There are many
reasons to configure access lists; for example, you can use access lists to
restrict contents of switching updates or to provide traffic flow control. One
of the most important reasons to configure access lists is to provide a basic
level of security for your network by controlling access to it. If you do not
configure access lists on your device, all packets passing through the device
could be allowed onto all parts of your network.
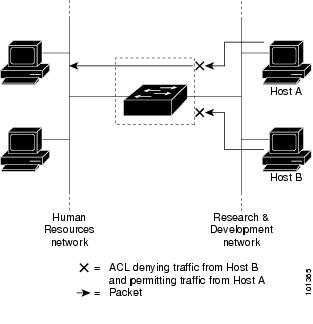
An access list can
allow one host to access a part of your network and prevent another host from
accessing the same area. For example, by applying an appropriate access list to
interfaces of a device, Host A is allowed to access the human resources network
and Host B is prevented from accessing the human resources network.
You can use access
lists on a device that is positioned between two parts of your network, to
control traffic entering or exiting a specific part of your internal network.
To provide some
security benefits of access lists, you should at least configure access lists
on border devices—devices located at the edges of your networks. Such an access
list provides a basic buffer from the outside network or from a less controlled
area of your own network into a more sensitive area of your network. On these
border devices, you should configure access lists for each network protocol
configured on the device interfaces. You can configure access lists so that
inbound traffic or outbound traffic or both are filtered on an interface.
Access lists are
defined on a per-protocol basis. In other words, you should define access lists
for every protocol enabled on an interface if you want to control traffic flow
for that protocol.

 Feedback
Feedback