Disable Proxy ARP on FTD Interfaces Using FlexConfig
Available Languages
Issue
Hosts on an FTD interface are unable to use statically assigned IP addresses and report "duplicate IP address" errors before falling back to 169.254.x.x addresses. Packet capture analysis reveals that when the host sends a gratuitous ARP (ARP probe) for its own IP address, the firewall responds claiming ownership of that IP address, preventing successful static IP assignment.
Environment
- Cisco Secure Firewall 2120 running FTD software version 7.4.4 (applicable to all versions and models)
- Cisco Secure Firewall Management Center (FMC) for device management
- Proxy ARP enabled on FTD by default.
Resolution
The issue is resolved by disabling Proxy ARP on the affected interface using a FlexConfig policy deployed through FMC. This prevents the firewall from responding to ARP probes for IP addresses it does not explicitly own.
1: Navigate to the FlexConfig section in FMC and create a new FlexConfig policy to disable Proxy ARP on the specific interface. The Sysopt_noproxyarp and the negating Sysopt_noproxyarp_negate are default objects in the FMC and can be cloned for custom use.
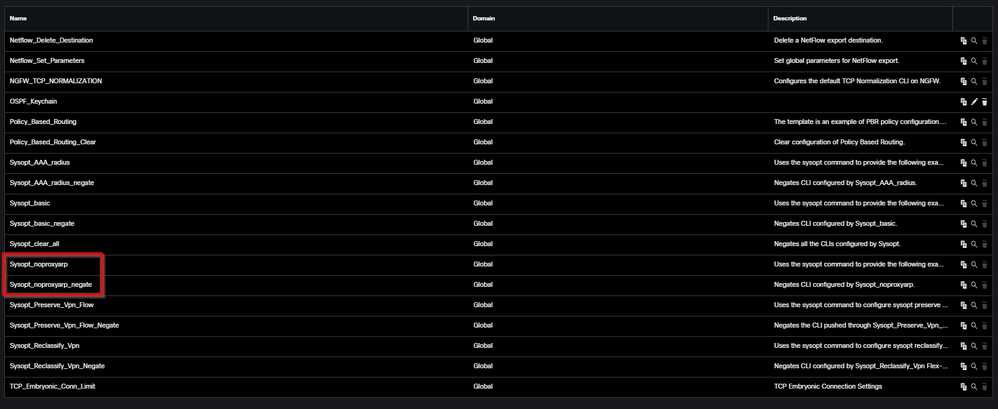 inline_image_0.png
inline_image_0.png2: Add the configuration command to the FlexConfig policy sysopt noproxyarp IFNAME:
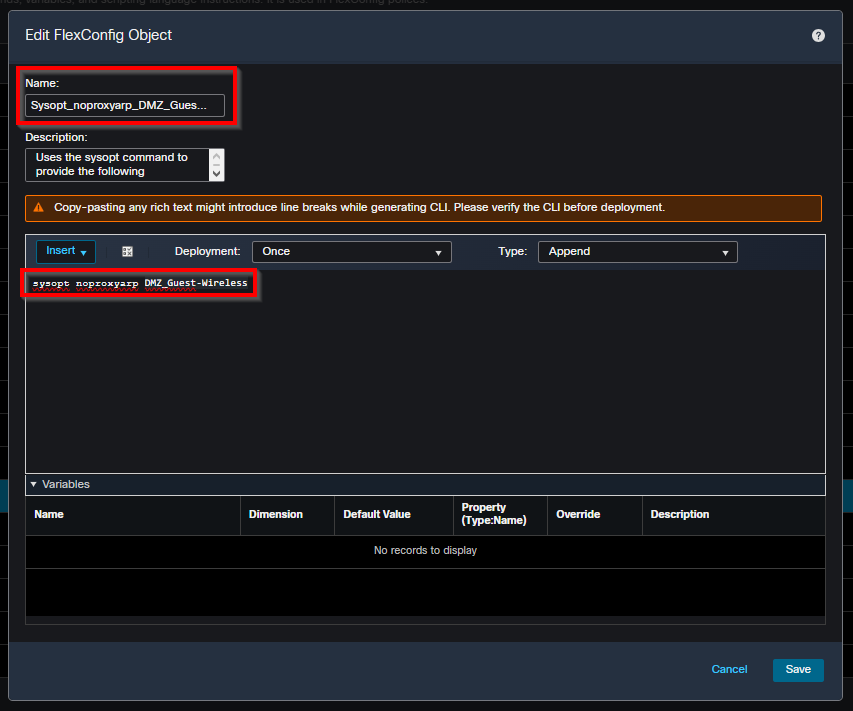 inline_image_1.png
inline_image_1.pngReplace IFNAME with the actual name of your affected interface.
3: Associate the new object to the FlexConfig policy of the FTD and deploy it through FMC. The configuration is applied to disable Proxy ARP behavior on the specified interface.
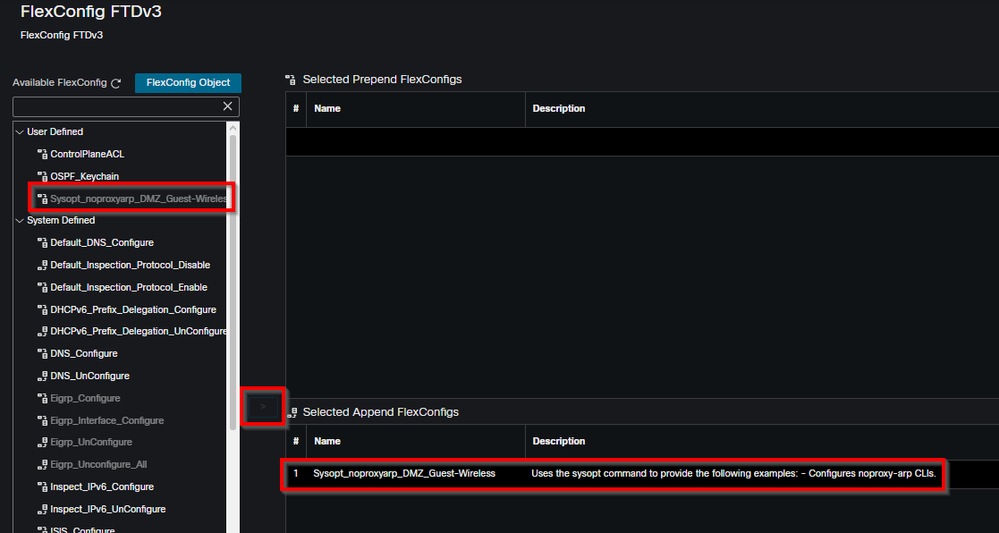 inline_image_2.png
inline_image_2.png4: After deployment, test the static IP assignment on the affected host. The firewall must no longer be able to respond to ARP probes for unassigned IP addresses, allowing hosts to successfully use their static IP configurations without duplicate IP address errors.
When applicable, consider disabling Proxy ARP at the NAT rule level rather than interface-wide to minimize unintended impact on other network functions. This provides more granular control over Proxy ARP behavior.
Cause
Proxy Address Resolution Protocol (Proxy ARP) was enabled on the FTD interface, causing the firewall to respond to ARP probes for IP addresses it did not explicitly own. This behavior resulted in hosts detecting a duplicate IP address condition during static address assignment. The firewall Proxy ARP functionality was responding with its own MAC address when hosts performed gratuitous ARP requests, making it appear as though the desired IP address was already in use by another device.
Related Content
Revision History
| Revision | Publish Date | Comments |
|---|---|---|
1.0 |
17-Apr-2026
|
Initial Release |
Contact Cisco
- Open a Support Case

- (Requires a Cisco Service Contract)
 Feedback
Feedback