Overview
Objective
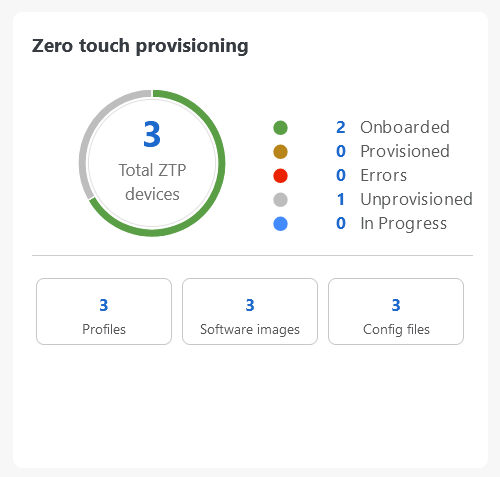
Allow users to quickly, easily, and automatically onboard new devices and provision them using a Cisco-certified software image and a day-zero software configuration.
Challenge
Deploying and configuring network devices is a tedious task. It requires extensive hands-on provisioning and configuration by knowledgeable personnel, which is time-consuming, expensive, and error-prone.
Solution
Automate onboarding of new devices using Crosswork Zero Touch Provisioning (Cisco Crosswork ZTP). Cisco Crosswork ZTP allows users to provision networking devices remotely without a trained specialist on site. After establishing an entry for the device in the DHCP server and the ZTP application, all the operators must connect the device to the network, power it on, and press reset to activate the devices. A certified image and configuration are downloaded and automatically applied to the device. After it is provisioned in this way, the new device is onboarded to the Crosswork device inventory, which can be monitored and managed like other devices.
How does it work?
-
Classic ZTP: The DHCP server verifies the device's identity based on its serial number and then offers to download the boot file and image. After the device is imaged, it downloads and executes the configuration file.
-
Secure ZTP: The device and the Cisco Crosswork ZTP bootstrap server authenticate each other using the device's Secure Unique Device Identifier (SUDI) and Crosswork server certificates over TLS/HTTPS. After a secure HTTPS channel is established, the Crosswork bootstrap server allows the device to request to download and apply a set of signed image and configuration artifacts adhering to the RFC 8572 YANG schema. After the image (if any) is downloaded and installed, and the device reloads with the new image, the device downloads configuration scripts and executes them.
-
Plug and Play (PnP) ZTP: The Cisco PnP agent on the IOS-XE device and the Cisco Crosswork PnP Server authenticate each other over HTTP using a PnP profile supplied on a TFTP server. They then establish a secure connection over HTTPS, and the PnP agent downloads and installs images (optional) and configuration artifacts.
Additional resources
Detailed information is available in the ZTP chapter in Cisco Crosswork Network Controller 7.0 Device Lifecycle Management.
 Feedback
Feedback