AnyConnect VPN Connectivity Options
Cisco Secure Client provides many options for automatically connecting, reconnecting, or disconnecting VPN sessions. These options provide a convenient way for your users to connect to your VPN, and they also support your network security requirements.
Starting and Restarting AnyConnect Connections
Configure VPN Connection Servers to provide the names and addresses of the secure gateways your users will manually connect to.
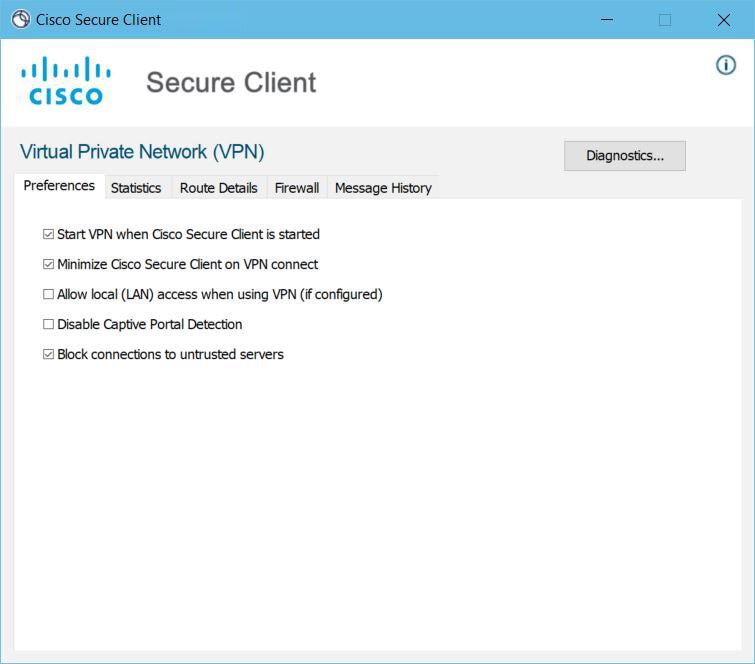
Choose from the following Cisco Secure Client capabilities to provide convenient, automatic VPN connectivity:
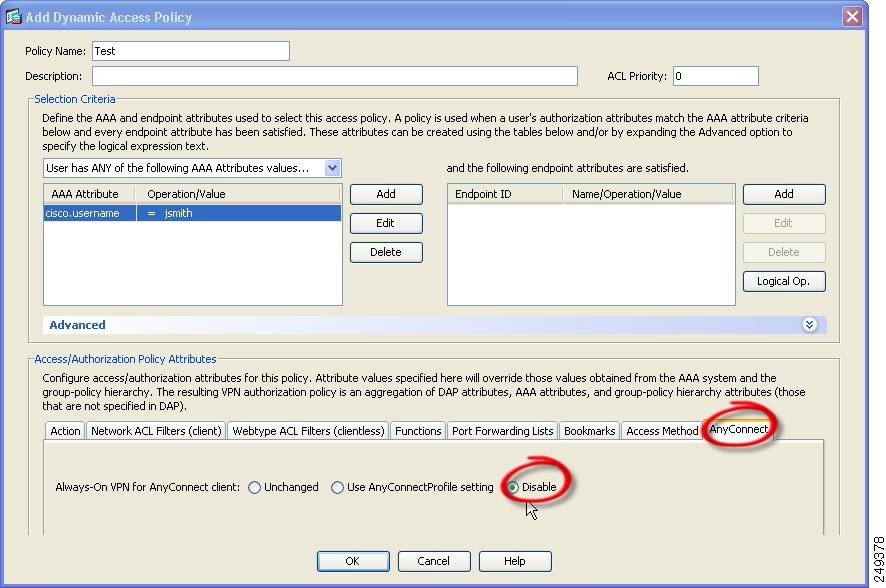
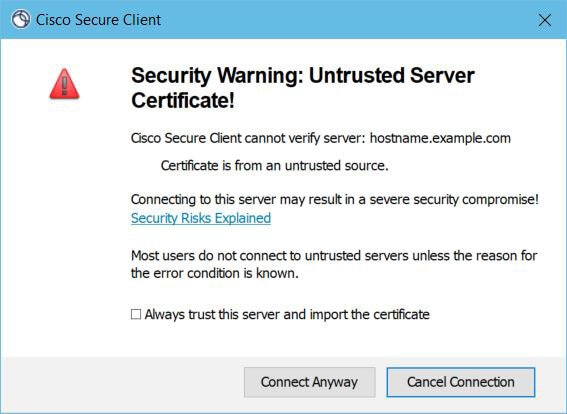
Also, consider using the following Automatic VPN Policy options to enforce greater network security or restrict network access to the VPN only:
Renegotiating and Maintaining the Cisco Secure Client Connection
You can limit how long the Secure Firewall ASA keeps an AnyConnect VPN connection available to the user even with no activity. If a VPN session goes idle, you can terminate the connection or re-negotiate the connection.
-
Keepalive—The Secure Firewall ASA sends keepalive messages at regular intervals. These messages are ignored by the Secure Firewall ASA, but are useful in maintaining connections with devices between the client and the Secure Firewall ASA.
For instructions to configure Keepalive with the ASDM or CLI, see the Enable Keepalive section in the Cisco ASA Series VPN Configuration Guide.
-
Dead Peer Detection—The Secure Firewall ASA and Cisco Secure Client send "R-U-There" messages. These messages are sent less frequently than IPsec's keepalive messages. You can enable both the Secure Firewall ASA (gateway) and Cisco Secure Client to send DPD messages, and configure a timeout interval.
-
If the client does not respond to the Secure Firewall ASA’s DPD messages, the ASA tries once more before putting the session into "Waiting to Resume" mode. This mode allows the user to roam networks, or enter sleep mode and later recover the connection. If the user does not reconnect before the idle timeout occurs, the Secure Firewall ASA will terminate the tunnel. The recommended gateway DPD interval is 300 seconds.
-
If the Secure Firewall ASA does not respond to the client's DPD messages, the client tries again before terminating the tunnel. The recommended client DPD interval is 30 seconds.
For instructions to configure DPD within the ASDM, refer to Configure Dead Peer Detection in the appropriate release of the Cisco ASA Series VPN ASDM Configuration Guide.
-
-
Best Practices:
-
Set Client DPD to 30 seconds (Group Policy > Advanced > AnyConnect Client > Dead Peer Detection).
-
Set Server DPD to 300 seconds (Group Policy > Advanced > AnyConnect Client > Dead Peer Detection).
-
Set Rekey, for both SSL and IPsec to 1 hour (Group Policy > Advanced > AnyConnect Client > Key Regeneration).
-
Terminating an AnyConnect VPN Connection
Terminating an AnyConnect VPN connection requires users to re-authenticate their endpoint to the secure gateway and create a new VPN connection.
The following connection parameters terminate the VPN session based on timeouts:
-
Maximum Connect Time—Sets the maximum user connection time in minutes. At the end of this time, the system terminates the connection. You can also allow unlimited connection time(default).
-
VPN Idle Timeout—Terminates any user’s session when the session is inactive for the specified time. If the VPN idle timeout is not configured, then the default idle timeout is used.
-
Default Idle Timeout—Terminates any user’s session when the session is inactive for the specified time. The default value is 30 minutes (or 1800 seconds).
See the Specify a VPN Session Idle Timeout for a Group Policy section in the appropriate release of the Cisco ASA Series VPN ASDM Configuration Guide to set these parameters.




 Feedback
Feedback