|
Log File Type |
Description |
Supports Syslog Push? |
Enabled by Default? |
|---|---|---|---|
|
Access Control Engine Logs |
Records messages related to the Web Proxy ACL (access control list) evaluation engine. |
No |
No |
|
Secure EndpointEngine Logs |
Records information about file reputation scanning and file analysis (Secure Endpoint.) |
Yes |
Yes |
|
Audit Logs |
Records AAA (Authentication, Authorization, and Accounting) events. Records all user interaction with the application and command-line interfaces, and captures committed changes. Some of the audit log details are as follows:
|
Yes |
Yes |
|
Access Logs |
Records Web Proxy client history. |
Yes |
Yes |
|
ADC Engine Framework Logs |
Records messages related to communication between the Web Proxy and the ADC engine. |
No |
No |
|
ADC Engine Logs |
Records debug messages from the ADC engine. |
Yes |
Yes |
|
Authentication Framework Logs |
Records authentication history and messages. |
No |
Yes |
|
AVC Engine Framework Logs |
Records messages related to communication between the Web Proxy and the AVC engine. |
No |
No |
|
AVC Engine Logs |
Records debug messages from the AVC engine. |
Yes |
Yes |
|
CLI Audit Logs |
Records a historical audit of command line interface activity. |
Yes |
Yes |
|
Configuration Logs |
Records messages related to the Web Proxy configuration management system. |
No |
No |
|
Connection Management Logs |
Records messages related to the Web Proxy connection management system. |
No |
No |
|
Data Security Logs |
Records client history for upload requests that are evaluated by the Cisco Data Security Filters. |
Yes |
Yes |
|
Data Security Module Logs |
Records messages related to the Cisco Data Security Filters. |
No |
No |
|
DCA Engine Framework Logs (Dynamic Content Analysis) |
Records messages related to communication between the Web Proxy and the Cisco Web Usage Controls Dynamic Content Analysis engine. |
No |
No |
|
DCA Engine Logs (Dynamic Content Analysis) |
Records messages related to the Cisco Web Usage Controls Dynamic Content Analysis engine. |
Yes |
Yes |
|
Default Proxy Logs |
Records errors related to the Web Proxy. This is the most basic of all Web Proxy related logs. To troubleshoot more specific aspects related to the Web Proxy, create a log subscription for the applicable Web Proxy module. |
Yes |
Yes |
|
Disk Manager Logs |
Records Web Proxy messages related to writing to the cache on disk. |
No |
No |
|
External Authentication Logs |
Records messages related to using the external authentication feature, such as communication success or failure with the external authentication server. Even with external authentication is disabled, this log contains messages about local users successfully or failing logging in. |
No |
Yes |
|
Feedback Logs |
Records the web users reporting misclassified pages. |
Yes |
Yes |
|
FTP Proxy Logs |
Records error and warning messages related to the FTP Proxy. |
No |
No |
|
FTP Server Logs |
Records all files uploaded to and downloaded from theSecure Web Applianceusing FTP. |
Yes |
Yes |
|
GUI Logs (Graphical User Interface) |
Records history of page refreshes in the web interface. GUI logs also include information about SMTP transactions, for example information about scheduled reports emailed from the appliance. |
Yes |
Yes |
|
Haystack Logs |
Haystack logs record web transaction tracking data processing. |
Yes |
Yes |
|
HTTPS Logs |
Records Web Proxy messages specific to the HTTPS Proxy (when the HTTPS Proxy is enabled). |
No |
No |
|
ISE Server Logs |
Records ISE server(s) connection and operational information. |
Yes |
Yes |
|
License Module Logs |
Records messages related to the Web Proxy’s license and feature key handling system. |
No |
No |
|
Logging Framework Logs |
Records messages related to the Web Proxy’s logging system. |
No |
No |
|
Logging Logs |
Records errors related to log management. |
Yes |
Yes |
|
McAfee Integration Framework Logs |
Records messages related to communication between the Web Proxy and the McAfee scanning engine. |
No |
No |
|
McAfee Logs |
Records the status of anti-malware scanning activity from the McAfee scanning engine. |
Yes |
Yes |
|
Memory Manager Logs |
Records Web Proxy messages related to managing all memory including the in-memory cache for the Web Proxy process. |
No |
No |
|
Miscellaneous Proxy Modules Logs |
Records Web Proxy messages that are mostly used by developers or customer support. |
No |
No |
|
AnyConnect Secure Mobility Daemon Logs |
Records the interaction between theSecure Web Applianceand the AnyConnect client, including the status check. |
Yes |
Yes |
|
NTP Logs (Network Time Protocol) |
Records changes to the system time made by the Network Time Protocol. |
Yes |
Yes |
|
PAC File Hosting Daemon Logs |
Records proxy auto-config (PAC) file usage by clients. |
Yes |
Yes |
|
Proxy Bypass Logs |
Records transactions that bypass the Web Proxy. |
No |
Yes |
|
Reporting Logs |
Records a history of report generation. |
Yes |
Yes |
|
Reporting Query Logs |
Records errors related to report generation. |
Yes |
Yes |
|
Request Debug Logs |
Records very detailed debug information on a specific HTTP transaction from all Web Proxy module log types. It is advisable to create this log subscription to troubleshoot a proxy issue with a particular transaction without creating all other proxy log subscriptions. Note:You can create this log subscription in the CLI only. |
No |
No |
|
Auth Logs |
Records messages related to the Access Control feature. |
Yes |
Yes |
|
SHD Logs (System Health Daemon) |
Records a history of the health of system services and a history of unexpected daemon restarts. |
Yes |
Yes |
|
SNMP Logs |
Records debug messages related to the SNMP network management engine. |
Yes |
Yes |
|
SNMP Module Logs |
Records Web Proxy messages related to interacting with the SNMP monitoring system. |
No |
No |
|
Sophos Integration Framework Logs |
Records messages related to communication between the Web Proxy and the Sophos scanning engine. |
No |
No |
|
Sophos Logs |
Records the status of anti-malware scanning activity from the Sophos scanning engine. |
Yes |
Yes |
|
Status Logs |
Records information related to the system, such as feature key downloads. |
Yes |
Yes |
|
System Logs |
Records DNS, error, and commit activity. |
Yes |
Yes |
|
Traffic Monitor Error Logs |
Records L4TM interface and capture errors. |
Yes |
Yes |
|
Traffic Monitor Logs |
Records sites added to the L4TM block and allow lists. |
No |
Yes |
|
UDS Logs (User Discovery Service) |
Records data about how the Web Proxy discovers the user name without doing actual authentication. It includes information about interacting with the Cisco adaptive security appliance for the Secure Mobility as well as integrating with the Novell eDirectory server for transparent user identification. |
Yes |
Yes |
|
Updater Logs |
Records a history of WBRS and other updates. |
Yes |
Yes |
|
W3C Logs |
Records Web Proxy client history in a W3C compliant format. For more information. |
Yes |
No |
|
WBNP Logs (SensorBase Network Participation) |
Records a history of Cisco SensorBase Network participation uploads to the SensorBase network. |
No |
Yes |
|
WBRS Framework Logs (Web Reputation Score) |
Records messages related to communication between the Web Proxy and the Web Reputation Filters. |
No |
No |
|
WCCP Module Logs |
Records Web Proxy messages related to implementing WCCP. |
No |
No |
|
Webcat Integration Framework Logs |
Records messages related to communication between the Web Proxy and the URL filtering engine associated with Cisco Web Usage Controls. |
No |
No |
|
Webroot Integration Framework Logs |
Records messages related to communication between the Web Proxy and the Webroot scanning engine. |
No |
No |
|
Webroot Logs |
Records the status of anti-malware scanning activity from the Webroot scanning engine. |
Yes |
Yes |
|
Welcome Page Acknowledgement Logs |
Records a history of web clients who click the Accept button on the end-user acknowledgement page. |
Yes |
Yes |
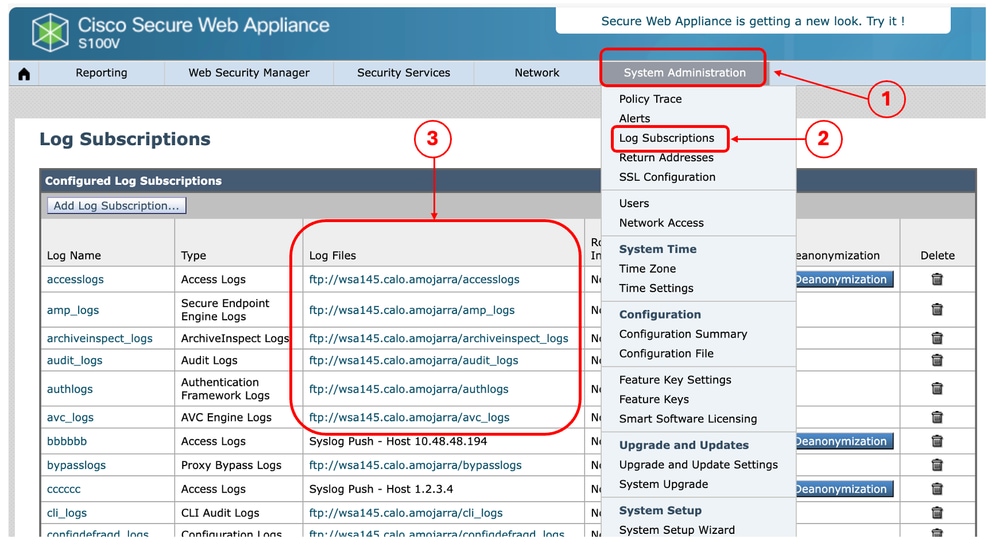
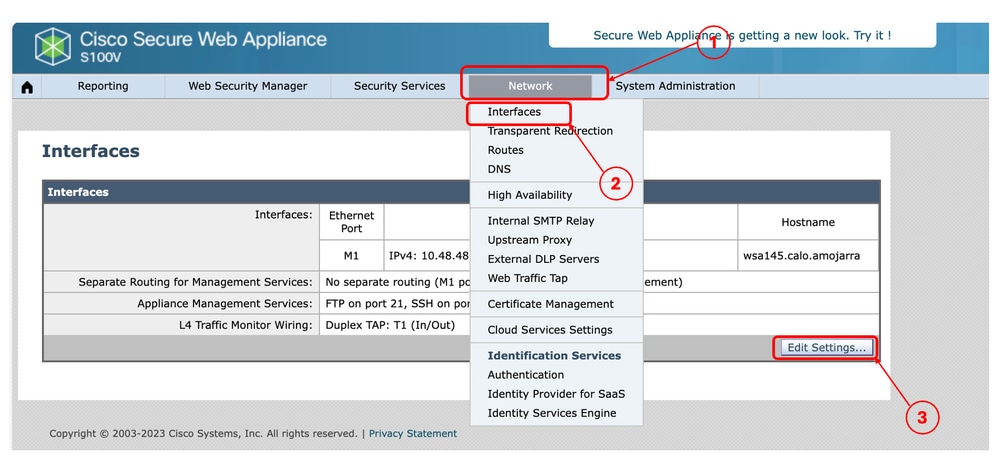
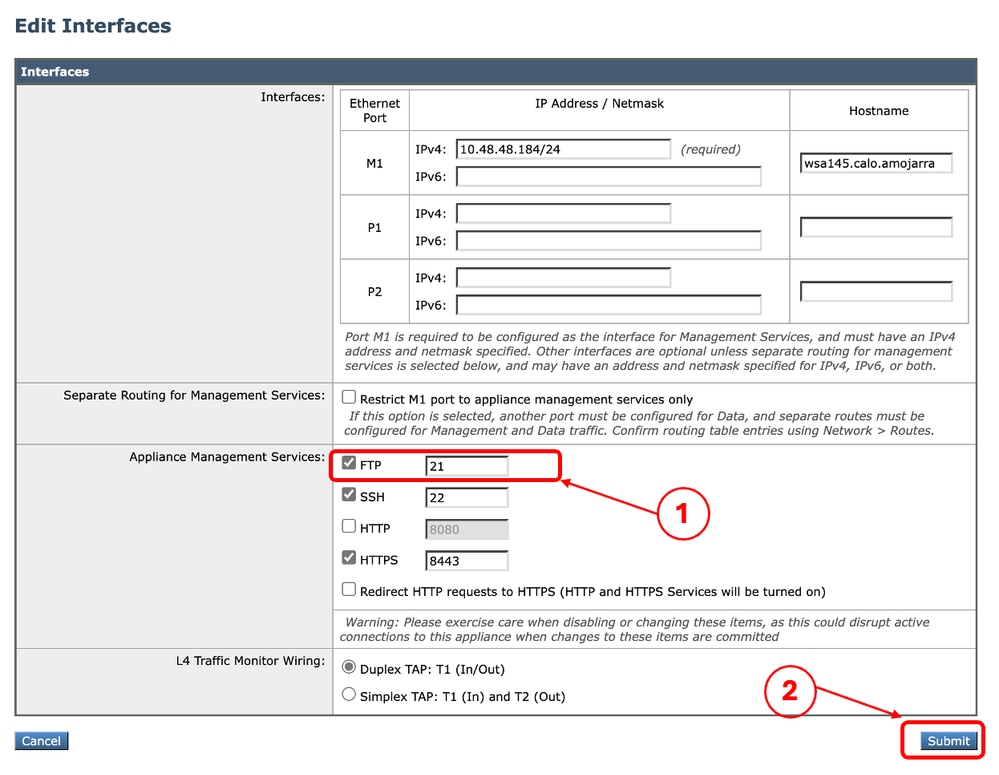
Access Secure Web Appliance Logs
Available Languages
Revision History
| Revision | Publish Date | Comments |
|---|---|---|
1.0 |
08-May-2024
|
Initial Release |
Contact Cisco
- Open a Support Case

- (Requires a Cisco Service Contract)


 Feedback
Feedback