Cisco IP Phone 7941/7961/7970 Inserts VLAN tags (802.1q header) on Ingress Packets from PC Port
Available Languages
Contents
Introduction
A Cisco IP Phone 7941/7961/7970 can insert VLAN tags (802.1q header) on ingress packets from the PC port when the PC voice VLAN access setting is set to disable. The behavior outlined in this document might interrupt network service to a host connected to the PC port of a phone if the access-VLAN on a switch port is changed at any time for any reason.
Prerequisites
Requirements
Cisco recommends that you have knowledge of these topics:
-
Configuring InterVLAN Routing, Understanding How InterVLAN Routing Works
-
Inter-Switch Link and IEEE 802.1Q Frame Format IEEE 802.1Q Frame
-
Cisco Unified IP Phone Administration Guide for Cisco Unified CallManager 5.1 (SCCP), Cisco Unified IP Phones 7961G/7961G-GE and 7941G/7941G-GE Security Configuration Menu
-
Cisco Unified IP Phone 7970G/7971G-GE Administration Guide for Cisco Unified CallManager 6.0 (SCCP and SIP) Security Configuration Menu
Components Used
This document is not restricted to specific software.
The information in this document is restricted to these Cisco IP Phone model types:
-
Cisco IP Phone 7941, 7961, 7970
The information in this document was created from the devices in a specific lab environment. All of the devices used in this document started with a cleared (default) configuration. If your network is live, make sure that you understand the potential impact of any command.
Conventions
Refer to Cisco Technical Tips Conventions for more information on document conventions.
Background Information
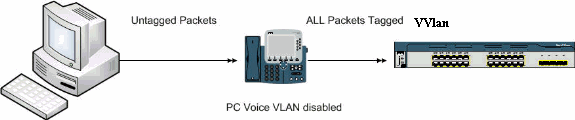
The particular built-in switch architecture of the phone model types listed in this document will cause the phone to insert the Voice VLAN tags in untagged ingress packets with the Voice VLAN.1q header when the phone is set to PC access voice VLAN disabled to avoid VLAN hopping. See this diagram:
Although this document makes reference to 7971 documentation, this is not affected by this behavior.
Solution
This section describes the solution to this problem.
Solution 1
Complete these steps:
-
Navigate to the Cisco Unified Communications Manager (formerly CallManager) Admin page, select device > phone and locate the phone in question.
-
Set the PC Voice VLAN access parameter to enabled.
The implication of doing this means that a PC has the ability to dot1q-tag traffic equivalent to the Voice-VLAN on the switch in an effort to launch an attack. It is recommended to employ the use of authentication in such circumstances, for example, Multi-Domain-Authentication on Cisco Catalyst switches.
Related Information
- Understanding How InterVLAN Routing Works
- IEEE 802.1Q Frame
- Cisco Unified IP Phone Administration Guide for Cisco Unified CallManager 5.1 (SCCP), Cisco Unified IP Phones 7961G/7961G-GE and 7941G/7941G-GE - Security Configuration Menu
- Cisco Unified IP Phone 7970G/7971G-GE Administration Guide for Cisco Unified CallManager 6.0 (SCCP and SIP) - Security Configuration Menu
- Voice Technology Support
- Voice and Unified Communications Product Support
- Troubleshooting Cisco IP Telephony

- Technical Support & Documentation - Cisco Systems
Revision History
| Revision | Publish Date | Comments |
|---|---|---|
1.0 |
11-Apr-2008
|
Initial Release |
Contact Cisco
- Open a Support Case

- (Requires a Cisco Service Contract)
 Feedback
Feedback