Options to boot NCS 1004
This topic explains the boot options available on NCS 1004, including local SSD, network-based iPXE, Zero Touch Provisioning, and Golden ISO, to help you select the appropriate method for your deployment environment.
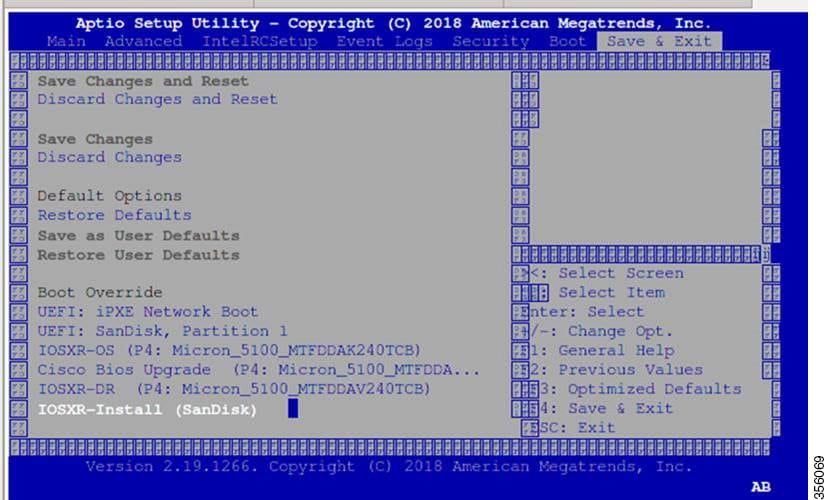
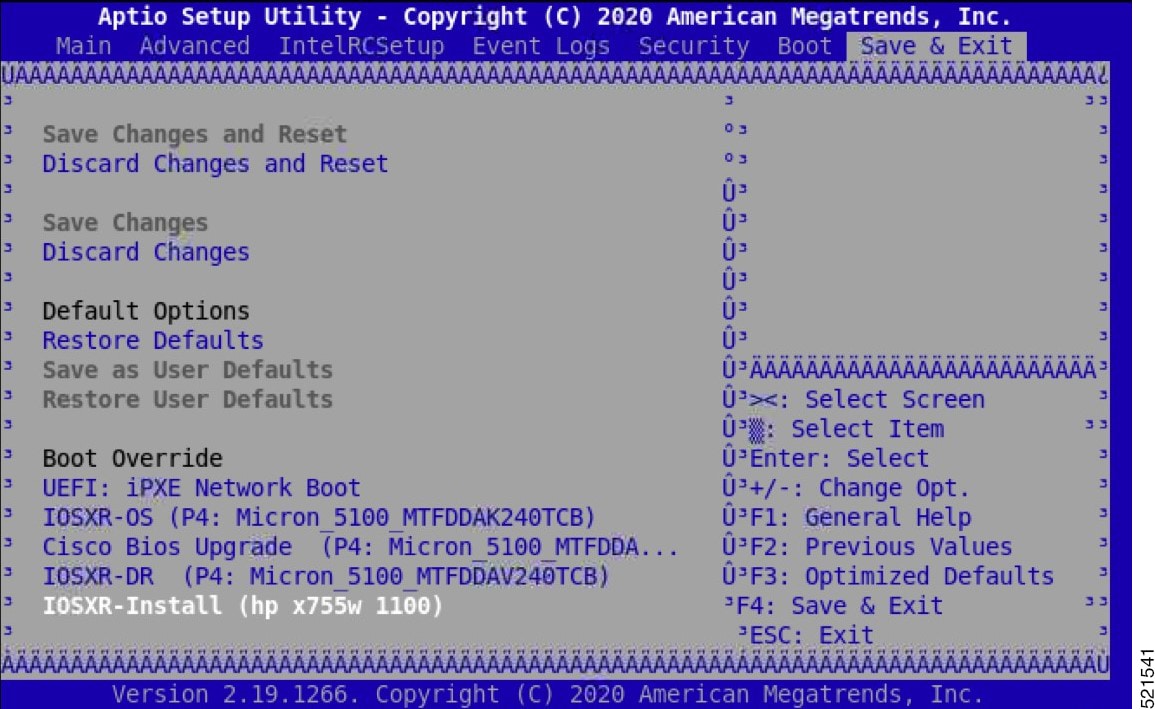
The boot options available on NCS 1004 are:
-
SSD (hard disk),
-
USB drive,
-
iPXE,
-
ZTP, and
-
Golden ISO.
 Note |
If bootable image is not available in any of these boot options, reboot the system. |
 Feedback
Feedback