list.html
Cisco UCS Express on Services Ready Engine
The Cisco Unified Computing System Express (UCS Express) and Services Ready Engine (SRE) allows retailers to securely deploy sensitive applications directly within the routing platform. By using UCS Express, retailers can remove legacy compute resources in the store, saving space, energy, and operational costs.
Cisco UCS Express is a converged networking, computing, and virtualization platform for hosting essential business applications in the store location. The SRE modules are router blades for the second generation of Cisco Integrated Services Routers (ISR G2) that provide the capability to host Cisco, third-party, and custom applications. A service-ready deployment model enables store applications to be provisioned remotely on the modules at any time. Cisco SRE modules have their own processors, storage, network interfaces, and memory, which operate independently of the host router resources and help ensure maximum concurrent routing and application performance.
|
|
|
Cisco UCS Express version 1.1 on SRE900 |
|
PCI Sub-Requirements Passed |
|
PCI 2 |
|
PCI 6 |
|
PCI 7 |
|
PCI 8 |
|
PCI 10 |
10.1, 10.2, 10.2.1, 10.2.2, 10.2.3, 10.2.4, 10.2.5, 10.2.6, 10.2.7, 10.3, 10.3.1, 10.3.2, 10.3.3, 10.3.4, 10.3.5, 10.3.6, 10.4.2, 10.4.3, 10.5.1, 10.5.2, 10.5.3 |
|
|
|
PCI 8 |
|
|
|
|
No sub-requirements were failed. |
|
Primary PCI Function
The main function of Cisco UCS Express is to securely host one primary compliance-related function per physical or virtual server.
It provides segmentation of sensitive applications from out-of-scope applications via physical and virtualization technology. Although technically, a firewall or ACL is used to enforce PCI Requirement 1, UCS extends Layer 3 boundaries to virtual NIC and storage adapters within the chassis. Using VLANs and VSANs, Cisco UCS allows a retailer to separate its payment systems (in-scope) from other non-sensitive data (out-of-scope).
Table 4-12 lists the component assessment details for the Cisco UCS Express and Cisco SRE.
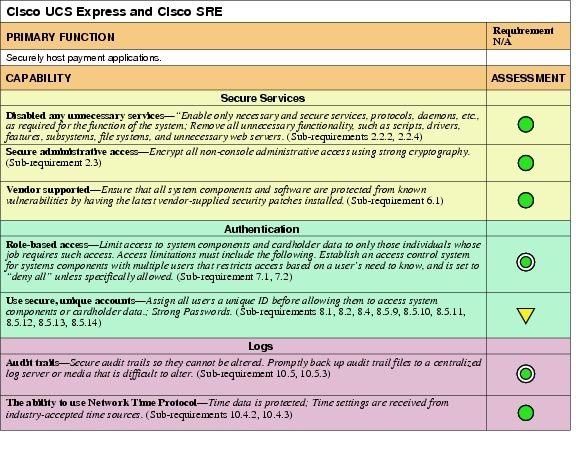
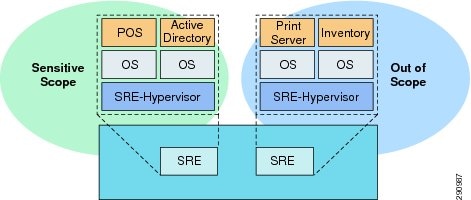
Design Considerations
The major consideration when using Cisco UCS Express with sensitive applications is the security of the hypervisor. PCI considers all hypervisors to be insecure. Therefore, use separate Cisco UCS Express implementations when scooping. Although it is acceptable to mix non-sensitive applications onto a Cisco UCS Express deployment with sensitive applications, that brings those applications into scope and audit. (See Figure 4-5.)
Figure 4-5 Using UCS Express with Cisco SRE
•![]() The audited version 1.1 of UCS Express has several limitations with local user accounts. There is no capability to use central authentication or management. This resulted in a need for compensating controls that are detailed below.
The audited version 1.1 of UCS Express has several limitations with local user accounts. There is no capability to use central authentication or management. This resulted in a need for compensating controls that are detailed below.

Note ![]() Newer versions of UCS Express (version 1.5 +) enable central management of the VMware ESXi on Cisco UCS Express through vCenter (upgrade license required) as well as eliminate the Cisco console VM and local user management/VMware ESXi management restrictions. With the new release, Cisco UCS can manage users on VMware ESXi exactly as it would on a standalone VMware ESXi 4.1 server. This feature was not able to be validated before publishing of this guide, and has not been assessed by Verizon Business or tested in the Cisco PCI solution lab.
Newer versions of UCS Express (version 1.5 +) enable central management of the VMware ESXi on Cisco UCS Express through vCenter (upgrade license required) as well as eliminate the Cisco console VM and local user management/VMware ESXi management restrictions. With the new release, Cisco UCS can manage users on VMware ESXi exactly as it would on a standalone VMware ESXi 4.1 server. This feature was not able to be validated before publishing of this guide, and has not been assessed by Verizon Business or tested in the Cisco PCI solution lab.

Note ![]() The Cisco UCS Express module comes installed with VMware ESXi. This is the primary function for the server module. Each module can host several independent operating systems as virtual servers. Each virtual server should have only one primary function.
The Cisco UCS Express module comes installed with VMware ESXi. This is the primary function for the server module. Each module can host several independent operating systems as virtual servers. Each virtual server should have only one primary function.
•![]() Cisco UCS Express requires the use of VLANs in the router. Depending on the deployment within the store, this may require the use of bridged virtual interfaces.
Cisco UCS Express requires the use of VLANs in the router. Depending on the deployment within the store, this may require the use of bridged virtual interfaces.
•![]() Cisco UCS Express is based on VMware's ESXi and uses vSphere client for management.
Cisco UCS Express is based on VMware's ESXi and uses vSphere client for management.
Scope Administration
Authentication
Cisco Secure Access Control Server
Cisco Secure Access Control Server (ACS) was used as a central authentication system for the majority of products validated in this solution. It links user authentication to Windows Active Directory using group mapping that segments users based on their role and function.
Cisco Secure ACS is an access policy control platform that helps you comply with growing regulatory and corporate requirements. By using a single authentication method for all system devices, insight into who made changes is simplified for internal administration, assessors, and post-breach audits. It supports multiple scenarios simultaneously, including the following:
•![]() Device administration—Authenticates administrators, authorizes commands, and provides an audit trail
Device administration—Authenticates administrators, authorizes commands, and provides an audit trail
•![]() Remote access—Works with VPN and other remote network access devices to enforce access policies
Remote access—Works with VPN and other remote network access devices to enforce access policies
•![]() Wireless—Authenticates and authorizes wireless users and hosts and enforces wireless-specific policies
Wireless—Authenticates and authorizes wireless users and hosts and enforces wireless-specific policies
•![]() Network admission control—Communicates with posture and audit servers to enforce admission control policies
Network admission control—Communicates with posture and audit servers to enforce admission control policies
Cisco Secure ACS lets you centrally manage access to network resources for a growing variety of access types, devices, and user groups. These key features address the current complexities of network access control:
•![]() Support for a range of protocols including Extensible Authentication Protocol (EAP) and non-EAP protocols provides the flexibility to meet all your authentication requirements
Support for a range of protocols including Extensible Authentication Protocol (EAP) and non-EAP protocols provides the flexibility to meet all your authentication requirements
•![]() Integration with Cisco products for device administration access control allows for centralized control and auditing of administrative actions
Integration with Cisco products for device administration access control allows for centralized control and auditing of administrative actions
•![]() Support for external databases, posture brokers, and audit servers centralizes access policy control and lets you integrate identity and access control systems
Support for external databases, posture brokers, and audit servers centralizes access policy control and lets you integrate identity and access control systems
|
|
|
Cisco Secure Access Control Server Release 4.2(1) Build 15 Patch 3 |
|
PCI Sub-Requirements Passed |
|
PCI 2 |
|
PCI 6 |
|
PCI 7 |
|
PCI 8 |
8.1, 8.2, 8.4, 8.5.5, 8.5.9, 8.5.10, 8.5.11, 8.5.12, 8.5.13, 8.5.14, 8.5.15 |
PCI 10 |
10.1, 10.2.1, 10.2.2,10.2.3, 10.2.4, 10.2.5, 10.2.6, 10.2.7, 10.3.1, 10.3.2, 10.3.3, 10.3.4, 10.3.5, 10.3.6, 10.4.2, 10.4.3, 10.5.1, 10.5.2, 10.5.3, 10.5.5 |
|
|
|
No compensating controls were required to satisfy any sub-requirements. |
|
|
|
|
No sub-requirements were failed. |
|
Primary PCI Function
The main function of Cisco Secure ACS is to securely authenticate users toi the systems within the cardholder environment.
Table 4-14 lists the component assessment details for Cisco Secure ACS.
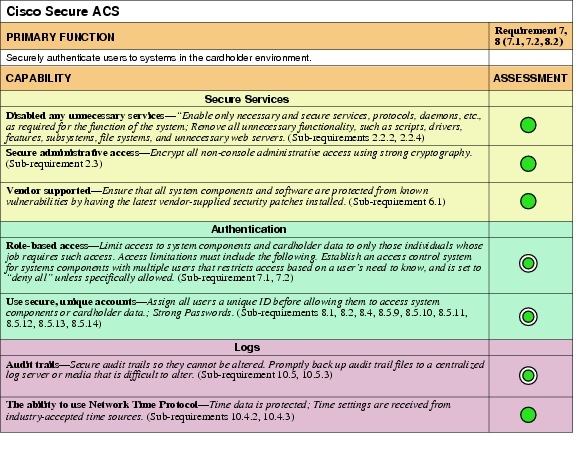
Design Considerations
•![]() Cisco Secure ACS has been configured to authenticate individual users using Active Directory (AD). This is accomplished by creating user groups in AD and mapping them to role-based groups in Cisco Secure ACS. This provides the granularity of secure authentication needed to address the PCI specification.
Cisco Secure ACS has been configured to authenticate individual users using Active Directory (AD). This is accomplished by creating user groups in AD and mapping them to role-based groups in Cisco Secure ACS. This provides the granularity of secure authentication needed to address the PCI specification.
•![]() The solution used the windows versions of Cisco Secure ACS. The CSA client was installed to protect and alert on unauthorized access of the log and audit trail.
The solution used the windows versions of Cisco Secure ACS. The CSA client was installed to protect and alert on unauthorized access of the log and audit trail.
•![]() Remove the default accounts for administration.
Remove the default accounts for administration.
•![]() Enable HTTPS and disable HTTP.
Enable HTTPS and disable HTTP.
•![]() User authentication services for Cisco Secure ACS are linked to a centralized Active Directory user database
User authentication services for Cisco Secure ACS are linked to a centralized Active Directory user database
RSA Authentication Manager
RSA Authentication Manager is the management component of the RSA SecurID®, a two-factor authentication solution, which provides a much more reliable level of user authentication than reusable passwords. SecurID authentication is based on something you know (a password or PIN) and something you have (an authenticator), and can be used to achieve compliance to PCI requirement 8.3, which requires two-factor authentication for remote access to the network by employees, administrators, and third parties. As the management component, RSA Authentication Manager is used to verify authentication requests and centrally administer authentication policies for enterprise networks.
|
|
|
RSA Authentication Manager 7.1 Service Pack 2 |
|
PCI Sub-Requirements Passed |
|
PCI 2 |
|
PCI 6 |
|
PCI 7 |
|
PCI 8 |
8.1, 8.2, 8.3, 8.4, 8.5.5, 8.5.9, 8.5.10, 8.5.11, 8.5.12, 8.5.13, 8.5.14, 8.5.15 |
PCI 10 |
10.1, 10.2.1, 10.2.2,10.2.3, 10.2.4, 10.2.5, 10.2.6, 10.2.7, 10.3.1, 10.3.2, 10.3.3, 10.3.4, 10.3.5, 10.3.6, 10.4.2, 10.4.3, 10.5.1, 10.5.2, 10.5.3, 10.5.5 |
|
|
|
No compensating controls were required to satisfy any sub-requirements. |
|
|
|
|
No sub-requirements were failed. |
|
Primary PCI Function
The main function of RSA Authentication Manager is to securely authenticate remote users using two-factor authentication.
Table 4-16 lists the component assessment details for RSA Authentication Manager.
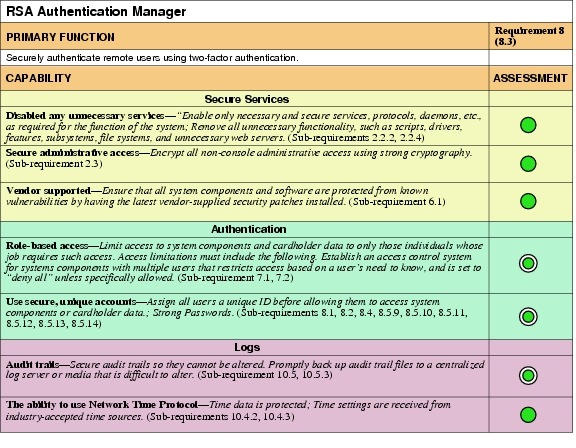
Design Considerations
RSA Authentication Manager stores and processes highly sensitive authentication information and should be deployed and operated in a secure manner. Detailed recommendations are found in the RSA Authentication Manager Security Best Practices Guide, which can be downloaded from RSA Secure Care Online (https://knowledge.rsasecurity.com/).
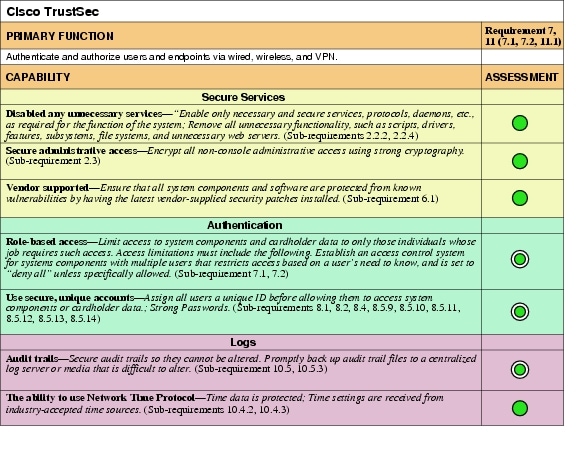
Cisco TrustSec
Cisco TrustSec, the security component of the Cisco Borderless Network architecture, provides visibility and control into who and what is connected to the network. Cisco TrustSec allows organizations to embrace the rapidly changing business environment of mobility, virtualization, and collaboration while enforcing compliance, maintaining data integrity and confidentiality, and establishing a consistent global access policy. Cisco TrustSec allows businesses to gain complete control over the access points into their networks. This includes all wired, wireless, and VPN network entry points.
Cisco TrustSec ensures that you know what devices and users are on your network, and that those devices and users comply with your security policies via the following components:
•![]() Cisco Identity Services Engine (ISE)—The Cisco ISE is a next-generation policy manager that delivers authentication, authorization, and accounting (AAA); posture; profiling; and guest management services on a single platform. The Cisco ISE automatically discovers and classifies endpoints, provides the right level of access based on identity, and provides the ability to enforce endpoint compliance by checking a device's posture. The Cisco ISE also provides advanced authorization and enforcement capabilities, including Security Group Access (SGA) through the use of security group tags (SGTs) and security group access control lists (ACLs). Administrators can centrally create and manage access control policies for users and endpoints in a consistent fashion, and gain end-to-end visibility into everything that is connected to the network.
Cisco Identity Services Engine (ISE)—The Cisco ISE is a next-generation policy manager that delivers authentication, authorization, and accounting (AAA); posture; profiling; and guest management services on a single platform. The Cisco ISE automatically discovers and classifies endpoints, provides the right level of access based on identity, and provides the ability to enforce endpoint compliance by checking a device's posture. The Cisco ISE also provides advanced authorization and enforcement capabilities, including Security Group Access (SGA) through the use of security group tags (SGTs) and security group access control lists (ACLs). Administrators can centrally create and manage access control policies for users and endpoints in a consistent fashion, and gain end-to-end visibility into everything that is connected to the network.
•![]() Cisco TrustSec Identity on Cisco Networking Infrastructure—Identity-based networking services on the Cisco routing, switching and wireless infrastructure provides the ability to authenticate users and devices via features such as 802.1x, MAC authentication bypass (MAB), and Web Authentication. In addition, this same infrastructure enforces the appropriate access into parts of the network via VLANs, downloadable or named ACLs, and security group ACLs.
Cisco TrustSec Identity on Cisco Networking Infrastructure—Identity-based networking services on the Cisco routing, switching and wireless infrastructure provides the ability to authenticate users and devices via features such as 802.1x, MAC authentication bypass (MAB), and Web Authentication. In addition, this same infrastructure enforces the appropriate access into parts of the network via VLANs, downloadable or named ACLs, and security group ACLs.
•![]() Client—Cisco AnyConnect VPN Client is a software client that enables you to deploy a single 802.1x authentication framework to access wired and wireless networks while the Cisco NAC agent delivers endpoint posture information. The Cisco TrustSec architecture also supports native OS supplicants.
Client—Cisco AnyConnect VPN Client is a software client that enables you to deploy a single 802.1x authentication framework to access wired and wireless networks while the Cisco NAC agent delivers endpoint posture information. The Cisco TrustSec architecture also supports native OS supplicants.
The Cisco TrustSec solution offers the following benefits:
•![]() Allows enterprises to authenticate and authorize users and endpoints via wired, wireless, and VPN with consistent policy throughout the enterprise
Allows enterprises to authenticate and authorize users and endpoints via wired, wireless, and VPN with consistent policy throughout the enterprise
•![]() Prevents unauthorized network access to protect corporate assets
Prevents unauthorized network access to protect corporate assets
•![]() Provides complete guest lifecycle management by empowering sponsors to on-board guests, thus reducing IT workload
Provides complete guest lifecycle management by empowering sponsors to on-board guests, thus reducing IT workload
•![]() Discovers, classifies, and controls endpoints connecting to the network to enable the appropriate services per endpoint type
Discovers, classifies, and controls endpoints connecting to the network to enable the appropriate services per endpoint type
•![]() Enforces security policies by blocking, isolating, and repairing noncompliant machines in a quarantine area without needing administrator attention
Enforces security policies by blocking, isolating, and repairing noncompliant machines in a quarantine area without needing administrator attention
•![]() Offers a built-in monitoring, reporting, and troubleshooting console to assist helpdesk operators and administrators streamline operations.
Offers a built-in monitoring, reporting, and troubleshooting console to assist helpdesk operators and administrators streamline operations.
Figure 4-6 shows an example of a Cisco ISE-based TrustSec LAN deployment.
Figure 4-6 Cisco ISE-Based TrustSec LAN Deployment
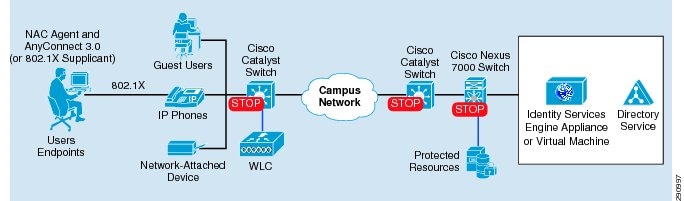
Primary PCI Function
Cisco ISE and TrustSec identity features detect and prevent rogue wireless devices from connecting to in-scope PCI networks (11.1); in addition, Cisco ISE locks down publicly accessible network ports to only authorized devices and users (9.1.2). In addition to its primary focus, Cisco ISE can also help with compliance and enforcement of requirements 6.1, 7.1, 7.2, 8.3, 8.5, and 10.
Table 4-18 lists the component assessment details for the Cisco TrustSec Solution.
Design Considerations
For the purposes of this guide, Cisco ISE is configured to authenticate individual users and ISE Admin users using Active Directory (AD). Cisco ISE is also used to profile and assess the posture of individual wired and wireless devices to ensure that they comply with the PCI standard. Cisco ISE relies on TrustSec wired and wireless identity features such as 802.1x, MAB, and web portal authentication on Cisco infrastructure to collect user identity information. It relies on the Cisco ISE NAC agent and the Cisco ISE profiler engine to collect posture and profiling information from devices. Note the following:
•![]() The solution tested used the virtual machine appliance version of Cisco ISE running on an ESX platform.
The solution tested used the virtual machine appliance version of Cisco ISE running on an ESX platform.
•![]() The default accounts for administration are removed.
The default accounts for administration are removed.
•![]() HTTPS is enabled and HTTP disabled.
HTTPS is enabled and HTTP disabled.
•![]() Cisco ISE communicates with the Cisco switches and wireless controllers using RADIUS.
Cisco ISE communicates with the Cisco switches and wireless controllers using RADIUS.
•![]() Cisco ISE can use dynamic VLAN and port or VLAN access control rules to provide PCI segmentation of a network. For example, members of the PCI active directory group are automatically moved to the PCI VLAN when they connect to the network. Cisco ISE can then apply strong access lists to this VLAN or directly to the user switch port to accomplish segmentation.
Cisco ISE can use dynamic VLAN and port or VLAN access control rules to provide PCI segmentation of a network. For example, members of the PCI active directory group are automatically moved to the PCI VLAN when they connect to the network. Cisco ISE can then apply strong access lists to this VLAN or directly to the user switch port to accomplish segmentation.
•![]() Access control rule sets must adhere to a "least amount of access necessary" policy. Rules must be defined by specific source/destination addressing and TCP/UDP ports required for the cardholder data environment on the point-of-sale networks.
Access control rule sets must adhere to a "least amount of access necessary" policy. Rules must be defined by specific source/destination addressing and TCP/UDP ports required for the cardholder data environment on the point-of-sale networks.
•![]() Configure appropriate banner messages on login, incoming, and exec modes of the router. The login banner warning should not reveal the identity of the company that owns or manages the router. The incoming and executive banners should state that these areas are considered private and that unauthorized access will result in prosecution to the full extent of the law.
Configure appropriate banner messages on login, incoming, and exec modes of the router. The login banner warning should not reveal the identity of the company that owns or manages the router. The incoming and executive banners should state that these areas are considered private and that unauthorized access will result in prosecution to the full extent of the law.
•![]() The Cisco ISE system is configured to be compliance with all of the access controls, logging controls, and other general system controls required by PCI DSS 2.0.
The Cisco ISE system is configured to be compliance with all of the access controls, logging controls, and other general system controls required by PCI DSS 2.0.
Management
Cisco Security Manager
The Cisco Security Manager is a powerful yet easy-to-use solution for configuring firewall, VPN, and IPS policies on Cisco security appliances, firewalls, routers, and switch modules.
Cisco Security Manager helps enable enterprises to manage and scale security operations efficiently and accurately. Its end-to-end tools provide consistent policy enforcement, quick troubleshooting of security events, and summarized reports from across the security deployment.
Cisco Security Manager enables you to centrally manage security policies over 250 types and models of Cisco security devices. Cisco Security Manager supports integrated provisioning of firewall, IPS, and VPN (most site-to-site, remote access, and SSL) services across the following:
•![]() Cisco IOS/ISR/ASR routers
Cisco IOS/ISR/ASR routers
•![]() Cisco Catalyst switches
Cisco Catalyst switches
•![]() Cisco ASA and PIX security appliances
Cisco ASA and PIX security appliances
•![]() Cisco Catalyst Service Modules related to firewall, VPN, and IPS
Cisco Catalyst Service Modules related to firewall, VPN, and IPS
•![]() Cisco IPS appliances and various service modules for routers and ASA devices
Cisco IPS appliances and various service modules for routers and ASA devices
For a complete list of devices and OS versions supported by Cisco Security Manager, see Supported Devices and Software Versions for Cisco Security Manager at the following URL: http://www.cisco.com/en/US/products/ps6498/products_device_support_tables_list.html.
The high-performance and easy-to-use integrated event viewer allows you to centrally monitor events from IPS, ASA, and FWSM devices and correlate them to the related configuration policies. This helps identify problems and troubleshoot configurations. Then, using Configuration Manager, you can make adjustments to the configurations and deploy them. Event Viewer supports event management for Cisco ASA, IPS, and FWSM devices.
In addition to the Primary Event Data Store, events can be copied and stored in the Extended Event Data Store. The Extended Event Data Store can be used to back up and archive a larger number of events. This is useful for historical review and analysis of events where Event Viewer can gather event data from both the Primary Event Data Store and the Extended Event Data Store. The Extended Event Data Store can be enabled in Event Management in Security Manager's Administration settings.
For supported platforms and more information, see the "Monitoring and Diagnostics" section of the User Guide for Cisco Security Manager 4.1 at the following URL: http://www.cisco.com/en/US/products/ps6498/products_user_guide_list.html.
The new integrated report management allows you to generate and schedule ASA, IPS, and remote access VPN reports. Reports for ASA and IPS devices are created by aggregating and summarizing events collected by the Event Viewer. Security reports can be used to efficiently monitor, track, and audit network use and security problems reported by managed devices. Report Manager helps in developing and customizing reports for Cisco ASA and IPS devices.
For supported platforms and more information, see the "Monitoring and Diagnostics" part of the User Guide for Cisco Security Manager 4.1 at the following URL: http://www.cisco.com/en/US/products/ps6498/products_user_guide_list.html.
|
|
|
Cisco Security Manager version 4.0.1 |
|
PCI Sub-Requirements Passed |
|
PCI 2 |
|
PCI 6 |
|
PCI 7 |
|
PCI 8 |
8.1, 8.2, 8.4, 8.5.5, 8.5.9, 8.5.10, 8.5.11, 8.5.12, 8.5.13, 8.5.14, 8.5.15 |
PCI 10 |
10.1, 10.2.1, 10.2.2,10.2.3, 10.2.4, 10.2.5, 10.2.6, 10.2.7, 10.3.1, 10.3.2, 10.3.3, 10.3.4, 10.3.5, 10.3.6, 10.4.2, 10.4.3, 10.5.1, 10.5.2, 10.5.3, 10.5.5 |
|
|
|
No compensating controls were required to satisfy any sub-requirements. |
|
|
|
|
No sub-requirements were failed. |
|
Primary PCI Function
The primary function of Cisco Security Manager is to implement security configuration in firewalls, routers, and intrusion detection devices based on policy templates to secure the cardholder data environment. (1.2)
Table 4-20 lists the component assessment details for Cisco Security Manager.
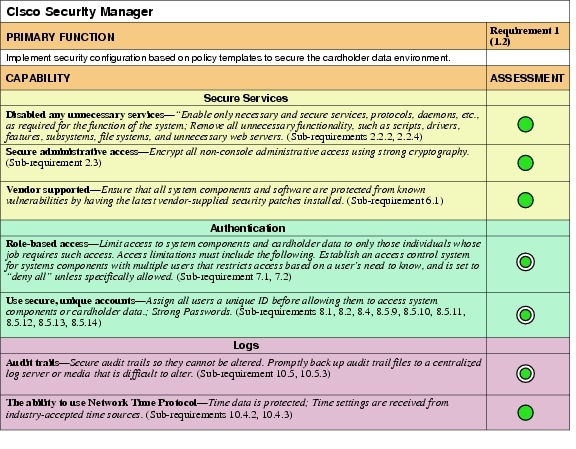
Design Considerations
•![]() Use descriptive notes for each rule set. These are displayed as remarks in the running configuration.
Use descriptive notes for each rule set. These are displayed as remarks in the running configuration.
•![]() Virtualize firewall rule set deployment by using a consistent interface naming standard.
Virtualize firewall rule set deployment by using a consistent interface naming standard.
•![]() Apply the anti-spoofing feature to all interfaces using FlexConfig.
Apply the anti-spoofing feature to all interfaces using FlexConfig.
EMC Ionix Network Configuration Manager
EMC Ionix Network Configuration Manager is a model-based, automated network compliance, change, and configuration management product. It delivers features, advantages, and benefits that ensure the compliance, operational efficiency, security, and availability of your network.
Ionix Network Configuration Manager supplies industry-recognized best practices, enhancing collaborative network infrastructure design, verifying controlled change processes, providing network device and service configuration transparency, and ensuring compliance with corporate and regulatory requirements.
|
|
|
EMC Ionix Network Configuration Manager version 4.1.0.863 HF7 |
|
PCI Sub-Requirements Passed |
|
PCI 2 |
|
PCI 6 |
|
PCI 7 |
|
PCI 8 |
8.1, 8.2, 8.4, 8.5.5, 8.5.9, 8.5.10, 8.5.11, 8.5.12, 8.5.13, 8.5.14, 8.5.15 |
PCI 10 |
10.2.1, 10.2.2,10.2.3, 10.2.4, 10.2.5, 10.2.6, 10.2.7, 10.3.1, 10.3.2, 10.3.3, 10.3.4, 10.3.5, 10.3.6, 10.4.2, 10.4.3, 10.5.1, 10.5.2, 10.5.3, 10.5.5 |
|
|
|
No compensating controls were required to satisfy any sub-requirements. |
|
|
|
|
No sub-requirements were failed. |
|
Primary PCI Function
The primary function is to manage network device configuration and verify configuration against policy templates.
Table 4-22 lists the component assessment details for EMC Ionix Network Configuration Manager.
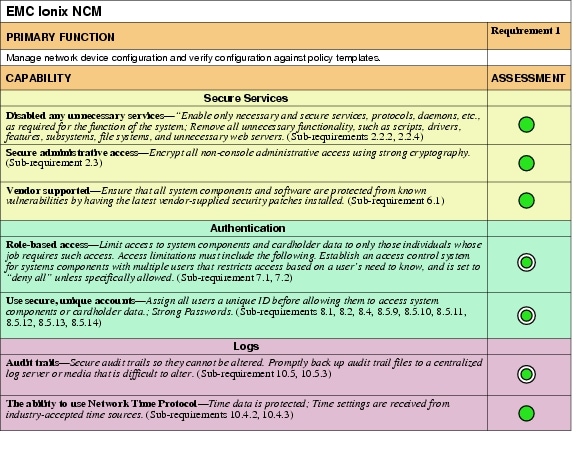
Design Considerations
No specific design considerations apply when implementing EMC Ionix NCM.
RSA Archer
The RSA Archer eGRC Suite for enterprise governance, risk, and compliance allows your organization to jumpstart your PCI compliance program by conducting continuous, automated assessments to gain the visibility you need to manage and mitigate risk.

Note ![]() RSA Archer was initially reviewed by Verizon Business and determined to be outside the scope of the PCI Audit. RSA Archer does store, process, or transmit sensitive cardholder data. There are no Assessment Summary or Capability Assessment details for this product.
RSA Archer was initially reviewed by Verizon Business and determined to be outside the scope of the PCI Audit. RSA Archer does store, process, or transmit sensitive cardholder data. There are no Assessment Summary or Capability Assessment details for this product.
RSA Archer provides a comprehensive library of policies, control standards, procedures, and assessments mapped to PCI DSS and other regulatory standards. RSA Archer is designed to orchestrate and visualize the security of both VMware virtualization infrastructure and physical infrastructure from a single console. (See Figure 4-7.)
Figure 4-7 Using Firewall and IDS/IPS

One of the major changes to PCI DSS 2.0 is its clarification on the use of virtualization technology in the cardholder data environment. If virtualization technology is used, the virtualization platform is always in scope for PCI. More than 130 control procedures in the Archer library have been written specifically for VMWare environments and have been mapped to PCI requirements. The RSA Cloud Security and Compliance solution includes software that substantially automates the assessment of whether VMware security controls have been implemented correctly. The results of these automated configuration checks are fed directly into the RSA Archer eGRC Platform, which also captures the results of configuration checks for physical assets via pre-built integration with commercially available scan technologies.
Although a significant number of the VMware control procedures are tested automatically, the remainder must be tested manually because their status cannot be directly inferred from the environment. For these control procedures, project managers can issue manual assessments from the RSA Archer eGRC Platform, using a pre-loaded bank of questions. Project managers can create new questionnaires within minutes and issue them to appropriate users based on asset ownership. Those users are automatically notified of their assessments via rules-driven workflow and My Tasks lists, and can complete their assessments online.
Results for both automated and manual assessments are consolidated in the RSA Archer eGRC Platform and mapped to PCI DSS and other regulations and standards. IT and security operations teams can then monitor compliance with regulations and internal policies across the physical and virtual infrastructure by device, policy, procedure, regulation, and other criteria. This information is presented through a graphical dashboard view, making the information easy to digest and understand.
Configuring the physical and virtual infrastructure according to best-practice security guidelines and regulatory requirements is critical. However, the security and compliance process does not stop there. Organizations also require the ability to monitor misconfigurations, policy violations, and control failures across their infrastructure; and to respond swiftly with appropriate remediation steps. Deficiencies identified through automated and manual configuration checks are captured within the RSA Archer eGRC Platform for management. Control failures are then assigned to appropriate personnel, who can respond by completing remediation tasks or logging exception requests that identify effective compensating controls and are tracked in a Policy Management dashboard, as shown in Figure 4-8.
Figure 4-8 RSA Archer Policy Management

Encryption
A subtle, yet potentially significant change to key management has been introduced with the PCI 2.0 standard. With past versions of the DSS, annual key rotations were required for encryption keys. PCI DSS 2.0 now requires that keys are rotated at the end of their cryptoperiod, and references the NIST 800-57 Special Publication to determine what an appropriate cryptoperiod is. The NIST 800-57 Special Publication is a 324-page, three-part document. Merchants, and even QSAs, may not have the expertise to fully understand such a document that includes countless encryption scenarios, with cryptoperiods ranging from as short as a day and as long as three years.
In an ideal world, with all parties being expert cryptographers, this risk-based change to the standard would be very appropriate and most welcome. However, given the number of scenarios and criteria for determining an appropriate cryptoperiod, it could suggest that this change is too subjective and may become a point of contention between a merchant and QSA assessor, as to what is an appropriate cryptoperiod, whereas the former, more prescriptive control, did not allow for flexibility in this area.
RSA Data Protection Manager
RSA Data Protection Manager (formerly RSA Key Manager) provides encryption, tokenization, and key management capabilities. It can be used to achieve PCI Requirement 3 compliance for protecting stored cardholder data, regardless of where the information resides.
RSA Data Protection Manager is an easy-to-use management tool for encrypting keys at the database, file server, and storage layers. It is designed to lower the total cost of ownership and simplify the deployment of encryption throughout the enterprise. It also helps ensure that information is properly secured and fully accessible when needed at any point in its lifecycle through a powerful management console and built-in high availability features. RSA Data Protection Manager provides a comprehensive platform for enforcing and managing the security of sensitive data.
|
|
|
RSA Data Protection Manager version KM-3.1 / AM-6.1.SP3 |
|
PCI Sub-Requirements Passed |
|
PCI 2 |
|
PCI 6 |
|
PCI 7 |
|
PCI 8 |
8.1, 8.2, 8.4, 8.5.5, 8.5.9, 8.5.10, 8.5.11, 8.5.12, 8.5.13, 8.5.14, 8.5.15 |
PCI 10 |
10.1, 10.2.1, 10.2.2,10.2.3, 10.2.4, 10.2.5, 10.2.6, 10.2.7, 10.3.1, 10.3.2, 10.3.3, 10.3.4, 10.3.5, 10.3.6, 10.4.2, 10.4.3, 10.5.1, 10.5.2, 10.5.3, 10.5.5 |
|
|
|
No compensating controls were required to satisfy any sub-requirements. |
|
|
|
|
No sub-requirements were failed. |
|
Primary PCI Function
The main function of RSA Data Protection Manager is to securely manage the keys that protect cardholder data. (3.5)
Table 4-24 lists the component assessment details for RSA Data Protection Manager.
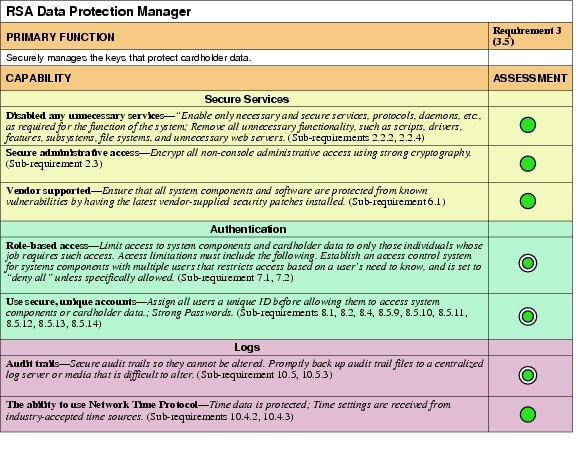
Design Considerations
RSA Data Protection Manager's encryption and key management capabilities can be used to store the data in a compliant manner. RSA Data Protection Manager provides application development libraries that support a wide range of development languages and enables developers to easily integrate encryption into point-of-sale, payment, CRM, ERP, and other business applications that create or process sensitive information. RSA Data Protection Manager can also be used to encrypt data as it flows to both disk and tape by providing key management services to Cisco MDS or EMC storage systems.
Because there were no card handling applications in the simulated lab environment, RSA Data Protection Manager was integrated with Cisco MDS to encrypt all data in the environment regardless of whether it was cardholder data or not.
Public Key Infrastructure (PKI) Requirements
In an RSA Data Protection Manager deployment, a PKI needs to be set up to enable secure communication between the RSA Data Protection server and its clients. (See Figure 4-9.)
Figure 4-9 RSA Data Protection Manager Deployment
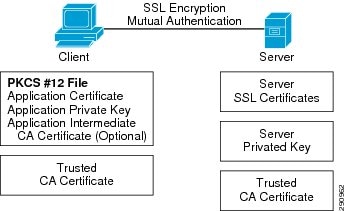
The certificates and credentials that need to be prepared include:
•![]() Client PKCS#12 certificate and key pair—Used to authenticate RSA Data Protection Manager clients to the RSA Data Protection Server
Client PKCS#12 certificate and key pair—Used to authenticate RSA Data Protection Manager clients to the RSA Data Protection Server
•![]() Server SSL certificate and key pair—Used by RSA Data Protection Manager Clients to authenticate the server
Server SSL certificate and key pair—Used by RSA Data Protection Manager Clients to authenticate the server
•![]() Trusted CA certificate—Installed on both clients and the server to verify the signature of certificates sent by a peer. For example, a RSA Key Manager Client has a trusted CA certificate to verify the signature of the Server certificate.
Trusted CA certificate—Installed on both clients and the server to verify the signature of certificates sent by a peer. For example, a RSA Key Manager Client has a trusted CA certificate to verify the signature of the Server certificate.
•![]() Middle CA certificate (optional)—If a certificate is not signed directly by a trusted CA certificate, a middle CA certificate should be installed and sent during SSL connection to verify the certificate chain.
Middle CA certificate (optional)—If a certificate is not signed directly by a trusted CA certificate, a middle CA certificate should be installed and sent during SSL connection to verify the certificate chain.
Security Recommendation
Because of vulnerabilities with RSA signatures with a small public exponent, especially 3, RSA recommends that an exponent of F4 (216+1) be used.
Storage
EMC SAN Disk Array
The EMC SAN disk array is used to securely store sensitive compliance data within the data center. Using virtual storage technology, retailers are able to safely combine (in-scope) sensitive date with (out-of-scope) data while maintaining the compliance boundary.
EMC technology combines midrange networked storage with innovative technology and robust software capabilities to manage and consolidate your data.
|
|
|
EMC CLARiiON CX-240 EMC Unified Infrastructure Manager version 2.0.1.1.160 |
|
PCI Sub-Requirements Passed |
|
PCI 2 |
|
PCI 6 |
|
PCI 7 |
|
PCI 8 |
8.1, 8.2, 8.4, 8.5.5, 8.5.9, 8.5.10, 8.5.11, 8.5.12, 8.5.13, 8.5.14, 8.5.15 |
PCI 10 |
10.1, 10.2.1, 10.2.2,10.2.3, 10.2.4, 10.2.5, 10.2.6, 10.2.7, 10.3.1, 10.3.2, 10.3.3, 10.3.4, 10.3.5, 10.3.6, 10.4.2, 10.4.3, 10.5.1, 10.5.2, 10.5.3, 10.5.5 |
|
|
|
No compensating controls were required to satisfy any sub-requirements. |
|
|
|
|
No sub-requirements were failed. |
|
Primary PCI Function
The main function of the EMC SAN disk array is to store cardholder data. There is no direct PCI requirement for this storage function.
Table 4-26 lists the component assessment details for the EMC SAN disk array.
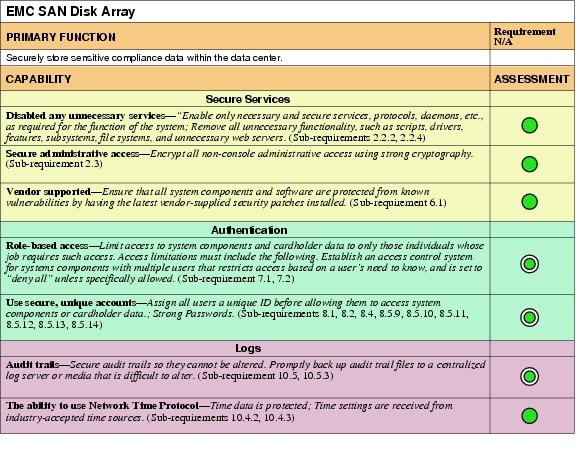
Design Considerations
The EMC SAN disk array is a primary component of VCE Vblock architecture. Vblock 1 is designed for medium-to-high numbers of virtual machines, and is ideally suited to a broad range of usage scenarios, including shared services, e-mail, file and print, virtual desktops, and collaboration.
Monitoring
RSA enVision
RSA enVision is a security information and event management (SIEM) platform that provides the capability to implement PCI requirement 10 to track and monitor all access to network resources and cardholder data. RSA enVision does this by collecting, permanently archiving, and processing all the log and event data generated by devices and applications within your network, and generating alerts when it observes suspicious patterns of behavior. Administrators can interrogate the full volume of stored data through an intuitive dashboard, and can use advanced analytical software to gain visibility and understanding of how their network is used and the threats and risks to the infrastructure and applications.
The RSA enVision platform can draw logs from tens of thousands of devices at once, including Cisco network devices, the VCE Vblock infrastructure, the VMware virtual environment, Cisco ASA firewalls, Cisco IPS devices, Cisco IronPort E-mail Appliance, other RSA products, and the HyTrust appliance. Out of the box, RSA enVision can produce PCI 2.0 compliance reports and alerts based on the log and event data it collects. RSA enVision also offers powerful tools to create custom reports and alerts specific to your environment.
|
|
|
|
|
|
PCI Sub-Requirements Passed |
|
PCI 2 |
|
PCI 6 |
|
PCI 7 |
|
PCI 8 |
8.1, 8.2, 8.4, 8.5.5, 8.5.9, 8.5.10, 8.5.11, 8.5.12, 8.5.13, 8.5.14, 8.5.15 |
PCI 10 |
10.1, 10.2.1, 10.2.2,10.2.3, 10.2.4, 10.2.5, 10.2.6, 10.2.7, 10.3.1, 10.3.2, 10.3.3, 10.3.4, 10.3.5, 10.3.6, 10.4.2, 10.4.3, 10.5.1, 10.5.2, 10.5.3 |
|
|
|
No compensating controls were required to satisfy any sub-requirements. |
|
|
|
|
No sub-requirements were failed. |
|
Primary PCI Function
The main function of RSA enVision is to securely store and correlate the system logs that is receives. (10.5)
Table 4-28 lists the component assessment details for RSA enVision.
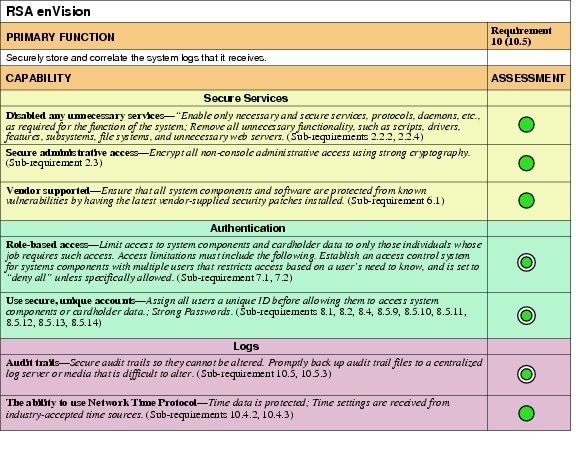
Design Considerations
Depending on the size of your network, RSA enVision may be deployed as a standalone, self-contained, security-hardened appliance or in a distributed deployment to cope with the demands of the largest enterprise networks. When deployed in a distributed architecture, multiple dedicated appliances are deployed where required to perform key roles. Local and remote collectors perform data collection. Data servers manage the data. Application servers perform analysis and reporting. Data itself can be stored using direct attached, online, near-line or offline storage from the full EMC storage portfolio.
RSA enVision does not require any client-side agents to pull log or event data from your infrastructure or applications. RSA enVision can integrate with event sources through standard protocols such as syslog or SNMP by configuring the event source to send data to enVision. For richer event data, enVision integrates with some event sources through their APIs or directly with their database backends. Specific event source device configuration procedures can be found at RSA Secure Care Online (https://knowledge.rsasecurity.com/)
RSA enVision is sold as a standalone appliance. It is available in a variety of hardware options based on the requirements of the enterprise design. The system comes pre-installed on an already hardened operation system.
HyTrust Appliance
Vblock Infrastructure Platforms from VCE allow retailers to take advantage of the architectural, operational, and financial benefits of virtualization in their PCI infrastructure. HyTrust Appliance (HTA) complements Vblock capabilities by providing:
•![]() Access control for virtual infrastructure including least privilege, separation of duties, and two-factor authentication
Access control for virtual infrastructure including least privilege, separation of duties, and two-factor authentication
•![]() Granular and exhaustive logging and auditing
Granular and exhaustive logging and auditing
•![]() Segmentation of infrastructure to support virtualized applications
Segmentation of infrastructure to support virtualized applications
PCI DSS 2.0 clarifies the use of virtualization technology with the cardholder data environment (CDE) and specifies that the platform is always in scope. This requirement is consistent with additional risks introduced by mobility and the fast-paced change rate of virtualized assets that can now be reconfigured, relocated, and duplicated by remote administrators. These capabilities combined with poor access control create a significant risk. Hypervisor logs geared toward software maintenance and troubleshooting are obviously useful, but not in the context of a compliance audit.
HyTrust Appliance systematically addresses the three broad areas of IT control objectives (access and user administration, change and configuration, and operations), by proactively enforcing policies for all administrative access, regardless of access method: Secure Shell (SSH) to host, VMware vSphere client to host, or VMware vCenter or any of the programmatic access. HyTrust Appliance provides two-factor authentication and role-based access control, logical segmentation of shared infrastructure, root password vaulting, and audit-quality logs of every attempted access.
|
|
|
HyTrust version 2.2.1.14064 |
|
PCI Sub-Requirements Passed |
|
PCI 2 |
|
PCI 6 |
|
PCI 7 |
|
PCI 8 |
8.1, 8.2, 8.4, 8.5.5, 8.5.9, 8.5.10, 8.5.11, 8.5.12, 8.5.13, 8.5.14, 8.5.15 |
PCI 10 |
10.1, 10.2.1, 10.2.2,10.2.3, 10.2.4, 10.2.5, 10.2.6, 10.2.7, 10.3.1, 10.3.2, 10.3.3, 10.3.4, 10.3.5, 10.3.6, 10.4.2, 10.4.3, 10.5.1, 10.5.2, 10.5.3 |
|
|
|
No compensating controls were required to satisfy any sub-requirements. |
|
|
|
|
No sub-requirements were failed. |
|
Primary PCI Function
The primary function of HyTrust Appliance is to provide an automated control and audit facility for the virtual infrastructure and cloud stack. (2, 7, and 10).
Table 4-30 lists the component assessment details for the HyTrust Appliance.
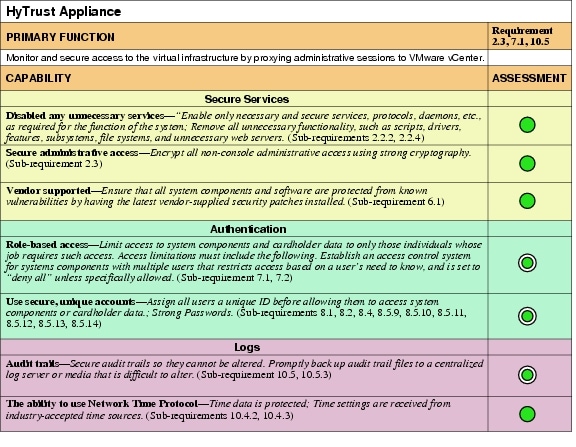
Design Considerations
Define rules and deploy policy to activate protection for the virtual infrastructure.
Administrators can define custom rules that restrict entitlement based on specific virtual infrastructure objects that users need to access and manage. Rules that define entitlement can be based on pre-defined roles or administrators can use custom user-defined roles.
The Hytrust appliance provides complete logging of administrator actions by proxying VMware vCenter client connections to the vSphere management server, and clients that try to connect directly to ESX/ESXi hosts. This logging includes the source IP address of the clients, permitted actions and actions that are blocked because the client may not have sufficient privileges (all requirements of PCI that VMware cannot perform natively).
Additional In Scope Devices
Any system that stores, processes, or transmits cardholder data is considered in scope for PCI compliance. Infrastructure components that provide network services such as load balancing or WAN optimization are often not considered when contemplating compliance. However, if these technologies pass sensitive data, they are subject to the same controls of traditional security products.
The capabilities that these components need to meet are highlighted in Table 4-1.
Infrastructure
Routing
Router—Store
The Cisco Integrated Services Router (ISR) is the component that is used as the primary routing and security platform of the stores. It can securely scale to the requirements of the business because it has integrated firewall, VPN, and IPS/IDS capabilities. WAN options include traditional terrestrial paths using T1, T3, Ethernet, and so on; wireless options include 3G/4G/Wi-Fi modules connecting stores over public paths for higher availability.
The Cisco ISR consolidates voice, data, and security into a single platform with local and centralized management services. It delivers scalable rich media, service virtualization, and energy efficiency ideal for deployments requiring business continuity, WAN flexibility, and superior collaboration capabilities. The Cisco ISR uses field-upgradeable motherboards, with services such as security, mobility, WAN optimization, unified communications, video, and customized applications.
Table 4-32 lists the performance of the Cisco ISR in satisfying PCI sub-requirements.
|
|
|
CISCO891W version c890-universalk9-mz.151-3.T.bin CISCO1941W-A/K9 version c1900-universalk9-mz.SPA.151-3.T.bin CISCO2921/K9 version c2900-universalk9-mz.SPA.151-3.T.bin CISCO2951/K9 version c2951-universalk9-mz.SPA.151-3.T.bin CISCO3945-SPE150/K9 version c3900-universalk9-mz.SPA.151-3.T.bin |
|
PCI Sub-Requirements Passed |
|
PCI 1 |
1.2.1, 1.2.2, 1.2.3, 1.3.1, 1.3.2, 1.3.3, 1.3.4, 1.3.5, 1.3.6, 1.3.7, 1.3.8 |
PCI 2 |
|
PCI 4 |
|
PCI 6 |
|
PCI 7 |
|
PCI 8 |
8.1, 8.2, 8.4, 8.5.5, 8.5.9, 8.5.10. 8.5.11, 8.5.12, 8.5.13, 8.5.14, 8.5.15 |
PCI 10 |
10.1, 10.2, 10.2.1, 10.2.2, 10.2.3, 10.2.4, 10.2.5, 10.2.6, 10.2.7, 10.3, 10.3.1, 10.3.2, 10.3.3, 10.3.4, 10.3.5, 10.3.6, 10.4.1,10.4.2, 10.4.3, 10.5.1, 10.5.2, 10.5.3 |
PCI 11 |
|
|
|
|
No compensating controls were required to satisfy any sub-requirements. |
|
|
|
|
No sub-requirements were failed. |
|
Primary PCI Function
The main function of the Cisco ISR is the segmentation of PCI scope and enforcement of that new scope boundary.
It has five primary functions/capabilities in relation to PCI.
1. ![]() As a router, directing traffic between networks
As a router, directing traffic between networks
A router in its simplest form routes between networks. By segmenting a network into sub-networks, a retailer can isolate sensitive information from non-sensitive information. The Cisco ISR can segment and route sensitive traffic separately from non-sensitive traffic to reduce the overall scope of a company's cardholder data environment. Depending on risk vectors within the store, different levels of enforcement might be required at the segmented scope boundary level. (See items 2, 3 and 4 following.)
2. ![]() As a router with ACLs, restricting traffic between the cardholder data environment and other areas of the network
As a router with ACLs, restricting traffic between the cardholder data environment and other areas of the network
A router with ACLs can be used to enforce segmented traffic only if the ACLs are used to filter and segment private networks of the retailer. They may not be used to filter untrusted networks. For example, many retailers have a central chokepoint in their data center that is the connection to the Internet (an untrusted network). As long as the retailer has only untrusted network connections outside of the store, (the data center, in this case), then a retailer may use router access lists to protect its scope from its own private internal networks. As soon as the store connects to untrusted networks directly, items 3 and 4 below become relevant. (See Figure 4-10.)
Figure 4-10 ACLs Segment Traffic

3. ![]() As a stateful firewall, restricting traffic between the cardholder data environment and other areas of the network
As a stateful firewall, restricting traffic between the cardholder data environment and other areas of the network
As soon as any untrusted network is introduced at the store level, firewalling and IDS/IPS must be deployed. The following are examples of untrusted networks:
–![]() The Internet
The Internet
–![]() Wireless
Wireless
–![]() Satellite
Satellite
–![]() 3G/4G cellular backup
3G/4G cellular backup
4. ![]() As an intrusion prevention system, inspecting all traffic going to and from the cardholder data environment
As an intrusion prevention system, inspecting all traffic going to and from the cardholder data environment
As soon as any untrusted network is introduced at the store level, firewalling and IDS/IPS must be deployed. (See Figure 4-11.)
Figure 4-11 Using Firewall and IDS/IPS
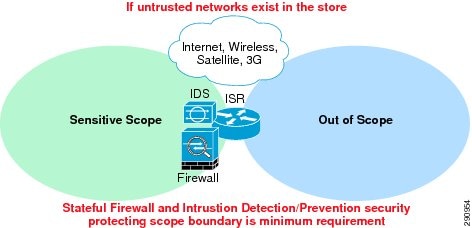
The Cisco ISR can be used to address segmentation challenges and enforce scope boundaries depending on the levels required by the retailer. Each of these features can be enabled by using a license key. This feature is particularly useful for retailers because it does not require a visit to every store to enable the firewall/IPS/IDS capability. If these capabilities are not used within the Cisco ISR, an external component(s) can be used to address this level of scope enforcement.
5. ![]() As a VPN system, encrypting all traffic going to and from the store across open and public networks.
As a VPN system, encrypting all traffic going to and from the store across open and public networks.
The Cisco ISR can be used to address the need to encrypt the transmission of cardholder data across open, public networks such as 3G/4G/Wi-fi, and satellite technologies using SSL and IPSec technologies.
Table 4-32 lists the component assessment details for the Cisco ISR.
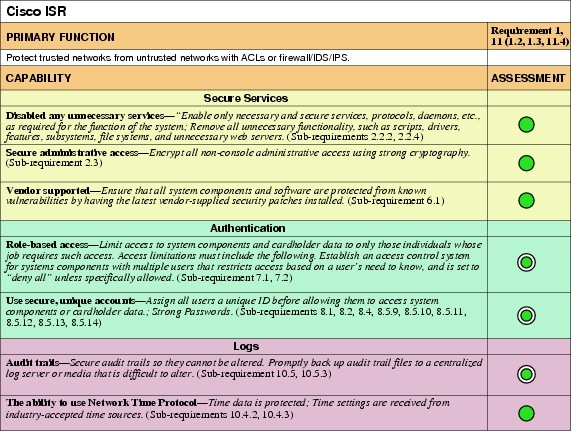
Design Considerations
•![]() The security features of the Cisco ISR routers in the store designs are configured using Cisco Security Manager. When adopting this as the primary method of router configuration, Cisco does not recommend making changes directly to the command-line interface (CLI) of the router. Unpredictable results can occur when central and local management are used concurrently.
The security features of the Cisco ISR routers in the store designs are configured using Cisco Security Manager. When adopting this as the primary method of router configuration, Cisco does not recommend making changes directly to the command-line interface (CLI) of the router. Unpredictable results can occur when central and local management are used concurrently.
•![]() The general configuration of the Cisco ISR routers in the store architectures are maintained with EMC Ionix Network Configuration Manager.
The general configuration of the Cisco ISR routers in the store architectures are maintained with EMC Ionix Network Configuration Manager.
•![]() Firewall rule sets must adhere to a "least amount of access necessary" policy. Rules must be defined by specific source/destination addressing and TCP/UDP ports required for the cardholder data environment (for example, point-of-sale) networks.
Firewall rule sets must adhere to a "least amount of access necessary" policy. Rules must be defined by specific source/destination addressing and TCP/UDP ports required for the cardholder data environment (for example, point-of-sale) networks.
•![]() Ensure that inspection rules and/or zones are enabled on the Cisco ISR router so that the firewall maintains state (none are enabled by default).
Ensure that inspection rules and/or zones are enabled on the Cisco ISR router so that the firewall maintains state (none are enabled by default).
•![]() Redundant Cisco IOS firewalls do not have the capability to maintain state between the routers. During a failure, client communication sessions need to be re-established through the alternate router. If high availability with statefulness is a requirement, Cisco ASA firewalls should be used.
Redundant Cisco IOS firewalls do not have the capability to maintain state between the routers. During a failure, client communication sessions need to be re-established through the alternate router. If high availability with statefulness is a requirement, Cisco ASA firewalls should be used.
•![]() Access into a store router from the WAN needs to be protected by a store-located firewall filter if the WAN technology is considered untrusted/public (for example, Internet DSL or cable network, public 3G or 4G, satellite). In the Cisco Retail PCI Solution lab, a private MPLS WAN is simulated, and filtering of the store traffic occurs on the WAN link of all in-scope locations.
Access into a store router from the WAN needs to be protected by a store-located firewall filter if the WAN technology is considered untrusted/public (for example, Internet DSL or cable network, public 3G or 4G, satellite). In the Cisco Retail PCI Solution lab, a private MPLS WAN is simulated, and filtering of the store traffic occurs on the WAN link of all in-scope locations.
•![]() Disable the HTTP server service on the router and enable the HTTP secure server.
Disable the HTTP server service on the router and enable the HTTP secure server.
•![]() Disable use of Telnet and enable use of only SSH version 2.
Disable use of Telnet and enable use of only SSH version 2.
•![]() Configure the session-timeout and exec-timeout commands to 15 minutes or less on the console, VTY, and line interfaces on the router. Disable the AUX interface.
Configure the session-timeout and exec-timeout commands to 15 minutes or less on the console, VTY, and line interfaces on the router. Disable the AUX interface.
•![]() Configure appropriate banner messages on login, incoming, and exec modes of the router. The login banner warning should not reveal the identity of the company that owns or manages the router. The incoming and executive banners should state that these areas are considered private and that unauthorized access will result in prosecution to the full extent of the law.
Configure appropriate banner messages on login, incoming, and exec modes of the router. The login banner warning should not reveal the identity of the company that owns or manages the router. The incoming and executive banners should state that these areas are considered private and that unauthorized access will result in prosecution to the full extent of the law.
•![]() Configure the primary login authentication of the router to be directed to the Cisco Secure ACS. Individual user account profiles need to be created. Configure secondary or tertiary authentication local to the router itself in the event of a WAN or failure.
Configure the primary login authentication of the router to be directed to the Cisco Secure ACS. Individual user account profiles need to be created. Configure secondary or tertiary authentication local to the router itself in the event of a WAN or failure.
•![]() Use the no service password-recovery command in conjunction with the service password encryption command to prevent password theft by physical compromise of the router.
Use the no service password-recovery command in conjunction with the service password encryption command to prevent password theft by physical compromise of the router.
•![]() Change default passwords and community strings to appropriate complexity.
Change default passwords and community strings to appropriate complexity.
•![]() Configure logs to be sent to a centralized syslog server, such as RSA enVision.
Configure logs to be sent to a centralized syslog server, such as RSA enVision.
•![]() Configure NTP to ensure all logging is coordinated.
Configure NTP to ensure all logging is coordinated.
•![]() Disable un-necessary services (for example, Bootp, Pad, ipv6).
Disable un-necessary services (for example, Bootp, Pad, ipv6).
•![]() Shutdown unused interfaces.
Shutdown unused interfaces.
Each of the store designs was implemented using guidance from the following:
•![]() Cisco Enterprise Branch Security Design Guide— http://www.cisco.com/en/US/docs/solutions/Enterprise/Branch/E_B_SDC1.html
Cisco Enterprise Branch Security Design Guide— http://www.cisco.com/en/US/docs/solutions/Enterprise/Branch/E_B_SDC1.html
•![]() Branch/WAN Design Zone— http://www.cisco.com/en/US/netsol/ns816/networking_solutions_design_guidances_list.html
Branch/WAN Design Zone— http://www.cisco.com/en/US/netsol/ns816/networking_solutions_design_guidances_list.html
Additional information for router hardening can be found at the following URLs:
•![]() Cisco Guide to Harden Cisco IOS Devices— http://www.cisco.com/en/US/tech/tk648/tk361/technologies_tech_note09186a0080120f48.shtml
Cisco Guide to Harden Cisco IOS Devices— http://www.cisco.com/en/US/tech/tk648/tk361/technologies_tech_note09186a0080120f48.shtml
•![]() Cisco IOS Security Configuration Guide, Release 12.4— http://www.cisco.com/en/US/docs/ios/security/configuration/guide/12_4/sec_12_4_book.html
Cisco IOS Security Configuration Guide, Release 12.4— http://www.cisco.com/en/US/docs/ios/security/configuration/guide/12_4/sec_12_4_book.html
Routers—Data Center
The primary function of data center routers from a PCI perspective is routing between sensitive networks and out-of scope networks. Data center routers function as WAN aggregation routers or connecting to larger networks such as the Internet. Therefore, performance and scalability are equally important as securely passing data. For this reason, and unlike the routers in the store, security functions are typically separated physically into distinct appliances. The Cisco 7206VXR and the the Cisco ASR1002 routers were used for the Internet edge and store WAN edge portions of the network within the solution testing.
Primary PCI Function
The main function of the data center routers is the segmentation of PCI scope and enforcement of that new scope boundary. The data center router has four primary functions/capabilities in relation to PCI:
1. ![]() As a router, directing traffic between networks
As a router, directing traffic between networks
A router in its simplest form routes between networks. By segmenting a network into sub-networks, a retailer can isolate sensitive information from non-sensitive information. Data center routers can segment and route sensitive traffic separately from non-sensitive traffic to reduce the overall scope of a company's cardholder data environment. Depending on risk vectors, different levels of enforcement might be required at the segmented scope boundary level. (See items 2, 3, and 4 following.)
2. ![]() As a router with ACLs, restricting traffic between the cardholder data environment and other areas of the network
As a router with ACLs, restricting traffic between the cardholder data environment and other areas of the network
A router with ACLs can be used to enforce segmented traffic only if the ACLs are used to filter and segment private networks of the retailer. They may not be used to filter untrusted networks. For example, if a data center router is used to segment sensitive PCI networks from internal inventory networks, a retailer may use router access lists to protect its scope. As soon as the store connects to untrusted networks directly, items 3 and 4 below become relevant.
3. ![]() As a stateful firewall, restricting traffic between the cardholder data environment and other areas of the network
As a stateful firewall, restricting traffic between the cardholder data environment and other areas of the network
As soon as any untrusted network is introduced to the connections of the data center router, firewalling and IDS/IPS must be deployed. The following are examples of untrusted networks:
–![]() Internet
Internet
–![]() Wireless
Wireless
–![]() Satellite
Satellite
–![]() Cellular backup
Cellular backup
4. ![]() As an intrusion prevention system, inspecting all traffic going to and from the cardholder data environment
As an intrusion prevention system, inspecting all traffic going to and from the cardholder data environment
As soon as any untrusted network is introduced to the connections of the data center router, firewalling and IDS/IPS must be deployed at that location.
Models Assessed |
|
CISCO7206VXR-NPE-G1 version c7200-advipservicesk9-mz.124-24.T4.bin, |
|
|
|
|
PCI 1 |
|
PCI 2 |
|
PCI 4 |
4.1 |
PCI 6 |
|
PCI 7 |
|
PCI 8 |
8.1, 8.2, 8.4, 8.5.5, 8.5.9, 8.5.10, 8.5.11, 8.5.12, 8.5.13, 8.5.14, 8.5.15 |
PCI 10 |
10.1, 10.2, 10.2.1, 10.2.2, 10.2.3, 10.2.4, 10.2.5, 10.2.6, 10.2.7, 10.3, 10.3.1, 10.3.2, 10.3.3, 10.3.4, 10.3.5, 10.3.6, 10.4.1, 10.4.2, 10.4.3, 10.5.1, 10.5.2, 10.5.3 |
|
|
|
No compensating controls were required to satisfy any sub-requirements. |
|
|
|
|
No sub-requirements were failed. |
|
Primary PCI Function
The data center routers protect trusted networks from untrusted networks with ACLs or firewall/IDS/IOS. (1.2, 1.3, 11.4)
Table 4-34 lists the component assessment details for the Cisco data center routers.
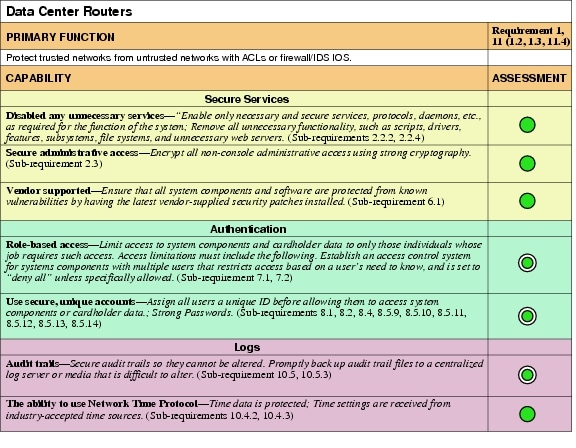
Design Considerations
•![]() Configuration was done manually on the router CLI, and backup of configuration and monitoring of configuration for changes and non-compliance were done through the EMC Ionix Network Configuration Manager (alternatively, CiscoWorks Resource Manager Essentials, a component of Cisco LMS, can be used as well).
Configuration was done manually on the router CLI, and backup of configuration and monitoring of configuration for changes and non-compliance were done through the EMC Ionix Network Configuration Manager (alternatively, CiscoWorks Resource Manager Essentials, a component of Cisco LMS, can be used as well).
•![]() The perimeter firewalling of the data center was provided by the Cisco ASA. As a result, the Cisco 7206VXR and the Cisco ASR1002 were not evaluated according to the set of 1.x requirements for firewalls.
The perimeter firewalling of the data center was provided by the Cisco ASA. As a result, the Cisco 7206VXR and the Cisco ASR1002 were not evaluated according to the set of 1.x requirements for firewalls.
•![]() Disable the HTTP server service on the router and enable the HTTP secure server.
Disable the HTTP server service on the router and enable the HTTP secure server.
•![]() Configure the session-timeout and exec-timeout commands to 15 minutes or less on the console, VTY, and line interfaces on the router. Disable the AUX interface.
Configure the session-timeout and exec-timeout commands to 15 minutes or less on the console, VTY, and line interfaces on the router. Disable the AUX interface.
•![]() Configure appropriate banner messages on login, incoming, and exec modes of the router. The login banner warning should not reveal the identity of the company that owns or manages the router. The incoming and executive banners should state that these areas are considered private and that unauthorized access will result in prosecution to the full extent of the law.
Configure appropriate banner messages on login, incoming, and exec modes of the router. The login banner warning should not reveal the identity of the company that owns or manages the router. The incoming and executive banners should state that these areas are considered private and that unauthorized access will result in prosecution to the full extent of the law.
•![]() Configure the primary login authentication of the router to be directed to the Cisco Secure ACS. Individual user account profiles need to be created. Configure secondary or tertiary authentication local to the router itself in the event of a WAN or Cisco Secure ACS failure.
Configure the primary login authentication of the router to be directed to the Cisco Secure ACS. Individual user account profiles need to be created. Configure secondary or tertiary authentication local to the router itself in the event of a WAN or Cisco Secure ACS failure.
•![]() Use the no service password-recovery command in conjunction with the service password encryption command to prevent password theft by physical compromise of the router.
Use the no service password-recovery command in conjunction with the service password encryption command to prevent password theft by physical compromise of the router.
•![]() Enable anti-spoofing on all interfaces.
Enable anti-spoofing on all interfaces.
•![]() Routers in the data center were implemented using guidance from the following:
Routers in the data center were implemented using guidance from the following:
–![]() Enterprise Data Center Design guide based on a Data Center 3.0 Architecture— http://www.cisco.com/en/US/netsol/ns743/networking_solutions_program_home.html
Enterprise Data Center Design guide based on a Data Center 3.0 Architecture— http://www.cisco.com/en/US/netsol/ns743/networking_solutions_program_home.html
–![]() Enterprise Internet Edge Design Guide— http://www.cisco.com/en/US/docs/solutions/Enterprise/Security/IE_DG.html
Enterprise Internet Edge Design Guide— http://www.cisco.com/en/US/docs/solutions/Enterprise/Security/IE_DG.html
•![]() For the Internet edge routers, use the access list below on the interface that is facing the Internet. This access list explicitly filters traffic destined for the infrastructure address space. Deployment of edge infrastructure access lists requires that you clearly define your infrastructure space and the required/authorized protocols that access this space. The access list is applied at the ingress to your network on all externally facing connections, such as peering connections, customer connections, and so forth.
For the Internet edge routers, use the access list below on the interface that is facing the Internet. This access list explicitly filters traffic destined for the infrastructure address space. Deployment of edge infrastructure access lists requires that you clearly define your infrastructure space and the required/authorized protocols that access this space. The access list is applied at the ingress to your network on all externally facing connections, such as peering connections, customer connections, and so forth.
!
ip access-list extended COARSE-FILTER-INTERNET-IN
remark --------------------------------------
remark ---Block Private Networks---
deny ip 10.0.0.0 0.255.255.255 any log
deny ip 172.16.0.0 0.15.255.255 any log
deny ip 192.168.0.0 0.0.255.255 any log
remark -
remark ---Block Autoconfiguration Networks---
deny ip 169.254.0.0 0.0.255.255 any log
remark -
remark ---Block Loopback Networks---
deny ip 127.0.0.0 0.0.255.255 any log
remark -
remark ---Block Multicast Networks---
deny ip 224.0.0.0 15.255.255.255 any log
remark -
remark ---Block Your assigned IP's at edge---
deny ip <YOUR_CIDR_BLOCK> any log
remark -
remark ---Allow remaining public internet traffic---
permit ip any any
!

Note ![]() The log keyword can be used to provide additional details about source and destinations for a given protocol. Although this keyword provides valuable insight into the details of access list hits, excessive hits to an access list entry that uses the log keyword increase CPU utilization. The performance impact associated with logging varies by platform.
The log keyword can be used to provide additional details about source and destinations for a given protocol. Although this keyword provides valuable insight into the details of access list hits, excessive hits to an access list entry that uses the log keyword increase CPU utilization. The performance impact associated with logging varies by platform.
The service provider network in the solution represented an Multiprotocol Label Switching (MPLS) network. At the writing of this document, MPLS is considered a private network, and secure tunneling across the WAN is not required. MPLS implementations may be public or private with regards to PCI, depending on how the service provider implements the MPLS network and whether the provider has satisfactorily completed their annual PCI audit. For best practices when in doubt, Cisco recommends VPN tunneling be implemented. For further information on implementing an IPSec VPN, see the IPSec VPN Direct Encapsulation Design Guide at the following URL: http://www.cisco.com/en/US/docs/solutions/Enterprise/WAN_and_MAN/Dir_Encap.html
Switching
Switches—Store
Cisco store switches provide connectivity for wired endpoints and the ability to segment them onto their own sensitive scope networks. Virtual local area networks (VLANs) are used to put sensitive PCI applications and devices onto their own network and segregate them from devices that are on non-sensitive networks.
Store switches are broken into three categories to provide scale and feature relevance;
•![]() Compact switches—Quiet, small form factor switches that can be used on store floors to extend the capability of the network to the register. These switches use power over Ethernet (PoE) pass-through, reducing expensive power and network cabling costs to new devices at the area of sale.
Compact switches—Quiet, small form factor switches that can be used on store floors to extend the capability of the network to the register. These switches use power over Ethernet (PoE) pass-through, reducing expensive power and network cabling costs to new devices at the area of sale.
•![]() Access switches—Stackable, expandable switches that can be used for wired device port density in the store wiring closets. Access switches offer a variety of modular and fixed configuration options, and feature operational efficiency with StackPower, FlexStack, and NetFlow to increase visibility and control.
Access switches—Stackable, expandable switches that can be used for wired device port density in the store wiring closets. Access switches offer a variety of modular and fixed configuration options, and feature operational efficiency with StackPower, FlexStack, and NetFlow to increase visibility and control.
•![]() Core/distribution—Highly redundant, powerful core switches allow for the most demanding business requirements of the store. Modular functionality provides the ability to insert security technology as the needs of the business expand into new areas.
Core/distribution—Highly redundant, powerful core switches allow for the most demanding business requirements of the store. Modular functionality provides the ability to insert security technology as the needs of the business expand into new areas.
|
|
|
WS-C3560E-PS-24 c3560e-universalk9-mz.122-35.SE5.bin |
|
PCI Sub-Requirements Passed |
|
PCI 2 |
|
PCI 6 |
|
PCI 7 |
|
PCI 8 |
8.1, 8.2, 8.4, 8.5.5, 8.5.9, 8.5.10, 8.5.11, 8.5.12, 8.5.13, 8.5.14, 8.5.15 |
PCI 10 |
10.1, 10.2, 10.2.1, 10.2.2, 10.2.3, 10.2.4, 10.2.5, 10.2.6, 10.2.7, 10.3, 10.3.1, 10.3.2, 10.3.3, 10.3.4, 10.3.5, 10.3.6, 10.4.1, 10.4.2, 10.4.3, 10.5.1, 10.5.2, 10.5.3 |
PCI 11 |
|
|
|
|
No compensating controls were required to satisfy any sub-requirements. |
|
|
|
|
No sub-requirements were failed. |
|
Primary PCI Function
The primary PCI compliance feature of store switches is to provide secure wired port access. (9.1.2, 11.1)
Store switches also provide PCI compliance via segmentation of sensitive networks from out-of-scope networks. Although technically a firewall or ACL is used to enforce PCI Requirement 1, switches extend that Layer 3 boundary to Layer 2. Using VLANs, Cisco store switches allow retailers to put their payment networks into separate VLANs (scopes) from other non-sensitive data (out-of-scope).
Figure 4-12 shows an example of switch segmentation.
Figure 4-12 Cisco Store Switch Segmentation
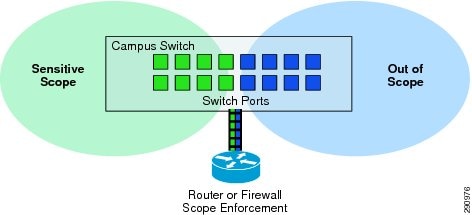
Although the enforcement of these boundaries would be handled by either a router or firewall, the switch provides the port density and access required to connect the payment devices from the store floor.
Table 4-36 lists the component assessment details for the Cisco store switches.
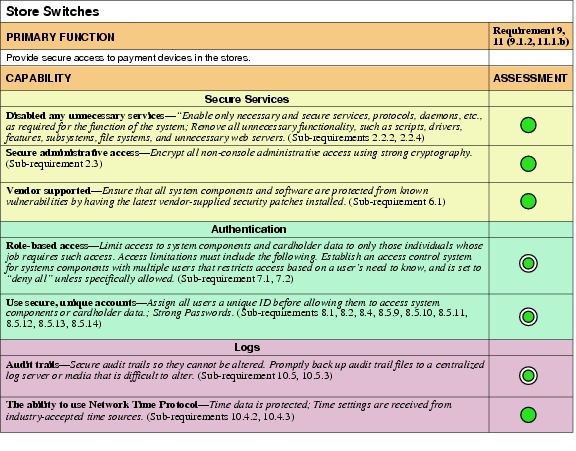
Design Considerations
•![]() The configurations of the Cisco Catalyst switches in the store architectures are maintained within EMC Ionix Network Configuration Manager (alternatively CiscoWorks Resource Manager Essentials, a component of C-LMS, can be used as well).
The configurations of the Cisco Catalyst switches in the store architectures are maintained within EMC Ionix Network Configuration Manager (alternatively CiscoWorks Resource Manager Essentials, a component of C-LMS, can be used as well).
•![]() The use of VLANs on the Cisco Catalyst switch enables the retailer to provide same-box wired access to its devices while maintaining segregated addressing schemes.
The use of VLANs on the Cisco Catalyst switch enables the retailer to provide same-box wired access to its devices while maintaining segregated addressing schemes.
•![]() Disable the HTTP server on the switch and enable the HTTP secure server.
Disable the HTTP server on the switch and enable the HTTP secure server.
•![]() Using the stacking capability of Cisco Catalyst switches improves high availability designs while simplifying configuration and support.
Using the stacking capability of Cisco Catalyst switches improves high availability designs while simplifying configuration and support.
•![]() Cisco SmartPorts simplifies connecting the right device to the right VLAN.
Cisco SmartPorts simplifies connecting the right device to the right VLAN.
•![]() Network Admission Control (NAC) protects the network from rogue devices being connected.
Network Admission Control (NAC) protects the network from rogue devices being connected.
•![]() Cisco compact switches can easily add more securely managed ports where needed (for example, Cash Wrap and customer service desk), and some models can use PoE.
Cisco compact switches can easily add more securely managed ports where needed (for example, Cash Wrap and customer service desk), and some models can use PoE.
•![]() Set the session and exec timeout commands to 15 minutes or less.
Set the session and exec timeout commands to 15 minutes or less.
•![]() Configure appropriate banner messages on login, incoming, and exec modes of the switch. The login banner warning should not reveal the identity of the company that owns or manages the switch. The incoming and executive banners should state that these areas are considered private and that unauthorized access will result in prosecution to the full extent of the law.
Configure appropriate banner messages on login, incoming, and exec modes of the switch. The login banner warning should not reveal the identity of the company that owns or manages the switch. The incoming and executive banners should state that these areas are considered private and that unauthorized access will result in prosecution to the full extent of the law.
•![]() Configure the primary login authentication of the switch to be directed to the Cisco Secure ACS. Individual user account profiles need to be created. Configure secondary or tertiary authentication local to the switch itself in the event of a WAN or Cisco Secure ACS failure.
Configure the primary login authentication of the switch to be directed to the Cisco Secure ACS. Individual user account profiles need to be created. Configure secondary or tertiary authentication local to the switch itself in the event of a WAN or Cisco Secure ACS failure.
•![]() Use the no service password-recovery command in conjunction with the service password encryption command to prevent password theft by physical compromise of the switch.
Use the no service password-recovery command in conjunction with the service password encryption command to prevent password theft by physical compromise of the switch.
Cisco Catalyst Switches—Data Center
The Cisco Catalyst family of data center switches securely switches data; from servers to high speed trunks, maintaining the integrity of segmented scopes of compliance. They provide scalable inter-switch connectivity, high port density for wired endpoints, and the ability to segment them into sensitive scope networks. VLANs are used to put sensitive PCI applications and devices onto their own network and segregate them from devices that are on non-sensitive networks. Data center Cisco Catalyst switches are highly redundant, capable of delivering high performance switching, with feature options depending on the needs of the business.
Modular functionality provides the ability to insert security technology to enforce compliance needs.
•![]() Security services include access control, firewall, and intrusion prevention.
Security services include access control, firewall, and intrusion prevention.
•![]() Wireless services can be aggregated into these switches for central policy control of unified wireless access points.
Wireless services can be aggregated into these switches for central policy control of unified wireless access points.
•![]() Application services include quality of service (QoS), content filtering, and load balancing.
Application services include quality of service (QoS), content filtering, and load balancing.
|
|
|
Catalyst6509-Sup720-3BXL version s72033-adventerprisek9_wan-mz.122-33.SXJ.bin |
|
PCI Sub-Requirements Passed |
|
PCI 1 |
|
PCI 2 |
|
PCI 6 |
|
PCI 7 |
|
PCI 8 |
8.1, 8.2, 8.4, 8.5.5, 8.5.9, 8.5.10, 8.5.11, 8.5.12, 8.5.13, 8.5.14, 8.5.15 |
PCI 9 |
|
PCI 10 |
10.1, 10.2, 10.2.1, 10.2.2, 10.2.3, 10.2.4, 10.2.5, 10.2.6, 10.2.7, 10.3, 10.3.1, 10.3.2, 10.3.3, 10.3.4, 10.3.5, 10.3.6, 10.4.1, 10.4.2, 10.4.3, 10.5.1, 10.5.2, 10.5.3 |
|
|
|
No compensating controls were required to satisfy any sub-requirements. |
|
|
|
|
No sub-requirements were failed. |
|
Primary PCI Function
The primary PCI compliance feature of Cisco Catalyst data center switches is securing the infrastructure. Cisco Catalyst switches have firewall/IDS modules for perimeter security. (See Figure 4-13.)
Figure 4-13 Cisco Catalyst Data Center Switches
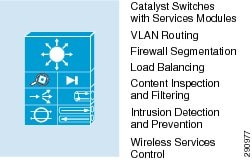
The main function of the Cisco Catalyst data center switches is segmentation of PCI scope and enforcement of that new scope boundary. These switches have five primary functions/capabilities in relation to PCI:
•![]() Using VLANs, Cisco Catalyst switches allow a retailer to put its payment networks into separate VLANs (scopes) from other non-sensitive data (out of scope).
Using VLANs, Cisco Catalyst switches allow a retailer to put its payment networks into separate VLANs (scopes) from other non-sensitive data (out of scope).
•![]() The Layer 3 Cisco Catalyst switch acts as a router, directing traffic between networks. By segmenting a network into sub-networks, a retailer can isolate sensitive information from non-sensitive information. The Cisco Catalyst switch can perform the ability to segment and route sensitive traffic from non-sensitive and reduce the overall scope of a company's cardholder data environment. Depending on risk vectors, different levels of enforcement are required at the segmented scope boundary level. See the following bullets for details.
The Layer 3 Cisco Catalyst switch acts as a router, directing traffic between networks. By segmenting a network into sub-networks, a retailer can isolate sensitive information from non-sensitive information. The Cisco Catalyst switch can perform the ability to segment and route sensitive traffic from non-sensitive and reduce the overall scope of a company's cardholder data environment. Depending on risk vectors, different levels of enforcement are required at the segmented scope boundary level. See the following bullets for details.
•![]() The Layer 3 Cisco Catalyst switch acts as a router with ACLs, restricting traffic between the cardholder data environment and other areas of the network. A Cisco Catalyst switch with ACLs can be used to enforce segmented traffic if the ACLs are used only to filter and segment private networks of the retailer. ACLs may not be used to segment untrusted networks.
The Layer 3 Cisco Catalyst switch acts as a router with ACLs, restricting traffic between the cardholder data environment and other areas of the network. A Cisco Catalyst switch with ACLs can be used to enforce segmented traffic if the ACLs are used only to filter and segment private networks of the retailer. ACLs may not be used to segment untrusted networks.
•![]() The Cisco Catalyst switch with a firewall service module restricts traffic between the cardholder data environment and other areas of the network. As soon as any untrusted network is introduced, firewalling and IDS/IPS must be deployed.
The Cisco Catalyst switch with a firewall service module restricts traffic between the cardholder data environment and other areas of the network. As soon as any untrusted network is introduced, firewalling and IDS/IPS must be deployed.
•![]() The Layer 3 Cisco Catalyst switch with an intrusion prevention module inspects all traffic going to and from the cardholder data environment. As soon as any untrusted network is introduced, firewalling and IDS/IPS must be deployed.
The Layer 3 Cisco Catalyst switch with an intrusion prevention module inspects all traffic going to and from the cardholder data environment. As soon as any untrusted network is introduced, firewalling and IDS/IPS must be deployed.
Table 4-38 lists the component assessment details for the Cisco Catalyst data center switches.
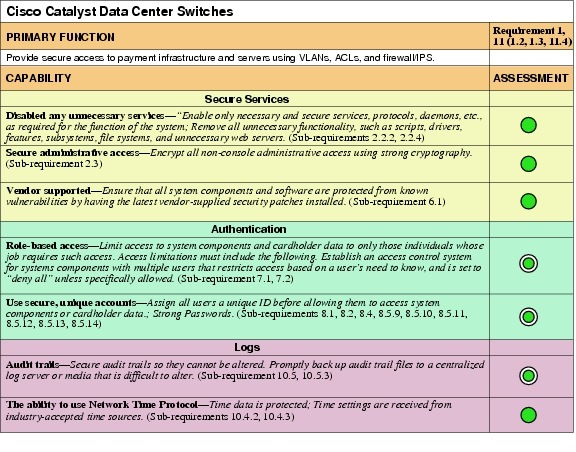
Design Considerations
•![]() The configurations of the Cisco Catalyst switches in the data center and Internet edge architectures are maintained within EMC Ionix Network Configuration Manager (alternatively CiscoWorks Resource Manager Essentials, a component of C-LMS, can be used as well).
The configurations of the Cisco Catalyst switches in the data center and Internet edge architectures are maintained within EMC Ionix Network Configuration Manager (alternatively CiscoWorks Resource Manager Essentials, a component of C-LMS, can be used as well).
•![]() The use of VLANs on the Cisco Catalyst switch enables the retailer to provide same-box wired access to its devices while maintaining segregated addressing schemes.
The use of VLANs on the Cisco Catalyst switch enables the retailer to provide same-box wired access to its devices while maintaining segregated addressing schemes.
•![]() Using the stacking capability of Cisco Catalyst switches improves high availability designs while simplifying configuration and support.
Using the stacking capability of Cisco Catalyst switches improves high availability designs while simplifying configuration and support.
•![]() Disable the HTTP server on the switch and enable the HTTP secure server.
Disable the HTTP server on the switch and enable the HTTP secure server.
•![]() Set the session and exec timeout commands to 15 minutes or less.
Set the session and exec timeout commands to 15 minutes or less.
•![]() Configure appropriate banner messages on login, incoming, and exec modes of the switch. The login banner warning should not reveal the identity of the company that owns or manages the switch. The incoming and executive banners should state that these areas are considered private and that unauthorized access will result in prosecution to the full extent of the law.
Configure appropriate banner messages on login, incoming, and exec modes of the switch. The login banner warning should not reveal the identity of the company that owns or manages the switch. The incoming and executive banners should state that these areas are considered private and that unauthorized access will result in prosecution to the full extent of the law.
•![]() Configure the primary login authentication of the switch to be directed to the Cisco Secure ACS. Individual user account profiles need to be created. Configure secondary or tertiary authentication local to the switch itself in the event of a WAN or Cisco Secure ACS failure.
Configure the primary login authentication of the switch to be directed to the Cisco Secure ACS. Individual user account profiles need to be created. Configure secondary or tertiary authentication local to the switch itself in the event of a WAN or Cisco Secure ACS failure.
•![]() Use the no service password-recovery command in conjunction with the service password encryption command to prevent password theft by physical compromise of the switch.
Use the no service password-recovery command in conjunction with the service password encryption command to prevent password theft by physical compromise of the switch.
Cisco Nexus 1000V Switch—Data Center
The Cisco Nexus 1000V Series Switch provides connectivity for virtual servers with the ability to segment them onto their own sensitive scope networks. VLANs are used to put sensitive PCI applications and devices onto their own network and segregate them from devices that are on non-sensitive networks.
The Cisco Nexus 1000V Series Switch provides advanced networking functions and a common network management model in a virtualized server environment. The Cisco Nexus 1000V Series Switch replaces the virtual switching functionality of the VMware vCenter data center container of servers. Each server in the data center container is represented as a line card in the Cisco Nexus 1000V Series Virtual Supervisor Module (VSM) and is managed as if it were a line card in a physical Cisco switch.
Key benefits of the Nexus 1000V include the following:
•![]() Policy-based virtual machine (VM) connectivity
Policy-based virtual machine (VM) connectivity
•![]() Mobile VM security and network policy
Mobile VM security and network policy
•![]() Non-disruptive operational model for your server virtualization, and networking teams
Non-disruptive operational model for your server virtualization, and networking teams
|
|
|
Cisco Nexus 1000V version 4.2(1)SV1(4) |
|
PCI Sub-Requirements Passed |
|
PCI 2 |
|
PCI 6 |
|
PCI 7 |
|
PCI 8 |
8.1, 8.2, 8.4, 8.5.5, 8.5.9, 8.5.10. 8.5.11, 8.5.12, 8.5.13, 8.5.14, 8.5.15 |
PCI 10 |
10.1, 10.2, 10.2.1, 10.2.2, 10.2.3, 10.2.4, 10.2.5, 10.2.6, 10.2.7, 10.3, 10.3.1, 10.3.2, 10.3.3, 10.3.4, 10.3.5, 10.3.6, 10.4.1, 10.4.2, 10.4.3, 10.5.1, 10.5.2, 10.5.3 |
|
|
|
No compensating controls were required to satisfy any sub-requirements. |
|
|
|
|
No sub-requirements were failed. |
|
Primary PCI Function
The primary PCI compliance feature of Cisco Nexus switches is secure aggregation and access layer connectivity.
•![]() Using VLANs, Cisco Nexus switches allow a retailer to put its payment network into separate VLANs (scopes) from other non-sensitive data (out of scope).
Using VLANs, Cisco Nexus switches allow a retailer to put its payment network into separate VLANs (scopes) from other non-sensitive data (out of scope).
•![]() The Layer 3 Cisco Nexus switch acts as a router, directing traffic between networks. By segmenting a network into sub-networks, a retailer can isolate sensitive information from non-sensitive information. The Cisco Nexus switch can segment and route sensitive traffic separately from non-sensitive traffic to reduce the overall scope of a company's cardholder data environment. Depending on risk vectors, various levels of enforcement are required at the segmented scope boundary level.
The Layer 3 Cisco Nexus switch acts as a router, directing traffic between networks. By segmenting a network into sub-networks, a retailer can isolate sensitive information from non-sensitive information. The Cisco Nexus switch can segment and route sensitive traffic separately from non-sensitive traffic to reduce the overall scope of a company's cardholder data environment. Depending on risk vectors, various levels of enforcement are required at the segmented scope boundary level.
•![]() The Layer 3 Cisco Nexus switch acts as a router with ACLs, restricting traffic between the cardholder data environment and other areas of the network. A Cisco Nexus switch with ACLs can be used to enforce segmented traffic if the ACLs are used only to filter and segment private networks of the retailer. ACLs may not be used to segment untrusted networks.
The Layer 3 Cisco Nexus switch acts as a router with ACLs, restricting traffic between the cardholder data environment and other areas of the network. A Cisco Nexus switch with ACLs can be used to enforce segmented traffic if the ACLs are used only to filter and segment private networks of the retailer. ACLs may not be used to segment untrusted networks.
•![]() The Cisco Nexus switch uses virtualization contexts, which are essentially virtualized switches. Each virtualized context has its own configuration and management interfaces that can be used to segregate not only data but administration as well.
The Cisco Nexus switch uses virtualization contexts, which are essentially virtualized switches. Each virtualized context has its own configuration and management interfaces that can be used to segregate not only data but administration as well.
Table 4-40 lists the component assessment details for the Cisco Nexus 1000V Series Switch.
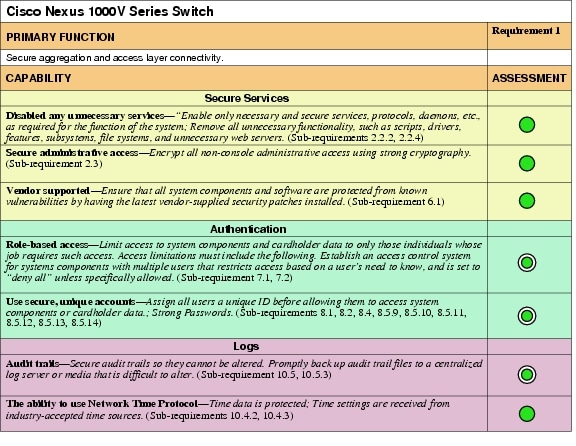
Design Considerations
The Cisco Nexus 1000V Series Switch includes the Cisco Integrated Security features that are found on Cisco physical switches to prevent a variety of attack scenarios. For example, a rogue virtual machine can spoof its MAC and IP addresses so that it appears to be an existing production virtual machine, send a rogue Address Resolution Protocol (ARP) transaction mimicking the way that VMware vMotion announces the location of a migrated virtual machine, and divert traffic from the production virtual machine to the rogue virtual machine. With Cisco Integrated Security features, this type of attack can easily be prevented with simple networking policy. Because server virtualization is being used for desktop and server workloads, it is critical that this type of security feature be deployed for the proper operation of a virtualized environment.
The Cisco Nexus 1000V Series implementation has two main components:
•![]() Virtual Supervisor Module (VSM)
Virtual Supervisor Module (VSM)
•![]() Virtual Ethernet module (VEM)
Virtual Ethernet module (VEM)
The Cisco Nexus 1000V VSM is installed as an appliance server on either a standalone Cisco UCS server (Cisco Nexus 1010) or as a virtual appliance on VMware ESXi server running on a blade of the Cisco UCS system.
Cisco Nexus Switches—Data Center
The Cisco Nexus family of data center switches securely switches data; from payment application servers to high speed trunks of the core, maintaining the integrity of segmented scopes of compliance. They provide scalable inter-switch connectivity and high port density for wired endpoints. VLANs are used to put sensitive PCI applications and devices onto their own network and segregate them from devices on non-sensitive networks.
Cisco Nexus switches are ideal for enterprise-class server and aggregation layer deployments. These multipurpose, multilayer switches can be deployed across a diverse set of traditional, virtualized, unified, and high-performance computing environments. They enable diverse transports over Ethernet (including Layer 2, Layer 3, and storage traffic) on one common platform. Nexus switches help transform your data center, with a standards-based, multipurpose, multiprotocol, Ethernet-based fabric.
Primary PCI Function
The primary PCI compliance feature of Cisco Nexus data center switches is secure aggregation and access layer connectivity.
•![]() Using VLANs, Cisco Nexus switches allow a retailer to put its payment network into separate VLANs (scopes) from other non-sensitive data (out of scope).
Using VLANs, Cisco Nexus switches allow a retailer to put its payment network into separate VLANs (scopes) from other non-sensitive data (out of scope).
•![]() The Layer 3 Cisco Nexus switch acts as a router, directing traffic between networks. By segmenting a network into sub-networks, a retailer can isolate sensitive information from non-sensitive information. The Cisco Nexus switch can segment and route sensitive traffic separately from non-sensitive traffic to reduce the overall scope of a company's cardholder data environment. Depending on risk vectors, various levels of enforcement are required at the segmented scope boundary level.
The Layer 3 Cisco Nexus switch acts as a router, directing traffic between networks. By segmenting a network into sub-networks, a retailer can isolate sensitive information from non-sensitive information. The Cisco Nexus switch can segment and route sensitive traffic separately from non-sensitive traffic to reduce the overall scope of a company's cardholder data environment. Depending on risk vectors, various levels of enforcement are required at the segmented scope boundary level.
•![]() The Layer 3 Cisco Nexus switch acts as a router with ACLs, restricting traffic between the cardholder data environment and other areas of the network. A Cisco Nexus switch with ACLs can be used to enforce segmented traffic if the ACLs are used only to filter and segment private networks of the retailer. ACLs may not be used to segment untrusted networks.
The Layer 3 Cisco Nexus switch acts as a router with ACLs, restricting traffic between the cardholder data environment and other areas of the network. A Cisco Nexus switch with ACLs can be used to enforce segmented traffic if the ACLs are used only to filter and segment private networks of the retailer. ACLs may not be used to segment untrusted networks.
•![]() The Cisco Nexus switch uses virtualization contexts, which are essentially virtualized switches. Each virtualized context has its own configuration and management interfaces that can be used to segregate not only data but administration as well.
The Cisco Nexus switch uses virtualization contexts, which are essentially virtualized switches. Each virtualized context has its own configuration and management interfaces that can be used to segregate not only data but administration as well.
Table 4-42 lists the component assessment details for the Cisco Nexus data center switches.
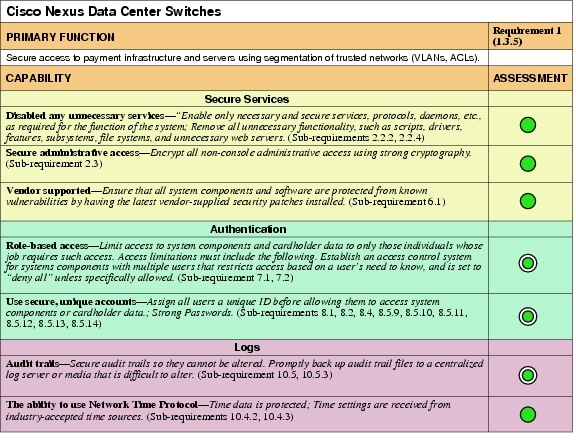
Design Considerations
•![]() Configuration was done manually on the router CLI, and backup of configuration and monitoring of configuration for changes and non-compliance were done through the EMC Ionix Network Configuration Manager (alternatively CiscoWorks Resource Manager Essentials, a component of C-LMS, can be used as well).
Configuration was done manually on the router CLI, and backup of configuration and monitoring of configuration for changes and non-compliance were done through the EMC Ionix Network Configuration Manager (alternatively CiscoWorks Resource Manager Essentials, a component of C-LMS, can be used as well).
•![]() Configure appropriate banner messages on login, incoming, and EXEC modes of the router. The login banner warning should not reveal the identity of the company that owns or manages the router. The incoming and executive banners should state that these areas are considered private and that unauthorized access will result in prosecution to the full extent of the law.
Configure appropriate banner messages on login, incoming, and EXEC modes of the router. The login banner warning should not reveal the identity of the company that owns or manages the router. The incoming and executive banners should state that these areas are considered private and that unauthorized access will result in prosecution to the full extent of the law.
•![]() Configure the primary login authentication of the router to be directed to the Cisco Secure ACS. Individual user account profiles need to be created. Configure secondary or tertiary authentication local to the router itself in the event of a WAN or Cisco Secure ACS failure.
Configure the primary login authentication of the router to be directed to the Cisco Secure ACS. Individual user account profiles need to be created. Configure secondary or tertiary authentication local to the router itself in the event of a WAN or Cisco Secure ACS failure.
•![]() Nexus switches in the data center were implemented using guidance from the Enterprise Data Center Design guide based on a Data Center 3.0 Architecture: http://www.cisco.com/en/US/netsol/ns743/networking_solutions_program_home.html
Nexus switches in the data center were implemented using guidance from the Enterprise Data Center Design guide based on a Data Center 3.0 Architecture: http://www.cisco.com/en/US/netsol/ns743/networking_solutions_program_home.html
Enterprise Internet Edge Design Guide: http://www.cisco.com/en/US/docs/solutions/Enterprise/Security/IE_DG.html
•![]() The Cisco Nexus 7010 and the Cisco Nexus 5000 were used for the aggregation block portions of the lab validation network.
The Cisco Nexus 7010 and the Cisco Nexus 5000 were used for the aggregation block portions of the lab validation network.
Cisco Wireless
Cisco Wireless technologies provide connectivity for mobile clients within the store. They can secure connectivity for traditional business functions such as guest access or inventory control, without increasing risk. Innovative customer experience services such as mobile point-of-sale are equally secure. In addition to expanding business functionality, Cisco wireless technology seamlessly provides the capability to detect rogues.
Industry-leading performance is available with Cisco Aironet access points for highly secure and reliable wireless connections for both indoor and outdoor environments. Cisco offers a broad portfolio of access points targeted to specific business needs and topologies.
Cisco wireless controllers help reduce the overall operational expenses of Cisco Unified Wireless Networks by simplifying network deployment, operations, and management. They extend the Cisco Borderless Network policy and security from the wired network to the wireless edge.
Cisco Wireless Control System (WCS) delivers full visibility and control of Cisco Aironet access points, Cisco Wireless LAN Controllers (WLC) and the Cisco Mobility Services Engine (MSE) with built-in support for Cisco adaptive wireless intrusion prevention systems (wIPS) and Cisco context-aware services. This robust platform helps you reduce total cost of ownership and maintain a business-ready wireless network.
Primary PCI Function
The primary PCI function of Cisco Unified Wireless is secure connectivity of wireless clients (4.1) and rogue detection (1.1).
Table 4-44 lists the component assessment details for Cisco wireless products.
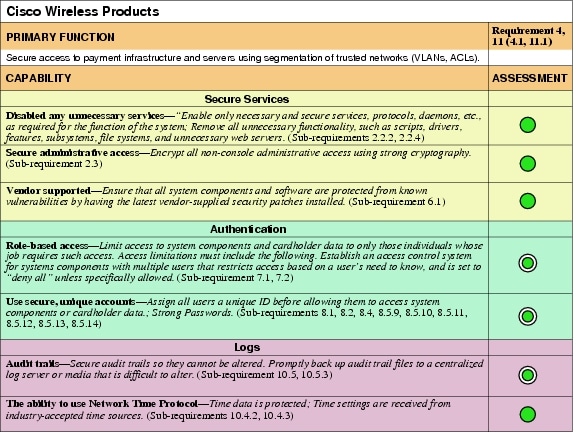
Design Considerations
Rogue detection for wireless technology in the store is required at a minimum of once a quarter, whether or not the retailer has wireless deployed. A hacker might infiltrate a store and install a rogue wireless device (for example, access point, wireless-enabled printer, or radio-enabled USB stick). This would allow a hacker remote access into the store (from the parking lot, for example) that is hard to detect. The PCI DSS offers several methods for detecting rogue devices. Cisco Unified Wireless offers the benefit of continuous rogue detection while simultaneously passing normal wireless traffic.
The PCI-DSS states that wireless technology is an untrusted network connection. Wireless technology in the store requires firewall and intrusion detection services to segment and protect the cardholder data environment. Stateful firewalls must be configured to limit traffic to and from the wireless environment (all enabled services, protocols, and ports must have documented justification for business purposes). All other access must be denied.
When including point-of-sale clients in the wireless network, strong wireless encryption technology needs to be implemented.

Wireless compliance is broken into the stages listed in Table 4-46.
Cisco recommends using the Unified Wireless (controller-based) architecture for retail wireless deployments because of the Cisco ongoing wireless strategy. The autonomous Cisco IOS access points are not being enhanced. Future security and user enhancements will be developed on the controller-based architecture.
For WCS servers running software versions prior to 4.1, Cisco recommends a combination of documented password policies, manual audit procedures, and firewall segmentation for WCS servers within the data center.
•![]() Configure unique SSIDs
Configure unique SSIDs
•![]() Disable broadcast of the SSIDs
Disable broadcast of the SSIDs
Storage
Cisco MDS Storage Switches
Cisco MDS storage switches provide the central switching infrastructure connecting servers to storage. They provide the added capability to encrypt all information on the fly between these systems for specified targets; specifically, the EMC storage array and Cisco UCS servers in the solution.
The Cisco MDS 9000 Series Multilayer SAN Switches can help lower the total cost of ownership of the most demanding storage environments. By combining robust and flexible hardware architecture with multiple layers of network and storage management intelligence, the Cisco MDS 9000 Series helps you build highly available, scalable storage networks with advanced security and unified management.
Primary PCI Function
The main function of Cisco MDS storage switches is to securely encrypt cardholder data at rest as it passes from server to storage. (3.4)
Table 4-47 lists the component assessment details for Cisco MDS storage switches.
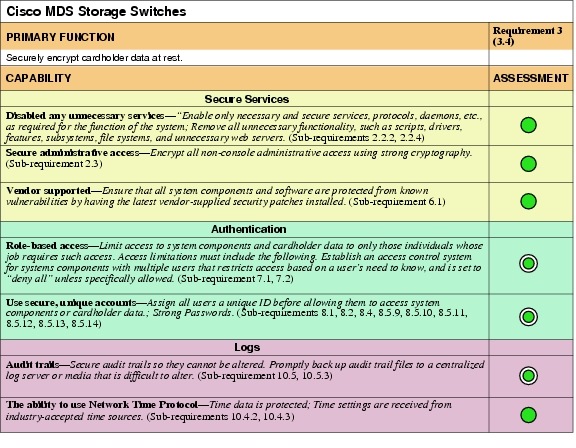
Design Considerations
The MDS 9500s were configured for zoning and LUN masking to secure the logical partitioning of disk used for storing cardholder data. Only host machines in the data center that require access to that logical disk partition were allowed access. Configuration of the VSANs, host UUIDs, and mappings was partially performed using EMC Unified Infrastructure Manager as directed by the Vblock architecture by VCE. Vblock requires specific software versions and pre-configurations to be completed as specified in the Vblock preparation guide.
More information of Vblock designs can be found at the following URL: http://www.vceportal.com/solutions/68580567.html#
Information in installing and configuring Cisco MDS can be found at the following URL: http://www.cisco.com/en/US/products/hw/ps4159/ps4358/tsd_products_support_series_home.html
Security
Cisco ASA 5500 Series—Store
The Cisco ASA 5500 Series Adaptive Security Appliances provide secure segmentation within the store. Their stateful firewall and modular intrusion detection modules enable the store to securely connect public networks to the cardholder data environment.
The Cisco ASA 5500 Series delivers superior scalability, a broad span of technology and solutions, and effective, always-on security designed to meet the needs of a wide array of deployments. By integrating the world's most proven firewall; a comprehensive, highly effective intrusion prevention system (IPS) with Cisco Global Correlation and guaranteed coverage; high-performance VPN and always-on remote access, the Cisco ASA 5500 Series helps organizations provide secure, high performance connectivity and protects critical assets for maximum productivity.
The Cisco ASA 5500 Series includes the Cisco ASA 5505, 5510, 5520, 5540, 5550, 5580, and 5585-X Adaptive Security Appliances-purpose-built, high-performance security solutions that take advantage of Cisco expertise in developing industry-leading, award-winning security and VPN solutions. Through Cisco Multi-Processor Forwarding (MPF), the Cisco ASA 5500 Series brings a new level of security and policy control to applications and networks. MPF enables highly customizable, flow-specific security policies that have been tailored to application requirements. The performance and extensibility of the Cisco ASA 5500 Series is enhanced through user-installable security service modules (SSMs). This adaptable architecture enables businesses to rapidly deploy security services when and where they are needed, such as tailoring inspection techniques to specific application and user needs or adding additional intrusion prevention and content security services such as those delivered by the Adaptive Inspection and Prevention (AIP) and Content Security and Control (CSC) SSMs. Furthermore, the modular hardware architecture of the Cisco ASA 5500 Series, along with the powerful MPF, provides the flexibility to meet future network and security requirements, extending the outstanding investment protection provided by the Cisco ASA 5500 Series and allowing businesses to adapt their network defenses to new threats as they arise.
All Cisco ASA 5500 Series appliances offer both IPsec and SSL/DTLS VPN solutions; clientless and AnyConnect VPN features are licensed at various price points, on a per-seat and per-feature basis. By converging SSL and IPsec VPN services with comprehensive threat defense technologies, the Cisco ASA 5500 Series provides highly customizable, granular network access tailored to meet the requirements of diverse deployment environments, while providing advanced endpoint and network-level security.
Primary PCI Function
The main function of the store Cisco ASA firewall is to securely segment public and cardholder data environment store networks, and provide intrusion detection capabilities. (1.2, 1.3, 11.4)
Table 4-49 lists the component assessment details for the Cisco ASA 5500 Series.
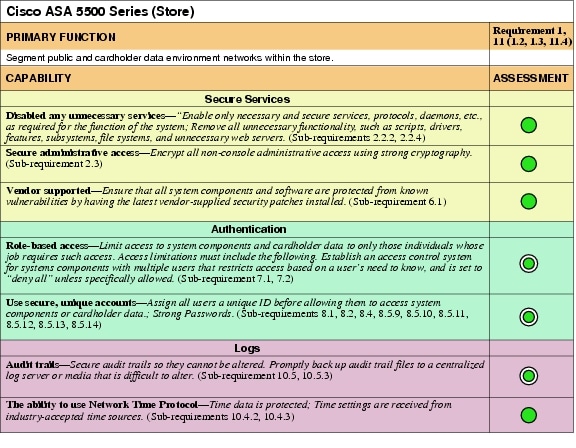
Design Considerations
•![]() Select the appropriate Cisco ASA model and SSM module for the traffic needs in the store.
Select the appropriate Cisco ASA model and SSM module for the traffic needs in the store.
•![]() Connect the SSM module to the secure management segment of the store network using the external Ethernet interface.
Connect the SSM module to the secure management segment of the store network using the external Ethernet interface.
•![]() Configure security policies, objects, and rules centrally with Cisco Security Manager.
Configure security policies, objects, and rules centrally with Cisco Security Manager.
Cisco ASA 5500 Series—Data Center
As a core component of Cisco Borderless Networks, Cisco ASA 5500 Series Adaptive Security Appliances provide:
•![]() Context-aware firewall capabilities
Context-aware firewall capabilities
•![]() Proven firewall services
Proven firewall services
•![]() Comprehensive real-time threat defense
Comprehensive real-time threat defense
•![]() Effective, always-on, highly secure remote access
Effective, always-on, highly secure remote access
•![]() Highly secure communication services
Highly secure communication services
These solutions help reduce deployment and operational costs while delivering comprehensive network security for networks of all sizes.
Context-aware firewalling capabilities combine:
•![]() In-depth local network context from TrustSec
In-depth local network context from TrustSec
•![]() Real-time global threat intelligence from Cisco Security Intelligence Operations (SIO)
Real-time global threat intelligence from Cisco Security Intelligence Operations (SIO)
•![]() Unique mobile client insight from AnyConnect
Unique mobile client insight from AnyConnect
In addition, these solutions offer an advanced intrusion prevention system (IPS) with Global Correlation, which is twice as effective as a traditional IPS and includes Cisco guaranteed coverage.
Primary PCI Function
The primary functions of the data center firewalls are twofold. They operate as a firewall, restricting traffic between the cardholder data environment and other areas of the network; and they operate as an intrusion prevention system, inspecting all traffic going to and from the cardholder data environment. These controls map directly to satisfying a number of PCI sub-requirements including Requirements 1, 2, 4, 7, 8, 10, and 11. The following is a description of how each of the PCI sub-requirements is satisfied for store routers.
Table 4-51 lists the component assessment details for Cisco ASA 5500 Series.
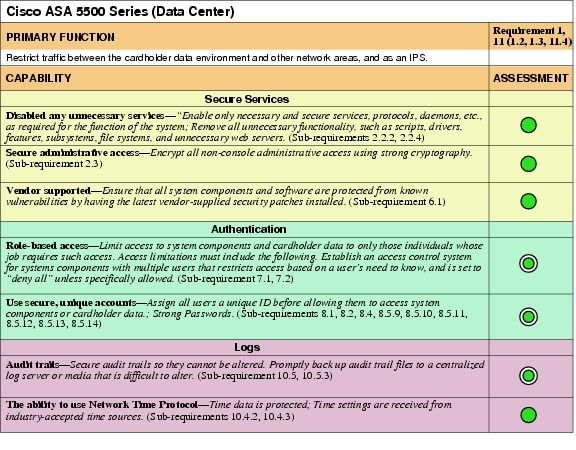
Design Considerations
•![]() Implementing Cisco ASA firewalls in transparent mode helps reduce network complexity.
Implementing Cisco ASA firewalls in transparent mode helps reduce network complexity.
•![]() IDS/IPS modules require the external network interface port to be connected to the network for management and automated reporting and alerts to be sent.
IDS/IPS modules require the external network interface port to be connected to the network for management and automated reporting and alerts to be sent.
•![]() When configuring high availability, only the primary Cisco ASA needs to be fully configured; the secondary Cisco ASA mirrors the primary's configurations once the failover interface and IP information are configured.
When configuring high availability, only the primary Cisco ASA needs to be fully configured; the secondary Cisco ASA mirrors the primary's configurations once the failover interface and IP information are configured.
•![]() Cisco Adaptive Security Device Manager (ADSM) is a good tool for making policy changes in small environments. For large enterprises, Cisco Security Manager provides the best platform for managing rules with a large number of objects across many devices.
Cisco Adaptive Security Device Manager (ADSM) is a good tool for making policy changes in small environments. For large enterprises, Cisco Security Manager provides the best platform for managing rules with a large number of objects across many devices.
•![]() Multi-context firewalls allow for traffic and administrative segmentation.
Multi-context firewalls allow for traffic and administrative segmentation.
•![]() Firewall rule sets must adhere to a "least amount of access necessary" policy. Rules must be defined by specific source/destination addressing and TCP/UDP ports required for the cardholder data environment (for example, point-of-sale) networks.
Firewall rule sets must adhere to a "least amount of access necessary" policy. Rules must be defined by specific source/destination addressing and TCP/UDP ports required for the cardholder data environment (for example, point-of-sale) networks.
•![]() Configure the primary login authentication of the Cisco ASA to be directed to the Cisco Secure ACS. Individual user account profiles need to be created. Configure secondary or tertiary authentication local to the Cisco ASA itself in the event of a WAN or Cisco Secure ACS failure.
Configure the primary login authentication of the Cisco ASA to be directed to the Cisco Secure ACS. Individual user account profiles need to be created. Configure secondary or tertiary authentication local to the Cisco ASA itself in the event of a WAN or Cisco Secure ACS failure.
•![]() Configure logs to be sent to a centralized syslog server such as RSA enVision.
Configure logs to be sent to a centralized syslog server such as RSA enVision.
•![]() Configure NTP to ensure all logging is coordinated
Configure NTP to ensure all logging is coordinated
•![]() Cisco ASA firewalls were used for the store WAN, Internet edge, and data center aggregation block.
Cisco ASA firewalls were used for the store WAN, Internet edge, and data center aggregation block.
Cisco Firewall Services Module (FWSM)—Data Center
The Cisco Firewall Services Module (FWSM) is an integrated module installed inside a Cisco Catalyst 6500 Series Switch or Cisco 7600 Internet Router. The Cisco FWSM allows any port on the Cisco Catalyst switch to operate as a firewall port and integrates firewall security inside the network infrastructure.
The Cisco FWSM includes a number of advanced features that help reduce costs and operational complexity while enabling organizations to manage multiple firewalls from the same management platform. Features such as the resource manager help organizations limit the resources allocated to any security context at any time, thus ensuring that one security context does not interfere with another. The transparent firewall feature configures the Cisco FWSM to act as a Layer 2 bridging firewall, resulting in minimal changes to network topology.
Primary PCI Function
The primary function of the Cisco FWSM is to restrict traffic between the cardholder data environment and other areas of the network (1.2, 1.3).
Table 4-53 lists the component assessment details for the Cisco FWSM.
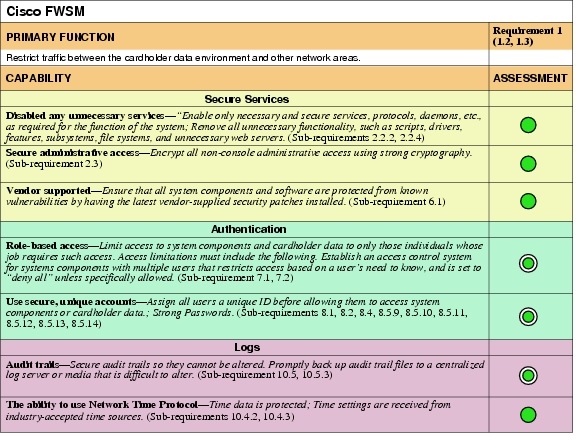
Design Considerations
•![]() Firewall rule sets must adhere to a "least amount of access necessary" policy. Rules must be defined by specific source/destination addressing and TCP/UDP ports.
Firewall rule sets must adhere to a "least amount of access necessary" policy. Rules must be defined by specific source/destination addressing and TCP/UDP ports.
•![]() For Internet edge, disable icmp permit on the outside interface of Cisco FWSM. If users need to access servers in the DMZ segment, make sure that external users can reach the servers using very specific protocol and ports.
For Internet edge, disable icmp permit on the outside interface of Cisco FWSM. If users need to access servers in the DMZ segment, make sure that external users can reach the servers using very specific protocol and ports.
•![]() Configure the ip verify reverse path command on all interfaces to provide anti-spoofing functionality.
Configure the ip verify reverse path command on all interfaces to provide anti-spoofing functionality.
•![]() Configure the console timeout commands to 15 minutes or less on the console of the Cisco FWSM.
Configure the console timeout commands to 15 minutes or less on the console of the Cisco FWSM.
•![]() Configure appropriate banner messages on login, incoming, and exec modes of the Cisco FWSM. The login banner warning should not reveal the identity of the company that owns or manages the Cisco FWSM. The incoming and executive banners should state that these areas are considered private and that unauthorized access will result in prosecution to the full extent of the law.
Configure appropriate banner messages on login, incoming, and exec modes of the Cisco FWSM. The login banner warning should not reveal the identity of the company that owns or manages the Cisco FWSM. The incoming and executive banners should state that these areas are considered private and that unauthorized access will result in prosecution to the full extent of the law.
•![]() Configure the primary login authentication of the Cisco FWSM to be directed to the Cisco Secure ACS. Individual user account profiles need to be created. Configure secondary or tertiary authentication local to the Cisco FWSM itself in the event of connectivity or Cisco Secure ACS failure.
Configure the primary login authentication of the Cisco FWSM to be directed to the Cisco Secure ACS. Individual user account profiles need to be created. Configure secondary or tertiary authentication local to the Cisco FWSM itself in the event of connectivity or Cisco Secure ACS failure.
•![]() Change default passwords and community strings to appropriate complexity.
Change default passwords and community strings to appropriate complexity.
•![]() Allow only SSHv2 (and not Telnet or SSHv1) connection from network management station to Cisco FWSM.
Allow only SSHv2 (and not Telnet or SSHv1) connection from network management station to Cisco FWSM.
Cisco Virtual Security Gateway
The Cisco Virtual Security Gateway (VSG) for Cisco Nexus 1000V Series Switches was used in the data center for setting a boundary between the sensitive scope of the retailer's cardholder data environment and out-of-scope networks. It is a virtual firewall for Cisco Nexus 1000V Series Switches that delivers security and compliance for virtual computing environments. Cisco VSG uses virtual service data path (vPath) technology embedded in the Cisco Nexus 1000V Series Virtual Ethernet Module (VEM), offering transparent firewall insertion and efficient deployment. All the policy management for VSG is done via Virtual Network Management Center (VNMC). Cisco VSG provides the following:
•![]() Zone-based security controls based on network as well as virtual machine attributes. This flexibility simplifies security policies, which are easy to troubleshoot and audit.
Zone-based security controls based on network as well as virtual machine attributes. This flexibility simplifies security policies, which are easy to troubleshoot and audit.
•![]() Secure multi-tenant deployment, protecting tenant workloads on a shared compute infrastructure.
Secure multi-tenant deployment, protecting tenant workloads on a shared compute infrastructure.
•![]() Leverages vPath intelligence for efficient network-wide deployment and accelerated performance through fast-path off-load.
Leverages vPath intelligence for efficient network-wide deployment and accelerated performance through fast-path off-load.
•![]() IT security, network, and server teams to collaborate while helping ensure administrative segregation to meet regulatory and audit requirements and reduce administrative errors.
IT security, network, and server teams to collaborate while helping ensure administrative segregation to meet regulatory and audit requirements and reduce administrative errors.
Primary PCI Function
The main function of the Cisco VSG is segmentation of PCI scope and enforcement of that new scope boundary. The Cisco VSG serves as a stateful firewall, restricting traffic between the cardholder data environment and other areas of the network. (1.2, 1.3)
Table 4-55 lists the component assessment details for the Cisco VSG.
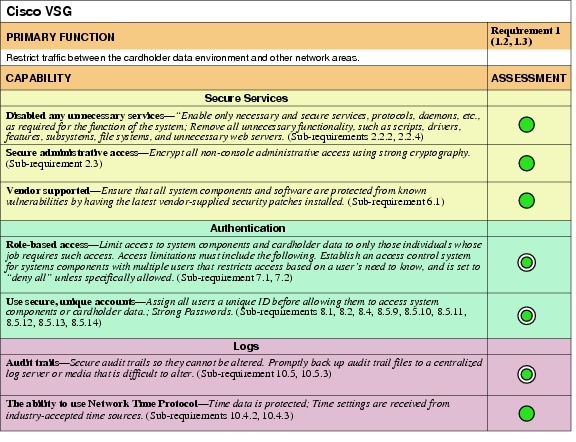
Design Considerations
Cisco VSG integrates with Cisco Nexus 1000V Series Switches to enforce security policies for your virtualized environment. VNMC provides policy management for a multitenant environment. One or more VSGs are required per tenant. VSG uses the vPath intelligence in the Virtual Ethernet Module (VEM) of the Cisco Nexus 1000V Series to provide the security policy enforcement.
Cisco VSG is deployed as a virtual appliance in vCenter. The primary function of Cisco VSG is to protect against unauthorized access to the cardholder environment.
Figure 4-14 Cisco Nexus VSG System Architecture
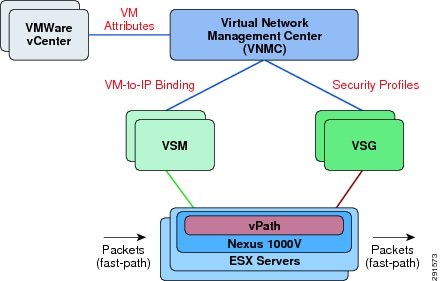
Intrusion Detection
Cisco Catalyst 6500 Series Intrusion Detection System Services Module 2
The Cisco Catalyst 6500 Series Intrusion Detection System Services Module 2 (IDSM2) is an important intrusion prevention system (IPS) solution that protects switched environments by integrating full-featured IPS functions directly into the network infrastructure through the widely deployed Cisco Catalyst chassis. This integration allows the user to monitor traffic directly off the switch backplane.
The Cisco IDSM-2 with Cisco IPS Sensor Software v6.0 helps users stop more threats with greater confidence, through the use of the following elements:
•![]() Multivector threat identification—Detailed inspection of Layer 2-7 traffic protects your network from policy violations, vulnerability exploitations, and anomalous activity.
Multivector threat identification—Detailed inspection of Layer 2-7 traffic protects your network from policy violations, vulnerability exploitations, and anomalous activity.
•![]() Accurate prevention technologies—The innovative Cisco Risk Rating feature and Meta Event Generator provide the confidence to take preventive actions on a broader range of threats without the risk of dropping legitimate traffic.
Accurate prevention technologies—The innovative Cisco Risk Rating feature and Meta Event Generator provide the confidence to take preventive actions on a broader range of threats without the risk of dropping legitimate traffic.
When combined, these elements provide a comprehensive inline prevention solution, providing the confidence to detect and stop the broadest range of malicious traffic before it affects business continuity.
Primary PCI Function
The primary PCI function of the Cisco ISDM2 is to monitor all traffic at the perimeter of the cardholder data environment as well as at critical points inside of the cardholder data environment, and alert personnel to suspected compromises (11.4).
Table 4-57 lists the component assessment details for the Cisco ISDM2.
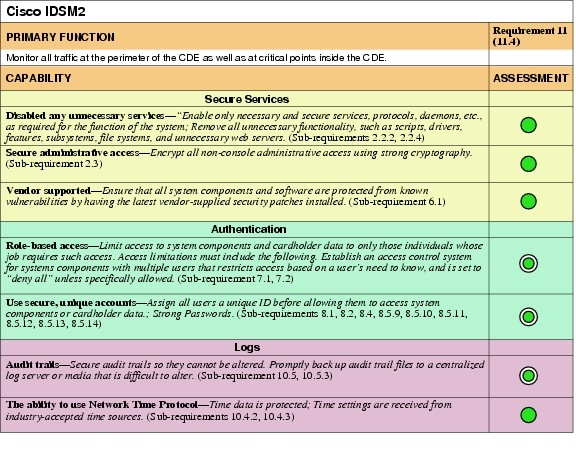
Design Considerations
•![]() Configure the Cisco IDSM2 to lock accounts so that users cannot keep trying to login after a certain number of failed attempts.
Configure the Cisco IDSM2 to lock accounts so that users cannot keep trying to login after a certain number of failed attempts.
•![]() Allow secure management of the Cisco IDSM2 only from a specific host/hosts.
Allow secure management of the Cisco IDSM2 only from a specific host/hosts.
•![]() Configure appropriate banner messages on login. The login banner warning should not reveal the identity of the company that owns or manages the Cisco IDSM2. The banners should state that these areas are considered private and that unauthorized access will result in prosecution to the full extent of the law.
Configure appropriate banner messages on login. The login banner warning should not reveal the identity of the company that owns or manages the Cisco IDSM2. The banners should state that these areas are considered private and that unauthorized access will result in prosecution to the full extent of the law.
•![]() Change default passwords and community strings to appropriate complexity.
Change default passwords and community strings to appropriate complexity.
 Feedback
Feedback