Configuring Layer 3 Virtualization
This chapter describes how to configure Layer 3 virtualization on the Cisco NX-OS device.
About Layer 3 Virtualization
Cisco NX-OS supports multiple virtual routing and forwarding instances (VRFs). Each VRF contains a separate address space with unicast and multicast route tables for IPv4 and IPv6 and makes routing decisions independent of any other VRF.
Each router has a default VRF and a management VRF:
- The management VRF is for management purposes only.
- Only the mgmt 0 interface can be in the management VRF.
- The mgmt 0 interface cannot be assigned to another VRF.
- No routing protocols can run in the management VRF (static only).
- All Layer 3 interfaces exist in the default VRF until they are assigned to another VRF.
- Routing protocols run in the default VRF context unless another VRF context is specified.
- The default VRF uses the default routing context for all show commands.
- The default VRF is similar to the global routing table concept in Cisco IOS.
VRF and Routing
All unicast and multicast routing protocols support VRFs. When you configure a routing protocol in a VRF, you set routing parameters for the VRF that are independent of routing parameters in another VRF for the same routing protocol instance.
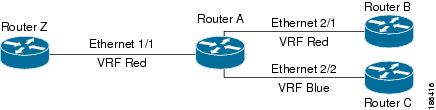
You can assign interfaces and route protocols to a VRF to create virtual Layer 3 networks. An interface exists in only one VRF. Figure 13-1 shows one physical network split into two virtual networks with two VRFs. Routers Z, A, and B exist in VRF Red and form one address domain. These routers share route updates that do not include Router C because Router C is configured in a different VRF.
By default, Cisco NX-OS uses the VRF of the incoming interface to select which routing table to use for a route lookup. You can configure a route policy to modify this behavior and set the VRF that Cisco NX-OS uses for incoming packets.
Route Leaking and Importing Routes from the Default VRF
Cisco NX-OS supports route leaking (import or export) between VRFs.
You can import IP prefixes from the global routing table (the default VRF) into any other VRF by using an import policy. The VRF import policy uses a route map to specify the prefixes to be imported into a VRF. The policy can import IPv4 and IPv6 unicast prefixes.

Note![]() Routes in the BGP default VRF can be imported directly. Any other routes in the default VRF should be redistributed into BGP first.
Routes in the BGP default VRF can be imported directly. Any other routes in the default VRF should be redistributed into BGP first.
IP prefixes are defined as match criteria for the import route map through standard route policy filtering mechanisms. For example, you can create an IP prefix list or an as-path filter to define an IP prefix or IP prefix range and use that prefix list or as-path filter in a match clause for the route map. Prefixes that pass through the route map are imported into the specified VRF using the import policy. IP prefixes that are imported into a VRF through this import policy cannot be reimported into another VRF.
For more information, see the “Guidelines and Limitations for VRF Route Leaking” section.
VRF-Aware Services
A fundamental feature of the Cisco NX-OS architecture is that every IP-based feature is VRF aware.
The following VRF-aware services can select a particular VRF to reach a remote server or to filter information based on the selected VRF:
- AAA—See the Cisco Nexus 9000 Series NX-OS Security Configuration Guide for more information.
- Call Home—See the Cisco Nexus 9000 Series NX-OS System Management Configuration Guide for more information.
- DNS—See Chapter 4, “Configuring DNS” for more information.
- HTTP—See the Cisco Nexus 9000 Series NX-OS Fundamentals Configuration Guide for more information.
- HSRP—See “Configuring HSRP,” for more information.
- NTP—See the Cisco Nexus 9000 Series NX-OS System Management Configuration Guide for more information.
- RADIUS—See the Cisco Nexus 9000 Series NX-OS Security Configuration Guide for more information.
- Ping and Traceroute —See the Cisco Nexus 9000 Series NX-OS Fundamentals Configuration Guide for more information.
- SSH—See the Cisco Nexus 9000 Series NX-OS Security Configuration Guide for more information.
- SNMP—See the Cisco Nexus 9000 Series NX-OS System Management Configuration Guide for more information.
- Syslog—See the Cisco Nexus 9000 Series NX-OS System Management Configuration Guide for more information.
- TACACS+—See the Cisco Nexus 9000 Series NX-OS Security Configuration Guide for more information.
- TFTP—See the Cisco Nexus 9000 Series NX-OS Fundamentals Configuration Guide for more information.
- VRRP—See “Configuring VRRP,” for more information.
- XML—See the Cisco NX-OS XML Management Interface User Guide for more information.
See the appropriate configuration guide for each service for more information on configuring VRF support in that service.
Reachability
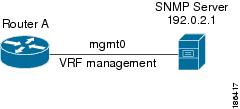
Reachability indicates which VRF contains the routing information needed to get to the server providing the service. For example, you can configure an SNMP server that is reachable on the management VRF. When you configure that server address on the router, you also configure which VRF that Cisco NX-OS must use to reach the server.
Figure 13-2 shows an SNMP server that is reachable over the management VRF. You configure Router A to use the management VRF for the SNMP server host 192.0.2.1.
Figure 13-2 Service VRF Reachability
Filtering
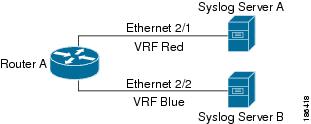
Filtering allows you to limit the type of information that goes to a VRF-aware service based on the VRF. For example, you can configure a syslog server to support a particular VRF. Figure 13-3 shows two syslog servers with each server supporting one VRF. syslog server A is configured in VRF Red, so Cisco NX-OS sends only system messages generated in VRF Red to syslog server A.
Figure 13-3 Service VRF Filtering
Combining Reachability and Filtering
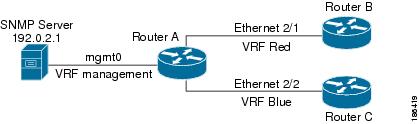
You can combine reachability and filtering for VRF-aware services. You can configure the VRF that Cisco NX-OS uses to connect to that service as well as the VRF that the service supports. If you configure a service in the default VRF, you can optionally configure the service to support all VRFs.
Figure 13-4 shows an SNMP server that is reachable on the management VRF. You can configure the SNMP server to support only the SNMP notifications from VRF Red, for example.
Figure 13-4 Service VRF Reachability Filtering
Licensing Requirements for VRFs
The following table shows the licensing requirements for this feature:
Guidelines and Limitations for VRFs
VRFs have the following configuration guidelines and limitations:
- When you make an interface a member of an existing VRF, Cisco NX-OS removes all Layer 3 configurations. You should configure all Layer 3 parameters after adding an interface to a VRF.
- You should add the mgmt0 interface to the management VRF and configure the mgmt0 IP address and other parameters after you add it to the management VRF.
- If you configure an interface for a VRF before the VRF exists, the interface is operationally down until you create the VRF.
- Cisco NX-OS creates the default and management VRFs by default. You should make the mgmt0 interface a member of the management VRF.
- The write erase boot command does not remove the management VRF configurations. You must use the write erase command and then the write erase boot command.
Guidelines and Limitations for VRF Route Leaking
VRF route leaking has the following configuration guidelines and limitations:
- Route leaking is supported between any two non-default VRFs and from the default VRF to a non-default VRF.
- You can restrict route leaking to specific routes using route map filters to match designated IP addresses.
- By default, the maximum number of IP prefixes that can be imported from the default VRF into a non-default VRF is 1000 routes.
- There is no limit on the number of routes that can be leaked between two non-default VRFs.
- VRF route leaking requires an Enterprise license, and BGP must be enabled.
Default Settings
Table 13-1 lists the default settings for VRF parameters.
|
|
|
|---|---|
Configuring VRFs
This section contains the following topics:
- Creating a VRF
- Assigning VRF Membership to an Interface
- Configuring VRF Parameters for a Routing Protocol
- Configuring a VRF-Aware Service
- Setting the VRF Scope

Note![]() If you are familiar with the Cisco IOS CLI, be aware that the Cisco NX-OS commands for this feature might differ from the Cisco IOS commands that you would use.
If you are familiar with the Cisco IOS CLI, be aware that the Cisco NX-OS commands for this feature might differ from the Cisco IOS commands that you would use.
Creating a VRF
SUMMARY STEPS
3.![]() (Optional) ip route {ip-prefix | ip-addr ip-mask} {[next-hop | nh-prefix] | [interface next-hop | nh-prefix]} [tag tag-value [pref]
(Optional) ip route {ip-prefix | ip-addr ip-mask} {[next-hop | nh-prefix] | [interface next-hop | nh-prefix]} [tag tag-value [pref]
DETAILED STEPS
To delete the VRF and the associated configuration, use the following command in global configuration mode:
|
|
|
|---|---|
Any commands available in global configuration mode are also available in VRF configuration mode.
This example shows how to create a VRF and add a static route to the VRF:
switch(config)# vrf context Enterprise
Assigning VRF Membership to an Interface
BEFORE YOU BEGIN
Assign the IP address for an interface after you have configured the interface for a VRF.
SUMMARY STEPS
2.![]() interface interface-type slot/port
interface interface-type slot/port
4.![]() ip-address ip-prefix/length
ip-address ip-prefix/length
5.![]() (Optional) show vrf vrf-name interface interface-type number
(Optional) show vrf vrf-name interface interface-type number
DETAILED STEPS
This example shows how to add an interface to the VRF:
switch(config)# interface ethernet 1/2
switch(config-if)# vrf member RemoteOfficeVRF
Configuring VRF Parameters for a Routing Protocol
You can associate a routing protocol with one or more VRFs. See the appropriate chapter for information on how to configure VRFs for the routing protocol. This section uses OSPFv2 as an example protocol for the detailed configuration steps.
SUMMARY STEPS
4.![]() (Optional) maximum-paths paths
(Optional) maximum-paths paths
5.![]() interface interface-type slot/port
interface interface-type slot/port
7.![]() ip address ip-prefix/length
ip address ip-prefix/length
DETAILED STEPS
This example shows how to create a VRF and add an interface to the VRF:
switch(config)# vrf context RemoteOfficeVRF
switch(config)# router ospf 201
switch(config-router)# vrf RemoteOfficeVRF
switch(config-router-vrf)# maximum-paths 4
switch(config-router-vrf)# interface ethernet 1/2
switch(config-if)# vrf member RemoteOfficeVRF
switch(config-if)# ip address 192.0.2.1/16
Configuring a VRF-Aware Service
You can configure a VRF-aware service for reachability and filtering. See the “VRF-Aware Services” section for links to the appropriate chapter or configuration guide for information on how to configure the service for VRFs. This section uses SNMP and IP domain lists as example services for the detailed configuration steps.
SUMMARY STEPS
2.![]() snmp-server host ip-address [filter-vrf vrf-name] [use-vrf vrf-name]
snmp-server host ip-address [filter-vrf vrf-name] [use-vrf vrf-name]
4.![]() ip domain-list domain-name [ all-vrfs ][ use-vrf vrf-name ]
ip domain-list domain-name [ all-vrfs ][ use-vrf vrf-name ]
DETAILED STEPS
This example shows how to send SNMP information for all VRFs to SNMP host 192.0.2.1, reachable on VRF Red:
switch(config)# snmp-server host 192.0.2.1 for-all-vrfs use-vrf Red
switch(config)# copy running-config startup-config
This example shows how to filter SNMP information for VRF Blue to SNMP host 192.0.2.12, reachable on VRF Red:
switch(config)# vrf context Blue
Setting the VRF Scope
You can set the VRF scope for all EXEC commands (for example, show commands). This automatically restricts the scope of the output of EXEC commands to the configured VRF. You can override this scope by using the VRF keywords available for some EXEC commands.
To set the VRF scope, use the following command in EXEC mode:
|
|
|
|---|---|
Sets the routing context for all EXEC commands. Default routing context is the default VRF. |
To return to the default VRF scope, use the following command in EXEC mode:
|
|
|
|---|---|
Verifying the VRF Configuration
To display VRF configuration information, perform one of the following tasks:
|
|
|
|---|---|
Configuration Examples for VRF
This example shows how to configure VRF Red, add an SNMP server to that VRF, and add an instance of OSPF to VRF Red:
snmp-server host 192.0.2.12 use-vrf Red
This example shows how to configure VRF Red and Blue, add an instance of OSPF to each VRF, and create an SNMP context for each OSPF instance in each VRF:
Additional References
For additional information related to implementing virtualization, see the following sections:
Related Documents
|
|
|
|---|---|
Cisco Nexus 9000 Series NX-OS Fundamentals Configuration Guide |
Standards
|
|
|
|---|---|
No new or modified standards are supported by this feature, and support for existing standards has not been modified by this feature. |
 Feedback
Feedback