Basic Wireless LAN Connection Configuration Example
Available Languages
Contents
Introduction
This document provides a sample configuration that shows how to set up a basic wireless LAN (WLAN) connection with the use of a Cisco Aironet Access Point (AP) and computers with Cisco-compatible client adapters. The example uses the GUI.
Prerequisites
Requirements
Ensure that you meet these requirements before you attempt this configuration:
-
Familiarity with basic wireless radio frequency (RF) technology
-
Basic understanding of how to access a Cisco AP
This document assumes that the drivers of the wireless client cards for the PCs or laptops are already installed.
Components Used
The information in this document is based on these software and hardware versions:
-
One Aironet 1200 Series AP that runs Cisco IOS® Software Release 12.3(7)JA
-
Three Aironet 802.11a/b/g Client Adapters that run firmware 2.5
-
Aironet Desktop Utility (ADU) version 2.5
Note: This document uses an AP that has an integrated antenna. If you use an AP which requires an external antenna, ensure that the antennas are connected to the AP. Otherwise, the AP is unable to connect to the wireless network. Certain AP models come with integrated antennas, whereas others need an external antenna for general operation. For information on the AP models that come with internal or external antennas, refer to the ordering guide/product guide of the appropriate device.
The information in this document was created from the devices in a specific lab environment. All of the devices used in this document started with a cleared (default) configuration. If your network is live, make sure that you understand the potential impact of any command or setup in the GUI.
Network Diagram
This document uses this network setup:
The network diagram is three Aironet 802.11a/b/g Client Adapters that are connected to a 1200 AP. This document depicts the configuration of the client adapters to communicate with each other via wireless interface through the AP.
The AP uses these settings:
-
Service Set Identifier (SSID): CISCO123
-
Basic authentication: Open authentication with Wired Equivalent Privacy (WEP) encryption
This document explains the configuration on the AP and the client adapters.
Note: You can also use other authentication and encryption methods. For information on the different authentication mechanisms that are supported, refer to Configuring Authentication Types. For information on the different encryption mechanisms that are supported, refer to Configuring Cipher Suites and WEP.
Conventions
Refer to Cisco Technical Tips Conventions for more information on document conventions.
Configuration
Configure the Access Point
You can configure the AP with the use of any of these:
-
GUI
-
Command-line interface (CLI), after you establish a Telnet session
-
The console port
Note: In order to connect to the AP through the console port, connect a nine-pin, straight-through DB-9 serial cable to the RS-232 serial port on the AP and to the COM port on a computer. Set up a terminal emulator in order to communicate with the AP. Use these settings for the terminal emulator connection:
-
9600 baud
-
8 data bits
-
No parity
-
1 stop bit
-
No flow control
Note: These settings are the default settings. If you cannot access the device after you set the terminal program to the settings, the problem can be that the device is not set to the defaults. Try different settings, and start with the baud rate. For more information on the console cable specifications, refer to the Connecting to the 1200 and 1230AG Series Access Points Locally section of Configuring the Access Point for the First Time.
-
This document explains how to configure the AP with the use of the GUI.
There are two ways to access the AP with the use of the GUI:
-
Assign an IP address to the device before you connect through the GUI.
-
Obtain an IP address with the use of DHCP.
The different models of Aironet APs exhibit different default IP address behaviors. When you connect an Aironet 350, 1130AG, 1200, or 1240AG series AP with a default configuration to your LAN network, the AP requests an IP address from your DHCP server. If the AP does not receive an address, it continues to send requests indefinitely.
When you connect an Aironet 1100 series AP with a default configuration to your LAN, the AP makes several attempts to get an IP address from the DHCP server. If the AP does not receive an address, it assigns itself the IP address 10.0.0.1 for 5 minutes. During this 5-minute period, you can browse to the default IP address and configure a static address. If after the 5 minutes the AP is not reconfigured, the AP discards the 10.0.0.1 address and requests an address from the DHCP server. If the AP does not receive an address, it sends requests indefinitely. If you miss the 5-minute window to browse to the AP at 10.0.0.1, you can power cycle the AP in order to repeat the process.
The network in this document uses a 1200 series AP. A login through the console configures the AP with a static IP address of 10.0.0.1. For information on how to assign IP addresses to the AP, refer to the Obtaining and Assigning an IP Address section of Configuring the Access Point for the First Time.
Step-by-Step Instructions
After configuration of the IP address, you can access the AP through the browser in order to configure the AP to accept client association requests from the client adapter.
Complete these steps:
-
In order to access the AP with the GUI and get the Summary Status window, complete these steps:
-
Open a web browser and enter 10.0.0.1 in the address line.
-
Press Tab in order to bypass the Username field and advance to the Password field.
The Enter Network Password window displays.
-
Enter the case-sensitive password Cisco, and press Enter.
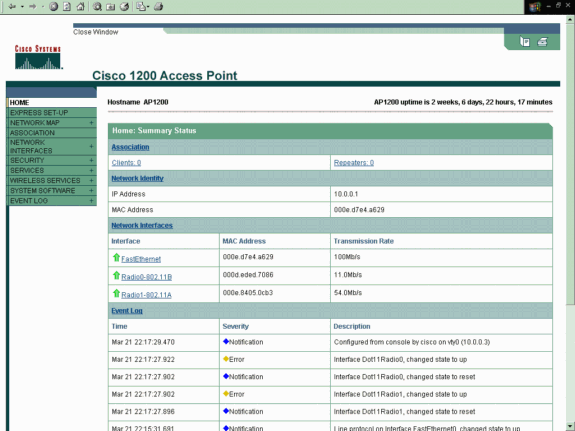
The Summary Status window displays, as this example shows:
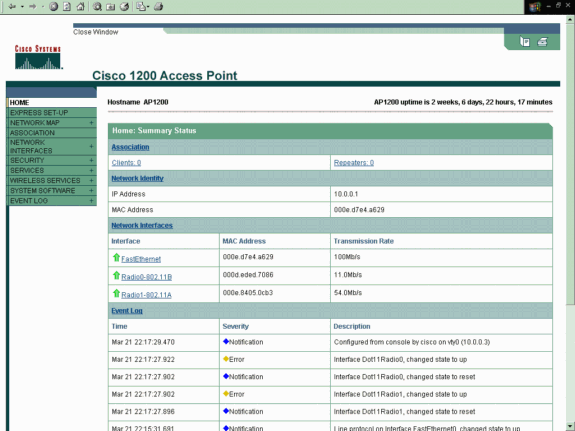
-
-
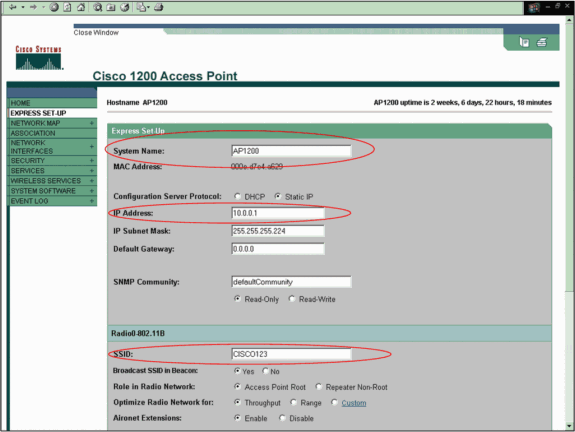
Click Express Setup in the menu on the left.
The Express Setup window displays. You can use this window to configure some of the basic parameters that are necessary to establish a wireless connection. Use the Express Setup window on the AP 1200 in order to configure the acceptance of wireless client associations. Here is an example of the window:
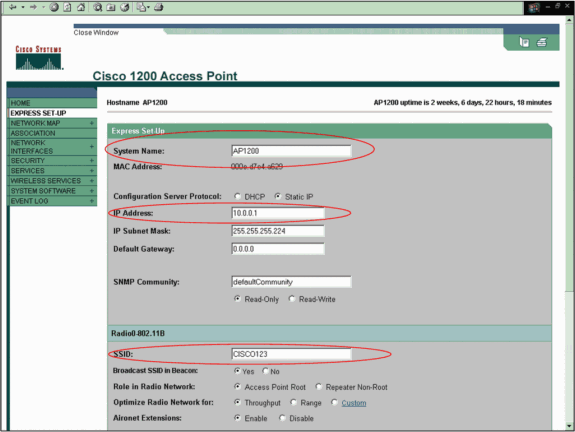
-
Enter the configuration parameters in the appropriate fields in the Express Setup window.
The configuration parameters include these parameters:
-
The host name of the AP
-
IP address configuration of the AP, if the address is a static IP
-
Default gateway
-
Simple Network Management Protocol (SNMP) community string
-
Role in the radio network
-
SSID
This example configures these parameters:
-
IP address: 10.0.0.1
-
Host name: AP1200
-
SSID: CISCO123
Note: SSIDs are unique identifiers that identify a WLAN network. Wireless devices use SSIDs to establish and maintain wireless connectivity. SSIDs are case-sensitive and can contain up to 32 alphanumeric characters. Do not use any spaces or special characters in an SSID.
Note: The other parameters are left with the default values.
-
-
Click Apply in order to save your settings.
-
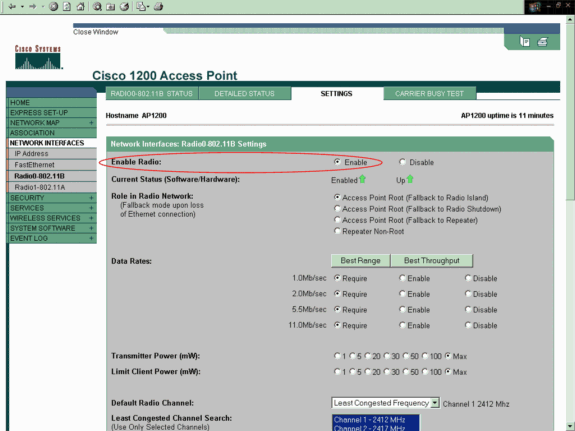
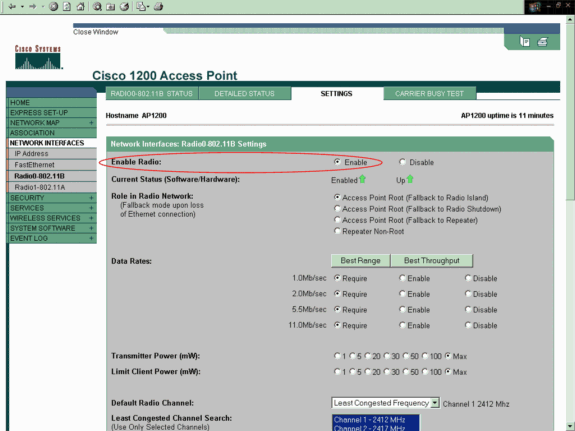
Complete these steps in order to set up the radio settings:
-
Click Network Interfaces in the menu on the left in order to browse to the Network Interfaces Summary page.
-
Select the radio interface that you want to use.
This example uses interface Radio0-802.11B. The action allows you to browse to the Network Interfaces: Radio Status page.
-
Click the Settings tab in order to browse to the Settings page for the radio interface.
-
Click Enable in order to enable the radio.
-
Leave all the other settings on the page with the default values.
-
Scroll down and click Apply at the bottom of the page in order to save the settings.
-
-
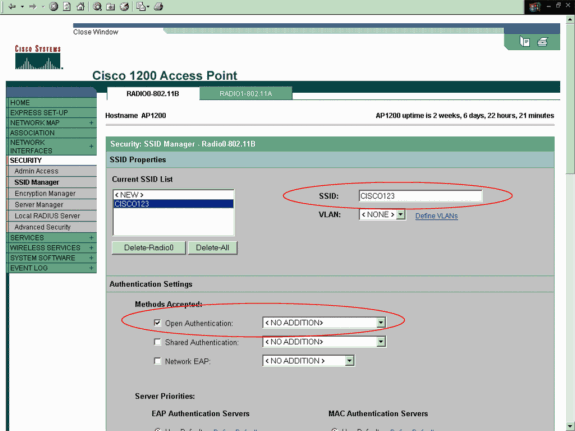
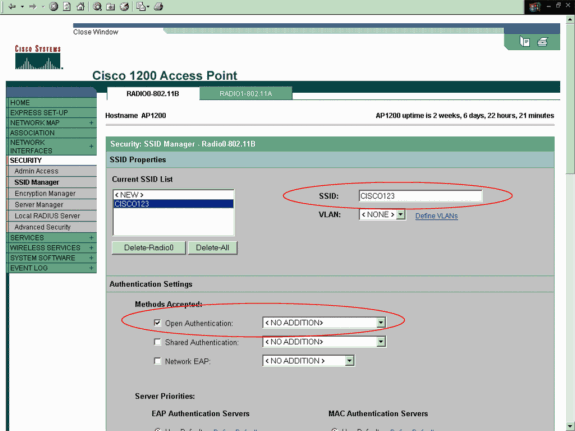
In order to configure the SSID and open authentication with WEP encryption, complete these steps:
-
Choose Security > SSID Manager in the menu on the left.
The SSID Manager page displays.
-
Select the SSID that you created in Step 3 from the Current SSID List menu.
This example uses CISCO123 as the SSID.
-
Under Authentication Settings, choose Open Authentication.
-
Leave all other parameters with their default values.
-
Click Apply at the bottom of the page.
-
-
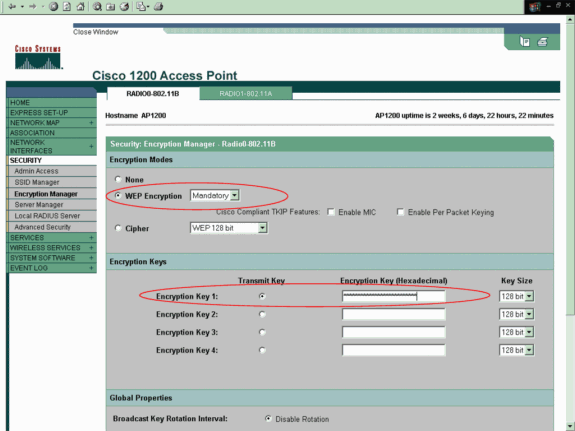
In order to configure the WEP keys, complete these steps:
-
Choose Security > Encryption Manager.
-
Click WEP Encryption under Encryption Modes, and choose Mandatory from the drop-down menu.
-
Enter the encryption key for WEP in the Encryption Keys area.
The WEP encryption keys can be 40 bits or 128 bits in length. This example uses the 128-bit WEP encryption key 1234567890abcdef1234567890.
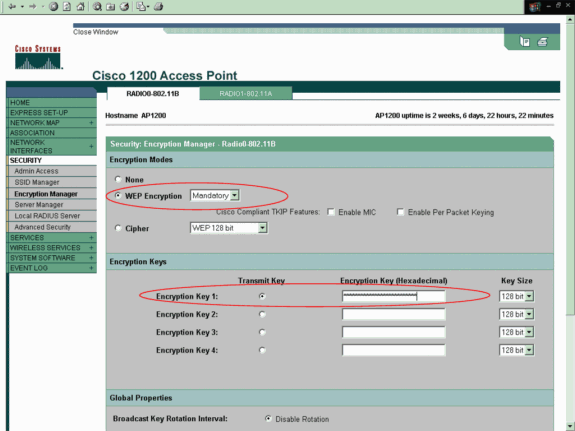
-
Click Apply in order to save the settings.
-
Configure the Wireless Client Adapter
Before configuration of the client adapter, you must install the client adapter and client adapter software components on the PC or laptop. For instructions on how to install the drivers and utilities for the client adapter, refer to Installing the Client Adapter.
Step-by-Step Instructions
After installation of the client adapter on the machine, you can configure it. This section explains how to configure the client adapter.
Complete these steps:
-
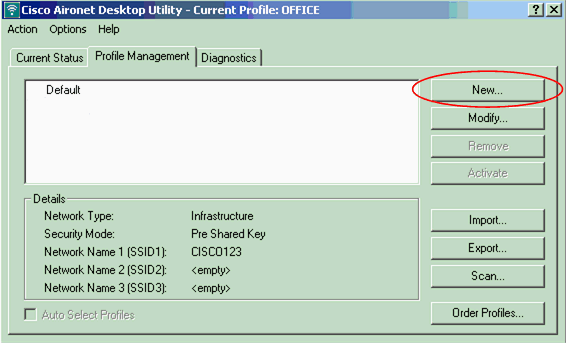
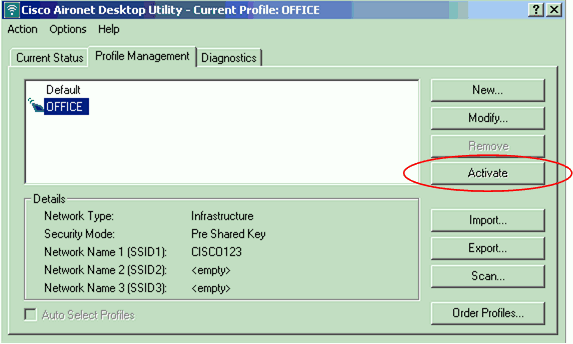
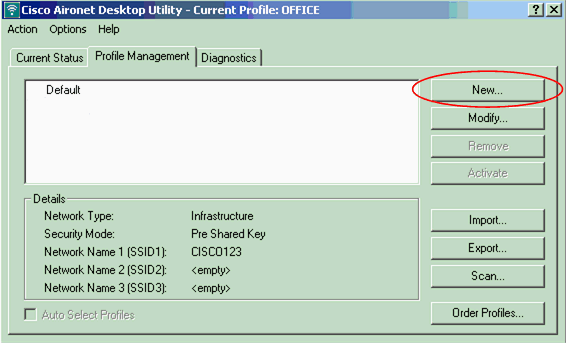
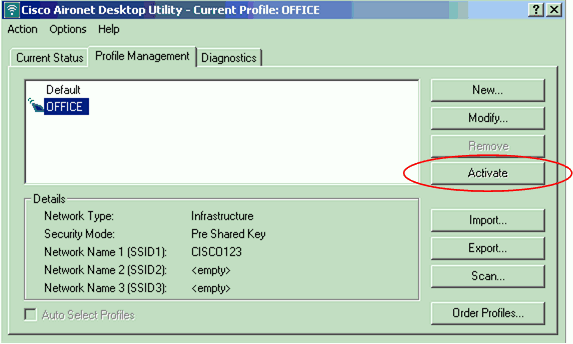
Create a profile on the ADU for the client adapter.
The profile defines the configuration settings that the client adapter uses in order to connect to the wireless network. You can configure a maximum of 16 different profiles on the ADU. You can switch between the different configured profiles on the basis of your requirement. Profiles enable you to use your client adapter in different locations, each of which requires different configuration settings. For example, you may want to set up profiles to use your client adapter at the office, at home, and in public areas, such as airports or hot spots.
In order to create a new profile, complete these steps:
-
Click the Profile Management tab on the ADU.
-
Click New.
Here is an example:
-
-
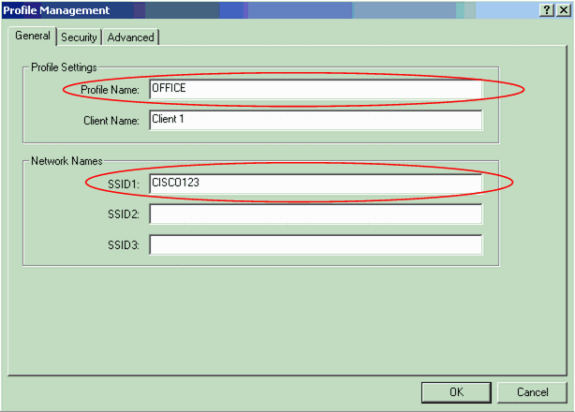
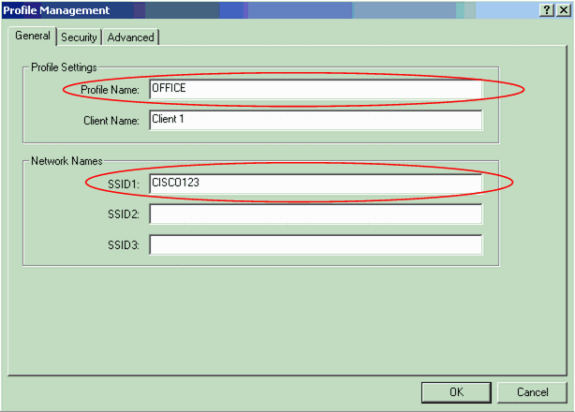
When the Profile Management (General) window displays, complete these steps in order to set the Profile Name, Client Name, and SSID:
-
Enter the name of the profile in the Profile Name field.
This example uses OFFICE as the Profile Name.
-
Enter the name of the client in the Client Name field.
The client name is used to identify the wireless client in the WLAN network. This configuration uses the name Client 1 for the first client.
-
Under Network Names, enter the SSID that is to be used for this Profile.
The SSID is the same as the SSID that you configured in the AP. The SSID in this example is CISCO123.
-
-
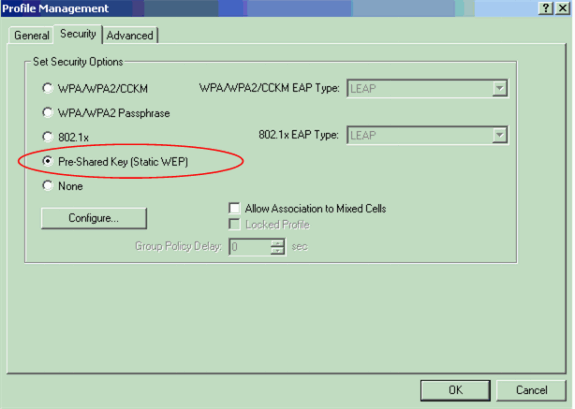
Complete these steps in order to set up the Security Options:
-
Click the Security tab at the top of the window.
-
Click Pre-Shared Key (Static WEP) under Set Security Options.
Here is an example:
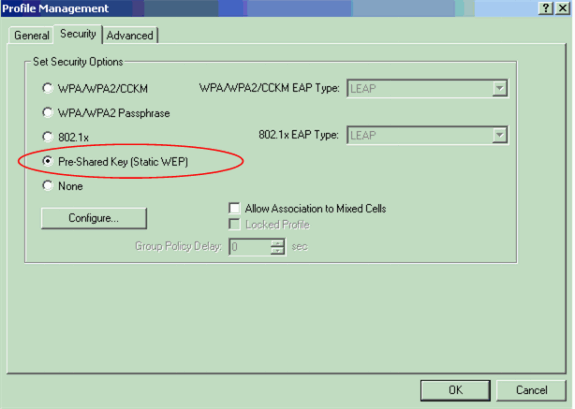
-
Click Configure.
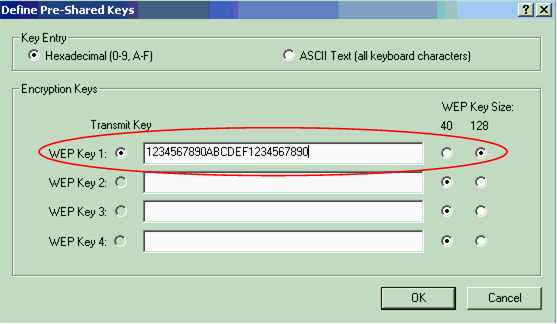
The Define Pre-Shared Keys window appears.
-
Click one of buttons in the Key Entry area in order to choose a key entry type.
This example uses Hexadecimal (0-9, A-F).
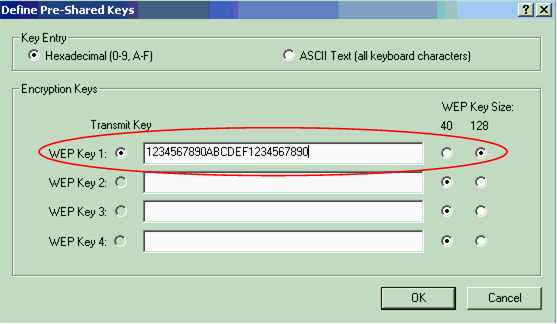
-
Under Encryption Keys, enter the WEP key that is to be used for encryption of the data packets.
This example uses the WEP key 1234567890abcdef1234567890. See the example in Step d.
Note: Use the same WEP key as the one you configured in the AP.
-
-
Click OK in order to save the WEP key.
-
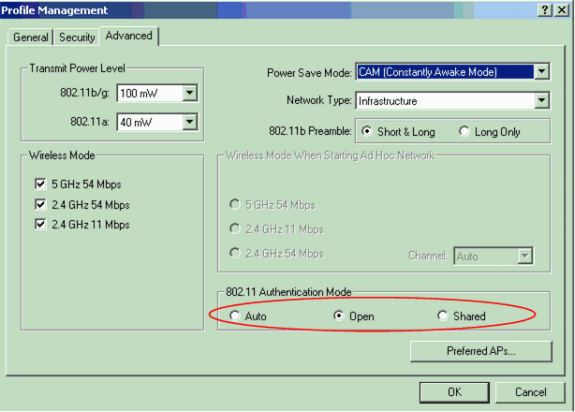
Complete these steps in order to set the authentication method to Open:
-
Click the Advanced tab at the top of the Profile Management window.
-
Be sure that Open is selected under 802.11 Authentication Mode.
Note: Open authentication is usually enabled by default.
-
Leave all the other settings with the default values.
-
Click OK.
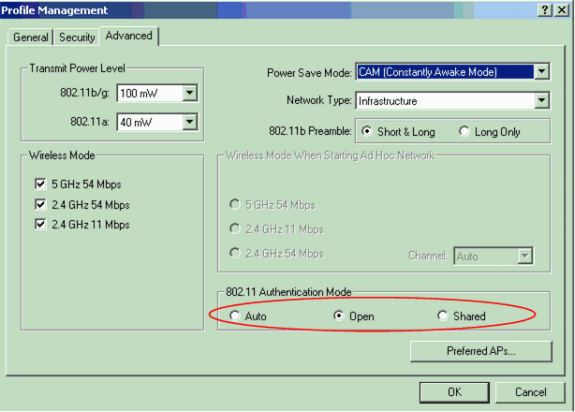
-
-
Click Activate in order to enable this profile.
Note: You can use these same Step-by-Step Instructions in order to create a completely new profile. In an alternate method to create a profile, the client adapter scans the RF environment in order to check for available networks and then creates a profile on the basis of the scan results. For more information on this method, refer to the Creating a New Profile section of Using the Profile Manager.
You can use the same procedure in order to configure the other two client adapters. You can use the same SSID on the other adapters. The only difference is the client name and the IP address that is statically given to the adapter.
Note: This example assumes that the client adapter IP address is configured manually and is in the same subnetwork as the AP.
Verify
This section explains how to confirm that your configuration works properly.
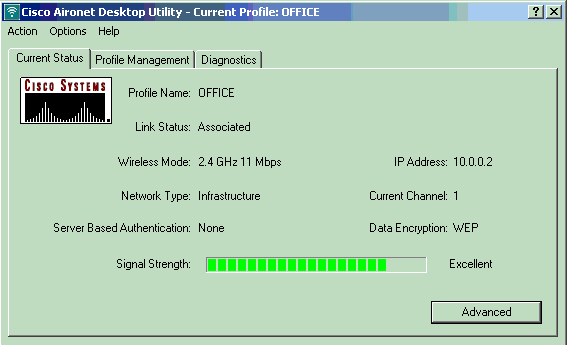
When you have completed the configurations and activated the profile, the client adapter connects to the AP. In order to check the status of the client connection, click the Current Status tab at the top of the ADU window.
This example illustrates a successful connection to the AP. You can see that the client uses Channel 1 for communication and uses WEP for encryption. Also, since only open authentication is used, the Server Based Authentication field shows None:
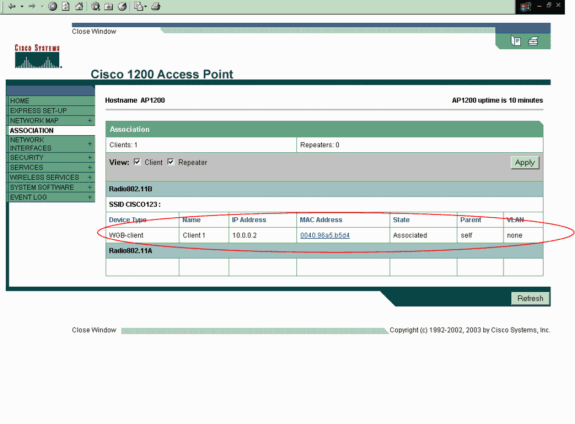
As another method to verify the client connection on the AP, click Association in the menu on the left side of the AP home page. Here is an example:
Troubleshoot
If 802.1x authentication is used, and a Cisco Catalyst 2950 or 3750 Switch is present in the network, an 802.1X client might fail to authenticate. This error message is displayed:
Jul 21 14:14:52.782 EDT: %RADIUS-3-ALLDEADSERVER: Group rad_eap: No active radius servers found. Id 254
This symptom is observed on 2950 and 3750 Switches when the RADIUS State(24) Field values change in between the Access Challenge and the Access Request. This is because of Cisco bug id CSCef50742. This is resolved in Cisco IOS Software Release 12.3(4) JA. With release 12.3(4)JA, clients no longer fail 802.1X authentication through Cisco Catalyst 2950 and 3750 Switches due to State (24) Field values that change.
Related Information
- Cisco IOS Software Configuration Guide for Cisco Aironet Access Points 12.3(7)JA
- Cisco Aironet 802.11a/b/g Wireless LAN Client Adapters (CB21AG and PI21AG) Installation and Configuration Guide, OL-4211-04
- Configuring the Access Point for the First Time
- Wireless Support Page
- Technical Support & Documentation - Cisco Systems
Revision History
| Revision | Publish Date | Comments |
|---|---|---|
1.0 |
28-Oct-2005
|
Initial Release |
Contact Cisco
- Open a Support Case

- (Requires a Cisco Service Contract)
 Feedback
Feedback