|
tenancy_ocid
|
String
|
OCID of the tenancy to which your account belongs. To know how to find your tenancy OCID, see here.
The tenancy OCID looks something like this - ocid1.tenancy.oc1..<unique_ID>
|
|
region
|
String
|
The unique identifier of the region in which you want the resources to be created.
Example - us-phoenix-1, us-ashburn-1
|
|
lb_size
|
String
|
A template that determines the total pre-provisioned bandwidth (ingress plus egress) of the external and internal load balancer.
Supported values: 100Mbps, 10Mbps, 10Mbps-Micro, 400Mbps, 8000Mbps
Example : 100Mbps
|
|
availability_domain
|
String
|
Example - Tpeb:PHX-AD-1, Tpeb:PHX-AD-2
|
Note
|
To get the availability domain names, see here.
|
|
|
min_and_max_instance_count
|
comma separated value
|
The minimum and the maximum number of instances that you would want to retain in the instance pool.
Example: 1,5
|
|
autoscale_group_prefix
|
String
|
The prefix to be used to name all the resources that are created using the template. For example, if the resource prefix is
given as 'autoscale', all the resources are named as follows - autoscale_resource1, autoscale_resource2 etc.
|
|
mgmt_subnet_ocid
|
String
|
OCID of the Management subnet that is to be used.
|
|
inside_subnet_ocid
|
String
|
OCID of the Inside subnet that is to be used.
|
|
function_subnet_ocid
|
String
|
OCID of the Function subnet that is to be used.
|
|
outside_subnet_ocid
|
String
|
OCID of the Outside subnet that is to be used.
|
|
mgmt_nsg_ocid
|
String
|
OCID of the Management subnet network security group that is to be used.
|
|
inside_nsg_ocid
|
String
|
OCID of the Inside subnet network security group that is to be used.
|
|
outside_nsg_ocid
|
String
|
OCID of the Outside subnet network security group that is to be used.
|
|
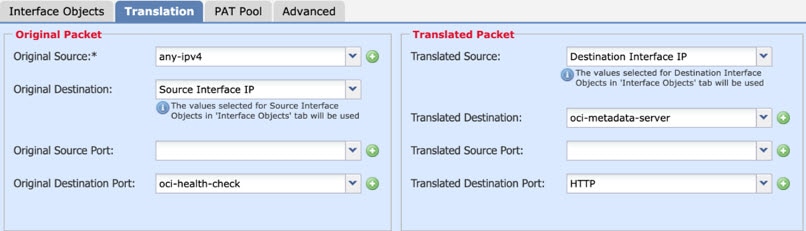
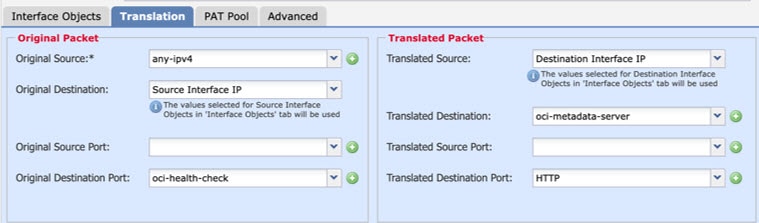
elb_listener_port
|
comma separated Values
|
List of the communication ports for the external load balancer listener.
Example: 80
|
|
ilb_listener_port
|
comma separated Values
|
List of the communication ports for the internal load balancer listener.
Example: 80
|
|
health_check_port
|
String
|
The backend server port of load balancer against which to run the health check.
Example: 8080
|
|
instance_shape
|
String
|
The shape of the instance to be created. The shape determines the number of CPUs, amount of memory, and other resources allocated
to the instance.
Supported shapes :"VM.Standard2.4" & "VM.Standard2.8"
|
|
lb_bs_policy
|
String
|
The load balancer policy to be used for the internal and external load balancer’s backend set. To know more about how load
balancer policies work, see here
Supported values: "ROUND_ROBIN", "LEAST_CONNECTIONS", "IP_HASH"
|
|
image_name
|
String
|
The name of the marketplace image to be used for creating the instance configuration.
Default value : " Cisco Firepower NGFW virtual firewall (NGFWv)"
|
Note
|
If the user wants to deploy custom image, user has to configure the custom_image_ocid parameter.
|
|
|
scaling_thresholds
|
Comma separated value
|
The CPU usage thresholds to be used for scale-in and scale-out. Provide the scale-in and scale-out threshold values as comma
separated input.
Example : 15,50
where, 15 is the scale-in threshold and 50 is the scale-out threshold.
|
|
compartment_id
|
String
|
The OCID of the compartment in which to create the resources.
Example: ocid1.compartment.oc1..<unique_ID>
|
|
compartment_name
|
String
|
Name of the compartment
|
|
custom_image_ocid
|
String
|
OCID of the custom image to be used to create instance configuration if the marketplace image is not to be used.
|
Note
|
custom_image_ocid is optional parameter
|
|
|
ftdv_password
|
String
|
The password for Firewall Threat Defense Virtual in the encrypted form, to SSH into the Firewall Threat Defense Virtual for configuration. Use configuration guide for the instructions on how to encrypt password or see here.
|
|
ftdv_license_type
|
String
|
Type of Firewall Threat Defense Virtual license either BYOL or PAYG. Currently, BYOL is supported.
|
|
cryptographic_endpoint
|
String
|
Cryptographic endpoint is a URL, that is used for decrypting password. It can be found in the Vault.
|
|
master_encryption_key_id
|
String
|
The OCID of key with which the password was encrypted. It can be found in the Vault.
|
Note
|
master_encryption_key_id and cryptographic_endpoint both must belong to same vault.
|
|
|
fmc_ip
|
String
|
IP address of Secure Firewall Management Center. IP of Firewall Management Center that will be used by customer to manage Firewall Threat Defense Virtual instances.
|
Note
|
Firewall Management Center IP can be private only if it is in the same subnet as Firewall Threat Defense Virtual, otherwise Public IP must be used for all other cases.
|
|
|
fmc_username
|
String
|
Username of the Firewall Management Center account. This username will be used to login into the Firewall Management Center to configure each time the new Firewall Threat Defense Virtual instance comes.
|
|
fmc_password
|
String
|
Password of Firewall Management Center in encrypted form. For procedure on how to encrypt password, see here.
|
|
fmc_device_group_name
|
String
|
There must be a device group in Firewall Management Center, all the Firewall Threat Defense Virtual part of this Autoscale solution will be added into that group, so that same policies and configuration can be applied to
all of them.
|
|
enable_memory_based_scaling
|
Bool
|
Publish Firewall Threat Defense Virtual Memory usage from the Secure Firewall Management Center Virtual. By enabling this flag Scaling can happen based on Memory utilization as well. By default CPU utilization is used.
|
|
fmc_metrics_username
|
String
|
In case you opt for Memory Utilization by enabling flag enable_memory_based_scaling, an extra Firewall Management Center user account is needed as that will be used continuously to pull memory usage from all the running Firewall Threat Defense Virtual instances.
|
|
fmc_metrics_password
|
String
|
Password of extra Firewall Management Center account in encrypted form. For procedure on how to encrypt password, see here.
|
|
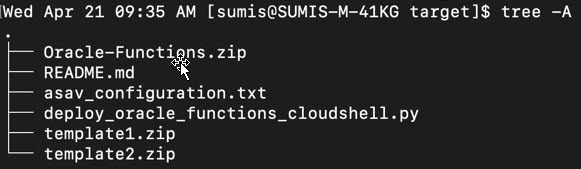
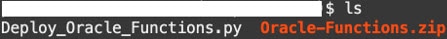
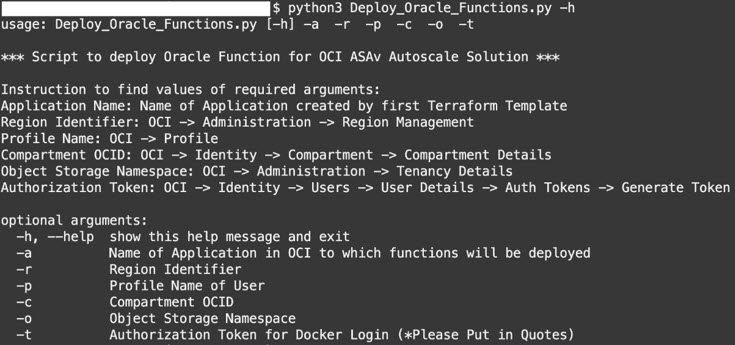
Profile Name
|
|
It is the User’s profile name in OCI. It can be found under profile section of the user. Example: “oracleidentitycloudservice/
<user>@<mail>.com”
|
|
Object Storage Namespace
|
|
It is unique identifier created at the time of Tenancy creation. Go to
|
|
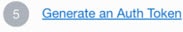
Authorization Token
|
|
This is used as password for docker login which authorizes it to push Oracle-Functions into the OCI container registry. Go
to .
|




 Feedback
Feedback