5G Converged Core Session Management Function
Introduction
This Release Notes identifies changes and issues related to this software release.
Release Lifecycle Milestones
|
Release Lifecycle Milestone |
Milestone |
Date |
|---|---|---|
|
First Customer Ship |
FCS |
31-Jan-2025 |
|
End of Life |
EoL |
31-Jan-2025 |
|
End of Software Maintenance |
EoSM |
1-Aug-2026 |
|
End of Vulnerability and Security Support |
EoVSS |
1-Aug-2026 |
|
Last Date of Support |
LDoS |
31-Aug-2027 |
These milestones and the intervals between them are defined in the Cisco Ultra Cloud Core (UCC) Software Release Lifecycle Product Bulletin available on cisco.com.
Release Package Version Information
|
Software Packages |
Version |
|---|---|
| ccg-2025.01.1.SPA.tgz |
2025.01.1 |
| NED package |
ncs-5.6.8-ccg-nc-2025.01.1 ncs-6.1.14-ccg-nc-2025.01.1 |
| NSO |
5.6.8 6.1.14 |
Descriptions for the various packages provided with this release are available in the Release Package Descriptions section.
Verified Compatibility
|
Products |
Version |
|---|---|
|
Ultra Cloud Core SMI |
2025.01.1.14 |
|
Ultra Cloud CDL |
1.12.0 |
|
Ultra Cloud Core UPF |
2025.01.0 |
|
Ultra Cloud cnSGWc |
2025.01.1 |
For information on the Ultra Cloud Core products, refer to the documents for this release available at:
What's New in this Release
Features and Enhancements
This section covers a brief description of the features and enhancements introduced in this release.
| Feature | Description |
|---|---|
|
New KPI metric for monitoring the default mapped flows |
SMF introduces a new metric smf_service_flow_stats in the Policy control total flow statistics category to indicate the mapped flows. The smf_service_flow_stats supports the following labels:
The following are the sample queries of smf_service_flow_stats: smf_service_flow_stats{app_name="smf",cluster="Local",data_center="DC",dnn="intershat#cisco.com", instance_id="0",mapped_flow="true",qos_5qi="13",rat_type="EUTRA",service_name="smf-service"} 1 smf_service_flow_stats{app_name="smf",cluster="Local",data_center="DC",dnn="intershat#cisco.com", instance_id="0",mapped_flow="true",qos_5qi="9",rat_type="EUTRA",service_name="smf-service"} 1 |
Behavior Changes
This section covers a brief description of behavior changes introduced in this release.
| Behavior Change | Description |
|---|---|
| Send service-names in plain string format |
Previous Behavior: During peer Network Function (NF) discovery, SMF sends service-names to Service Communication Proxy (SCP) in an array format. Example: 3gpp-Sbi-Discovery-service-names:["nudm-uecm"] New Behavior: SMF now sends the service-names in plain string format to SCP during the peer NF discovery. Example: "sbi_discovery_service_names_3gpp": nudm-uecm |
Related Documentation
Installation and Upgrade Notes
This Release Note does not contain general installation and upgrade instructions. Refer to the existing installation documentation for specific installation and upgrade considerations.
Software Integrity Verification
To verify the integrity of the software image you have from Cisco, you can validate the SHA512 checksum information against the checksum identified by Cisco for the software.
Image checksum information is available through Cisco.com Software Download Details. To find the checksum, hover the mouse pointer over the software image you have downloaded.

At the bottom you find the SHA512 checksum, if you do not see the whole checksum you can expand it by pressing the "..." at the end.
To validate the information, calculate a SHA512 checksum using the information in Table 1 and verify that it matches either the one provided on the software download page.
To calculate a SHA512 checksum on your local desktop, refer to the table below.
|
Operating System |
SHA512 checksum calculation command examples |
||
|---|---|---|---|
|
Microsoft Windows |
Open a command line window and type the following command:
|
||
|
Apple MAC |
Open a terminal window and type the following command:
|
||
|
Linux |
Open a terminal window and type the following command:
OR
|
||
|
|||
If the SHA512 checksum matches, you can be sure that no one has tampered with the software image or the image has not been corrupted during download.
If the SHA512 checksum does not match, we advise you to not attempt upgrading any systems with the corrupted software image. Download the software again and verify the SHA512 checksum again. If there is a constant mismatch, please open a case with the Cisco Technical Assistance Center.
Certificate Validation
SMF software images are signed via x509 certificates. Please view the .README file packaged with the software for information and instructions on how to validate the certificates.
Open Bugs for this Release
There are no open bugs in this software release.
Resolved Bugs for this Release
The following table lists the resolved bugs in this specific software release.
 Note |
This software release may contain bug fixes first introduced in other releases. Additional information for all resolved bugs for this release are available in the Cisco Bug Search Tool. |
|
Bug ID |
Headline |
Behavior Change |
|---|---|---|
| Release procedure KPI impact, sending 500 instead of 204 |
No |
|
| Need metrics to monitor the default bearer which have 5QI remaped |
No |
|
|
snssai label is empty in bulkstats for few procedures |
No |
|
| CBR has UL and DL filters set in TFT when more filters present, rejected by MME |
No |
|
| CSCwn95332 | PTI=0, PDU session ID=0 lead to rest pod panic |
No |
|
Rest EP pod panic during NRF discovery |
No |
|
| CSCwo06527 | Discovery for status notification, multiple n40 release seen |
No |
| Not handling smContextStatusUri value as fqdn, svc crashes while creating n40req |
No |
|
| Not sending 3gpp-SBI-discovery-service-names in plain string format to scp |
Yes |
|
|
UE decoding problem - SMF sending multiple QOS rules in same container |
Yes |
|
| Unable to handle smContextRetrieveReq w/o payload, throws 503 marshall error |
No |
Operator Notes
Cloud Native Product Version Numbering System
The show helm list command displays detailed information about the version of the cloud native product currently deployed.
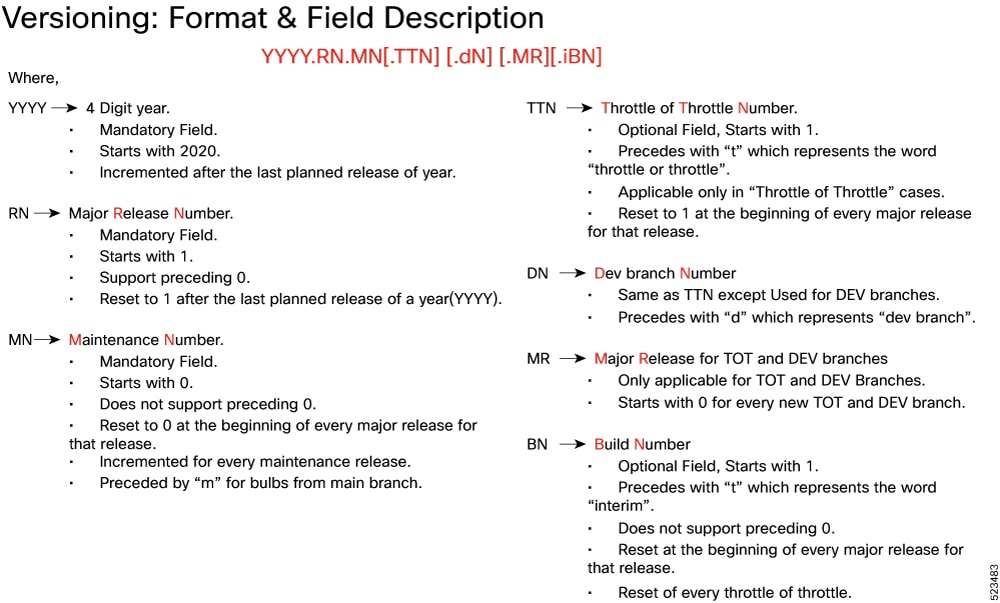
The appropriate version number field increments after a version has been released. The new version numbering format is a contiguous sequential number that represents incremental changes between releases. This format facilitates identifying the changes between releases when using Bug Search Tool to research software releases.
Release Package Descriptions
The following table provides descriptions for the packages that are available with this release.
|
Software Packages |
Description |
|---|---|
|
ccg.<version>.SPA.tgz |
The SMF offline release signature package. This package contains the SMF deployment software, NED package, as well as the release signature, certificate, and verification information. |
|
ncs-<nso_version>-ccg-nc-<version>.tar.gz |
The NETCONF NED package. This package includes all the yang files that are used for NF configuration. Note that NSO is used for the NED file creation. |
Obtaining Documentation and Submitting a Service Request
For information on obtaining documentation, using the Cisco Bug Search Tool (BST), submitting a service request, and gathering additional information, refer to https://www.cisco.com/c/en/us/support/index.html.
 Feedback
Feedback