Configure Virtual Local Area Network (VLAN) Interface Settings on an Sx350, SG350X, or Sx550X Switch
Available Languages
Objective
A Virtual Local Area Network (VLAN) allows you to logically segment a Local Area Network (LAN) into different broadcast domains. In scenarios where sensitive data may be broadcast on a network, VLANs can be created to enhance security by designating a broadcast to a specific VLAN. Only users that belong to a VLAN are able to access and manipulate the data on that VLAN. VLANs can also be used to enhance performance by reducing the need to send broadcasts and multicasts to unnecessary destinations.
You can create a VLAN, but this has no effect until the VLAN is attached to at least one port, either manually or dynamically. Ports must always belong to one or more VLANs.
Each VLAN must be configured with a unique VLAN ID (VID) with a value from 1 to 4094. The device reserves VID 4095 as the Discard VLAN. All packets classified to the Discard VLAN are discarded at ingress, and are not forwarded to a port.
This article provides instructions on how to configure VLAN interface settings on an Sx350, SG350X, or SG550X Series Switch.
Applicable Devices
- Sx350 Series
- SG350X Series
- Sx550X Series
Software Version
- 2.2.5.68
Configure VLAN Interface Settings on a Switch
Important: Before proceeding with the steps below, make sure VLANs have been configured on the switch. To know how to configure VLAN settings on your switch, click here for instructions.
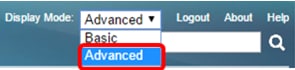
Step 1. Log in to the web-based utility and choose Advanced from the Display Mode drop-down list.
Step 2. Choose VLAN Management >Interface Settings.
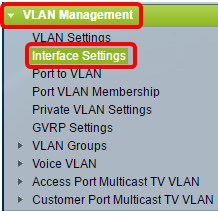
Note: The available menu options may vary depending on the switch that you have. In this example, SG350X switch is used.
Step 3. Choose an interface from the Interface Type drop-down list.
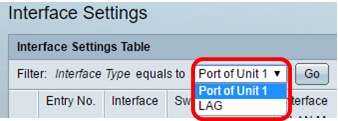
- Port — From the Interface Type drop-down list, choose Port if only a single port needs to be chosen.
- LAG — From the Interface Type drop down list, choose the LAG to configure. This affects the group of ports defined in the LAG configuration.
Note: In this example, Port of Unit 1 is chosen.
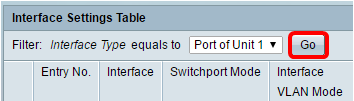
Step 4. Click Go to bring up a list of ports or LAGs on the interface.
Step 5. Click the radio button for the port or LAG you want to modify.
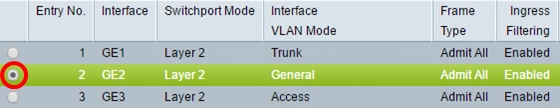
Note: In this example, GE2 is chosen.
Step 6. Scroll down the page then click Edit.
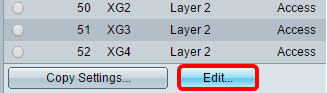
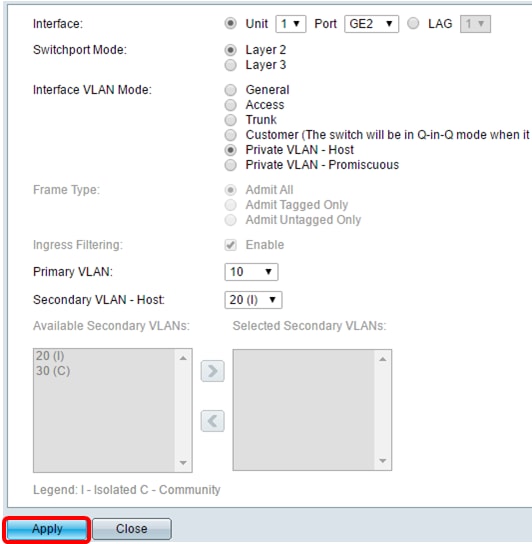
Step 7. (Optional) Click the radio button that corresponds to the desired Interface.
- Port — From the Unit drop-down list, choose the port to configure. This affects the single port chosen.
- LAG — From the LAG drop down list, choose the LAG to configure. This affects the group of ports defined in the LAG configuration.
Note: In this example, port GE2 of Unit 1 is chosen.
Step 8. Click the radio button of your preferred Switchport Mode.

- Layer 2 — The data link layer which contains the protocols that control the physical layer (Layer 1) and how data is framed before being transmitted on the medium. The Layer 2 function of filtering and forwarding data in frames between two segments on a LAN is known as bridging.
- Layer 3 — The network layer is primarily responsible for the routing of data in packets across logical internetwork paths. The logical Layer 3 VLAN interfaces integrate the functions of routing and bridging.
Note: In this example, Layer 2 is chosen.
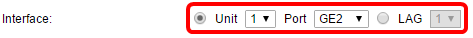
Step 9. Click the radio button that corresponds to the desired VLAN mode for the interface.
- General — The interface can be a tagged or untagged member of one or more VLANs.
- Access — The interface is an untagged member of a single VLAN. If this option is chosen, skip to Step 15.
- Trunk — The interface is an untagged member of at most one VLAN and is a tagged member of one or more VLANs. If this option is chosen, skip to Step 15.
- Customer — The interface is in Q-in-Q mode. This enables the link partner to use their own VLAN arrangements across the provider network. If this option is chosen, skip to Step 15.
- Private VLAN – Host — This option sets the interface as either isolated or community. You can then choose either an isolated or community VLAN in the Secondary VLAN - Host area.
- Private VLAN – Promiscuous — This option sets the interface as promiscuous.
Note: In this example, Private VLAN – Host is chosen.
Step 10. (Optional) Click the radio button that corresponds to the desired frame type that the interface can receive. Frames that are not this frame type are discarded at ingress.

- Admit All — The interface accepts all types of frames (untagged, tagged, and priority tagged frames).
- Admit Tagged Only — The interface accepts only tagged frames.
- Admit Untagged Only — The interface accepts only untagged and priority tagged frames.
Note: In this example, Admit Tagged Only is clicked.
Step 11. (Optional) Check Enable to enable ingress filtering on the interface. When ingress filtering is enabled, the interface discards all incoming frames that are classified as VLANs of which the interface is not a member.

Note: Ingress filtering is always enabled on access ports and trunk ports.
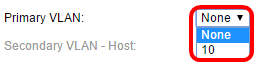
Step 12. (Optional) Choose the primary VLAN from the Primary VLAN drop-down list. The primary VLAN is used to allow Layer 2 connectivity from promiscuous ports to isolated ports and to community ports.
Note: Alternatively, you can choose None if the interface is not in private VLAN mode. If None is chosen, skip to Step 15.
Step 13. (Optional) Choose an isolated or community VLAN for those hosts that only require a single secondary VLAN.
Note: The Secondary VLAN – Host drop-down list is only available if Private VLAN – Host is clicked in Step 9.

Note: In this example, VLAN 20 (I) is chosen.
Step 14. (Optional) For promiscuous ports, choose all secondary VLANs that are required for normal packet forwarding from the Available Secondary VLANs then click the > button. Promiscuous and trunk ports can be members in multiple VLANs.
Note: These areas are only available if Private VLAN – Promiscuous is clicked in Step 9.

Note: In this example, VLAN 20 (I) is moved to the Selected Secondary VLANs area.
Step 15. Click Apply then click Close.
Step 16. (Optional) Click Save to save settings to the startup configuration file.
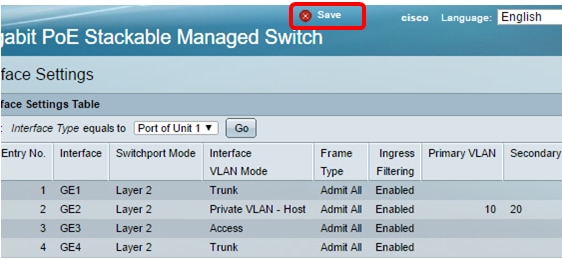
You should now have configured the VLAN interface settings on your Sx350, SG350X, or Sx550X Series Switch.
 Feedback
Feedback