Reading, Discarding, and Deploying Configuration Changes
Read All Device Configurations
If a configuration change is made to a device outside of Security Cloud Control, the device configuration stored on Security Cloud Control and the device's local copy of its configuration are no longer the same. You many want to overwrite Security Cloud Control's copy of the device's configuration with the configuration stored on the device to make the configurations the same again. You can perform this task on many devices simultaneously using the Read All link.
For more information about how Security Cloud Control manages the two copies of the device configuration, refer to Reading, Discarding, Checking for, and Deploying Configuration Changes.
Here are three configuration statuses where clicking Read All will overwrite Security Cloud Control's copy of the device's configuration with the device's copy of the configuration.
-
Conflict Detected: If conflict detection is enabled, Security Cloud Control polls the devices it manages every 10 minutes for changes made to their configurations. If Security Cloud Control finds that the configuration on the device has changed, Security Cloud Control displays a "Conflict detected" configuration status for the device.
-
Synced: If the device is in a synced state, and you click Read All, Security Cloud Control immediately checks the devices to determine if there have been any changes made to its configurations directly. After clicking Read All, Security Cloud Control confirms your intent to overwrite its copy of the device's configuration and then Security Cloud Control performs the overwrite.
-
Not Synced: If the device is in the Not Synced state, and you click Read All, Security Cloud Control warns you that there are pending changes made to the device's configuration using Security Cloud Control and that proceeding with the Read All operation will delete those changes and then overwrite Security Cloud Control's copy of the configuration with the configuration on the device. This Read All functions like Discard Changes.
Procedure
|
Step 1 |
From the Security Cloud Control Home page, click Firewall. |
|
Step 2 |
Choose . |
|
Step 3 |
Click the Devices tab. |
|
Step 4 |
Click the appropriate device type tab. |
|
Step 5 |
(Optional) Create a change request label to identify the results of this bulk action easily in the change log. |
|
Step 6 |
Select the devices whose configurations you want to save in Security Cloud Control. |
|
Step 7 |
Click Read All to continue. |
|
Step 8 |
Look at the notifications tab for the progress of the Read All configurations operation. If you want more information about how individual actions in the bulk operation succeeded or failed, click the blue Review link and you will be directed to the Jobs page. |
|
Step 9 |
If you created and activated a change request label, remember to clear it so that you don't inadvertently associate other configuration changes with this event. |
Read Configuration Changes from FDM-Managed Device to Security Cloud Control
Why Does Security Cloud Control Read FDM-managed device Configurations?
In order to manage an FDM-managed device, Security Cloud Control must have its own stored copy of the FDM-managed device's configuration. When Security Cloud Control reads a configuration from an FDM-managed device, it takes a copy of the FDM-managed device's deployed configuration and saves it to its own database. The first time Security Cloud Control reads and saves a copy of the device's configuration file is when the device is onboarded. See Reading, Discarding, Checking for, and Deploying Configuration Changes for more information.
Pending and Deployed Changes
Configuration changes made to the FDM-managed device directly through the Firepower Device Manager (FDM) or its CLI are referred to as staged changes on the FDM-managed device until they are deployed. A staged, or pending, change can be edited or deleted without having any affect on traffic running through the FDM-managed device. Once the pending changes are deployed, however, they are enforced by the FDM-managed device and affect traffic running through the device.
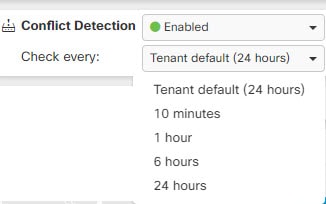
Conflict Detected
If you enable Conflict Detection on the device, Security Cloud Control checks for configuration changes every 10 minutes. If the copy of the configuration stored on the device has changed, Security Cloud Control notifies you by displaying the "Conflict Detected" configuration status. If you do not have Conflict Detection enabled, or a change has been made to the device's configuration within the 10 minute interval between automatic polling, clicking Check for Changes prompts Security Cloud Control to immediately compare the copy of the configuration on the device with the copy of the configuration stored on Security Cloud Control. You can choose to Review Conflict to examine the differences between the device configuration and the configuration saved to Security Cloud Control, then select Discard Changes to remove the staged changes and revert to the saved configuration or confirm the changes. You can also choose to Accept without Review; this option takes the configuration and overwrites what is currently saved to Security Cloud Control.
Discard Changes Procedure
To discard configuration changes from the FDM-managed device, follow this procedure:
Procedure
|
Step 1 |
In the left pane, click . |
||||
|
Step 2 |
Click the Devices tab. |
||||
|
Step 3 |
Click the appopriate device type tab. |
||||
|
Step 4 |
Select the device whose configuration is set to Conflict Detected and gives you the link to Revert Pending Changes. The message explains that you can click the link to revert pending changes or you can log on to the device using the local manager FDM and deploy the changes first.
|
||||
|
Step 5 |
Review the changes on FDM before clicking Revert Pending Changes:
|
If Reverting Pending Changes Fails
Changes to the system databases and security feeds can't be reverted by Security Cloud Control. Security Cloud Control recognizes that there are pending changes, attempts to revert them and then fails. To determine if the revert failure is
due to pending database updates or security feed updates, log into the device's FDM console. It will have an orange circle
indicating that there are changes ready to deploy  . Click the deploy button to review the pending changes and deploy them or discard them as is appropriate.
. Click the deploy button to review the pending changes and deploy them or discard them as is appropriate.
Review Conflict Procedure
To review configuration changes from the FDM-managed device, follow this procedure:
Procedure
|
Step 1 |
In the left pane, click . |
||
|
Step 2 |
Click the Devices tab. |
||
|
Step 3 |
Click the appropriate device type tab. |
||
|
Step 4 |
Select the device whose configuration is marked Conflict Detected and gives you a link to Review Conflict in the Conflict Detected pane on the right. |
||
|
Step 5 |
Click Review Conflict. |
||
|
Step 6 |
Compare the two configurations presented to you. |
||
|
Step 7 |
Take one of these actions:
|
Accept Without Review Procedure
To accept configuration changes from the FDM-managed device without reviewing, follow this procedure:
Procedure
|
Step 1 |
In the left pane, click the tab. |
|
Step 2 |
Click the appopriate device type tab. |
|
Step 3 |
Select the device whose configuration is marked Conflict Detected and gives you a link to Accept Without Review in the Conflict Detected pane on the right. |
|
Step 4 |
Click Accept Without Review. Security Cloud Control accepts and overwrites the current configuration. |
Preview and Deploy Configuration Changes for All Devices
Security Cloud Control informs you when you have made a configuration change to a device in your
organization, but you have not deployed that change, by displaying an
orange dot on the Deploy icon  . The devices affected by these changes show the status "Not Synced" in the
Security Devices page. By clicking
Deploy, you can review which devices have pending changes
and deploy the changes to those devices.
. The devices affected by these changes show the status "Not Synced" in the
Security Devices page. By clicking
Deploy, you can review which devices have pending changes
and deploy the changes to those devices.
This deployment method is available for all supported devices.
You can use this deployment method for single configuration changes or wait and deploy multiple changes at once.
This deployment method is only available when Security Cloud Control Firewall Management has been onboarded to Security Cloud Control.
Procedure
|
Step 1 |
In the menu bar of Security Cloud Control click the Deploy button |
|
Step 2 |
Select the devices with changes you want to deploy. If a device has a yellow caution triangle, you cannot deploy changes to that device. Hover your mouse over the yellow caution triangle to find out why you can't deploy changes to that device. |
|
Step 3 |
(Optional) If you want to see more information about a pending change, click the View Detailed Change log link to open the change log associated with that change. Click the Deploy icon to return to the Devices with Pending Changes page. |
|
Step 4 |
Click Deploy Now to deploy the changes immediately to the devices you selected. You'll see the progress in the Active jobs indicator in the Jobs tray. |
|
Step 5 |
(Optional) After the deployment has finished, in the Platform menu, click Firewall, and then select . You will see a recent "Deploy Changes" job showing the results of the deployment. |
Deploy Configuration Changes from Security Cloud Control to FDM-Managed Device
Why Does Security Cloud Control Deploy Changes to an FDM-Managed Device?
As you manage and make changes to a device's configuration with Security Cloud Control, Security Cloud Control saves the changes you make to its own copy of the configuration file. Those changes are considered staged on Security Cloud Control until they are deployed to the device. Staged configuration changes have no effect on the network traffic running through the device. Only after Security Cloud Control deploys the changes to the device do they have an affect on the traffic running through the device. When Security Cloud Control deploys changes to the device's configuration, it only overwrites those elements of the configuration that were changed. It does not not overwrite the entire configuration file stored on the device.
Like Security Cloud Control, FDM-managed device has the concept of pending changes and deployed changes. Pending changes on FDM-managed device are the equivalent of staged changes on Security Cloud Control. A pending change can be edited or deleted without having any affect on traffic running through the FDM-managed device. Once the pending changes are deployed, however, they are enforced by the FDM-managed device and affect traffic running through the device.
Because of FDM-managed devices two step process for editing configuration files, Security Cloud Control deploys changes to an FDM-managed device slightly differently than it does to other devices it manages. Security Cloud Control first deploys the changes to FDM-managed device and the changes are in the pending state. Then, Security Cloud Control deploys the changes on the devices and they become live. Now that the changes have been deployed, they are enforced and affect traffic running through the FDM-managed device. This applies to both standalone and high availability (HA) devices.
Deployments can be initiated for a single device or on more than one device simultaneously. You can schedule individual deployments or recurring deployments for a single device.
Two things will prevent Security Cloud Control from deploying changes to an FDM-managed device:
-
If there are staged changes on the FDM-managed device. See Conflict Detected for more information on how to resolve this state.
-
Security Cloud Control does not deploy changes if there are changes in the process of being deployed to the FDM-managed device.
Scheduling Automatic Deployments
You can also configure your tenant to schedule deployments to a single device with pending changes scheduling automatic deployments.
Deploy Changes to a Device
Procedure
|
Step 1 |
When you make a configuration change for a device using Security Cloud Control and save it, that change is saved in the Security Cloud Control instance of the device configuration. |
|
Step 2 |
From the Security Cloud Control Home page, click Firewall. |
|
Step 3 |
Choose . |
|
Step 4 |
Click the Devices tab. |
|
Step 5 |
Click the appropriate device type tab. The configuration status of the device will display "Not synced" after you make changes. |
|
Step 6 |
To deploy the changes, select one of these methods:
|
Cancelling Changes
If, when deploying a change from Security Cloud Control to a device, you click Cancel, the changes you made are not deployed to the device. The process is canceled. The changes you made are still pending on Security Cloud Control and can be edited further before you finally deploy them to FDM-managed device.
Discarding Changes
If, when previewing changes, you click Discard all, the changes you made, and any other changes any other user made but did not deploy to the device, are deleted. Security Cloud Control reverts its pending configuration to the last read or deployed configuration before any changes were made.
Bulk Deploy Device Configurations
If you have made changes to multiple devices, for instance by editing a shared object, you can apply those change to all of the affected devices at once:
Procedure
|
Step 1 |
In the left pane, click . |
||
|
Step 2 |
Click the Devices tab. |
||
|
Step 3 |
Click the appropriate device type tab. |
||
|
Step 4 |
Select all of the devices for which you have made configuration changes on Security Cloud Control. These devices should show "Not Synced" status. |
||
|
Step 5 |
Deploy the changes using one of these methods:
|
||
|
Step 6 |
(Optional) Click the Jobs icon |
About Scheduled Automatic Deployments
Using Security Cloud Control, you can make configuration changes to one or more of the devices it manages and then schedule the changes to be deployed to those devices at a time that is convenient for you.
You can only schedule deployments if you Enable scheduled automatic deployments in the Tenant Settings tab of the Settings page. Once this option is enabled, you can create, edit, or delete scheduled deployments. A scheduled deployment deploys all the staged changes saved on Security Cloud Control at the date and time set. You can also view and delete scheduled deployments from the Jobs page.
If there were changes made directly to the device that have not been read to Security Cloud Control, the scheduled deployment will be skipped until that conflict is resolved. The Jobs page will list any instance where a scheduled deployment fails. If Enable the Option to Schedule Automatic Deployments is turned off, all scheduled deployments are deleted.
 Caution |
If you schedule a new deployment for multiple devices, and some of those devices already have deployments scheduled, the new scheduled deployment overwrites the existing scheduled deployments. |
 Note |
When you create a scheduled deployment, the schedule is created in your local time, not in the time zone of the device. Scheduled deployments do not automatically adjust for daylight savings time. |
Schedule an Automatic Deployment
The deployment schedule can be a single event or a recurring event. You may find recurring automatic deployments a convenient way to line up recurring deployments with your maintenance window. Follow this procedure to schedule a one-time or a recurring deployment for a single device.
 Important |
This procedure applies only to ASAs and FDM-managed devices. To schedule deployments for Secure Firewall Threat Defense devices managed by on-premises Firewall Management Center or Cloud-Delivered Firewall Management Center, see Scheduling. |
 Note |
If you schedule a deployment for a device that has an existing deployment scheduled, the new scheduled deployment overwrites the existing deployment. |
Procedure
|
Step 1 |
From the Security Cloud Control home page, choose . |
|
Step 2 |
Click the Devices tab. |
|
Step 3 |
Click the appropriate device type tab. |
|
Step 4 |
Select one ore more devices. |
|
Step 5 |
In the Device Details pane, locate the Scheduled Deployments tab and click Schedule. |
|
Step 6 |
Select when the deployment should occur.
|
|
Step 7 |
Click Save. |
Edit a Scheduled Deployment
Follow this procedure to edit a scheduled deployment:
Procedure
|
Step 1 |
From the Security Cloud Control home page, choose . |
|
Step 2 |
Click the Devices tab. |
|
Step 3 |
Click the appropriate device type tab. |
|
Step 4 |
Select one or more devices. |
|
Step 5 |
In the Device Details pane, locate the Scheduled Deployments tab and click Edit . 
|
|
Step 6 |
Edit the recurrence, date, or time of a scheduled deployment. |
|
Step 7 |
Click Save. |
Delete a Scheduled Deployment
Follow this procedure to delete a scheduled deployment:
 Note |
If you schedule a deployment for multiple devices, and then change or delete the schedule for some of the devices, the original scheduled deployment for the remaining devices will be preserved. |
Procedure
|
Step 1 |
From the Security Cloud Control home page, choose . |
|
Step 2 |
Click the Devices tab. |
|
Step 3 |
Click the appropriate device type tab. |
|
Step 4 |
Select one or more devices. |
|
Step 5 |
In the Device Details pane, locate the Scheduled Deployments tab and click Delete
|
What to do next
Check for Configuration Changes
Check for Changes to determine if the device's configuration has been changed directly on the device and it is no longer the same as the copy of the configuration stored on Security Cloud Control. You will see the this option when the device is in the "Synced" state.
To check changes:
Procedure
|
Step 1 |
From the Security Cloud Control home page, choose . |
|
Step 2 |
Click the Devices tab. |
|
Step 3 |
Click the appropriate device type tab. |
|
Step 4 |
Select the device, whose configuration you suspect may have been changed directly on the device. |
|
Step 5 |
Click Check for Changes in the Synced pane on the right. |
|
Step 6 |
The behavior that follows is slightly different depending on the device:
|
Discard Configuration Changes
Click Discard Changes when you want to "undo" all the undeployed configuration changes you made to a device's configuration using Security Cloud Control. When you click Discard Changes, Security Cloud Control completely overwrites its local copy of a device's configuration with the configuration stored on the device.
When you click Discard Changes, your device's configuration status is in a Not Synced state. After you discard your changes, the copy of the configuration on Security Cloud Control will be the same as the copy of the configuration on the device and the configuration status in Security Cloud Control will return to Synced.
To discard, or "undo," all of your undeployed configuration changes for a device:
Procedure
|
Step 1 |
From the Security Cloud Control home page, choose . |
|
Step 2 |
Click the Devices tab. |
|
Step 3 |
Click the appropriate device type tab. |
|
Step 4 |
Select the device you have been making configuration changes to. |
|
Step 5 |
Click Discard Changes in the Not Synced pane on the right.
|
Out-of-Band Changes on Devices
Out-of-band changes refer to changes made directly on the device without using Security Cloud Control. These changes may be made using the device's command-line interface over an SSH connection or by using a local manager like the Adaptive Security Device Manager (ASDM) for the ASA, the FDM for the FDM-managed device, or for an On-Premises Firewall Management Center on the On-Premises Firewall Management Center user interface. An out-of-band change causes a conflict between the device's configuration stored on Security Cloud Control and the configuration stored on the device itself.
Detecting Out-of-Band Changes on Devices
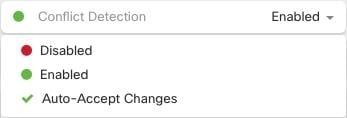
If Conflict Detection is enabled for an ASA, or an FDM-managed device, a Cisco IOS device, or an On-Premises Firewall Management Center, Security Cloud Control checks the device every 10 minutes searching for any new changes made directly to the device's configuration outside of Security Cloud Control.
If Security Cloud Control finds that there are changes to the device's configuration that are not stored on Security Cloud Control, it changes the Configuration Status of that device to the "Conflict Detected" state.
When Security Cloud Control detects a conflict, one of two conditions is likely:
-
There have been configuration changes made to the device directly that have not been saved to Security Cloud Control's database.
-
In the case of an FDM-managed device, there may be "pending" configuration changes on the FDM-managed device that have not been deployed.
-
In the case of an On-Premises Firewall Management Center, there may be changes made, for instance, to objects outside Security Cloud Control, which are pending to be synchronized with Security Cloud Control or changes made in Security Cloud Control which are pending to be deployed to the On-Premises Firewall Management Center.
 on the details pane. Review any warnings and click
on the details pane. Review any warnings and click  in the navigation bar to view the results of the bulk deploy.
in the navigation bar to view the results of the bulk deploy.
 .
.
 Feedback
Feedback