Introduction
This document describes how to collect internal wired Packet Capture(PCAP) from Access Point (AP) Command Line Interface (CLI) with Trivial File Transfer Protocol (TFTP) server.
Contributed by Jasia Ahsan, Cisco TAC Engineer.
Prerequisites
Requirements
Cisco recommends that you have knowledge of these topics:
- CLI access to AP with Secure Shell (SSH) or Console Access.
- TFTP server
- .PCAP files
Components Used
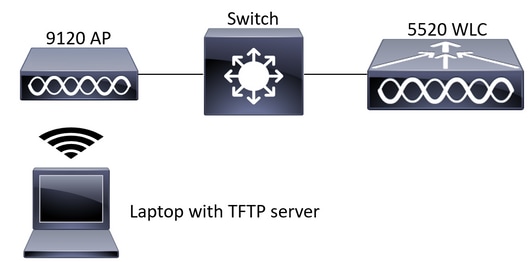
- 5520 Wireless Lan Controller(WLC) on 8.10.112 code.
- AP 9120AXI
- TFTP server
The information in this document was created from the devices in a specific lab environment. All of the devices used in this document started with a cleared (default) configuration. If your network is live, ensure that you understand the potential impact of any command.
Configure
Network Diagram
Configurations
The PCAP configuration has been done with SSH to AP. Three traffic types can be selected IP,TCP and UDP. In this case IP traffic has been selected.
Step 1. Log in to the AP CLI with SSH.
Step 2. Start the PCAP for IP traffic and run this command,
CLI:
# debug traffic wired ip capture
% Writing packets to "/tmp/pcap/2802_capture.pcap0"
#reading from file /dev/click_wired_log, link-type EN10MB (Ethernet)
Step 3. Notice the output is written to a file in /tmp/pcap folder with the AP name added to the pcap file.
Step 4. Start a ping test to capture the IP traffic.
CLI:
#ping 10.201.236.91
Sending 5, 100-byte ICMP Echos to 10.201.236.91, timeout is 2 seconds
!!!!!
Step 5. Stop the capture.
CLI:
#no debug traffic wired ip capture
Step 6. Copy the file to a tftp server.
CLI:
# copy pcap 2802_capture.pcap0 tftp: 10.201.236.33
###################################################################################################################################################### 100.0%
Note: There is a space before the tftp server ip address.
Verify
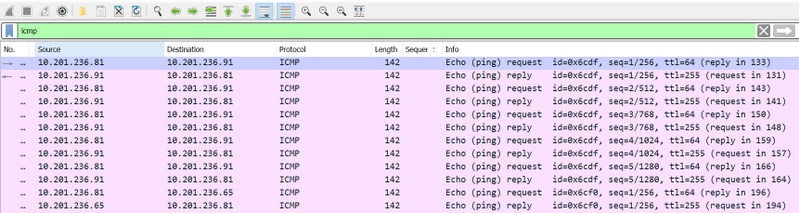
Open the file with any packet analysis tool. Wireshark is used here to open this file.
The ping test results can be seen in the image.
Troubleshoot
There is currently no specific troubleshooting information available for this configuration.
