- Securing User Services Overview
- Autosecure
-
-
-
- Configuring RADIUS
- AAA Dead-Server Detection
- ACL Default Direction
- Attribute Screening for Access Requests
- Enable Multilink PPP via RADIUS for Preauthentication User
- Enhanced Test Command
- Framed-Route in RADIUS Accounting
- Offload Server Accounting Enhancement
- Per VRF AAA
- RFC-2867 RADIUS Tunnel Accounting
- RADIUS Attribute Screening
- RADIUS Centralized Filter Management
- RADIUS Debug Enhancements
- RADIUS Logical Line ID
- RADIUS NAS-IP-Address Attribute Configurability
- RADIUS Route Download
- RADIUS Support of 56-Bit Acct Session-Id
- RADIUS Tunnel Preference for Load Balancing and Fail-Over
- RADIUS Server Reorder on Failure
- Tunnel Authentication via RADIUS on Tunnel Terminator
-
-
-
- RADIUS Attributes Overview and RADIUS IETF Attributes
- RADIUS Vendor-Proprietary Attributes
- Vendor-Specific Attributes (VSA) and RADIUS Disconnect-Cause Attribute Values
- Connect-Info RADIUS Attribute 77
- Encrypted Vendor Specific Attributes
- Local AAA Server
- Per-User QoS via AAA Policy Name
- RADIUS Attribute 5 (NAS-Port) Format Specified on a Per-Server Group Level
- RADIUS Attribute 8 (Framed-IP-Address) in Access Requests
- RADIUS Attribute 82: Tunnel Assignment ID
- RADIUS Attribute 104
- RADIUS Progress Codes
- RADIUS Timeout Set During Pre-Authentication
- RADIUS Tunnel Attribute Extensions
- V.92 Reporting Using RADIUS Attribute v.92-info
-
- Cisco IOS Login Enhancements (Login Block)
- Cisco IOS Resilient Configuration
- Image Verification
- IP Source Tracker
- Role-Based CLI Access
- Finding Feature Information
- Contents
- Prerequisites for Network Admission Control
- Restrictions for Network Admission Control
- Information About Network Admission Control
- Configuring the ACL and Admission Control
- Configuring Global EAPoUDP Values
- Configuring an Interface-Specific EAPoUDP Association
- Configuring AAA for EAPoUDP
- Configuring the Identity Profile and Policy
- Clearing EAPoUDP Sessions That Are Associated with an Interface
- Verifying Network Admission Control
- Troubleshooting Network Admission Control
- Monitoring and Controlling NAC with the CISCO-NAC-NAD-MIB
Network Admission Control
The Network Admission Control feature addresses the increased threat and impact of worms and viruses have on business networks. This feature is part of the Cisco Self-Defending Network Initiative that helps customers identify, prevent, and adapt to security threats.
In its initial phase, the Cisco Network Admission Control (NAC) functionality enables Cisco routers to enforce access privileges when an endpoint attempts to connect to a network. This access decision can be on the basis of information about the endpoint device, such as its current antivirus state. The antivirus state includes information such as version of antivirus software, virus definitions, and version of scan engine.
Network admission control systems allow noncompliant devices to be denied access, placed in a quarantined area, or given restricted access to computing resources, thus keeping insecure nodes from infecting the network.
The key component of the Cisco Network Admission Control program is the Cisco Trust Agent, which resides on an endpoint system and communicates with Cisco routers on the network. The Cisco Trust Agent collects security state information, such as what antivirus software is being used, and communicates this information to Cisco routers. The information is then relayed to a Cisco Secure Access Control Server (ACS) where access control decisions are made. The ACS directs the Cisco router to perform enforcement against the endpoint.
Finding Feature Information
Your software release may not support all the features documented in this module. For the latest feature information and caveats, see the release notes for your platform and software release. To find information about the features documented in this module, and to see a list of the releases in which each feature is supported, see the "Feature Information for Network Admission Control" section.
Use Cisco Feature Navigator to find information about platform support and Cisco IOS and Catalyst OS software image support. To access Cisco Feature Navigator, go to http://tools.cisco.com/ITDIT/CFN/jsp/index.jsp. An account on Cisco.com is not required.
Contents
•![]() Prerequisites for Network Admission Control
Prerequisites for Network Admission Control
•![]() Restrictions for Network Admission Control
Restrictions for Network Admission Control
•![]() Information About Network Admission Control
Information About Network Admission Control
•![]() How to Configure Network Admission Control
How to Configure Network Admission Control
•![]() Configuration Examples for Network Admission Control
Configuration Examples for Network Admission Control
•![]() Feature Information for Network Admission Control
Feature Information for Network Admission Control
Prerequisites for Network Admission Control
•![]() The Cisco IOS router must be running Cisco IOS software Release 12.3(8)T or later.
The Cisco IOS router must be running Cisco IOS software Release 12.3(8)T or later.
•![]() The Cisco Trust Agent must be installed on the endpoint devices (for example, on PCs and laptops).
The Cisco Trust Agent must be installed on the endpoint devices (for example, on PCs and laptops).
•![]() A Cisco Secure ACS is required for authentication, authorization, and accounting (AAA).
A Cisco Secure ACS is required for authentication, authorization, and accounting (AAA).
•![]() A proficiency with configuring access control lists (ACLs) and AAA is necessary.
A proficiency with configuring access control lists (ACLs) and AAA is necessary.
Restrictions for Network Admission Control
•![]() This feature is available only on Cisco IOS firewall feature sets.
This feature is available only on Cisco IOS firewall feature sets.
Information About Network Admission Control
Before configuring the Network Admission Control feature, the following concepts need to be understood:
•![]() Virus Infections and Their Effect on Networks
Virus Infections and Their Effect on Networks
•![]() How Network Admission Control Works
How Network Admission Control Works
•![]() Network Admission Control and Authentication Proxy
Network Admission Control and Authentication Proxy
Virus Infections and Their Effect on Networks
Virus infections are the single largest cause of serious security breaches for networks and often result in huge financial losses. Sources of virus infections are insecure endpoints (for example, PCs, laptops, and servers). Although the endpoints may have antivirus software installed, the software is often disabled. Even if the software is enabled, the endpoints may not have the latest virus definitions and scan engines. A larger security risk is from devices that do not have any antivirus software installed. Although antivirus vendors today are making it more difficult to disable the antivirus software, they are not addressing the risk of outdated virus definitions and scan engines.
How Network Admission Control Works
Endpoint systems, or clients, are normally hosts on the network, such as PCs, laptops, workstations, and servers. The endpoint systems are a potential source of virus infections, and their antivirus states have to be validated before they are granted network access. When an endpoint attempts an IP connection to a network through an upstream Cisco network access device (typically a Cisco IOS router), the router challenges the endpoint for its antivirus state. The endpoint systems run a client called Cisco Trust Agent, which collects antivirus state information from the end device and transports the information to the Cisco network access device. This information is then communicated to a Cisco Secure ACS where the antivirus state of the endpoint is validated and access control decisions are made and returned to Cisco network access devices. The network devices either permit, deny, or quarantine the end device. The Cisco Secure ACS may in turn use back-end antivirus vendor-specific servers for evaluating the antivirus state of the endpoint.
Figure 1 illustrates how Cisco Network Admission Control works.
Figure 1 Cisco IOS Network Admission Control System
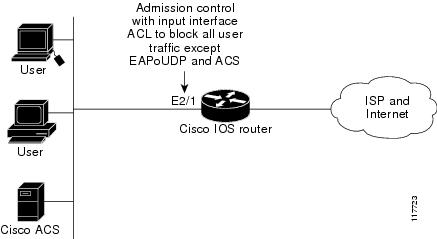
Figure 1 shows that IP admission control is applied at the LAN interface. All network devices must be validated for their antivirus states upon their initial IP connections through the router. Until then, all traffic from endpoint systems (except for EAPoUDP and Cisco Secure ACS traffic) is blocked at the interface.
The endpoint system is then challenged for its antivirus state over an EAPoUDP association. The endpoint system gains access to the network if it complies with the network admission control policy as evaluated by the Cisco Secure ACS. If the endpoint system does not comply, the device is either denied access or quarantined.
Network Access Device
A network access device (NAD) is typically a Cisco IOS router (a Layer 3 Extensible Authentication Protocol over User Datagram Protocol [EAPoUDP] access point) that provides connectivity to external networks, such as the Internet or remote enterprise networks. Cisco Network Admission Control functionality may have an Intercept ACL, which determines connections that are intercepted for network admission. Connections from endpoints that match the access list are intercepted by Network Admission Control and are challenged for their antivirus states over a Layer 3 association before they are granted network access.
Cisco Trust Agent
Cisco Trust Agent is a specialized software that runs on endpoint systems. Cisco Trust Agent responds to challenges from the router about the antivirus state of an endpoint system. If an endpoint system is not running the Cisco Trust Agent, the network access device (router) classifies the endpoint system as "clientless." The network access device uses the EOU clientless username and EOU clientless password that are configured on the network access device as the credentials of the endpoint system for validation with Cisco Secure ACS. The policy attributes that are associated with this username are enforced against the endpoint system.
Cisco Secure ACS
Cisco Secure ACS provides authentication, authorization, and accounting services for network admission control using industry-standard RADIUS authentication protocol. Cisco Secure ACS returns access control decisions to the network access device on the basis of the antivirus credentials of the endpoint system.
Using RADIUS cisco_av_pair vendor-specific attributes (VSAs), the following attribute-value pairs (AV pairs) can be set on the Cisco Secure ACS. These AV pairs are sent to the network access device along with other access-control attributes.
•![]() url-redirect—Enables the AAA client to intercept an HTTP request and redirect it to a new URL. This redirection is especially useful if the result of posture validation indicates that the network access control endpoint requires an update or patch to be made available on a remediation web server. For example, a user can be redirected to a remediation web server to download and apply a new virus Directory Administration Tool (DAT) file or an operating system patch. (See the following example.)
url-redirect—Enables the AAA client to intercept an HTTP request and redirect it to a new URL. This redirection is especially useful if the result of posture validation indicates that the network access control endpoint requires an update or patch to be made available on a remediation web server. For example, a user can be redirected to a remediation web server to download and apply a new virus Directory Administration Tool (DAT) file or an operating system patch. (See the following example.)
url-redirect=http://10.1.1.1
•![]() posture-token—Enables Cisco Secure ACS to send a text version of a system posture token (SPT) that is derived by posture validation. The SPT is always sent in numeric format, and using the posture-token AV pair makes it easier to view the result of a posture validation request on the AAA client. (See the following example.)
posture-token—Enables Cisco Secure ACS to send a text version of a system posture token (SPT) that is derived by posture validation. The SPT is always sent in numeric format, and using the posture-token AV pair makes it easier to view the result of a posture validation request on the AAA client. (See the following example.)
posture-token=Healthy
Valid SPTs, in order of best to worst, are as follows:
–![]() Healthy
Healthy
–![]() Checkup
Checkup
–![]() Quarantine
Quarantine
–![]() Infected
Infected
–![]() Unknown
Unknown
•![]() status-query-timeout—Overrides the status-query default value of the AAA client with the user specified value, in seconds. (See the following example.)
status-query-timeout—Overrides the status-query default value of the AAA client with the user specified value, in seconds. (See the following example.)
status-query-timeout=150
For more information about AV pairs that are supported by Cisco IOS software, see the documentation for the releases of Cisco IOS software that are implemented on your AAA clients.
Remediation
Network Admission Control supports HTTP redirection that redirects any HTTP request from the endpoint device to a specified redirect address. This support mechanism redirects all HTTP requests from a source to a specified web page (URL) to which the latest antivirus files can be downloaded. For the HTTP redirection to work, the value must be set for the "url-redirect" VSA on the ACS and, correspondingly, associate an access control entry in the downloadable ACL that permits the access of the endpoint system to the redirect URL address. After the value of the url-redirect VSA has been set and the access control entry has been associated, any HTTP request that matches the IP admission Intercept ACL are redirected to the specified redirect URL address.
Network Admission Control and Authentication Proxy
It is possible that network admission control and authentication proxy can be configured for the same set of hosts on a given interface. In each case, the Intercept ACL should be the same for IP admission EAPoUDP and authentication proxy. IP admission proxy with proxy authentication should be configured first, followed by IP admission control.
NAC MIB
The NAC MIB feature adds Simple Network Management Protocol (SNMP) support for the NAC subsystem. Using SNMP commands (get and set operations), an administrator can monitor and control NAC sessions on the network access device (NAD).
For more information about SNMP get and set operations, see the subsection "Related Documents" in the section "Additional References."
Correlation Between SNMP Get and Set Operations and the Cisco CLI
Most of the objects in the object tables in the NAC MIB (CISCO-NAC-NAD-MIB.my) describe various EAPoUDP and session parameters that are applicable to the setup of a NAD. These properties can be viewed and modified by performing various SNMP get and set operations. Many of the values of the table objects can also be viewed or modified by configuring corresponding command-line interface (CLI) commands on a router. For example, an SNMP get operation can be performed on the cnnEOUGlobalObjectsGroup table or the show eou command can be configured on a router. The parameter information obtained from the SNMP get operation is the same as the output from the show eou command. Similarly, performing an SNMP get operation on the table cnnEouIfConfigTable provides interface-specific parameters that can also be viewed in output from the show eou command.
SNMP set operations are allowed for table objects that have corresponding CLI commands, which can be used to modify table object values. For example, to change the value range for the cnnEouHostValidateAction object in the cnnEouHostValidateAction MIB table to 2, you can either perform the SNMP set operation or configure the eou initialize all command on a router.
For examples of NAC MIB output, see the subsection "NAC MIB Output: Examples" in the section "Configuration Examples for Network Admission Control."
Initializing and Revalidating Sessions
NAC allows administrators to initialize and revalidate sessions using the following CLI commands:
•![]() eou initialize all
eou initialize all
•![]() eou initialize authentication clientless
eou initialize authentication clientless
•![]() eou initialize authentication eap
eou initialize authentication eap
•![]() eou initialize authentication static
eou initialize authentication static
•![]() eou initialize ip {ip-address}
eou initialize ip {ip-address}
•![]() eou initialize mac {mac-address}
eou initialize mac {mac-address}
•![]() eou initialize posturetoken {string}
eou initialize posturetoken {string}
•![]() eou revalidate all
eou revalidate all
•![]() eou revalidate authentication clientless
eou revalidate authentication clientless
•![]() eou revalidate authentication eap
eou revalidate authentication eap
•![]() eou revalidate authentication static
eou revalidate authentication static
•![]() eou revalidate ip {ip-address}
eou revalidate ip {ip-address}
•![]() eou revalidate mac {mac-address}
eou revalidate mac {mac-address}
•![]() eou revalidate posturetoken {string}
eou revalidate posturetoken {string}
The initialization and revalidation actions can also be accomplished by performing SNMP set operations on the objects of the cnnEouHostValidateAction table. For more information about initializing and revalidating sessions, see the section "CLI Commands That Correlate to cnnEouHostValidateAction Table Objects."
For examples of CLI commands that correlate to changes that can be made to cnnEouHostValidateAction table objects, see the subsection "NAC MIB Output: Examples" in the section "Configuration Examples for Network Admission Control."
Session-Specific Information
The NAC MIB provides a way to view session-specific details using the cnnEouHostQueryTable and cnnEouHostResultTable. The cnnEouHostQueryTable is used to build the query. The query is the same format as the show eou ip {ip-address} command (that is, the IP address would be shown as in the show eou ip command—for example, 10.1.1.1). Administrators must use the SNMP set operation on the objects of the cnnEouHostQueryTable to create the query. The results of the query are stored as a row in the cnnEouHostResultTable. For more information about viewing session-specific details, see the section "Viewing MIB Query Results."
Using show Commands to View MIB Object Information
The CLI commands show eou, show eou all, show eou authentication, show eou initialize, show eou ip, show eou mac, show eou posturetoken, show eou revalidate, and show ip device tracking all provide the same output information as that in the CISCO-NAC-NAD-MIB tables using SNMP get operations.
For examples of show command output information that can also be viewed in MIB object tables, see the subsection "NAC MIB Output: Examples" in the section "Configuration Examples for Network Admission Control."
How to Configure Network Admission Control
This section contains the following procedures:
•![]() Configuring the ACL and Admission Control (required)
Configuring the ACL and Admission Control (required)
•![]() Configuring Global EAPoUDP Values (optional)
Configuring Global EAPoUDP Values (optional)
•![]() Configuring an Interface-Specific EAPoUDP Association (optional)
Configuring an Interface-Specific EAPoUDP Association (optional)
•![]() Configuring AAA for EAPoUDP (optional)
Configuring AAA for EAPoUDP (optional)
•![]() Configuring the Identity Profile and Policy (required)
Configuring the Identity Profile and Policy (required)
•![]() Clearing EAPoUDP Sessions That Are Associated with an Interface (optional)
Clearing EAPoUDP Sessions That Are Associated with an Interface (optional)
•![]() Verifying Network Admission Control (optional)
Verifying Network Admission Control (optional)
•![]() Troubleshooting Network Admission Control (optional)
Troubleshooting Network Admission Control (optional)
•![]() Monitoring and Controlling NAC with the CISCO-NAC-NAD-MIB (optional)
Monitoring and Controlling NAC with the CISCO-NAC-NAD-MIB (optional)
Configuring the ACL and Admission Control
Network admission control is applied in the inbound direction at any interface. Applying network admission control inbound at an interface causes network admission control to intercept the initial IP connections of the intercept end system through the router.
Use the steps in this section to configure an intercept ACL.

Note ![]() In this configuration, an intercept ACL is defined as "101," and the Intercept ACL is associated with the IP admission control rule "greentree." Any IP traffic that is destined to the 192.50.0.0 network are subjected to validation. In addition, beginning with Step 5, an intercept ACL is applied inbound to the interface that is associated with network admission control. This ACL typically blocks access to endpoint systems until they are validated. This ACL is referred to as the default access list.
In this configuration, an intercept ACL is defined as "101," and the Intercept ACL is associated with the IP admission control rule "greentree." Any IP traffic that is destined to the 192.50.0.0 network are subjected to validation. In addition, beginning with Step 5, an intercept ACL is applied inbound to the interface that is associated with network admission control. This ACL typically blocks access to endpoint systems until they are validated. This ACL is referred to as the default access list.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() access-list access-list-number {permit | deny} protocol source destination
access-list access-list-number {permit | deny} protocol source destination
4. ![]() ip admission name admission-name [eapoudp | proxy {ftp | http | telnet}] [list {acl | acl-name}]
ip admission name admission-name [eapoudp | proxy {ftp | http | telnet}] [list {acl | acl-name}]
5. ![]() interface type slot/port
interface type slot/port
6. ![]() ip address ip-address mask
ip address ip-address mask
7. ![]() ip admission admission-name
ip admission admission-name
8. ![]() exit
exit
9. ![]() access-list access-list-number {permit | deny} protocol source destination
access-list access-list-number {permit | deny} protocol source destination
10. ![]() ip access-group {access-list-number | access-list-name} in
ip access-group {access-list-number | access-list-name} in
DETAILED STEPS
Configuring Global EAPoUDP Values
To configure global EAPoUDP values, perform the following steps.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() eou {allow | clientless | default | initialize | logging | max-retry | port | rate-limit | revalidate | timeout}
eou {allow | clientless | default | initialize | logging | max-retry | port | rate-limit | revalidate | timeout}
DETAILED STEPS
Configuring an Interface-Specific EAPoUDP Association
To configure an EAPoUDP association that can be changed or customized for a specific interface that is associated with network admission control, perform the following steps.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() interface type slot/port
interface type slot/port
4. ![]() eou [default | max-retry | revalidate | timeout]
eou [default | max-retry | revalidate | timeout]
DETAILED STEPS
Configuring AAA for EAPoUDP
To set up AAA for EAPoUDP, perform the following steps.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() aaa new-model
aaa new-model
4. ![]() aaa authentication eou default enable group radius
aaa authentication eou default enable group radius
5. ![]() aaa authorization network default group radius
aaa authorization network default group radius
6. ![]() radius-server host {hostname | ip-address}
radius-server host {hostname | ip-address}
7. ![]() radius-server key {0 string | 7 string | string}
radius-server key {0 string | 7 string | string}
DETAILED STEPS
Configuring the Identity Profile and Policy
Identity is a common infrastructure that is used to specify local profile and policy configurations. The identity profile allows you to statically authorize or validate individual devices on the basis of IP address, MAC address, or device type. Each statically authenticated device can be associated with a local policy that specifies the network access control attributes. Hosts are added to this "exception list" using the identity profile command, and corresponding policies are associated with these hosts using the identity policy command.
If the client is part of the identity (that is, the client is on the exception list), the status of the client is set on the basis of the identity configuration. The client does not have to go through the posture validation process, and the associated identity policy is applied for the client.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() configure terminal
configure terminal
3. ![]() identity profile eapoudp
identity profile eapoudp
4. ![]() device {authorize {ip address ip-address {policy policy-name} | mac-address mac-address | type {cisco | ip | phone}} | not-authorize}
device {authorize {ip address ip-address {policy policy-name} | mac-address mac-address | type {cisco | ip | phone}} | not-authorize}
5. ![]() exit
exit
6. ![]() identity policy policy-name [access-group group-name | description line-of-description | redirect url | template [virtual-template interface-name]]
identity policy policy-name [access-group group-name | description line-of-description | redirect url | template [virtual-template interface-name]]
7. ![]() access-group group-name
access-group group-name
8. ![]() exit
exit
9. ![]() exit
exit
10. ![]() ip access-list extended access-list-name
ip access-list extended access-list-name
11. ![]() {permit | deny} source source-wildcard destination destination-wildcard
{permit | deny} source source-wildcard destination destination-wildcard
DETAILED STEPS
Clearing EAPoUDP Sessions That Are Associated with an Interface
To clear EAPoUDP sessions that are associated with a particular interface or that are on the NAD, perform the following steps.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() clear eou all
clear eou all
DETAILED STEPS
Verifying Network Admission Control
To verify EAP and EAPoUDP messages or sessions, perform the following steps. The show commands may be used in any order or independent of the other show command.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() show eou all
show eou all
3. ![]() show ip admission eapoudp
show ip admission eapoudp
DETAILED STEPS
Troubleshooting Network Admission Control
The following commands may be used to display information about EAP and EAPoUDP messages or sessions. The debug commands may be used in any order or independent of the other debug commands.
SUMMARY STEPS
1. ![]() enable
enable
2. ![]() debug eap {all | errors | packets | sm}
debug eap {all | errors | packets | sm}
3. ![]() debug eou {all | eap | errors | packets | sm}
debug eou {all | eap | errors | packets | sm}
4. ![]() debug ip admission eapoudp
debug ip admission eapoudp
DETAILED STEPS
Monitoring and Controlling NAC with the CISCO-NAC-NAD-MIB
This section includes the following tasks:
•![]() CLI Commands That Correlate to cnnEouHostValidateAction Table Objects
CLI Commands That Correlate to cnnEouHostValidateAction Table Objects
•![]() CLI Commands That Correlate to cnnEouIfConfigTable Objects
CLI Commands That Correlate to cnnEouIfConfigTable Objects
•![]() CLI Commands That Correlate to cnnEouHostValidateAction Table Objects
CLI Commands That Correlate to cnnEouHostValidateAction Table Objects
CLI Commands That Correlate to cnnEouGlobalObjectsGroup Table Objects
An SNMP get or set operation can be performed to obtain or change information about value ranges for objects in the cnnEouGlobalObjectsGroup table. The same information can be viewed in output from the show eou command. Table 1 displays examples of some global configuration objects and the SNMP get and set operations required to obtain or change their values.
For an example of show eou command output, see the section "show eou" section.
CLI Commands That Correlate to cnnEouIfConfigTable Objects
An SNMP get operation is performed to obtain information about value ranges for objects in the cnnEouIfConfigTable. The same information can be viewed in output from the show eou command. Table 2 displays examples of some interface-specific configuration objects and the SNMP get operations required to obtain their values.
CLI Commands That Correlate to cnnEouHostValidateAction Table Objects
EOU sessions can be initialized or revalidated by the CLI or by using the SNMP set operation on the table cnnEouHostValidateAction.
Following are some examples (listed by CLI command) that correlate to MIB objects.
eou initialize all
EOU initialization can be accomplished for all sessions by using the eou initialize all command or by using an SNMP set operation on the object cnnEouHostValidateAction. This object must be set to the numeric value 2.
eou initialize authentication clientless
EOU initialization can be accomplished for sessions having an authentication type "clientless" using the eou initialize authentication clientless command or an SNMP set operation on the object cnnEouHostValidateAction. This object must be set to the numeric value 3.
eou initialize ip
EOU initialization can be accomplished for a particular session using the eou initialize ip {ip-address} command.
To achieve the same result using an SNMP operation, three objects have to be set in the cnnEouHostValidateAction MIB table:
•![]() cnnEouHostValidateAction—The value range must be set.
cnnEouHostValidateAction—The value range must be set.
•![]() cnnEouHostValidateIpAddrType—The IP address type must be set. This value must be set to IPv4 because IPv4 is currently the only address type supported by NAC. (This value is the type of address being set for the cnnEouHostValidateIPAddr object.)
cnnEouHostValidateIpAddrType—The IP address type must be set. This value must be set to IPv4 because IPv4 is currently the only address type supported by NAC. (This value is the type of address being set for the cnnEouHostValidateIPAddr object.)
•![]() cnnEouHostValidateIPAddr—The IP address must be set.
cnnEouHostValidateIPAddr—The IP address must be set.

Note ![]() The three MIB objects should be set in a single SNMP set operation.
The three MIB objects should be set in a single SNMP set operation.
eou initialize posturetoken
All sessions having a particular posturetoken can be initialized using the eou initialize posturetoken {string} command. The default value range for this command is 8.
To achieve the same result using an SNMP set operation, you must set the following objects:
•![]() cnnEouHostValidateAction—Set this value to 8.
cnnEouHostValidateAction—Set this value to 8.
•![]() cnnEouHostValidatePostureTokenStr—Set the string value.
cnnEouHostValidatePostureTokenStr—Set the string value.

Note ![]() The two MIB objects should be set in a single SNMP set operation.
The two MIB objects should be set in a single SNMP set operation.
Creating MIB Query Tables
The MIB table cnnEouHostQueryTable is used to create, or build, MIB queries.
MIB Query Correlating to the CLI show eou all Command
To build a query that provides the same results as using the show eou all command, perform the following SNMP get operation.
The object cnnEouHostQueryMask in the table cnnEouHostQueryTable indicates the kind of query. The corresponding value of the cnnEouHostQueryMask object in output from the show eou all command is 8 (the integer value).
SUMMARY STEPS
1. ![]() Set the cnnEouHostQueryStatus object to createandgo.
Set the cnnEouHostQueryStatus object to createandgo.
2. ![]() Set the cnnEouHostQueryMask object to 8.
Set the cnnEouHostQueryMask object to 8.
3. ![]() Set the cnnEouHostQueryStatus object to active to indicate that query creation is complete.
Set the cnnEouHostQueryStatus object to active to indicate that query creation is complete.
DETAILED STEPS

Note ![]() Examples are not shown in the previous table because the format differs depending on the software you are using.
Examples are not shown in the previous table because the format differs depending on the software you are using.
What to Do Next
View the results. See the section "Viewing MIB Query Results Correlating to the show eou all Command."
Viewing MIB Query Results Correlating to the show eou all Command
After the MIB query has been built and you have indicated that you are finished (with the "active" status), the results can be viewed. A query in the cnnEouHostQueryTable is represented by a row. The row number is the Query Index. Similarly, the cnnEouHostResultTable is composed of result rows. Each row in the cnnEouHostResultTable is uniquely identified by a combination of Query Index and Result Index. The results of the cnnEouHostQueryTable index and the cnnEouHostResultTable have to be matched. Match one row in the Query table to one of the rows in the Result table. For example, if a query that corresponds to a show command results in ten sessions, the Result table has ten rows, each row corresponding to a particular session. The first row in the Result table is R1.1. The second row is R1.2, and so on to R1.10. If another query is created in the Query table, and it results in five sessions, five rows are created in the Result table (R2.1, R2.2, R2.3, R2.4, and R2.5).
Table 3 illustrates how the Query table sessions are mapped to Result table rows.
|
|
|
|---|---|
Q1 (10 sessions) |
R1.1, R1.2, R1.3, R1.4, R1.5, R1.6, R1.7, R1.8, R1.9, R1.10 |
Q2 (5 sessions) |
R2.1, R2.2, R2.3, R2.4, R2.5 |
Creating the SNMP Query
To create an SNMP query that provides the same information as output from the show eou ip {ip-address} command, perform the following steps.
SUMMARY STEPS
1. ![]() Set cnnEouHostQueryStatus to createandgo.
Set cnnEouHostQueryStatus to createandgo.
2. ![]() Set cnnEouHostQueryIpAddrType to IPv4 and the IP address (for example, 10.2.3.4).
Set cnnEouHostQueryIpAddrType to IPv4 and the IP address (for example, 10.2.3.4).
3. ![]() Set cnnEouHostQueryStatus to active.
Set cnnEouHostQueryStatus to active.
DETAILED STEPS

Note ![]() Examples are not shown in the previous table because the format differs depending on the software you are using.
Examples are not shown in the previous table because the format differs depending on the software you are using.
Viewing the Results
To view the results in the cnnEouHostResultTable, perform the following steps.
SUMMARY STEPS
1. ![]() Perform a get operation on cnnEouHostQueryRows.
Perform a get operation on cnnEouHostQueryRows.
2. ![]() Perform a get operation on the cnnEouHostResultTable objects in the format resultTableObjectName.QueryIndex.ResultIndex.
Perform a get operation on the cnnEouHostResultTable objects in the format resultTableObjectName.QueryIndex.ResultIndex.
DETAILED STEPS

Note ![]() Examples are not shown in the above table because the format differs depending on the software you are using.
Examples are not shown in the above table because the format differs depending on the software you are using.
MIB Query Correlating to the show eou ip Command
To build a MIB query that provides the same results as the show eou ip {ip-address}command, perform the following SNMP get operation.
SUMMARY STEPS
1. ![]() Set the cnnEouHostQueryStatus object to createandgo.
Set the cnnEouHostQueryStatus object to createandgo.
2. ![]() Set the cnnEouHostQueryIpAddrType object to "IPv4".
Set the cnnEouHostQueryIpAddrType object to "IPv4".
3. ![]() Set the cnnEouHostQueryIpAddr object to IP address (for example, 10.2.3.4).
Set the cnnEouHostQueryIpAddr object to IP address (for example, 10.2.3.4).
4. ![]() Set the cnnEouHostQueryStatus object to active.
Set the cnnEouHostQueryStatus object to active.
DETAILED STEPS

Note ![]() Examples are not shown in the previous table because the format differs depending on the software you are using.
Examples are not shown in the previous table because the format differs depending on the software you are using.
Viewing MIB Query Results
After the MIB query has been built, the results can be viewed in cnnEouHostResultTable. For information about how to review the results, see the subsection "Viewing MIB Query Results Correlating to the show eou all Command" section" for more information.
Splitting a Query into Subqueries
If you are doing a MIB query that correlates to the show eou all command, there could possibly be as many as 2,000 rows of output. To ensure that you can view all the information in a MIB query, you can split the query into subqueries. For example, for a query having 2,000 rows of output, you could split the query into four subqueries to view the results in a page-by-page format. The first subquery would include rows 1 through 500 (the first 500 sessions); the second subquery would include rows 501 through 1,000; the third subquery would include rows 1,001 through 1,500; and the fourth subquery would include rows 1,501 through 2,000.

Note ![]() The cnnEouHostQueryTotalHosts object provides the total number of hosts (number of rows) that match a query criterion. By looking at this number, you can determine how many subqueries are necessary. However, you cannot get the cnnEouHostQueryTotalHosts object number until you have built your first query.
The cnnEouHostQueryTotalHosts object provides the total number of hosts (number of rows) that match a query criterion. By looking at this number, you can determine how many subqueries are necessary. However, you cannot get the cnnEouHostQueryTotalHosts object number until you have built your first query.
Build your query by performing the following steps.
SUMMARY STEPS
1. ![]() Set the cnnEouHostQueryStatus object to createandgo.
Set the cnnEouHostQueryStatus object to createandgo.
2. ![]() Set the cnnEouHostQueryMask object to 8.
Set the cnnEouHostQueryMask object to 8.
3. ![]() Set cnnEouHostQueryRows to 500.
Set cnnEouHostQueryRows to 500.
4. ![]() Set cnnEouHostQuerySkipNHosts to 0.
Set cnnEouHostQuerySkipNHosts to 0.
5. ![]() Set the cnnEouHostQueryStatus object to active.
Set the cnnEouHostQueryStatus object to active.
DETAILED STEPS

Note ![]() Examples are not shown in the previous table because the format differs depending on the software you are using. The table is on the basis of a query having 2,000 sessions (rows).
Examples are not shown in the previous table because the format differs depending on the software you are using. The table is on the basis of a query having 2,000 sessions (rows).
What to Do Next
After the above task is performed, information for the first 500 hosts (rows) is queried. To view query information for the next 500 hosts (rows), perform the same five steps, with the exception of changing the cnnEouHostQuerySkipNHosts object value to 500 in Step 4. This task results in query information for rows 501 through 1000. In the same way, to obtain query information for the remaining hosts (through 2000), perform the same five steps again, with the exception of changing the cnnEouHostQuerySkipNHosts object values in Step 4 to 1000 and 1500, respectively.
Configuration Examples for Network Admission Control
This section includes the following example.
•![]() Network Admission Control: Example
Network Admission Control: Example
Network Admission Control: Example
The following output example shows that IP admission control has been configured on a Cisco IOS router:
Router# show running-config
Building configuration...
Current configuration: 1240 bytes
!
version 12.3
service timestamps debug datetime msec
service timestamps log datetime msec
no service password-encryption
!
hostname Router
!
boot-start-marker
boot-end-marker
!
aaa new-model
!
!
aaa authentication eou default group radius
aaa session-id common
ip subnet-zero
ip cef
!
! The following line creates a network admission rule. A list is not specified; therefore,
! the rule intercepts all traffic on the applied interface.
ip admission name avrule eapoudp
!
eou logging
!
!
interface FastEthernet0/0
ip address 10.13.11.106 255.255.255.0
duplex auto
speed auto
!
interface FastEthernet0/1
ip address 10.0.0.1 255.255.255.0
ip access-group 102 in
! The following line configures an IP admission control interface.
ip admission avrule
duplex auto
speed auto
!
ip http server
no ip http secure-server
ip classless
!
!
! The following lines configure an interface access list that allows EAPoUDP traffic
! and blocks the rest of the traffic until it is validated.
access-list 102 permit udp any any eq 21862
access-list 102 deny ip any any
!
!
! The following line configures RADIUS.
radius-server host 10.13.11.105 auth-port 1645 acct-port 1646 key cisco
!
control-plane
!
!
!
line con 0
exec-timeout 0 0
line aux 0
line vty 0 4
!
!
end
NAC MIB Output: Examples
The following are examples of show command output displaying MIB object information.
show eou
The show eou command provides output for information that can also be viewed in various CISCO-NAC-NAD-MIB tables. The information that follows the show eou command can also be found in the cnnEouGlobalObjectsGroup table and the information that follows the show eou all command can be found in the cnnEouIfConfigTable.
Router# show eou
Global EAPoUDP Configuration
----------------------------
EAPoUDP Version = 1
EAPoUDP Port = 0x5566
Clientless Hosts = Enabled
IP Station ID = Disabled
Revalidation = Enabled
Revalidation Period = 36000 Seconds
ReTransmit Period = 3 Seconds
StatusQuery Period = 300 Seconds
Hold Period = 30 Seconds
AAA Timeout = 60 Seconds
Max Retries = 3
EAP Rate Limit = 20
EAPoUDP Logging = Enabled
Clientless Host Username = clientless
Clientless Host Password = clientless
Router# show eou all
Interface Specific EAPoUDP Configurations
-----------------------------------------
Interface Vlan333
AAA Timeout = 60 Seconds
Max Retries = 3
eou initialize interface {interface-name}
eou revalidate interface {interface-name}
show ip device tracking all
The show ip device tracking all command provides output for information that can also be found in the cnnIpDeviceTrackingObjectsGroup MIB table. The following is an example of such show command output:
Router# show ip device tracking all
IP Device Tracking = Enabled
Probe Count: 2
Probe Interval: 10
Additional References
Related Documents
|
|
|
|---|---|
Configuring ACLs |
"IP Access List Overview" feature module. |
Authentication, authorization, and accounting |
"Authentication, Authorization, and Accounting" section of Cisco IOS Security Configuration Guide: Securing User Services, Release 12.4T. |
Interfaces, configuring |
Cisco IOS Configuration Fundamentals Configuration Guide, Release 12.4T. |
SNMP and SNMP get and set operations |
MIBs
|
|
|
|---|---|
None. |
To locate and download MIBs for selected platforms, Cisco IOS releases, and feature sets, use Cisco MIB Locator found at the following URL: |
Technical Assistance
Feature Information for Network Admission Control
Table 4 lists the release history for this feature.
Use Cisco Feature Navigator to find information about platform support and software image support. Cisco Feature Navigator enables you to determine which software images support a specific software release, feature set, or platform. To access Cisco Feature Navigator, go to http://www.cisco.com/go/cfn. An account on Cisco.com is not required.

Note ![]() Table 4 lists only the software release that introduced support for a given feature in a given software release train. Unless noted otherwise, subsequent releases of that software release train also support that feature.
Table 4 lists only the software release that introduced support for a given feature in a given software release train. Unless noted otherwise, subsequent releases of that software release train also support that feature.
|
|
|
|
|---|---|---|
Network Admission Control |
12.3(8)T |
The Network Admission Control feature addresses the increased threat and impact of worms and viruses to networked businesses. This feature is part of the Cisco Self-Defending Network Initiative that helps customers identify, prevent, and adapt to security threats. In its initial phase, the Cisco Network Admission Control functionality enables Cisco routers to enforce access privileges when an endpoint attempts to connect to a network. The following sections provide information about this feature: • • • • • The following commands were introduced or modified by this feature: aaa authentication eou default enable group radius, access-group (identity policy), auth-type, clear eou, clear ip admission cache, debug eap, debug eou, debug ip admission eapoudp, description (identity policy), description (identity profile), device (identity profile), eou allow, eou clientless, eou default, eou initialize, eou logging, eou max-retry, eou port, eou rate-limit, eou revalidate, eou timeout, identity policy, identity profile eapoudp, ip admission, ip admission name, redirect (identity policy), show eou, show ip admission, template (identity policy). |
NAC MIB |
12.4(15)T |
Support was added for the CISCO-NAC-NAD-MIB. This MIB module is used to monitor and configure the NAD on the Cisco NAC system. The following sections provide information about this feature: • The following commands were introduced or modified by this feature: show ip device tracking. |
12.2(33)SXI |
This feature was integrated into Cisco IOS Release 12.2(33)SXI. |
Glossary
default access policy—Set of ACLs that are applied to a client device until its credentials are validated by the AAA server.
EAPoUDP—Extensible Authentication Protocol over User Datagram Protocol. EAP is a framework that supports multiple, optional authentication mechanisms for PPP, including clear-text passwords, challenge-response, and arbitrary dialogue sequences. UDP is a connectionless transport layer protocol in the TCP/IP protocol stack. UDP is a simple protocol that exchanges datagrams without acknowledgments or guaranteed delivery, and it requires that error processing and retransmission be handled by other protocols. UDP is defined in RFC 768.
ip admission rule—Named rule that defines how IP admission control is applied. The IP admission rule is associated with an Intercept ACL and provides control over which hosts can use the IP admission feature. To create an IP admission control rule, use the ip admission name command.
posture token—Status that is used to convey the result of the evaluation of posture credentials. The AAA server maps the posture token (its status can be Healthy, Checkup, Quarantine, Infected, or Unknown) to a network access policy (ACL, URL, redirect, or status query timer) for the peer that the client wants to reach.
 Feedback
Feedback