Secure Firewall FTD Event Logging to CDO/cdFMC Fails Due to DNS Resolution
Available Languages
Issue
Connection event logging stopped appearing in Cisco Defense Orchestrator (CDO) Event Logging and cloud-delivered Firewall Management Center (cdFMC) Events pages for a single Firewall Threat Defense (FTD). The affected device was unable to send connection event logs to the cloud management platform, impacting production visibility and troubleshooting capabilities. Analysis revealed that the FTD was experiencing repeated failures to connect to Cisco eventing services due to temporary name resolution failures, with the timestamp of DNS resolution failures correlating exactly with when connection events stopped appearing in eventing pages.
Environment
Cisco Secure Firewall FTD managed by CDO with cdFMC
DNS server configured at FTD management interface
Production environment requiring connection event visibility for troubleshooting
Resolution
1: Review the CDO Event Logging and cdFMC Unified/Connection Event pages to determine the time of eventing loss.
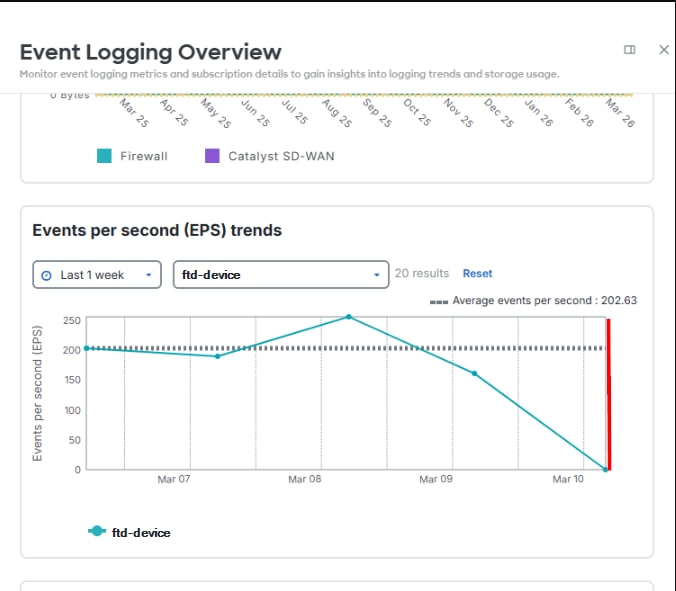 inline_image_0.png
inline_image_0.pnginline_image_0.png
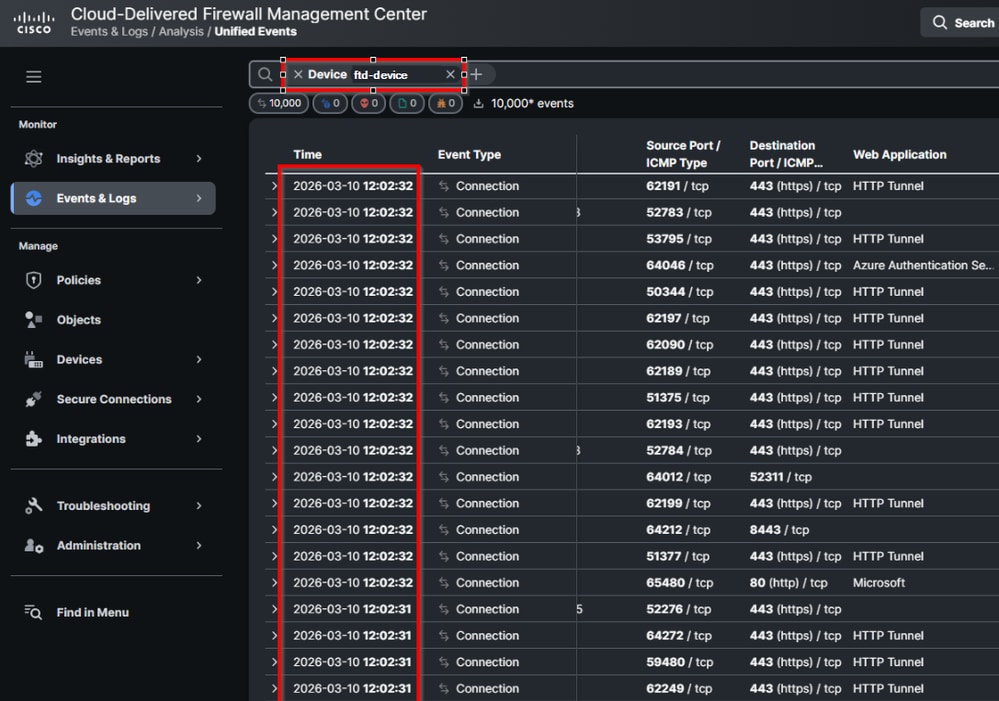 inline_image_1.png
inline_image_1.pnginline_image_1.png
2: Ensure the necessary FTD processes are running to permit the event generation and sending:
root@ftd-device:/ngfw/var/log# pmtool status | grep Event
Required by: SFDataCorrelator,expire-session,TSS_Daemon,snapshot_manager,fpcollect,Syncd,Pruner,ActionQueueScrape,rotate_stats,sfestreamer,tomcat,EventHandler
EventHandler (normal) - Running 17453
Command: /ngfw/usr/local/sf/bin/EventHandler
LD_LIBRARY_PATH=/ngfw/usr/local/sf/lib64/EventHandlerModules
PID File: /ngfw/var/sf/run/EventHandler.pid
Enable File: /ngfw/etc/sf/EventHandler.run
--
root@ftd-device:/ngfw/var/log# pmtool status | grep SSE
SSEConnector (system) - Running 20697
Required by: ngfwManager,ASAConfig,tomcat,SSEConnector,rsyncd,hmdaemon,srt,UUID3: Review the FTD to find the correlating EventHandler and Connector log data indicating the cause:
/ngfw/var/log/EventHandlerStat.* | grep -E "TotalEvents|SSEConnector"
{"Time": "2026-03-10T16:00:25Z", "TotalEvents": 104659, "PerSec": 348, "UserCPUSec": 9.242, "SysCPUSec": 1.497, "%CPU": 3.6, "MemoryKB": 78984}
{"Time": "2026-03-10T16:00:25Z", "Consumer": "SSEConnector", "Events": 104649, "PerSec": 348, "CPUSec": 9.924, "%CPU": 3.3}
{"Time": "2026-03-10T16:00:25Z", "ConsumerEvent": "SSEConnector-ConnectionEvent", "InTransforms": 104649, "OutTransforms": 104649}
{"Time": "2026-03-10T16:05:25Z", "TotalEvents": 57651, "PerSec": 192, "UserCPUSec": 5.382, "SysCPUSec": 1.329, "%CPU": 2.2, "MemoryKB": 78984}
{"Time": "2026-03-10T16:05:25Z", "Consumer": "SSEConnector", "Events": 57641, "PerSec": 192, "CPUSec": 5.900, "%CPU": 2.0, "OutputWaitSec": 132.792}
{"Time": "2026-03-10T16:05:25Z", "ConsumerEvent": "SSEConnector-ConnectionEvent", "InTransforms": 57641, "OutTransforms": 57641}
{"Time": "2026-03-10T16:10:25Z", "TotalEvents": 24, "PerSec": 0, "UserCPUSec": 0.314, "SysCPUSec": 0.545, "%CPU": 0.3, "MemoryKB": 78984}
{"Time": "2026-03-10T16:10:25Z", "Consumer": "SSEConnector", "Events": 14, "PerSec": 0, "CPUSec": 0.046, "%CPU": 0.0, "OutputWaitSec": 300.223, "ProcessingWaitSec": 286.117}
{"Time": "2026-03-10T16:10:25Z", "ConsumerEvent": "SSEConnector-ConnectionEvent", "InTransforms": 14, "OutTransforms": 14}
{"Time": "2026-03-10T16:15:25Z", "TotalEvents": 10, "PerSec": 0, "UserCPUSec": 0.214, "SysCPUSec": 0.603, "%CPU": 0.3, "MemoryKB": 78984}
{"Time": "2026-03-10T16:15:25Z", "Consumer": "SSEConnector", "Events": 0, "PerSec": 0, "CPUSec": 0.009, "%CPU": 0.0, "OutputWaitSec": 300.161, "ProcessingWaitSec": 300.161}
{"Time": "2026-03-10T16:10:25Z", "ConsumerEvent": "SSEConnector-ConnectionEvent", "InTransforms": 0, "OutTransforms": 0}
---
/ngfw/var/log/messages | grep "SSEConnector"
Mar 12 11:36:01 ftd-device SF-IMS[62079]: [62112] EventHandler:EventHandler [ERROR] Consumer SSEConnector publishing blocked for 330.801 sec: Resource temporarily unavailable
---
/ngfw/var/log/connector/connector.log | grep "failure in name resolution"
time="2026-03-10T12:02:44.329750985-04:00" level=error msg="[ftd-device][events.go:100 events:connectWebSocket] dial tcp: lookup eventing-ingest.sse.itd.cisco.com: Temporary failure in name resolution"
time="2026-03-10T12:02:44.329830226-04:00" level=warning msg="[ftd-device][events.go:181 events:(*Service).Start] Could not connect to WebSocket endpoint wss://eventing-ingest.sse.itd.cisco.com:443/ingest: dial tcp: lookup eventing-ingest.sse.itd.cisco.com: Temporary failure in name resolution"4: Verify the FTDs configured DNS server and reachability:
> show network ===============[System Information]=============== Hostname : ftd-device DNS Servers : 10.0.0.10 DNS from router : enabled Management port : 8305 IPv4 Default route Gateway : 10.0.0.1 ==================[management0]=================== Admin State : Enabled Admin Speed : 40gbps Link : Up Channels : Management & Events Mode : Non-Autonegotiation MDI/MDIX : Auto/MDIX MTU : 1500 MAC Address : A1:A2:A3:A4:A5:A6 ----------------------[IPv4]---------------------- Configuration : Manual Address : 10.0.0.2 Netmask : 255.255.255.0 Gateway : 10.0.0.1 ----------------------[IPv6]---------------------- Configuration : Disabled > expert admin@device:~$ sudo su Password: [enter admin password] root@device:/Volume/home/admin# ping 10.0.0.10 PING 10.0.0.10 (10.0.0.10) 56(84) bytes of data. 64 bytes from 10.0.0.10: icmp_seq=1 ttl=58 time=1.64 ms 64 bytes from 10.0.0.10: icmp_seq=2 ttl=58 time=1.72 ms 64 bytes from 10.0.0.10: icmp_seq=3 ttl=58 time=1.70 ms ^C --- 10.0.0.10 ping statistics --- 4 packets transmitted, 4 received, 0% packet loss, time 144ms rtt min/avg/max/mdev = 1.639/1.678/1.724/0.033 ms
5: Verify DNS resolution and HTTPS connectivity from the FTD to Cisco eventing services:
root@device:/Volume/home/admin# nslookup eventing-ingest.sse.itd.cisco.com root@device:/Volume/home/admin# curl -v -k https://eventing-ingest.sse.itd.cisco.com root@device:/Volume/home/admin# telnet eventing-ingest.sse.itd.cisco.com 443
Actions
The user identified and resolved an internal issue with their DNS server. Once DNS functionality was restored:
The FTD was able to resolve required Cisco eventing domains.
The FTD automatically re-established eventing connectivity.
Connection event logs resumed appearing in cdFMC as designed.
All corrective actions were performed by the user with no configuration changes required.
Cause
The root cause was a DNS resolution failure on the FTD management interface, specifically caused by an issue with the configured DNS server. Because the FTD could not resolve required Cisco eventing domains, including eventing-ingest.sse.itd.cisco.com, it was unable to establish outbound eventing connections, resulting in connection events not being delivered to the Cisco Security Cloud. After DNS resolution was restored, the user confirmed that connection event logging was fully operational and functioning normally in the production environment.
Related Content
About Secure Firewall Threat Defense and Cisco XDR Integration
Possible Defect beyond this article: Cisco bug ID CSCwr75332 FTD Fails to Forward Events to Security Cloud Control
Revision History
| Revision | Publish Date | Comments |
|---|---|---|
2.0 |
21-Apr-2026
|
Reformatting. |
1.0 |
20-Apr-2026
|
Initial Release |
Contact Cisco
- Open a Support Case

- (Requires a Cisco Service Contract)
 Feedback
Feedback