What is driving adoption of SASE?
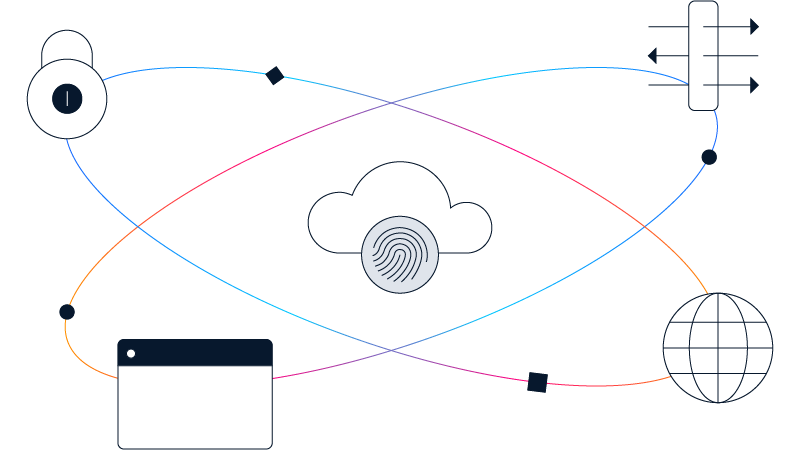
With the digital transformation of businesses, security is moving to the cloud. This is driving a need for converged services to reduce complexity, improve speed and agility, enable multicloud networking and secure the new SD-WAN-enabled architecture.
How can I benefit from a SASE model?
The SASE model consolidates numerous networking and security functions--traditionally delivered in siloed point solutions--in a single, integrated cloud service. By consolidating with SASE, enterprises can:
- Reduce costs and complexity
- Provide centralized orchestration and real-time application optimization
- Help secure seamless access for users
- Enable more secure remote and mobile access
- Restrict access based on user, device, and application identity
- Improve security by applying consistent policy
- Increase network and security staff effectiveness with centralized management&
What are the challenges to realizing SASE?
Gartner considers SASE to be a vision of a future secure networking model for enterprises to strive for. It is not currently a reality from any vendor. Today SASE is best represented by the convergence of cloud-managed SD-WAN and cloud-delivered security.
Moving to a SASE model will be a gradual process as IT rethinks how to connect a remote workforce to the distributed information resources they need. There will also likely be an increasing demand for "as-a-service" procurement models that offer more flexibility.