-
Dial Configuration Guide, Cisco IOS Release 15M&T
- Part 1: Dial Interfaces, Controllers, and Lines
-
Part 2: Modem Configuration and Management
-
Overview of Modem Interfaces
-
Configuring and Managing Integrated Modems
-
1- and 2-Port V.90 Modem WICs for Cisco 2600 and Cisco 3600 Series Multiservice Platforms
-
Call Tracker show Commands Extensions
-
Cisco NM-8AM-V2 and NM-16AM-V2 Analog Modem Network Modules with V.92
-
MICA and NextPort Modem Tech-Support Command Additions
-
PIAFS Wireless Data Protocol Version 2.1 for Cisco MICA Modems
-
V.92 and V.44 Support for Digital Modems
-
V.92 Modem on Hold for Cisco AS5300 and Cisco AS5800 Universal Access Servers
-
V.92 Modem on Hold for Cisco AS5350, Cisco AS5400, and Cisco AS5850 Universal Gateways and Cisco AS5800 Universal Access Servers
-
V.92 Quick Connect for Cisco AS5300 and Cisco AS5800 Universal Access Servers
-
V.92 Quick Connect for Cisco AS5350, Cisco AS5400, and Cisco AS5850 Universal Gateways and Cisco AS5800 Universal Access Servers
-
V.92 Reporting Using RADIUS Attribute v.92-info
-
Configuring and Managing Cisco Access Servers and Dial Shelves
-
Configuring and Managing External Modems
-
Modem Signal and Line States
-
Creating and Using Modem Chat Scripts
-
Cisco Modem User Interface
-
Modem Script and System Script Support in Large-Scale Dial-Out
-
-
Part 3: ISDN Configuration
-
Configuring ISDN BRI
-
Leased and Switched BRI Interface for ETSI NET3
-
ISDN BCAC and Round-Robin Channel Selection Enhancements
-
Configuring Virtual Asynchronous Traffic over ISDN
-
Configuring Modem Use over ISDN BRI
-
Configuring X.25 on ISDN
-
Configuring X.25 on ISDN Using AO/DI
-
Configuring ISDN on Cisco 800 Series Routers
-
- Part 4: Signaling Configuration
-
Part 5: Dial-on-Demand Routing Configuration
-
Preparing to Configure DDR
-
Configuring Legacy DDR Spokes
-
Configuring Legacy DDR Hubs
-
Configuring Peer-to-Peer DDR with Dialer Profiles
-
Dialer Map VRF-Aware for an MPLS VPN
-
Dialer Persistent
-
PPPoE Client DDR Idle-Timer
-
Redial Enhancements
-
Rotating Through Dial Strings
-
Configuring Dialer CEF
-
CEF Support for Dialer Profiles on Cisco 7500 Routers
-
IPv6 Cisco Express Forwarding Switching on Dialer Interfaces
-
Configuring Snapshot Routing
-
- Part 6: Dial-Backup Configuration
- Part 7: Dial-Related Addressing Services
- Part 8: Virtual Templates and Profiles
-
Part 9: PPP Configuration
-
Configuring Asynchronous SLIP and PPP
-
Optimized PPP Negotiation
-
Customer Profile Idle Timer Enhancements for Interesting Traffic
-
Multilink PPP Minimum Links Mandatory
-
Configuring Media-Independent PPP and Multilink PPP
-
PPP/MLP MRRU Negotiation Configuration
-
Troubleshooting Enhancements for Multilink PPP over ATM Link Fragmentation and Interleaving
-
Multichassis Multilink PPP
-
- Part 10: Callback and Bandwidth Allocation Configuration
- Configuring Large-Scale Dial-Out
- Part 11: Dial Access Specialized Features
- Part 12: Dial Access Scenarios
Table Of Contents
Configuring Dial Backup Using Dialer Watch
Prerequisites for Configuring Dial Backup Using Dialer Watch
Information About Configuring Dial Backup Using Dialer Watch
How to Configure Dialer Backup Using Dialer Watch
Configuring the Interface to Perform DDR Backup
Setting the Disable Timer on the Backup Interface
Configuration Examples for Dialer Watch
Configuring Dialer Watch Prior to Cisco IOS Release 12.3(11)T: Example
Configuring Dialer Watch with Cisco IOS Release 12.3(11)T and Later Releases: Example
Feature Information for Configuring Dial Backup Using Dialer Watch
Configuring Dial Backup Using Dialer Watch
First Published: February 24, 1998Last Updated: February 18, 2010The Dialer Watch feature provides enhancements to the Hot Standby Router Protocol (HSRP) function. This feature provides the backup router and backup links as soon as the primary routers and links become inactive.
Finding Feature Information
Your software release may not support all the features documented in this module. For the latest feature information and caveats, see the release notes for your platform and software release. To find information about the features documented in this module, and to see a list of the releases in which each feature is supported, see the "Feature Information for Configuring Dial Backup Using Dialer Watch" section.
Use Cisco Feature Navigator to find information about platform support and Cisco IOS and Catalyst OS software image support. To access Cisco Feature Navigator, go to http://www.cisco.com/go/cfn. An account on Cisco.com is not required.
Contents
•
Prerequisites for Configuring Dial Backup Using Dialer Watch
•
Information About Configuring Dial Backup Using Dialer Watch
•
How to Configure Dialer Backup Using Dialer Watch
•
Configuration Examples for Dialer Watch
•
Feature Information for Configuring Dial Backup Using Dialer Watch
Prerequisites for Configuring Dial Backup Using Dialer Watch
•
Decide which interfaces on which routers will act as primary and secondary interfaces. Unlike traditional backup methods, you can define multiple interfaces on multiple routers instead of a singly defined interface on one router.
•
Determine which addresses and networks are to be monitored or watched. Typically, this will be the address of an interface on a remote router or a network advertised by a central or remote router.
Information About Configuring Dial Backup Using Dialer Watch
To configure dial backup using the Dialer Watch feature, you should understand the following concept:
Dialer Watch Overview
Dialer Watch is a backup feature that integrates dial backup with routing capabilities. Prior dial backup implementations used the following conditions to trigger backup:
•
Interesting packets were defined at central and remote routers using dial-on-demand routing (DDR).
•
Connection loss occurred on a primary interface using a back up interface with floating static routes.
•
Traffic thresholds were exceeded using a dialer load threshold.
Prior backup implementations may not have supplied optimum performance on some networks, such as those using Frame Relay multipoint subinterfaces or Frame Relay connections that do not support end-to-end permanent virtual circuit (PVC) status updates.
Dialer Watch provides reliable connectivity without relying solely on defining interesting traffic to trigger outgoing calls at the central router. Dialer Watch uses the convergence times and characteristics of dynamic routing protocols. Integrating backup and routing features enables Dialer Watch to monitor every deleted route. By configuring a set of watched routes that define the primary interface, you are able to monitor and track the status of the primary interface as watched routes are added and deleted. Monitoring the watched routes is done in the following sequence:
1.
Whenever a watched route is deleted, Dialer Watch checks whether there is at least one valid route for any of the defined watched IP addresses.
2.
If no valid route exists, the primary line is considered down and unusable.
3.
If a valid route exists for at least one of the defined IP addresses and if the route is pointing to an interface other than the backup interface configured for Dialer Watch, the primary link is considered up.
4.
If the primary link goes down, Dialer Watch is immediately notified by the routing protocol and the secondary link is brought up.
5.
Once the secondary link is up, at the expiration of each idle timeout, the primary link is rechecked.
6.
If the primary link remains down, the idle timer is indefinitely reset.
7.
If the primary link is up, the secondary backup link is disconnected. Additionally, you can set a disable timer to create a delay for the secondary link to disconnect, after the primary link is reestablished.
Dialer Watch provides the following advantages:
•
Routing—Backup initialization is linked to the dynamic routing protocol, rather than a specific interface or static route entry. Therefore, both primary and backup interfaces can be any interface type, and can be used across multiple interfaces and multiple routers. Dialer Watch also relies on convergence, which is sometimes preferred over traditional DDR links.
•
Routing protocol independent—Static routes or dynamic routing protocols, such as Interior Gateway Routing Protocol (IGRP), Enhanced IGRP (EIGRP) or Open Shortest Path First (OSPF) can be used.
•
Nonpacket semantics—Dialer Watch does not exclusively rely on interesting packets to trigger dialing. The link is automatically brought up when the primary line goes down without postponing dialing.
•
Dial backup reliability—DDR redial functionality is extended to dial indefinitely in the event that secondary backup lines are not initiated. Typically, DDR redial attempts are affected by enable-timeouts and wait-for-carrier time values. Intermittent media difficulties or flapping interfaces can cause problems for traditional DDR links. However, Dialer Watch automatically reestablishes the secondary backup line on ISDN, synchronous, and asynchronous serial links.
The following prerequisites apply to Dialer Watch:
•
The router is dial backup capable, meaning the router has a data communications equipment (DCE), terminal adapter, or network termination 1 device attached that supports V.25bis.
•
The router is configured for DDR. This configuration includes traditional commands such as dialer map and dialer in-band commands, and so on.
•
Dialer Watch is only supported for IP at this time.
For information on how to configure traditional DDR for dial backup, see the other chapters in the "Dial Backup" part of this publication.
Note
The Multilink PPP Minimum Links Mandatory feature has priority over the Dialer Watch feature. If both features are configured simultaneously then the ISDN link will not become inactive even if the primary link is active.
How to Configure Dialer Backup Using Dialer Watch
This section contains the following sections:
•
Configuring the Interface to Perform DDR Backup (Required)
•
Creating a Dialer List (Required)
•
Setting the Disable Timer on the Backup Interface (Optional)
Configuring the Interface to Perform DDR Backup
Perform this task to configure the interface to perform DDR backup. This task initiates Dialer Watch.
SUMMARY STEPS
1.
enable
2.
configure terminal
3.
interface type number
4.
dialer watch-group group-number
DETAILED STEPS
Creating a Dialer List
Perform this task to create a dialer list. This task defines the IP addresses that you want to be watched.
SUMMARY STEPS
1.
enable
2.
configure terminal
3.
dialer watch-list group-number ip ip-address address-mask
DETAILED STEPS
Setting the Disable Timer on the Backup Interface
Perform this task to set the disable timer on the backup interface. You may want to implement a delay before the backup interface is dropped once the primary interface recovers. This delay can ensure stability, especially for flapping interfaces or interfaces experiencing frequent route changes.
Note
The dialer watch-disable command used in Dialer Watch configurations was replaced in Cisco IOS Release 12.3(11)T by the dialer watch-list delay command. When using the dialer watch-list delay command in software later than Cisco IOS Release 12.3(11)T, you can specify both a connect and disconnect timer for the disable timer. The disconnect time specifies that the disconnect timer is started when the secondary link is up and after the idle timeout period has expired, and only when software has determined that the primary route has come up.
In Cisco IOS Releases Prior to 12.3(11)T
Perform this task to apply a disable timer.
SUMMARY STEPS
1.
enable
2.
configure terminal
3.
interface type number
4.
dialer watch-disable seconds
DETAILED STEPS
In Cisco IOS Release 12.3(11)T and Later
Perform this task to apply a disable timer.
SUMMARY STEPS
1.
enable
2.
configure terminal
3.
interface type number
4.
dialer watch-list group-number delay {connect connect-time | disconnect disconnect-time}
DETAILED STEPS
Configuration Examples for Dialer Watch
The dialer watch-disable command used in Dialer Watch configurations was replaced in Cisco IOS Release 12.3(11)T by the dialer watch-list delay command. The following sections provide examples of how to configure Dialer Watch in software before and after the dialer watch-disable command was replaced.
•
Configuring Dialer Watch Prior to Cisco IOS Release 12.3(11)T: Example
•
Configuring Dialer Watch with Cisco IOS Release 12.3(11)T and Later Releases: Example
Configuring Dialer Watch Prior to Cisco IOS Release 12.3(11)T: Example
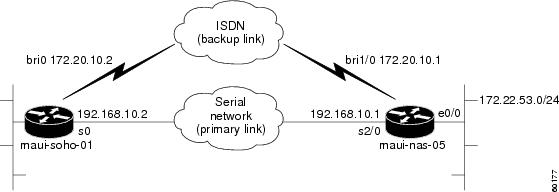
In the following example, an ISDN BRI line is used to back up a serial leased line connection by configuring the Dialer Watch feature on a router named maui-soho-01. The Dialer Watch feature enables the router to monitor the existence of a specified route. If that route is not present, the backup interface is activated. Unlike other backup methods, the Dialer Watch feature does not require interesting traffic to activate the backup interface. The configuration shown in Figure 1 uses legacy dial-on-demand routing (DDR) and the Open Shortest Path First (OSPF) routing protocol. Dialer profiles can be used in place of DDR. Once the backup connection is activated, you must ensure that the routing table is updated to use the new backup route. Additional information about the Dialer Watch feature is available at the following website:
http://www.cisco.com/warp/public/129/bri-backup-map-watch.html
For additional information on configuring legacy DDR, dialer profiles, PPP, and traditional dial backup features, see the relevant chapters in this publication.
Figure 1 Dialer Watch for Frame Relay Interfaces
Note
The following example uses commands supported in Cisco IOS software prior to Release 12.3(11)T. See the updated example for configuring Dialer Watch after Cisco IOS Release 12.3(11)T that follows this example.
Configuration for maui-soho-01
maui-soho-01# show running-configBuilding configuration...Current configuration : 1546 bytes!version 12.1no service single-slot-reload-enableservice timestamps debug uptimeservice timestamps log uptimeno service password-encryption!hostname maui-soho-01!logging rate-limit console 10 except errorsaaa new-modelaaa authentication login default localaaa authentication login NO_AUTHEN noneaaa authentication ppp default local!This is basic AAA configuration for PPP calls.enable secret 5 <deleted>!username maui-nas-05 password 0 cisco!Username for remote router (maui-nas-05) and shared secret.!Shared secret(used for CHAP authentication) must be the same on both sides.ip subnet-zerono ip finger!isdn switch-type basic-ni!interface Loopback0ip address 209.165.200.225 255.255.255.224!interface Ethernet0ip address 209.165.200.226 255.255.255.224!interface Serial0!Primary link.ip address 209.165.200.227 255.255.255.224encapsulation pppppp authentication chap!interface BRI0ip address 209.165.200.228 255.255.255.224!IP address for the BRI interface (backup link).encapsulation pppdialer idle-timeout 30!Idle timeout(in seconds)for this backup link.!Dialer watch checks the status of the primary link every time the!idle-timeout expires.dialer watch-disable 15!Delays disconnecting the backup interface for 15 seconds after the!primary interface is found to be up.dialer map ip 192.0.2.0 name maui-nas-05 broadcast 5550111!Dialer map for the BRI interface of the remote router.dialer map ip 192.0.2.1 name maui-nas-05 broadcast 5550111!Map statement for the route/network being watched by the!dialer watch-list command.!This address must exactly match the network configured with the!dialer watch-list command.!When the watched route disappears, this dials the specified phone number.dialer watch-group 8!Enable Dialer Watch on this backup interface.!Watch the route specified with dialer watch-list 8.dialer-group 1!Apply interesting traffic defined in dialer-list 1.isdn switch-type basic-niisdn spid1 51255522220101 5550112isdn spid2 51255522230101 5550112ppp authentication chap!Use chap authentication.!router ospf 5log-adjacency-changesnetwork 209.165.200.230 255.255.255.224 area 0network 209.165.200.231 255.255.255.224 area 0network 209.165.200.232 255.255.255.224 area 0network 209.165.200.233 255.255.255.224 area 0!ip classlessno ip http server!dialer watch-list 8 ip 209.165.200.234 255.255.255.224!This defines the route(s) to be watched.!This exact route(including subnet mask) must exist in the routing table.!Use the dialer watch-group 8 command to apply this list to the backup interface.access-list 101 remark Define Interesting Trafficaccess-list 101 deny ospf any any!Mark OSPF as uninteresting.!This will prevent OSPF hellos from keeping the link up.Access-list 101 permit ip any anydialer-list 1 protocol ip list 101!Interesting traffic is defined by access-list 101.!This is applied to BRI0 using dialer-group 1.!line con 0login authentication NO_AUTHENtransport input noneline vty 0 4!endConfiguration for maui-nas-05
maui-nas-05# show running-configBuilding configuration...Current configuration:!version 12.1service timestamps debug uptimeservice timestamps log uptimeno service password-encryption!hostname maui-nas-05!aaa new-modelaaa authentication login default localaaa authentication login NO_AUTHEN noneaaa authentication ppp default local! -- This is basic AAA configuration for PPP calls.Enable secret 5 <deleted>!username maui-soho-01 password 0 cisco!Username for remote router (maui-soho-01) and shared secret.!Shared secret(used for CHAP authentication) must be the same on both sides.!ip subnet-zero!isdn switch-type basic-ni!interface Loopback0ip address 209.165.200.230 255.255.255.224!interface Ethernet0/0ip address 209.165.200.231 255.255.255.224!interface Ethernet0/1no ip addressshutdown!interface BRI1/0!Backup link.ip address 209.165.200.231 255.255.255.224encapsulation pppdialer map ip 172.20.10.2 name maui-soho-01 broadcast!Dialer map with IP address and authenticated username for remote destination.!The name should match the authentication username provided by the remote side.!The dialer map statement is used even though this router is not dialing out.Dialer-group 1!Apply interesting traffic defined in dialer-list 1.isdn switch-type basic-niisdn spid1 51255501110101 5550111isdn spid2 51255501120101 5550112ppp authentication chap!...!interface Serial2/0ip address 209.165.200.232 255.255.255.224encapsulation pppclockrate 64000ppp authentication chap!...!router ospf 5network 209.165.200.230 255.255.255.224 area 0network 209.165.200.231 255.255.255.224 area 0network 209.165.200.232 255.255.255.224 area 0network 209.165.200.233 255.255.255.224 area 0default-information originate!ip classlessip route 209.165.200.229 255.255.255.224 Ethernet0/0no ip http server!dialer-list 1 protocol ip permit!This defines all IP traffic as interesting.!line con 0login authentication NO_AUTHENtransport input noneline 97 102line aux 0line vty 0 4!endConfiguring Dialer Watch with Cisco IOS Release 12.3(11)T and Later Releases: Example
The following example shows how to configure Dialer Watch using the dialer watch-list delay command that replaced the dialer watch-disable command.
Configuration for maui-soho-01
maui-soho-01# show running-configBuilding configuration...Current configuration : 1546 bytes!version 12.4no service single-slot-reload-enableservice timestamps debug uptimeservice timestamps log uptimeno service password-encryption!hostname maui-soho-01!logging rate-limit console 10 except errorsaaa new-modelaaa authentication login default localaaa authentication login NO_AUTHEN noneaaa authentication ppp default local!This is basic AAA configuration for PPP calls.enable secret 5 <deleted>!username maui-nas-05 password 0 cisco!Username for remote router (maui-nas-05) and shared secret.!Shared secret(used for CHAP authentication) must be the same on both sides.ip subnet-zerono ip finger!isdn switch-type basic-ni!interface Loopback0ip address 209.165.200.225 255.255.255.224!interface Ethernet0ip address 209.165.200.226 255.255.255.224!interface Serial0!Primary link.ip address 209.165.200.227 255.255.255.224encapsulation pppppp authentication chap!interface BRI0ip address 209.165.200.228 255.255.255.224!IP address for the BRI interface (backup link).encapsulation pppdialer idle-timeout 30!Idle timeout(in seconds)for this backup link.!Dialer watch checks the status of the primary link every time the!idle-timeout expires.dialer map ip 192.0.2.1 name maui-nas-05 broadcast 5550111!Dialer map for the BRI interface of the remote router.dialer map ip 192.0.2.2 name maui-nas-05 broadcast 5550111!Map statement for the route/network being watched by the!dialer watch-list command.!This address must exactly match the network configured with the!dialer watch-list command.!When the watched route disappears, this dials the specified phone number.dialer watch-group 8!Enable Dialer Watch on this backup interface.!Watch the route specified with dialer watch-list 8.dialer-group 1!Apply interesting traffic defined in dialer-list 1.isdn switch-type basic-niisdn spid1 51255522220101 5552222isdn spid2 51255522230101 5552223ppp authentication chap!Use chap authentication.dialer watch-list 8 delay disconnect 15!Delays disconnecting the backup interface for 15 seconds after the!primary interface is found to be up.!router ospf 5log-adjacency-changesnetwork 209.165.200.225 255.255.255.224 area 0network 209.165.200.226 255.255.255.224 area 0network 209.165.200.227 255.255.255.224 area 0network 209.165.200.228 255.255.255.224 area 0!ip classlessno ip http server!dialer watch-list 8 ip 209.165.200.229 255.255.255.224!This defines the route(s) to be watched.!This exact route(including subnet mask) must exist in the routing table.!Use the dialer watch-group 8 command to apply this list to the backup interface.access-list 101 remark Define Interesting Trafficaccess-list 101 deny ospf any any!Mark OSPF as uninteresting.!This will prevent OSPF hellos from keeping the link up.Access-list 101 permit ip any anydialer-list 1 protocol ip list 101!Interesting traffic is defined by access-list 101.!This is applied to BRI0 using dialer-group 1.!line con 0login authentication NO_AUTHENtransport input noneline vty 0 4!endConfiguration for maui-nas-05
maui-nas-05# show running-configBuilding configuration...Current configuration:!version 12.4service timestamps debug uptimeservice timestamps log uptimeno service password-encryption!hostname maui-nas-05!aaa new-modelaaa authentication login default localaaa authentication login NO_AUTHEN noneaaa authentication ppp default local! -- This is basic AAA configuration for PPP calls.Enable secret 5 <deleted>!username maui-soho-01 password 0 cisco!Username for remote router (maui-soho-01) and shared secret.!Shared secret(used for CHAP authentication) must be the same on both sides.!ip subnet-zero!isdn switch-type basic-ni!interface Loopback0ip address 209.165.200.225 255.255.255.224!interface Ethernet0/0ip address 209.165.200.226 255.255.255.224!interface Ethernet0/1no ip addressshutdown!interface BRI1/0!Backup link.ip address 209.165.200.227 255.255.255.224encapsulation pppdialer map ip 192.0.2.2 name maui-soho-01 broadcast!Dialer map with IP address and authenticated username for remote destination.!The name should match the authentication username provided by the remote side.!The dialer map statement is used even though this router is not dialing out.Dialer-group 1!Apply interesting traffic defined in dialer-list 1.isdn switch-type basic-niisdn spid1 51255501110101 5550111isdn spid2 51255501120101 5550112ppp authentication chap!! <<-- irrelevant output removed!interface Serial2/0ip address 192.168.10.1 255.255.255.252encapsulation pppclockrate 64000ppp authentication chap!! <<-- irrelevant output removed!router ospf 5network 209.165.200.225 255.255.255.224 area 0network 209.165.200.226 255.255.255.224 area 0network 209.165.200.227 255.255.255.224 area 0network 209.165.200.228 255.255.255.224 area 0default-information originate!ip classlessip route 209.165.200.225 255.255.255.224 Ethernet0/0no ip http server!dialer-list 1 protocol ip permit!This defines all IP traffic as interesting.!line con 0login authentication NO_AUTHENtransport input noneline 97 102line aux 0line vty 0 4!endAdditional References
The following sections provide references related to the Configuring Dial Backup Using Dialer Watch.
Related Documents
Standards
No new or modified standards are supported by this feature, and support for existing standards has not been modified by this feature.
—
MIBs
RFCs
No new or modified RFCs are supported by this feature, and support for existing RFCs has not been modified by this feature.
—
Technical Assistance
Feature Information for Configuring Dial Backup Using Dialer Watch
Table 1 lists the release history for this feature.
Not all commands may be available in your Cisco IOS software release. For release information about a specific command, see the command reference documentation.
Use Cisco Feature Navigator to find information about platform support and software image support. Cisco Feature Navigator enables you to determine which Cisco IOS and Catalyst OS software images support a specific software release, feature set, or platform. To access Cisco Feature Navigator, go to http://www.cisco.com/go/cfn. An account on Cisco.com is not required.
Note
Table 1 lists only the Cisco IOS software release that introduced support for a given feature in a given Cisco IOS software release train. Unless noted otherwise, subsequent releases of that Cisco IOS software release train also support that feature.
Cisco and the Cisco Logo are trademarks of Cisco Systems, Inc. and/or its affiliates in the U.S. and other countries. A listing of Cisco's trademarks can be found at www.cisco.com/go/trademarks. Third party trademarks mentioned are the property of their respective owners. The use of the word partner does not imply a partnership relationship between Cisco and any other company. (1005R)
Any Internet Protocol (IP) addresses and phone numbers used in this document are not intended to be actual addresses and phone numbers. Any examples, command display output, network topology diagrams, and other figures included in the document are shown for illustrative purposes only. Any use of actual IP addresses or phone numbers in illustrative content is unintentional and coincidental.
© 1998-2010 Cisco Systems, Inc. All rights reserved.

 Feedback
Feedback