- Preface
- Overview
- Using the Command-Line Interface
- Configuring the Switch Alarms
- Assigning the Switch IP Address and Default Gateway
- Configuring Cisco IOS Configuration Engine
- Clustering Switches
- Administering the Switch
- Configuring PTP
- Configuring PROFINET
- Configuring SDM Templates
- Configuring Switch-Based Authentication
- Configuring IEEE 802.1x Port-Based Authentication
- Configuring Web-Based Authentication
- Configuring Interface Characteristics
- Configuring Smartports Macros
- Configuring VLANs
- Configuring VTP
- Configuring Voice VLAN
- Configuring Private VLANs
- Configuring IEEE 802.1Q and Layer 2 Protocol Tunneling
- Configuring STP
- Configuring MSTP
- Configuring Optional Spanning-Tree Features
- Configuring Resilient Ethernet Protocol
- Configuring Flex Links and the MAC Address-Table Move Update Feature
- Configuring DHCP Features and IP Source Guard Features
- Configuring Dynamic ARP Inspection
- Configuring IGMP Snooping and MVR
- Configuring Port-Based Traffic Control
- Configuring SPAN and RSPAN
- Configuring LLDP, LLDP-MED, and Wired Location Service
- Configuring CDP
- Configuring UDLD
- Configuring RMON
- Configuring System Message Logging
- Configuring SNMP
- Configuring Embedded Event Manager
- Configuring Network Security with ACLs
- Configuring QoS
- Configuring EtherChannels and Link-State Tracking
- Configuring IP Unicast Routing
- Configuring IPv6 Unicast Routing
- Implementing IPv6 Multicast
- Configuring IPv6 ACLs
- Configuring IPv6 MLD Snooping
- Configuring HSRP and VRRP
- Configuring Cisco IOS IP SLAs Operations
- Configuring Enhanced Object Tracking
- Configuring Web Cache Services By Using WCCP
- Configuring IP Multicast Routing
- Configuring MSDP
- Configuring Fallback Bridging
- Troubleshooting
- Working with the Cisco IOS File System, Configuration Files, and Software Images
- Unsupported Commands in Cisco IOS Release 15.0(2)EY
- Index
Configuring Optional Spanning-Tree Features
This chapter describes how to configure optional spanning-tree features on the IE 3000 switch. You can configure all of these features when your switch is running the per-VLAN spanning-tree plus (PVST+). You can configure only the noted features when your switch is running the Multiple Spanning Tree Protocol (MSTP) or the rapid per-VLAN spanning-tree plus (rapid-PVST+) protocol.
For information on configuring the PVST+ and rapid PVST+, see Chapter21, “Configuring STP” For information about the Multiple Spanning Tree Protocol (MSTP) and how to map multiple VLANs to the same spanning-tree instance, see Chapter22, “Configuring MSTP”

Note![]() For complete syntax and usage information for the commands used in this chapter, see the command reference for this release.
For complete syntax and usage information for the commands used in this chapter, see the command reference for this release.
Understanding Optional Spanning-Tree Features
These sections contain this conceptual information:
- Understanding Port Fast
- Understanding BPDU Guard
- Understanding BPDU Filtering
- Understanding UplinkFast
- Understanding BackboneFast
- Understanding EtherChannel Guard
- Understanding Root Guard
- Understanding Loop Guard
Understanding Port Fast
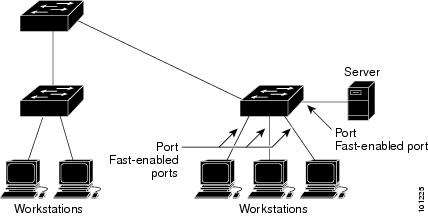
Port Fast immediately brings an interface configured as an access or trunk port to the forwarding state from a blocking state, bypassing the listening and learning states. You can use Port Fast on interfaces connected to a single workstation or server, as shown in Figure 23-1, to allow those devices to immediately connect to the network, rather than waiting for the spanning tree to converge.
Interfaces connected to a single workstation or server should not receive bridge protocol data units (BPDUs). An interface with Port Fast enabled goes through the normal cycle of spanning-tree status changes when the switch is restarted.

Note![]() Because the purpose of Port Fast is to minimize the time interfaces must wait for spanning-tree to converge, it is effective only when used on interfaces connected to end stations. If you enable Port Fast on an interface connecting to another switch, you risk creating a spanning-tree loop.
Because the purpose of Port Fast is to minimize the time interfaces must wait for spanning-tree to converge, it is effective only when used on interfaces connected to end stations. If you enable Port Fast on an interface connecting to another switch, you risk creating a spanning-tree loop.
You can enable this feature by using the spanning-tree portfast interface configuration or the spanning-tree portfast default global configuration command.
Figure 23-1 Port Fast-Enabled Interfaces
Understanding BPDU Guard
The BPDU guard feature can be globally enabled on the switch or can be enabled per port, but the feature operates with some differences.
At the global level, you enable BPDU guard on Port Fast-enabled ports by using the spanning-tree portfast bpduguard default global configuration command. Spanning tree shuts down ports that are in a Port Fast-operational state if any BPDU is received on them. In a valid configuration, Port Fast-enabled ports do not receive BPDUs. Receiving a BPDU on a Port Fast-enabled port means an invalid configuration, such as the connection of an unauthorized device, and the BPDU guard feature puts the port in the error-disabled state. When this happens, the switch shuts down the entire port on which the violation occurred.
To prevent the port from shutting down, you can use the errdisable detect cause bpduguard shutdown vlan global configuration command to shut down just the offending VLAN on the port where the violation occurred.
At the interface level, you enable BPDU guard on any port by using the spanning-tree bpduguard enable interface configuration command w ithout also enabling the Port Fast feature. When the port receives a BPDU, it is put in the error-disabled state.
The BPDU guard feature provides a secure response to invalid configurations because you must manually put the interface back in service. Use the BPDU guard feature in a service-provider network to prevent an access port from participating in the spanning tree.
Understanding BPDU Filtering
The BPDU filtering feature can be globally enabled on the switch or can be enabled per interface, but the feature operates with some differences.
At the global level, you can enable BPDU filtering on Port Fast-enabled interfaces by using the spanning-tree portfast bpdufilter default global configuration command. This command prevents interfaces that are in a Port Fast-operational state from sending or receiving BPDUs. The interfaces still send a few BPDUs at link-up before the switch begins to filter outbound BPDUs. You should globally enable BPDU filtering on a switch so that hosts connected to these interfaces do not receive BPDUs. If a BPDU is received on a Port Fast-enabled interface, the interface loses its Port Fast-operational status, and BPDU filtering is disabled.
At the interface level, you can enable BPDU filtering on any interface by using the spanning-tree bpdufilter enable interface configuration command w ithout also enabling the Port Fast feature. This command prevents the interface from sending or receiving BPDUs.

You can enable the BPDU filtering feature for the entire switch or for an interface.
Understanding UplinkFast
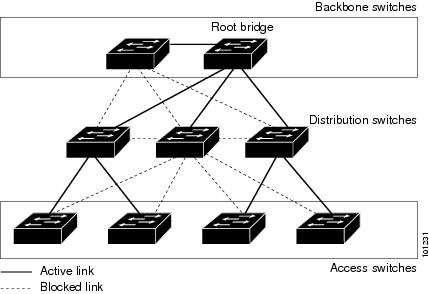
Switches in hierarchical networks can be grouped into backbone switches, distribution switches, and access switches. Figure 23-2 shows a complex network where distribution switches and access switches each have at least one redundant link that spanning tree blocks to prevent loops.
Figure 23-2 Switches in a Hierarchical Network
If a switch loses connectivity, it begins using the alternate paths as soon as the spanning tree selects a new root port. By enabling UplinkFast with the spanning-tree uplinkfast global configuration command, you can accelerate the choice of a new root port when a link or switch fails or when the spanning tree reconfigures itself. The root port transitions to the forwarding state immediately without going through the listening and learning states, as it would with the normal spanning-tree procedures.
When the spanning tree reconfigures the new root port, other interfaces flood the network with multicast packets, one for each address that was learned on the interface. You can limit these bursts of multicast traffic by reducing the max-update-rate parameter (the default for this parameter is 150 packets per second). However, if you enter zero, station-learning frames are not generated, so the spanning-tree topology converges more slowly after a loss of connectivity.

Note![]() UplinkFast is most useful in wiring-closet switches at the access or edge of the network. It is not appropriate for backbone devices. This feature might not be useful for other types of applications.
UplinkFast is most useful in wiring-closet switches at the access or edge of the network. It is not appropriate for backbone devices. This feature might not be useful for other types of applications.
UplinkFast provides fast convergence after a direct link failure and achieves load balancing between redundant Layer 2 links using uplink groups. An uplink group is a set of Layer 2 interfaces (per VLAN), only one of which is forwarding at any given time. Specifically, an uplink group consists of the root port (which is forwarding) and a set of blocked ports, except for self-looping ports. The uplink group provides an alternate path in case the currently forwarding link fails.
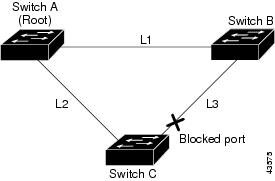
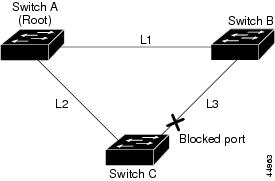
Figure 23-3 shows an example topology with no link failures. Switch A, the root switch, is connected directly to Switch B over link L1 and to Switch C over link L2. The Layer 2 interface on Switch C that is connected directly to Switch B is in a blocking state.
Figure 23-3 UplinkFast Example Before Direct Link Failure
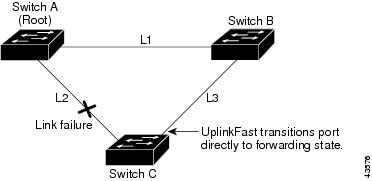
If Switch C detects a link failure on the currently active link L2 on the root port (a direct link failure), UplinkFast unblocks the blocked interface on Switch C and transitions it to the forwarding state without going through the listening and learning states, as shown in Figure 23-4. This change takes approximately 1 to 5 seconds.
Figure 23-4 UplinkFast Example After Direct Link Failure
Understanding BackboneFast
BackboneFast detects indirect failures in the core of the backbone. BackboneFast is a complementary technology to the UplinkFast feature, which responds to failures on links directly connected to access switches. BackboneFast optimizes the maximum-age timer, which controls the amount of time the switch stores protocol information received on an interface. When a switch receives an inferior BPDU from the designated port of another switch, the BPDU is a signal that the other switch might have lost its path to the root, and BackboneFast tries to find an alternate path to the root.
BackboneFast, which is enabled by using the spanning-tree backbonefast global configuration command, starts when a root port or blocked interface on a switch receives inferior BPDUs from its designated switch. An inferior BPDU identifies a switch that declares itself as both the root bridge and the designated switch. When a switch receives an inferior BPDU, it means that a link to which the switch is not directly connected (an indirect link) has failed (that is, the designated switch has lost its connection to the root switch). Under spanning-tree rules, the switch ignores inferior BPDUs for the configured maximum aging time specified by the spanning-tree vlan vlan-id max-age global configuration command.
The switch tries to find if it has an alternate path to the root switch. If the inferior BPDU arrives on a blocked interface, the root port and other blocked interfaces on the switch become alternate paths to the root switch. (Self-looped ports are not considered alternate paths to the root switch.) If the inferior BPDU arrives on the root port, all blocked interfaces become alternate paths to the root switch. If the inferior BPDU arrives on the root port and there are no blocked interfaces, the switch assumes that it has lost connectivity to the root switch, causes the maximum aging time on the root port to expire, and becomes the root switch according to normal spanning-tree rules.
If the switch has alternate paths to the root switch, it uses these alternate paths to send a root link query (RLQ) request. The switch sends the RLQ request on all alternate paths and waits for an RLQ reply from other switches in the network.
If the switch discovers that it still has an alternate path to the root, it expires the maximum aging time on the interface that received the inferior BPDU. If all the alternate paths to the root switch indicate that the switch has lost connectivity to the root switch, the switch expires the maximum aging time on the interface that received the RLQ reply. If one or more alternate paths can still connect to the root switch, the switch makes all interfaces on which it received an inferior BPDU its designated ports and moves them from the blocking state (if they were in the blocking state), through the listening and learning states, and into the forwarding state.
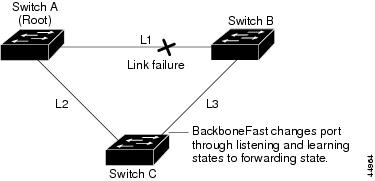
Figure 23-5 shows an example topology with no link failures. Switch A, the root switch, connects directly to Switch B over link L1 and to Switch C over link L2. The Layer 2 interface on Switch C that connects directly to Switch B is in the blocking state.
Figure 23-5 BackboneFast Example Before Indirect Link Failure
If link L1 fails as shown in Figure 23-6, Switch C cannot detect this failure because it is not connected directly to link L1. However, because Switch B is directly connected to the root switch over L1, it detects the failure, elects itself the root, and begins sending BPDUs to Switch C, identifying itself as the root. When Switch C receives the inferior BPDUs from Switch B, Switch C assumes that an indirect failure has occurred. At that point, BackboneFast allows the blocked interface on Switch C to move immediately to the listening state without waiting for the maximum aging time for the interface to expire. BackboneFast then transitions the Layer 2 interface on Switch C to the forwarding state, providing a path from Switch B to Switch A. The root-switch election takes approximately 30 seconds, twice the Forward Delay time if the default Forward Delay time of 15 seconds is set. Figure 23-6 shows how BackboneFast reconfigures the topology to account for the failure of link L1.
Figure 23-6 BackboneFast Example After Indirect Link Failure
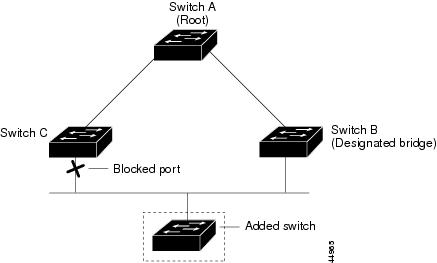
If a new switch is introduced into a shared-medium topology as shown in Figure 23-7, BackboneFast is not activated because the inferior BPDUs did not come from the recognized designated switch (Switch B). The new switch begins sending inferior BPDUs that indicate it is the root switch. However, the other switches ignore these inferior BPDUs, and the new switch learns that Switch B is the designated switch to Switch A, the root switch.
Figure 23-7 Adding a Switch in a Shared-Medium Topology
Understanding EtherChannel Guard
You can use EtherChannel guard to detect an EtherChannel misconfiguration between the switch and a connected device. A misconfiguration can occur if the switch interfaces are configured in an EtherChannel, but the interfaces on the other device are not. A misconfiguration can also occur if the channel parameters are not the same at both ends of the EtherChannel. For EtherChannel configuration guidelines, see the “EtherChannel Configuration Guidelines” section.
If the switch detects a misconfiguration on the other device, EtherChannel guard places the switch interfaces in the error-disabled state, and displays an error message.
You can enable this feature by using the spanning-tree etherchannel guard misconfig global configuration command.
Understanding Root Guard
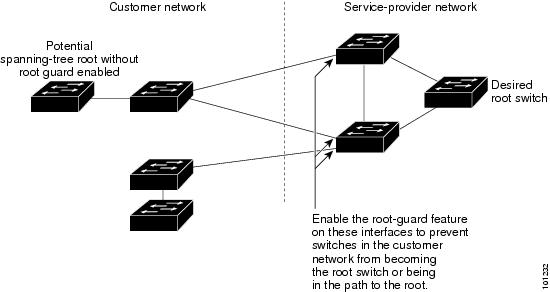
The Layer 2 network of a service provider (SP) can include many connections to switches that are not owned by the SP. In such a topology, the spanning tree can reconfigure itself and select a customer switch as the root switch, as shown in Figure 23-8. You can avoid this situation by enabling root guard on SP switch interfaces that connect to switches in your customer’s network. If spanning-tree calculations cause an interface in the customer network to be selected as the root port, root guard then places the interface in the root-inconsistent (blocked) state to prevent the customer’s switch from becoming the root switch or being in the path to the root.
If a switch outside the SP network becomes the root switch, the interface is blocked (root-inconsistent state), and spanning tree selects a new root switch. The customer’s switch does not become the root switch and is not in the path to the root.
If the switch is operating in multiple spanning-tree (MST) mode, root guard forces the interface to be a designated port. If a boundary port is blocked in an internal spanning-tree (IST) instance because of root guard, the interface also is blocked in all MST instances. A boundary port is an interface that connects to a LAN, the designated switch of which is either an IEEE 802.1D switch or a switch with a different MST region configuration.
Root guard enabled on an interface applies to all the VLANs to which the interface belongs. VLANs can be grouped and mapped to an MST instance.
You can enable this feature by using the spanning-tree guard root interface configuration command.

Figure 23-8 Root Guard in a Service-Provider Network
Understanding Loop Guard
You can use loop guard to prevent alternate or root ports from becoming designated ports because of a failure that leads to a unidirectional link. This feature is most effective when it is enabled on the entire switched network. Loop guard prevents alternate and root ports from becoming designated ports, and spanning tree does not send BPDUs on root or alternate ports.
You can enable this feature by using the spanning-tree loopguard default global configuration command.
When the switch is operating in PVST+ or rapid-PVST+ mode, loop guard prevents alternate and root ports from becoming designated ports, and spanning tree does not send BPDUs on root or alternate ports.
When the switch is operating in MST mode, BPDUs are not sent on nonboundary ports only if the interface is blocked by loop guard in all MST instances. On a boundary port, loop guard blocks the interface in all MST instances.
Configuring Optional Spanning-Tree Features
These sections contain this configuration information:
- Default Optional Spanning-Tree Configuration
- Optional Spanning-Tree Configuration Guidelines
- Enabling Port Fast (optional)
- Enabling BPDU Guard (optional)
- Enabling BPDU Filtering (optional)
- Enabling UplinkFast for Use with Redundant Links (optional)
- Enabling BackboneFast (optional)
- Enabling EtherChannel Guard (optional)
- Enabling Root Guard (optional)
- Enabling Loop Guard (optional)
Default Optional Spanning-Tree Configuration
Table 23-1 shows the default optional spanning-tree configuration.
|
|
|
|---|---|
Globally disabled (unless they are individually configured per interface). |
|
Optional Spanning-Tree Configuration Guidelines
You can configure PortFast, BPDU guard, BPDU filtering, EtherChannel guard, root guard, or loop guard if your switch is running PVST+, rapid PVST+, or MSTP.
You can configure the UplinkFast or the BackboneFast feature for rapid PVST+ or for the MSTP, but the feature remains disabled (inactive) until you change the spanning-tree mode to PVST+.
Enabling Port Fast
An interface with the Port Fast feature enabled is moved directly to the spanning-tree forwarding state without waiting for the standard forward-time delay.

If you enable the voice VLAN feature, the Port Fast feature is automatically enabled. When you disable voice VLAN, the Port Fast feature is not automatically disabled. For more information, see Chapter18, “Configuring Voice VLAN”
You can enable this feature if your switch is running PVST+, rapid PVST+, or MSTP.
Beginning in privileged EXEC mode, follow these steps to enable Port Fast. This procedure is optional.

Note![]() You can use the spanning-tree portfast default global configuration command to globally enable the Port Fast feature on all nontrunking ports.
You can use the spanning-tree portfast default global configuration command to globally enable the Port Fast feature on all nontrunking ports.
To disable the Port Fast feature, use the spanning-tree portfast disable interface configuration command.
Enabling BPDU Guard
When you globally enable BPDU guard on ports that are Port Fast-enabled (the ports are in a Port Fast-operational state), spanning tree continues to run on the ports. They remain up unless they receive a BPDU.
In a valid configuration, Port Fast-enabled ports do not receive BPDUs. Receiving a BPDU on a Port Fast-enabled port means an invalid configuration, such as the connection of an unauthorized device, and the BPDU guard feature puts the port in the error-disabled state. When this happens, the switch shuts down the entire port on which the violation occurred.
To prevent the port from shutting down, you can use the errdisable detect cause bpduguard shutdown vlan global configuration command to shut down just the offending VLAN on the port where the violation occurred.
The BPDU guard feature provides a secure response to invalid configurations because you must manually put the port back in service. Use the BPDU guard feature in a service-provider network to prevent an access port from participating in the spanning tree.

You also can use the spanning-tree bpduguard enable interface configuration command to enable BPDU guard on any port without also enabling the Port Fast feature. When the port receives a BPDU, it is put it in the error-disabled state.
You can enable the BPDU guard feature if your switch is running PVST+, rapid PVST+, or MSTP.
Beginning in privileged EXEC mode, follow these steps to globally enable the BPDU guard feature. This procedure is optional.
|
|
|
|
|---|---|---|
Specify the interface connected to an end station, and enter interface configuration mode. |
||
To disable BPDU guard, use the no spanning-tree portfast bpduguard default global configuration command.
You can override the setting of the no spanning-tree portfast bpduguard default global configuration command by using the spanning-tree bpduguard enable interface configuration command.
Enabling BPDU Filtering
When you globally enable BPDU filtering on Port Fast-enabled interfaces, it prevents interfaces that are in a Port Fast-operational state from sending or receiving BPDUs. The interfaces still send a few BPDUs at link-up before the switch begins to filter outbound BPDUs. You should globally enable BPDU filtering on a switch so that hosts connected to these interfaces do not receive BPDUs. If a BPDU is received on a Port Fast-enabled interface, the interface loses its Port Fast-operational status, and BPDU filtering is disabled.

You can also use the spanning-tree bpdufilter enable interface configuration command to enable BPDU filtering on any interface without also enabling the Port Fast feature. This command prevents the interface from sending or receiving BPDUs.

You can enable the BPDU filtering feature if your switch is running PVST+, rapid PVST+, or MSTP.
Beginning in privileged EXEC mode, follow these steps to globally enable the BPDU filtering feature. This procedure is optional.
|
|
|
|
|---|---|---|
Specify the interface connected to an end station, and enter interface configuration mode. |
||
To disable BPDU filtering, use the no spanning-tree portfast bpdufilter default global configuration command.
You can override the setting of the no spanning-tree portfast bpdufilter default global configuration command by using the spanning-tree bpdufilter enable interface configuration command.
Enabling UplinkFast for Use with Redundant Links
UplinkFast cannot be enabled on VLANs that have been configured with a switch priority. To enable UplinkFast on a VLAN with switch priority configured, first restore the switch priority on the VLAN to the default value by using the no spanning-tree vlan vlan-id priority global configuration command.

Note![]() When you enable UplinkFast, it affects all VLANs on the switch. You cannot configure UplinkFast on an individual VLAN.
When you enable UplinkFast, it affects all VLANs on the switch. You cannot configure UplinkFast on an individual VLAN.
You can configure the UplinkFast feature for rapid PVST+ or for the MSTP, but the feature remains disabled (inactive) until you change the spanning-tree mode to PVST+.
Beginning in privileged EXEC mode, follow these steps to enable UplinkFast. This procedure is optional.
When UplinkFast is enabled, the switch priority of all VLANs is set to 49152. If you change the path cost to a value less than 3000 and you enable UplinkFast or UplinkFast is already enabled, the path cost of all interfaces and VLAN trunks is increased by 3000 (if you change the path cost to 3000 or above, the path cost is not altered). The changes to the switch priority and the path cost reduce the chance that a switch will become the root switch.
When UplinkFast is disabled, the switch priorities of all VLANs and path costs of all interfaces are set to default values if you did not modify them from their defaults.
To return the update packet rate to the default setting, use the no spanning-tree uplinkfast max-update-rate global configuration command. To disable UplinkFast, use the no spanning-tree uplinkfast command.
Enabling BackboneFast
You can enable BackboneFast to detect indirect link failures and to start the spanning-tree reconfiguration sooner.

Note![]() If you use BackboneFast, you must enable it on all switches in the network. BackboneFast is not supported on Token Ring VLANs. This feature is supported for use with third-party switches.
If you use BackboneFast, you must enable it on all switches in the network. BackboneFast is not supported on Token Ring VLANs. This feature is supported for use with third-party switches.
You can configure the BackboneFast feature for rapid PVST+ or for the MSTP, but the feature remains disabled (inactive) until you change the spanning-tree mode to PVST+.
Beginning in privileged EXEC mode, follow these steps to enable BackboneFast. This procedure is optional.
|
|
|
|
|---|---|---|
To disable the BackboneFast feature, use the no spanning-tree backbonefast global configuration command.
Enabling EtherChannel Guard
You can enable EtherChannel guard to detect an EtherChannel misconfiguration if your switch is running PVST+, rapid PVST+, or MSTP.
Beginning in privileged EXEC mode, follow these steps to enable EtherChannel guard. This procedure is optional.
|
|
|
|
|---|---|---|
To disable the EtherChannel guard feature, use the no spanning-tree etherchannel guard misconfig global configuration command.
You can use the show interfaces status err-disabled privileged EXEC command to show which switch ports are disabled because of an EtherChannel misconfiguration. On the remote device, you can enter the show etherchannel summary privileged EXEC command to verify the EtherChannel configuration.
After the configuration is corrected, enter the shutdown and no shutdown interface configuration commands on the port-channel interfaces that were misconfigured.
Enabling Root Guard
Root guard enabled on an interface applies to all the VLANs to which the interface belongs. Do not enable the root guard on interfaces to be used by the UplinkFast feature. With UplinkFast, the backup interfaces (in the blocked state) replace the root port in the case of a failure. However, if root guard is also enabled, all the backup interfaces used by the UplinkFast feature are placed in the root-inconsistent state (blocked) and are prevented from reaching the forwarding state.

Note![]() You cannot enable both root guard and loop guard at the same time.
You cannot enable both root guard and loop guard at the same time.
You can enable this feature if your switch is running PVST+, rapid PVST+, or MSTP.
Beginning in privileged EXEC mode, follow these steps to enable root guard on an interface. This procedure is optional.
|
|
|
|
|---|---|---|
Specify an interface to configure, and enter interface configuration mode. |
||
To disable root guard, use the no spanning-tree guard interface configuration command.
Enabling Loop Guard
You can use loop guard to prevent alternate or root ports from becoming designated ports because of a failure that leads to a unidirectional link. This feature is most effective when it is configured on the entire switched network. Loop guard operates only on interfaces that are considered point-to-point by the spanning tree.

Note![]() You cannot enable both loop guard and root guard at the same time.
You cannot enable both loop guard and root guard at the same time.
You can enable this feature if your switch is running PVST+, rapid PVST+, or MSTP.
Beginning in privileged EXEC mode, follow these steps to enable loop guard. This procedure is optional.
|
|
|
|
|---|---|---|
To globally disable loop guard, use the no spanning-tree loopguard default global configuration command. You can override the setting of the no spanning-tree loopguard default global configuration command by using the spanning-tree guard loop interface configuration command.
Displaying the Spanning-Tree Status
To display the spanning-tree status, use one or more of the privileged EXEC commands in Table 23-2 :
You can clear spanning-tree counters by using the clear spanning-tree [ interface interface-id ] privileged EXEC command.
For information about other keywords for the show spanning-tree privileged EXEC command, see the command reference for this release.
 Feedback
Feedback