Troubleshoot FTD Registration Issues with Umbrella
Available Languages
Contents
Issue
The Umbrella Network Devices dashboard shows the Cisco Firewall Management Center (FMC) already integrated and connected. The FMC is also able to pull Umbrella policies to the FMC and deploy them to the Cisco Firewall Threat Defense (FTD). However, the FTD is not able to register to Umbrella to redirect DNS traffic.
Environment
Cisco Secure Firewall Firepower FTD 10.0.0 (Applicable to versions 7.2+)
Firewall Management Center (FMC) version 10.0.0 (Applicable to versions 7.2+)
Deployment in Azure Virtual WAN environment (Applicable to hardware models also)
FMC successfully integrated with Cisco Umbrella
Umbrella DNS Connector configuration on FTD
Resolution
Troubleshooting and Analysis Steps
1: Verify that the FMC is fully integrated and receiving Umbrella DNS policies and that they are deployed to the FTD.
Ensure the certificate is installed and valid.
Validate that the Umbrella token and public key are with resolvers configured.
Ensure that the Umbrella policy has been applied to the FTD and the Umbrella registration status shows 200 SUCCESS.
Firepower# show crypto ca trustpoints Trustpoint Umbrella_Certificate: Subject Name: CN=DigiCert TLS RSA SHA256 2020 CA1 O=DigiCert Inc C=US Serial Number: 0a3508d55c292b017df8ad65c00ff7e4 Certificate configured. firepower# show running-config all umbrella-global umbrella-global token ABCDEFGHIJKLMNOP1234567890987654321 public-key AAAA:BBBB:CCCC:1111:2222:3333:4444:AAAA:BBBB:CCCC:DDDD:1111:2222:3333:4444:5555 timeout edns 0:02:00 resolver ipv4 208.67.220.220 resolver ipv6 2620:119:53::53 firepower# show running-config policy-map type inspect dns ! policy-map type inspect dns preset_dns_map parameters message-length maximum client auto message-length maximum 512 umbrella tag Umbrella_for_FMC_Policy no tcp-inspection firepower# show service-policy inspect dns Global policy: Service-policy: global_policy Class-map: inspection_default Inspect: dns preset_dns_map, packet 5982, lock fail 0, drop 1, reset-drop 0, 5-min-pkt-rate 0 pkts/sec, v6-fail-close 0 sctp-drop-override 0 message-length maximum client auto, drop 0 message-length maximum 512, drop 0 dns-guard, count 2975 protocol-enforcement, drop 0 nat-rewrite, count 0 Umbrella registration: tag: Umbrella_for_FMC_Policy, status: 200 SUCCESS, device-id: 010ac1891448df39, retry 0 Umbrella resolver mode: fail-close Umbrella resolver ipv4: 208.67.220.220 - operational Umbrella resolver ipv6: 2620:119:53::53 - operational Umbrella: bypass 0, req inject 3007 - sent 3007, res recv 3007 - inject 2975, local-domain-bypass 0 Class-map: class_snmp
2: If the Umbrella registration status shows Unknown, use debugs and show commands to validate that a DNS server group is configured on the necessary data interfaces for Umbrella redirection.
firepower# show run dns firepower# debug umbrella firepower# debug dns all firepower# debug ssl 255
Example of failed FTD-Umbrella registration with debugs on FTD CLI due to "No interfaces enabled" for DNS in FTD Platform Settings:
firepower# show run dns
DNS server-group DefaultDNS <== No interfaces enabled
---
Registration Req header: application/json
Host: api.opendns.com
Authorization:OpenDNS,api_key="ABCDEFGHIJKLMNOP1234567890987654321",token="ABCDEFGHIJKLMNOP1234567890987654321"
payload: {"model":"9AU9A8XD6QH","macAddress":"deadbeef0000","tag":"DNS_Policy","label":"cisco_NGFWv","name":"cisco_NGFWv","serialNumber":"SERIAL"}
DNS: get global group DefaultDNS handle 267051f
DNS: Resolve request for 'api.opendns.com' group DefaultDNS
DNS: No interfaces enabled
Response is NULL
odns_cluster_send_device_id_update not ready to send device-id update
odns_ha_send_device_id_update not ready to send device-id update
Registration failed. Retrying...
3: Updating the necessary configurations for platform settings on the FTD does not automatically trigger Umbrella registration again. To force a new registration attempt, restart the DNS inspection service on the FTD from the CLISH prompt:
firepower# show run dns
dns domain-lookup outside
dns domain-lookup inside
DNS server-group DefaultDNS
DNS server-group Umbrella
retries 3
timeout 3
name-server 208.67.220.220
name-server 208.67.222.222
--
Registration Req header: application/json
Host: api.opendns.com
Authorization:OpenDNS,api_key="ABCDEFGHIJKLMNOP1234567890987654321",token="ABCDEFGHIJKLMNOP1234567890987654321"
payload: {"model":"9AU9A8XD6QH","macAddress":"deadbeef0000","tag":"DNS_Policy","label":"cisco_NGFWv","name":"cisco_NGFWv","serialNumber":"SERIAL"}
Response is NULL
odns_cluster_send_device_id_update not ready to send device-id update
odns_ha_send_device_id_update not ready to send device-id update
Registration failed. Retrying...
--
> configure inspection dns disable
> configure inspection dns enable
Example of successful FTD-Umbrella registration with debugs on FTD CLI:
Registration Req header: application/json
Host: api.opendns.com
Authorization:OpenDNS,api_key="09E3D179DF3EC142402CF501361A0BFB",token="1D2ED3B50C59C64C002703447A6B0BF00079A6AB"
payload: {"model":"9AU9A8XD6QH","macAddress":"deadbeef0000","tag":"DNS_Policy_Corporate","label":"cisco-tdv-nva000001_NGFWv","name":"cisco-tdv-nva000001","serialNumber":"SERIAL"}
DNS: get global group Umbrella handle 4a081ff
DNS: Resolve request for 'api.opendns.com' group Umbrella
dns_cache: Lukup ptr created for thread umbrella_reg,members in lookup_ptr_namelist=1 ,total =1
DNS: Selected interface to send out DNS packet outside
DNS: Message Validated
DNS: Converting Response to DNS Cache Entry
DNS: ** Answer Section **
AN(0): Name: api.opendns.com, RR type=1, class=1, ttl=10, datalen=4
DNS: Entry not found in cache, so create one
DNS: namelen 16, txtlen 0
DNS: Reparsing for adding to cache
DNS: hostname is api.opendns.com, RR type=1, class=1, ttl=10, n=4
DNS: Added New Cache Entry
DNS: Added Response to cache
Registration succeeded with deviceID 010a8850c25440ee!
odns_cluster_send_device_id_update not ready to send device-id update
odns_ha_send_device_id_update not ready to send device-id update
Registration process exiting...
4: Review FTD DNS inspection, injection, and redirection to Umbrella using similar debugs.
Umbrella: DNS REQ map transaction id [0xd77c] to [0x83f0] Umbrella: modifying REQ [0x83f0] 10.3.0.4 -> 208.67.220.220 Umbrella: adding edns devid: 010a8850c25440ee Umbrella: modify dst: 208.67.220.220 to 208.67.220.220 dnscrypt_is_ready: CONN inspect 0x0000148f1e216c00, dns_param 0x0000148f1e216c70, flags 2c7, magic_query[0] 71 Umbrella: inject new REQ [0x83f0] downstream flow handle 9a9b0722 Umbrella: create map_id: [0x83f0] aid_entry: 0x0000148f1e203140 Umbrella: send REQ [0x83f0] 10.3.0.4 -> 208.67.220.220 downstream flow handle 9a9b0722. snp_fp_dnscrypt: forward flow 10.3.0.4/52952 --> 208.67.220.220/443; inspect 0x0000148f1e213000 dnscrypt_is_ready: CONN inspect 0x0000148f1e213000, dns_param 0x0000148f1e213070, flags 2c7, magic_query[0] 71 snp_fp_dnscrypt: Received c2s EDNS query pkt from umbrella. dnscrypt_egress_encrypt: Payload just encrypted. snp_fp_dnscrypt: Dispatching the packet. snp_fp_dnscrypt: reverse flow 208.67.220.220/443 --> 192.168.200.245/52952; inspect 0x0000148f1e213000 dnscrypt_is_ready: CONN inspect 0x0000148f1e213000, dns_param 0x0000148f1e213070, flags 2c7, magic_query[0] 71 snp_fp_dnscrypt: Received u2c in upstream flow; try to decrypt. dnscrypt_ingress_decrypt: dns udp 0x0000001193282d22 start 0x0000001193282d2a end 0x0000001193282ed7 wptr 0x0000001193282ed7 dns_len 429. dnscrypt_ingress_decrypt: new dns_len 397. dnscrypt_ingress_decrypt: Payload just decrypted; dns_len 173. dnscrypt_ingress_decrypt: Orig c2s/c2u flow 10.3.0.4/52952 -> 208.67.220.220/443 dnscrypt_ingress_decrypt: Dispatch clear text edns packet -- Umbrella: recv RES [0x83f0] 192.168.200.245 <- 208.67.220.220 Umbrella: umbrella_pull_tranxn: pull flow (0x0000148f0d6baf68) aid_entry 0x0000148f1e203140 (id=33776/0x83f0) use_real 1. Umbrella: umbrella_pull_tranxn: pull found flow (0x0000148f0d6baf68)aid_entry (0x0000148f1e203140) id=33776/0x83f0 use_real 1. Umbrella: umbrella_pull_tranxn: Deleting flow (0x0000148f0d6baf68) aid_entry 0x0000148f1e203140 (id=33776/83f0) use_real 1. Umbrella: modify src: 208.67.220.220 to 208.67.220.220 dnscrypt_is_ready: CONN inspect 0x0000148f1e213000, dns_param 0x0000148f1e213070, flags 2c7, magic_query[0] 71 Umbrella: restore src port: 53 to 53 Umbrella: modified RES [0x83f0] 192.168.200.245 <- 208.67.220.220 Umbrella: inject new RES [0x83f0] snp_dbregex_re_get: Getting regexp table 0x00005594320b9f30 for context 0. umbrella_dbregex_check: matching domain name settings-win.data.microsoft.com (31) against re table 0x00005594320b9f30. umbrella_dbregex_check: matched result 0x0000000000000000; matched len 31 regex id 0.
5: Check Umbrella dashboard Activity logs to verify that the FTD traffic reaches Umbrella and that the Umbrella policies are being applied to it. End-users see a Cisco Umbrella block page indicating denial to specific site categories, based on policy configurations.
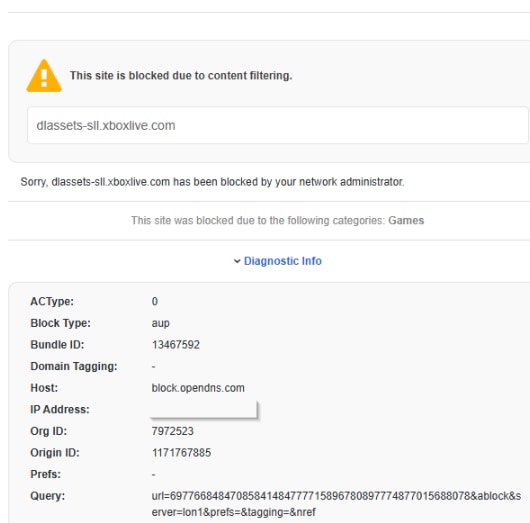 inline_image_0.png
inline_image_0.png
6: Update end-user DNS configuration to use public DNS servers instead of OpenDNS/Umbrella resolvers directly.
Example DNS server configuration change:
Primary DNS: 8.8.8.8 Secondary DNS: 8.8.4.4
Cause
Client virtual machines were configured to use OpenDNS/Umbrella resolvers directly instead of standard public DNS servers, preventing proper DNS redirection and identity attribution by the FTD Umbrella DNS Connector. When VMs explicitly point to Umbrella DNS servers, the firewall cannot correctly intercept, inject, and forward DNS queries on behalf of the clients using the configured Umbrella organization and policy.
Prevention and Recommendations
Ensure endpoints use standard DNS resolvers (internal DNS or public DNS such as Google DNS) when relying on the FTD Umbrella DNS Connector for enforcement.
Avoid configuring clients to point directly to Umbrella/OpenDNS resolvers when DNS redirection or injection is expected from network security devices.
Validate DNS flow using Umbrella activity search and policy checker tools after any DNS or routing changes.
Test DNS resolution behavior in both production and lab environments before deployment.
Related Content
Configuring the Umbrella DNS Connector for Cisco Secure Firewall Management Center
Renew Umbrella Root Certificate for Token Based Configuration
Revision History
| Revision | Publish Date | Comments |
|---|---|---|
2.0 |
23-Apr-2026
|
Initial Release, formatting |
1.0 |
17-Apr-2026
|
Initial Release |
Contact Cisco
- Open a Support Case

- (Requires a Cisco Service Contract)
 Feedback
Feedback