Introduction
This document describes how to configure two RFC-compliant RADIUS servers on ISE as proxy and authorization, respectively.
Prerequisites
Requirements
Cisco recommends that you have knowledge of these topics:
- Basic knowledge of RADIUS protocol
- Expertise in Identity Services Engine (ISE) policy configuration
Components Used
The information in this document is based on Cisco ISE versions 2.2 and 2.4.
The information in this document was created from the devices in a specific lab environment. All of the devices used in this document started with a cleared (default) configuration. If your network is live, ensure that you understand the potential impact of any command.
Configure
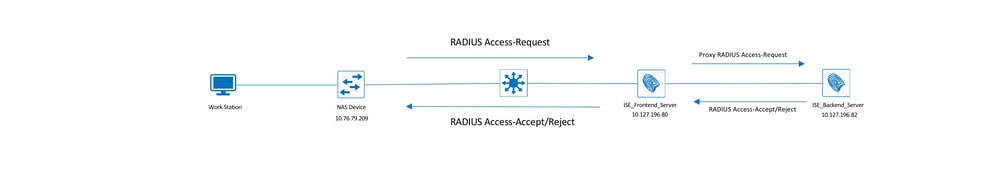
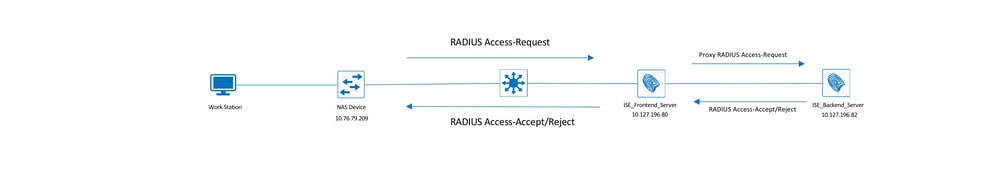
Network Diagram
Configure ISE (Frontend Server)
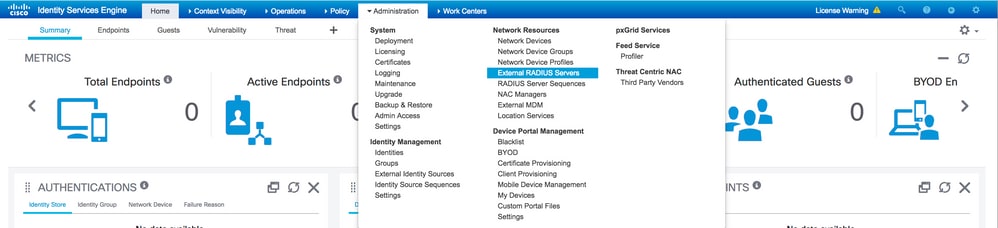
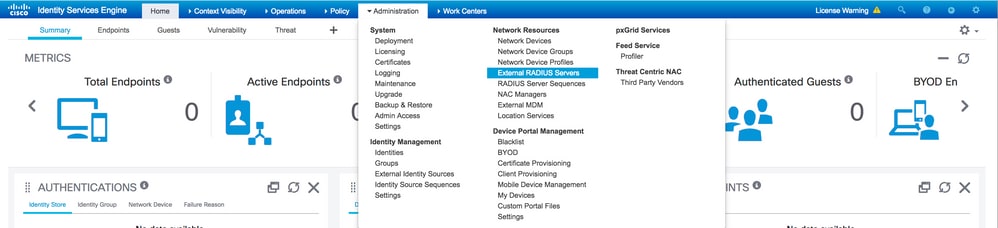
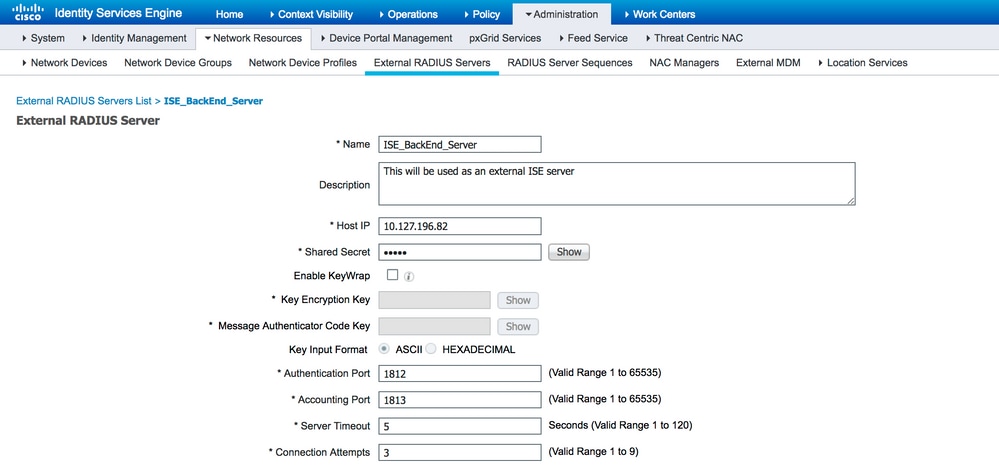
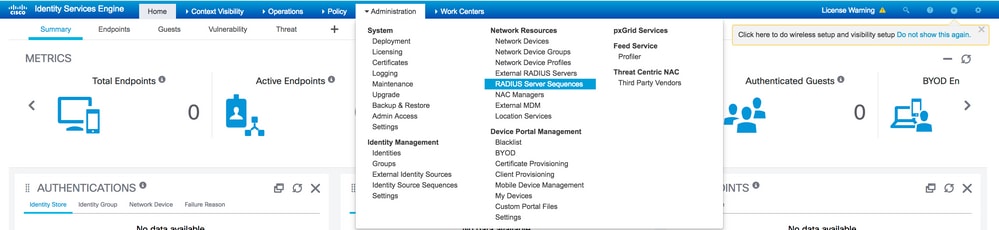
Step 1. Multiple external RADIUS servers can be configured and used in order to authenticate users on the ISE. In order to configure external RADIUS servers, navigate to Administration > Network Resources > External RADIUS Servers > Add, as shown in the image:
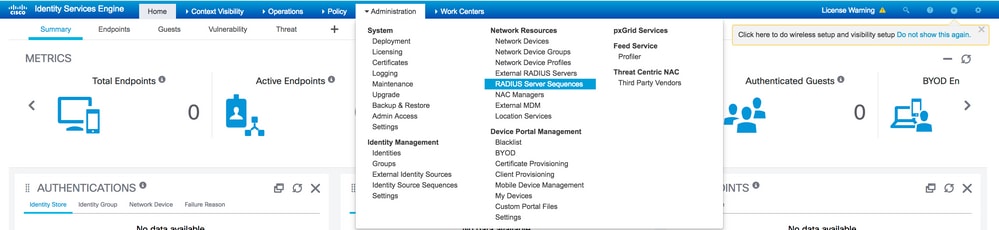
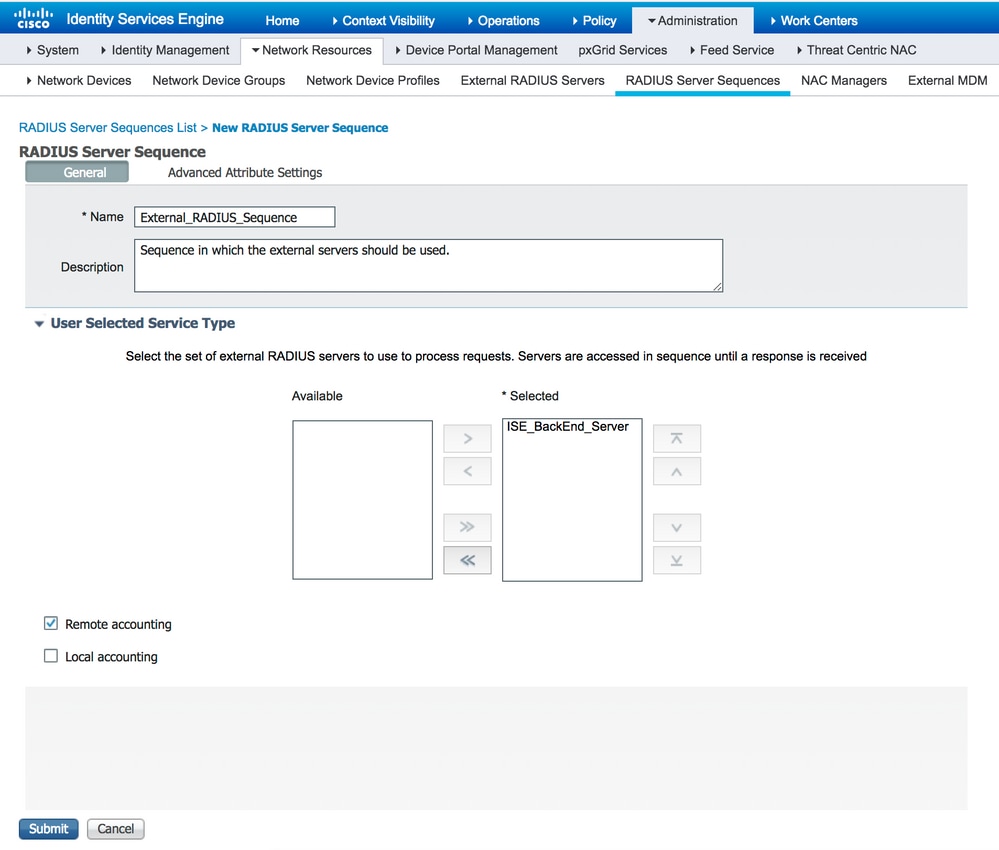
Step 2. In order to use the configured external RADIUS server, a RADIUS server sequence must be configured similar to the Identity source sequence. In order to configure the same, navigate to Administration > Network Resources > RADIUS Server Sequences > Add, as shown in the image:
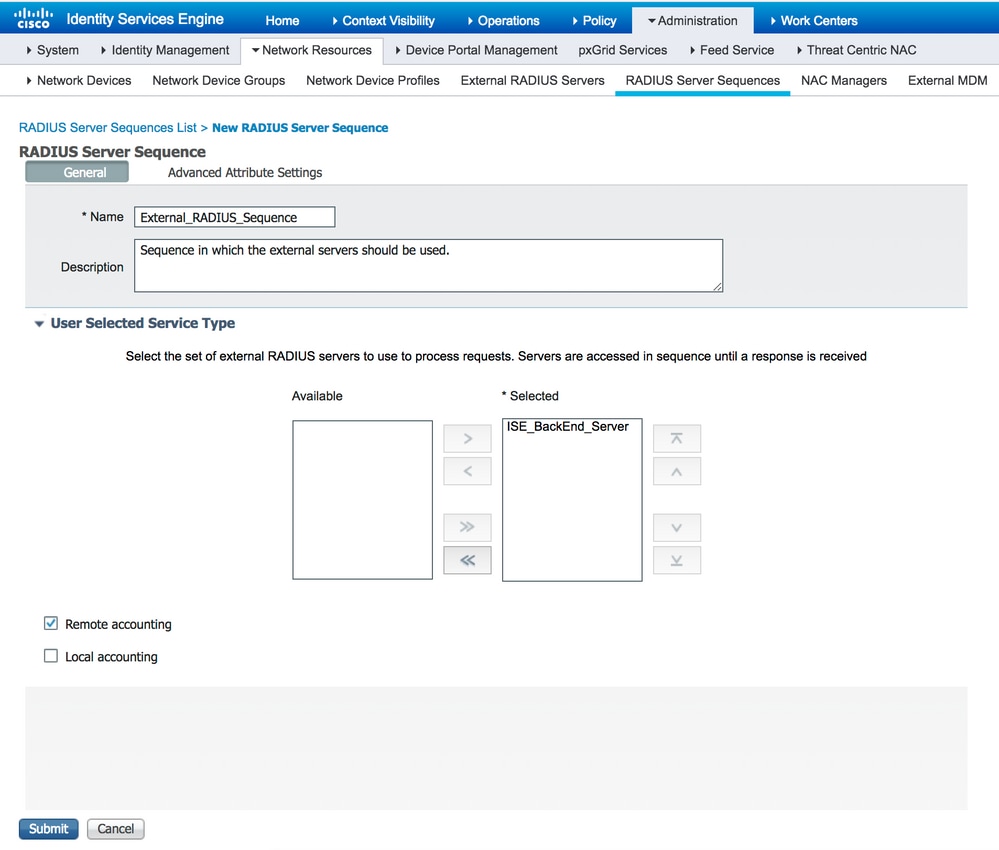
Note: One of the options available while the server sequence is created is to choose whether accounting must be done locally on the ISE or on the external RADIUS server. Based on the option chosen here, ISE decides on whether to proxy the accounting requests or store those logs locally.
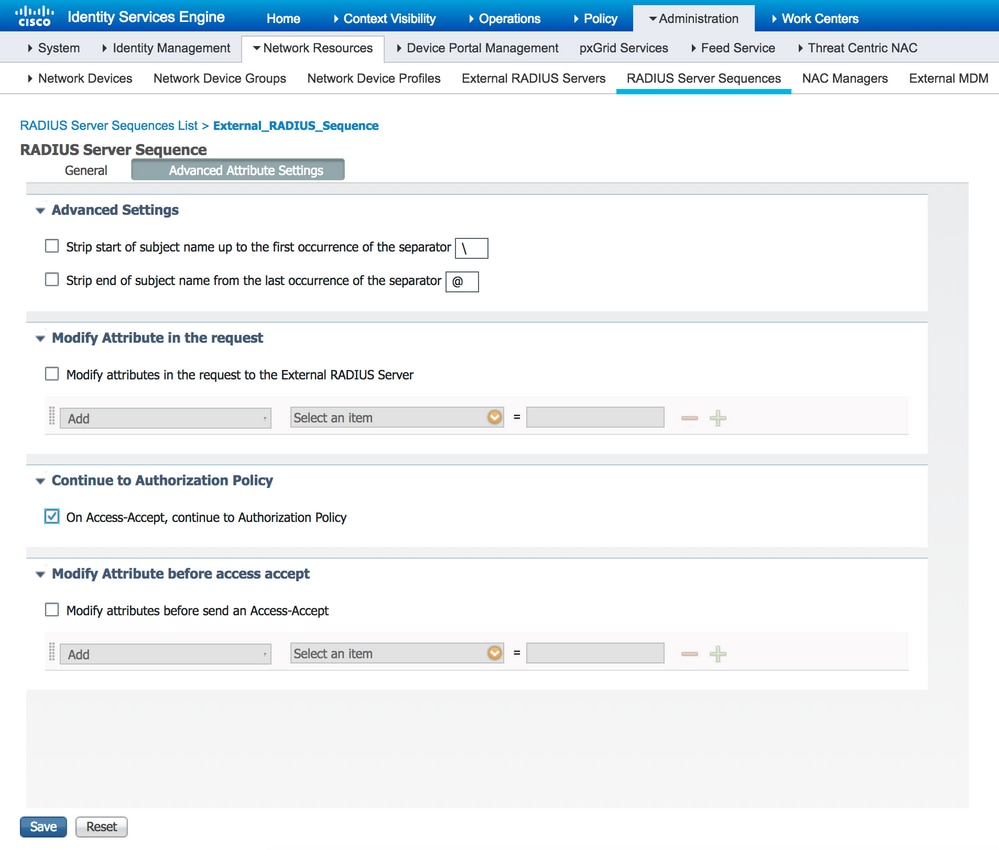
Step 3. There is an additional section that gives more flexibility on how ISE must behave when it proxies requests to external RADIUS servers. It can be found under Advance Attribute Settings, as shown in the image:
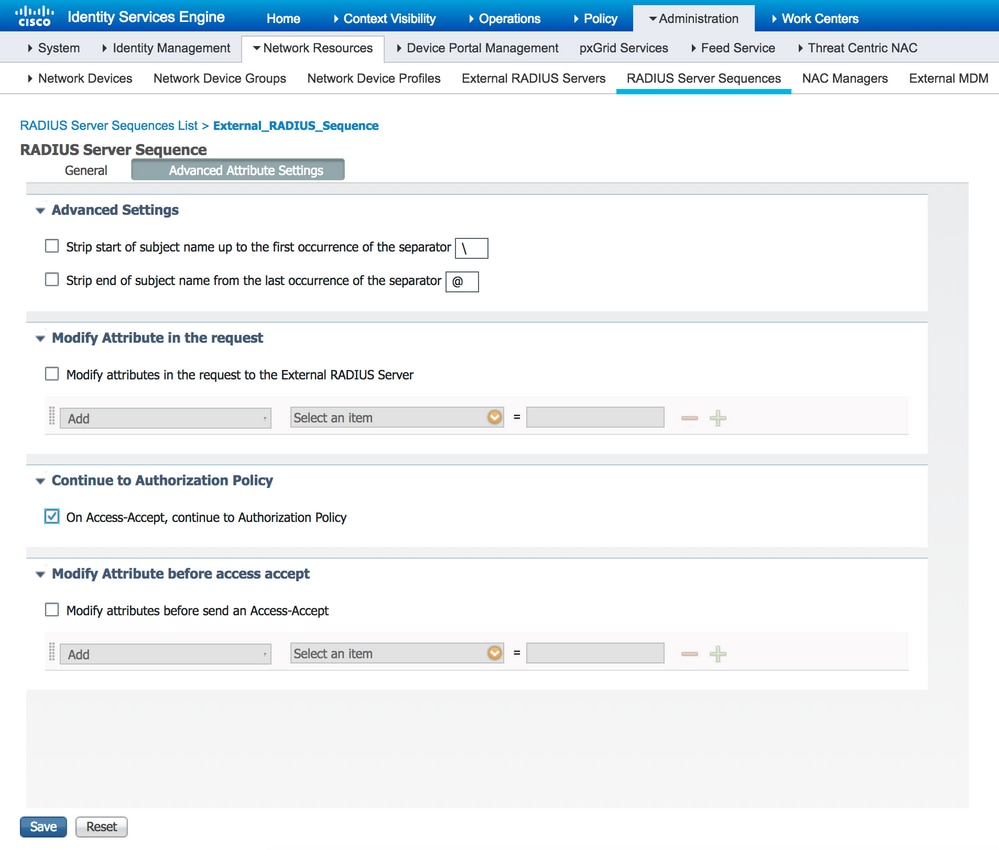
- Advanced Settings: Provides options to strip the start or the end of the username in RADIUS requests with a delimiter.
- Modify Attribute in the request: Provides the option to modify any RADIUS attribute in the RADIUS requests. The list here shows the attributes that can be added/removed/updated:
User-Name--[1]
NAS-IP-Address--[4]
NAS-Port--[5]
Service-Type--[6]
Framed-Protocol--[7]
Framed-IP-Address--[8]
Framed-IP-Netmask--[9]
Filter-ID--[11]
Framed-Compression--[13]
Login-IP-Host--[14]
Callback-Number--[19]
State--[24]
VendorSpecific--[26]
Called-Station-ID--[30]
Calling-Station-ID--[31]
NAS-Identifier--[32]
Login-LAT-Service--[34]
Login-LAT-Node--[35]
Login-LAT-Group--[36]
Event-Timestamp--[55]
Egress-VLANID--[56]
Ingress-Filters--[57]
Egress-VLAN-Name--[58]
User-Priority-Table--[59]
NAS-Port-Type--[61]
Port-Limit--[62]
Login-LAT-Port--[63]
Password-Retry--[75]
Connect-Info--[77]
NAS-Port-Id--[87]
Framed-Pool--[88]
NAS-Filter-Rule--[92]
NAS-IPv6-Address--[95]
Framed-Interface-Id--[96]
Framed-IPv6-Prefix--[97]
Login-IPv6-Host--[98]
Error-Cause--[101]
Delegated-IPv6-Prefix--[123]
Framed-IPv6-Address--[168]
DNS-Server-IPv6-Address--[169]
Route-IPv6-Information--[170]
Delegated-IPv6-Prefix-Pool--[171]
Stateful-IPv6-Address-Pool--[172]
-
Continue to Authorization Policy on Access-Accept: Provides an option to choose if ISE must just send the Access-Accept as it is or proceed to provide access based on the Authorization Policies configured on the ISE rather than the authorization provided by the external RADIUS server. If this option is selected, the authorization provided by the external RADIUS server is overwritten with the authorization provided by ISE.
Note: This option works only if the external RADIUS server sends an Access-Accept in response to the proxied RADIUS Access-Request.
-
Modify Attribute before Access-Accept: Similar to the Modify Attribute in the request, the attributes mentioned earlier can be added/removed/updated present in the Access-Accept sent by the external RADIUS server before it is sent to the network device.
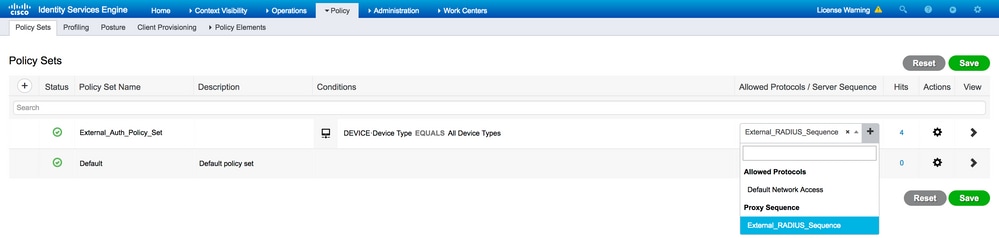
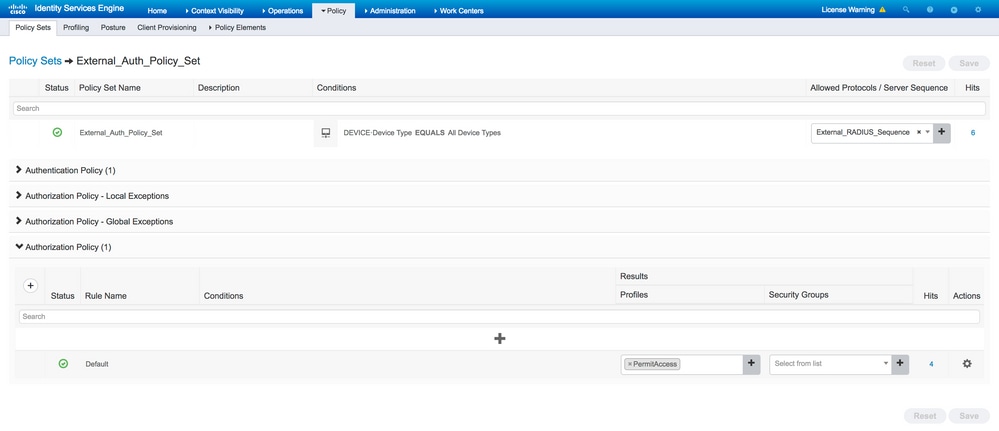
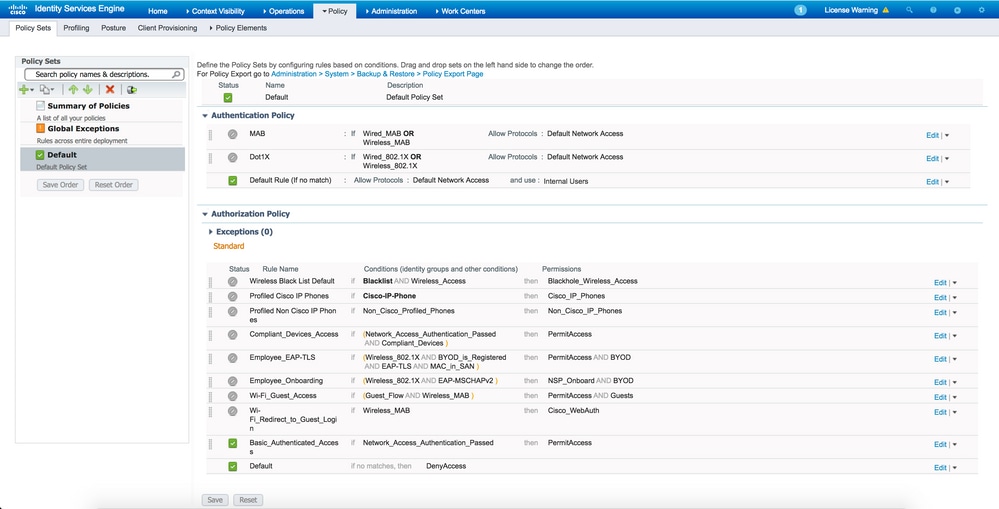
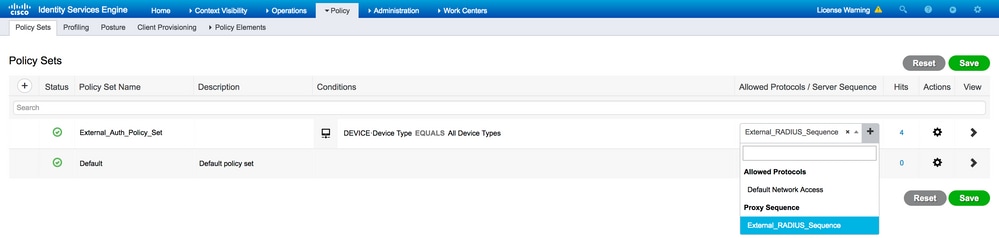
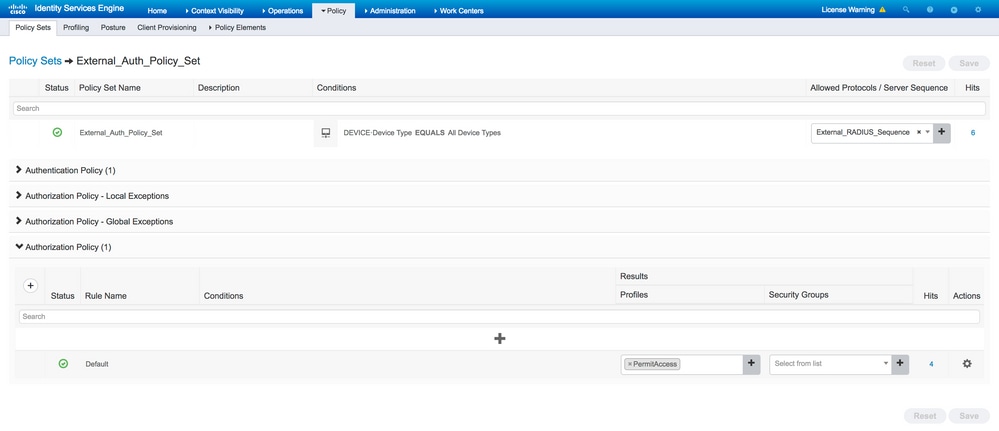
Step 4. The next part is to configure the Policy Sets in order to use the RADIUS Server Sequence instead of Allowed Protocols so that the requests are sent to the external RADIUS server. It can be configured under Policy > Policy Sets. Authorization policies can be configured under the Policy Set but only come into effect if the Continue to Authorization Policy on Access-Accept option is chosen. If not, ISE simply acts as a proxy for the RADIUS requests in order to match the conditions configured for this Policy Set.
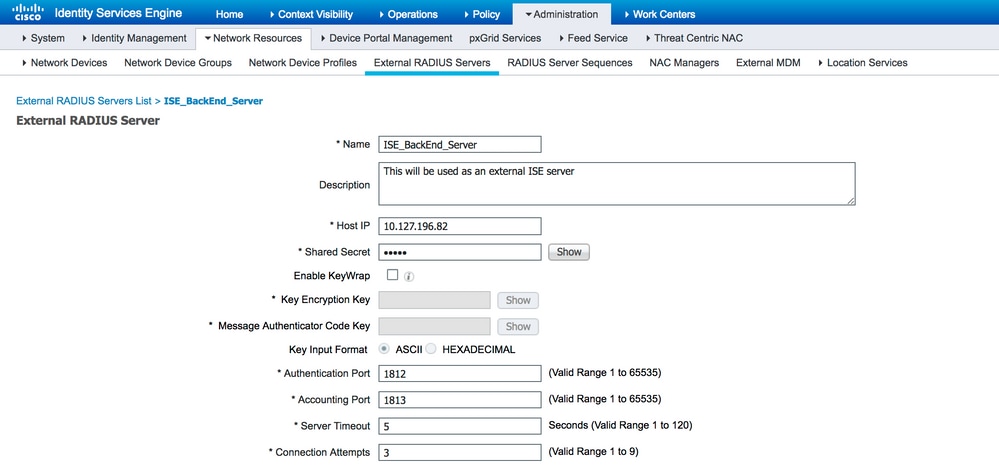
Configure the External RADIUS Server
Step 1. In this example, another ISE server (version 2.2) is used as an external RADIUS server named ISE_Backend_Server. The ISE (ISE_Frontend_Server) must be configured as a network device or traditionally called NAS in the external RADIUS server (ISE_Backend_Server in this example), since the NAS-IP-Address attribute in the Access-Request that is forwarded to the external RADIUS server is replaced with the IP address of theISE_Frontend_Server. The shared secret to be configured is the same as the one configured for the external RADIUS server on the ISE_Frontend_Server.

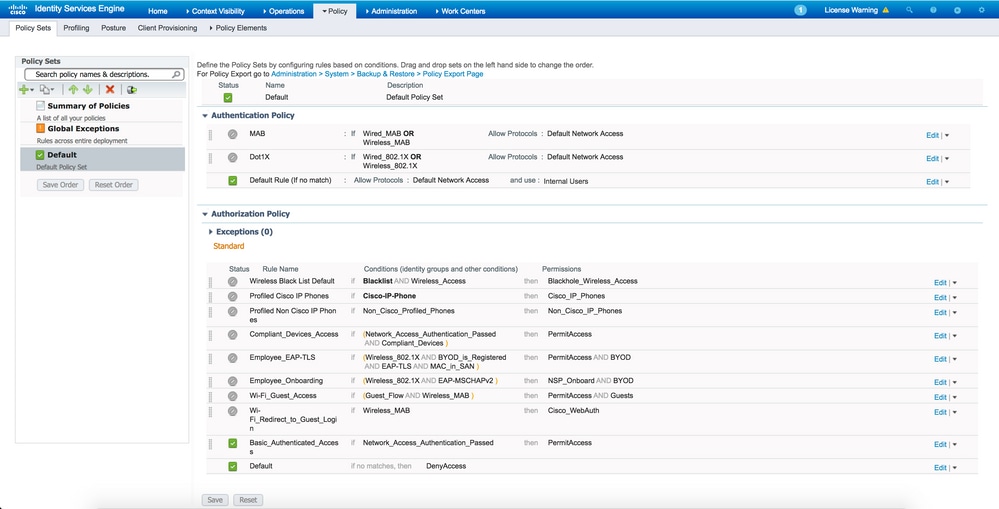
Step 2. The external RADIUS server can be configured with its own authentication and authorization policies in order to serve the requests proxied by the ISE. In this example, a simple policy is configured in order to check the user in the internal users and then permit access if authenticated.
Verify
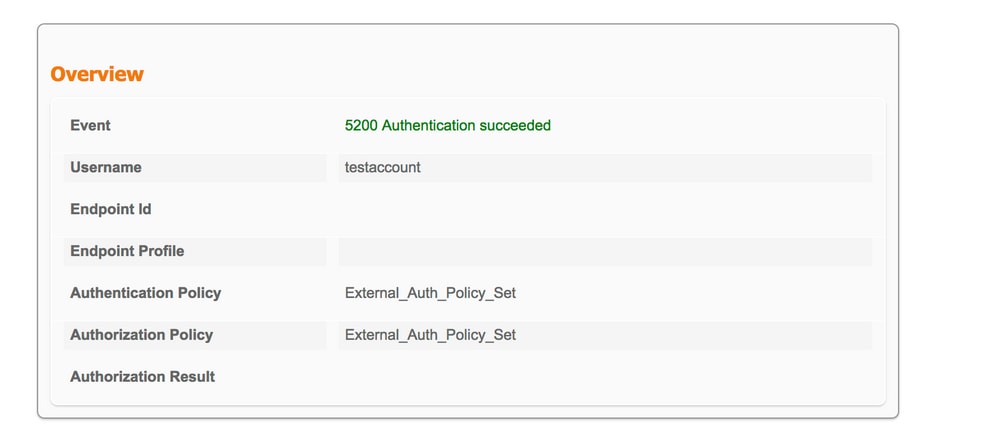
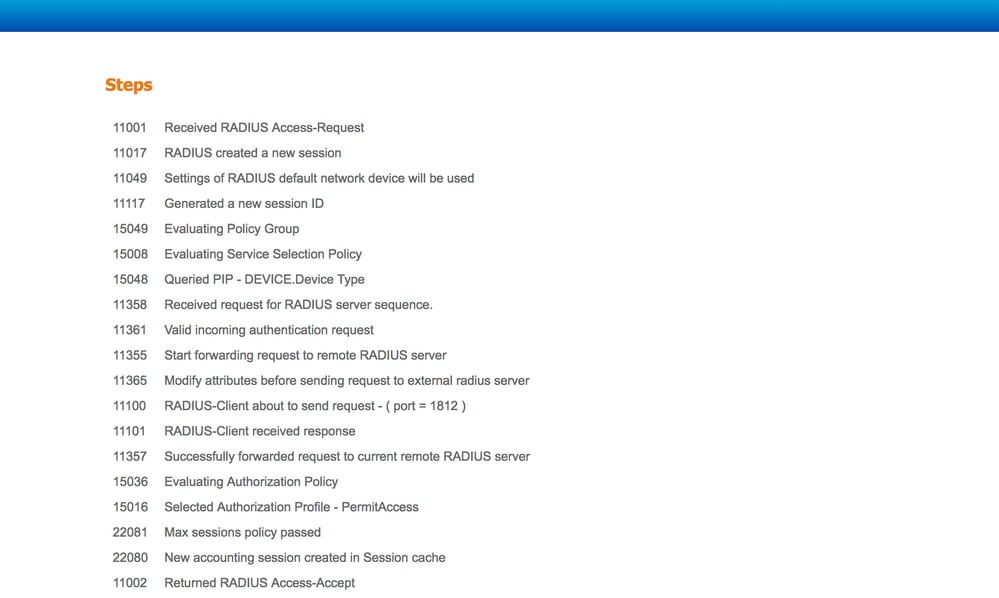
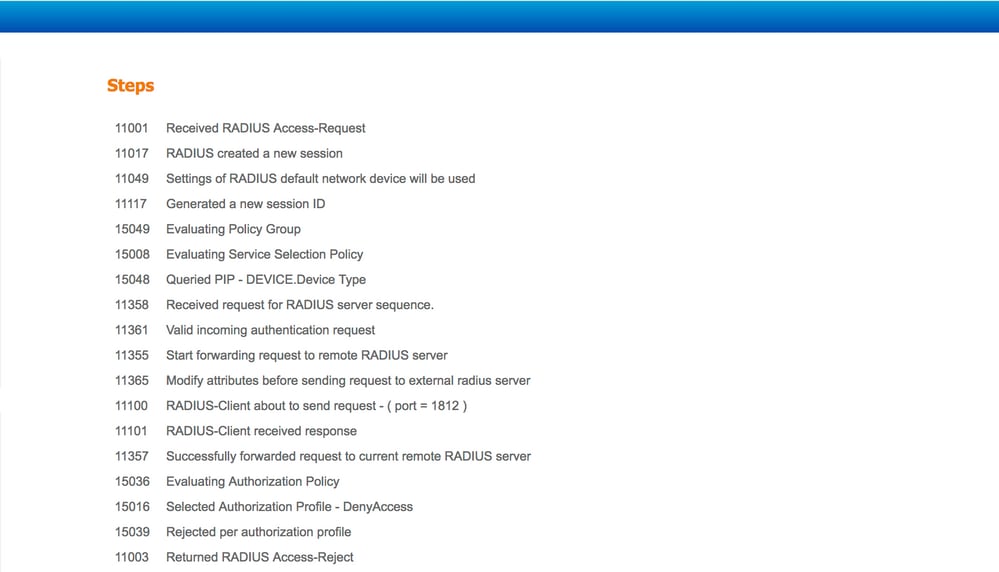
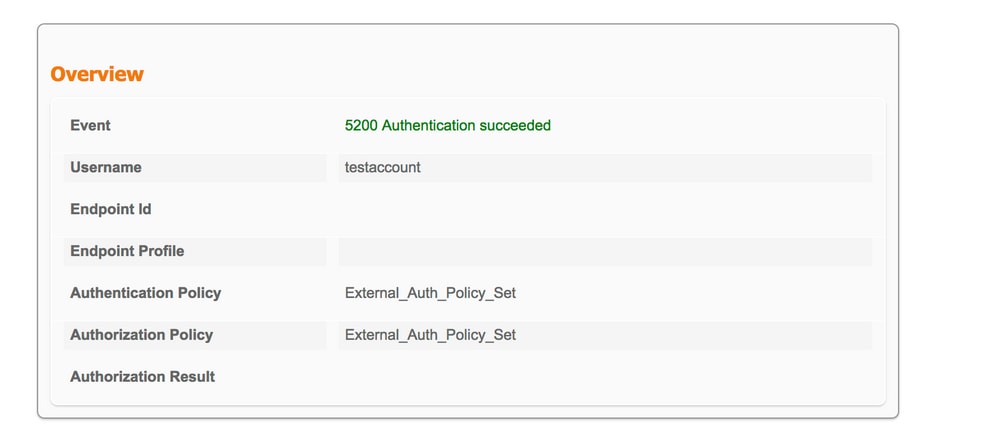
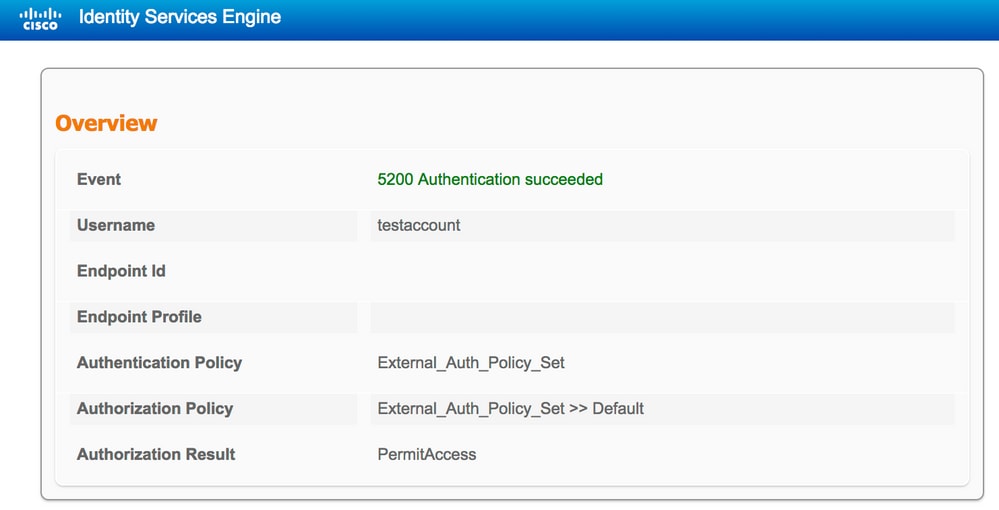
Step 1. Check ISE live logs if the request is received, as shown in the image.

Step 2. Check if the correct policy set is selected, as shown in the image.
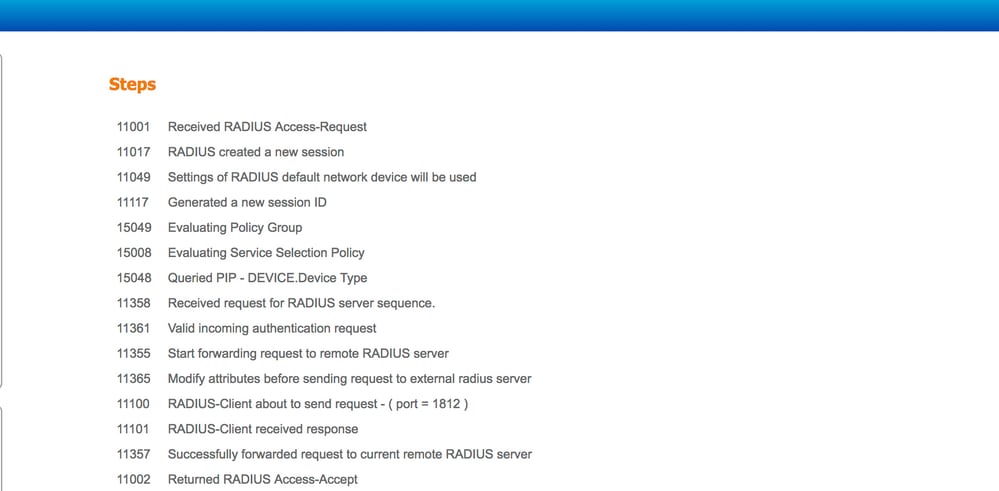
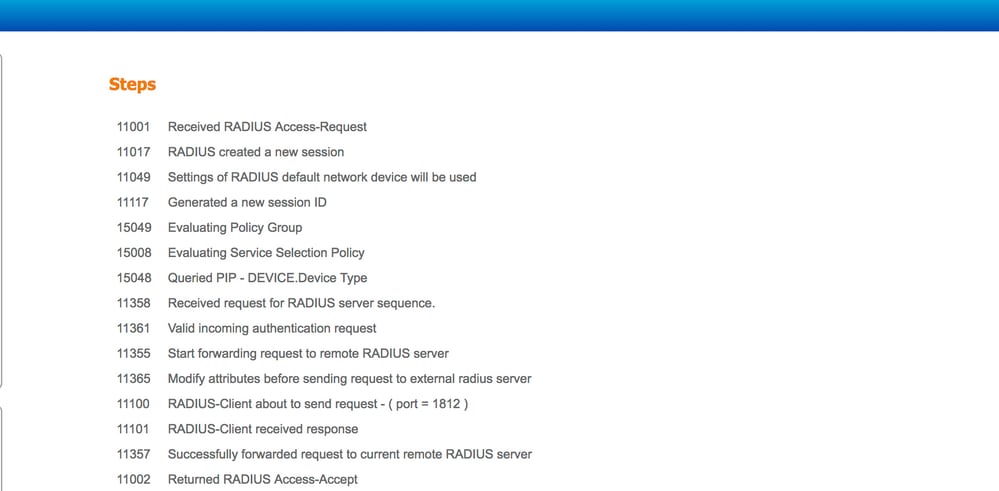
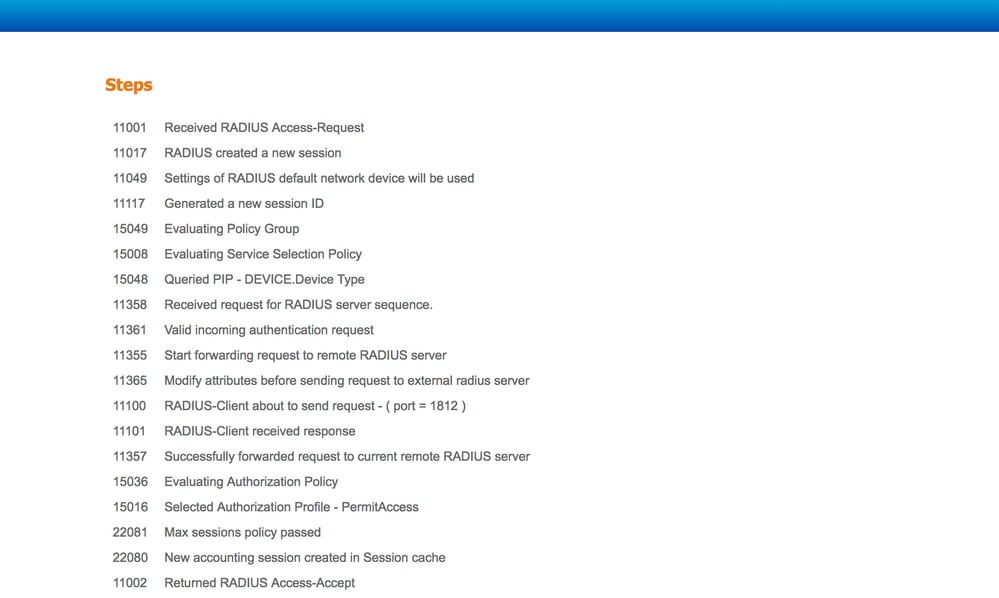
Step 3. Check if the request is forwarded to the external RADIUS server.
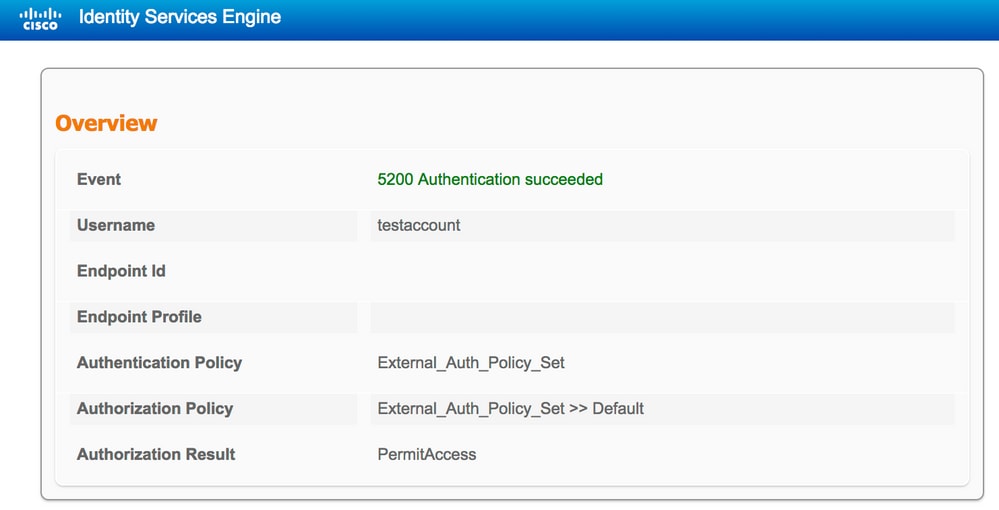
4. If the Continue to Authorization Policy on Access-Accept option is chosen, check if the authorization policy is evaluated.
Troubleshoot
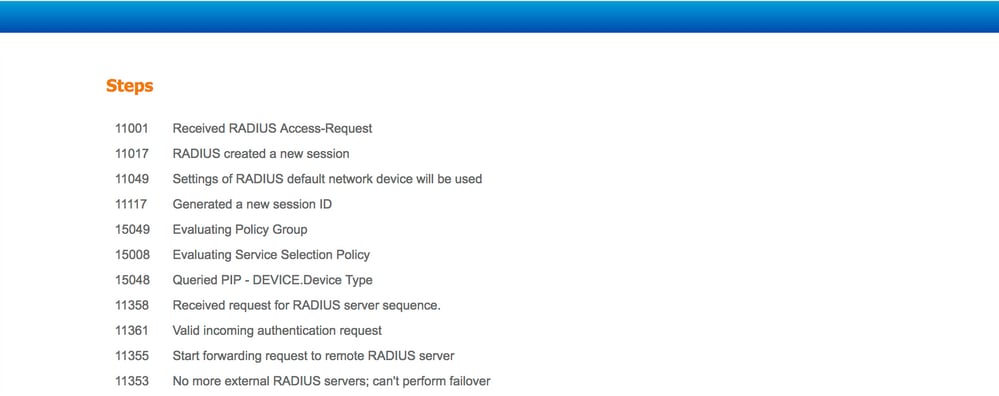
Scenario 1. Event - 5405 RADIUS Request Dropped
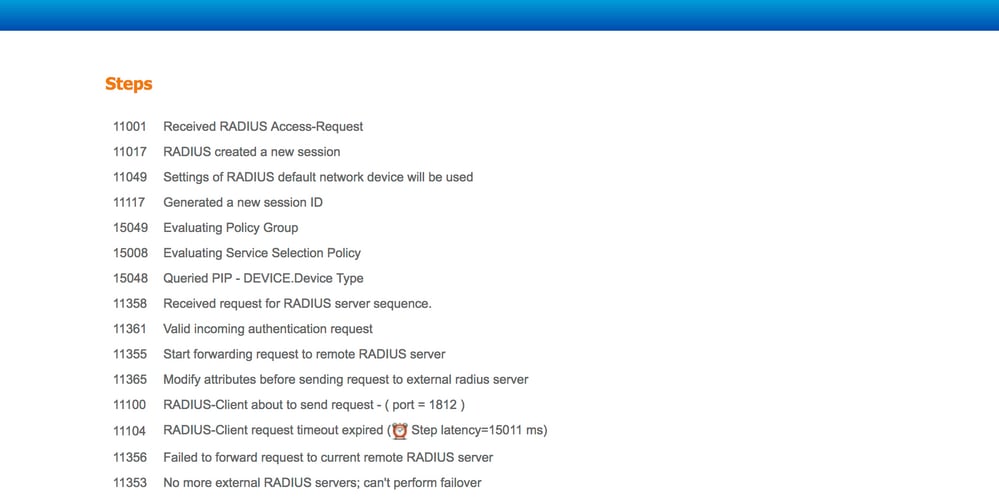
- The most important thing that must be verified is the steps in the detailed authentication report. If the steps say the "RADIUS-Client request timeout expired", it means that the ISE did not receive any response from the configured external RADIUS server. This can happen when:
- There is a connectivity issue with the external RADIUS server. ISE is unable to reach the external RADIUS server on the ports configured for it.
- ISE is not configured as a Network Device or NAS on the external RADIUS Server.
- Packets are dropped by the external RADIUS Server either by configuration or because of some problem on the external RADIUS server.
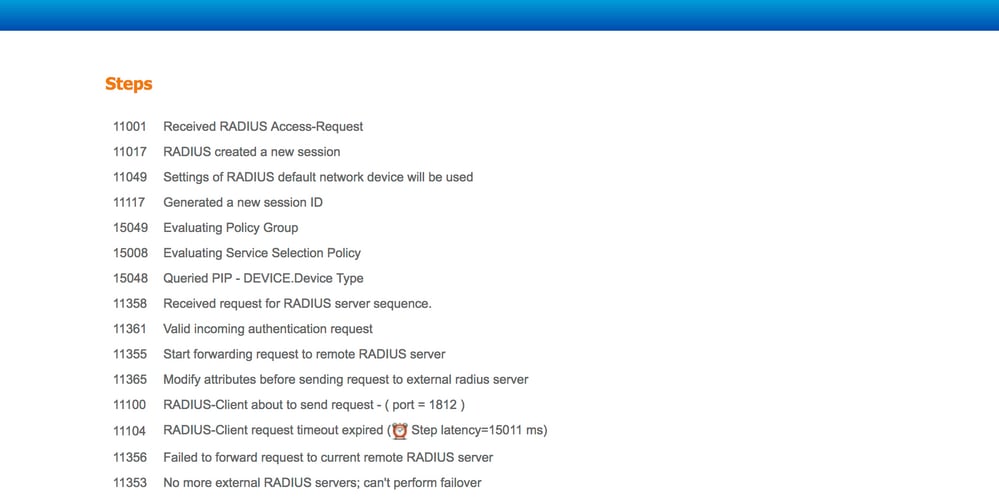
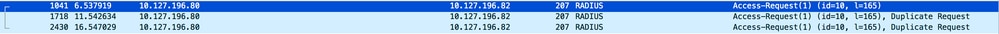
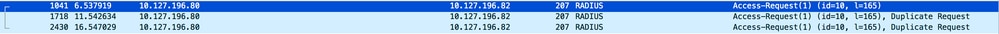
Check packet captures as well in order to see if it is not a false message; that is, ISE receives the packet back from the server but still reports that the request timed out.
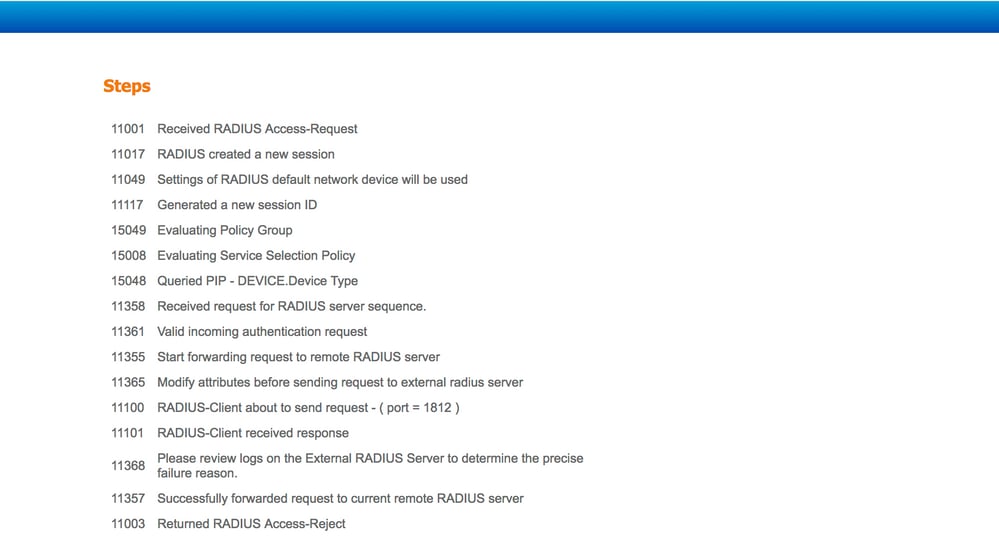
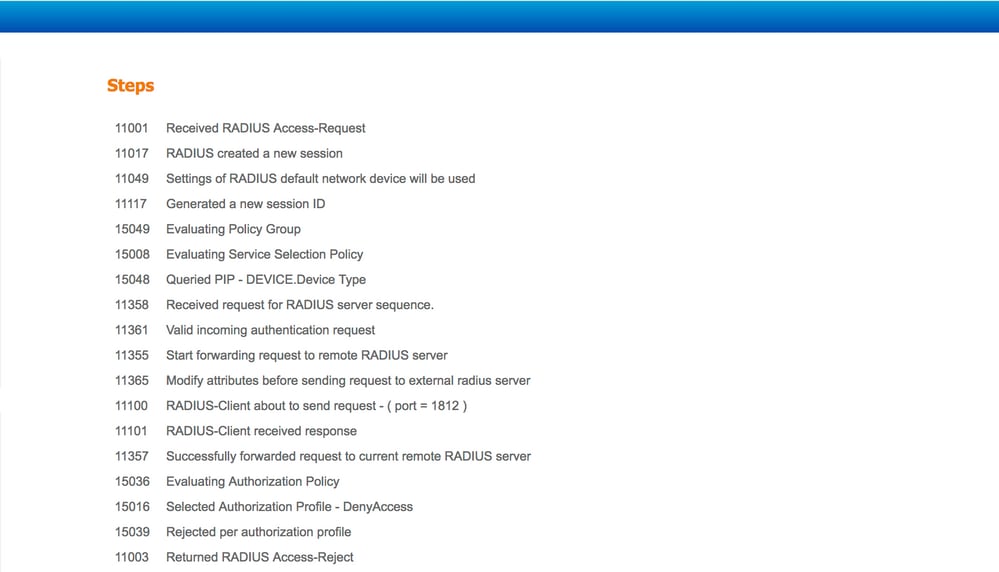
Scenario 2. Event - 5400 Authentication Failed
- In this event, if the steps say "11368 Please review logs on the External RADIUS Server to determine the precise failure reason", it means that the authentication has failed on the external RADIUS server itself and it has sent an Access-Reject.
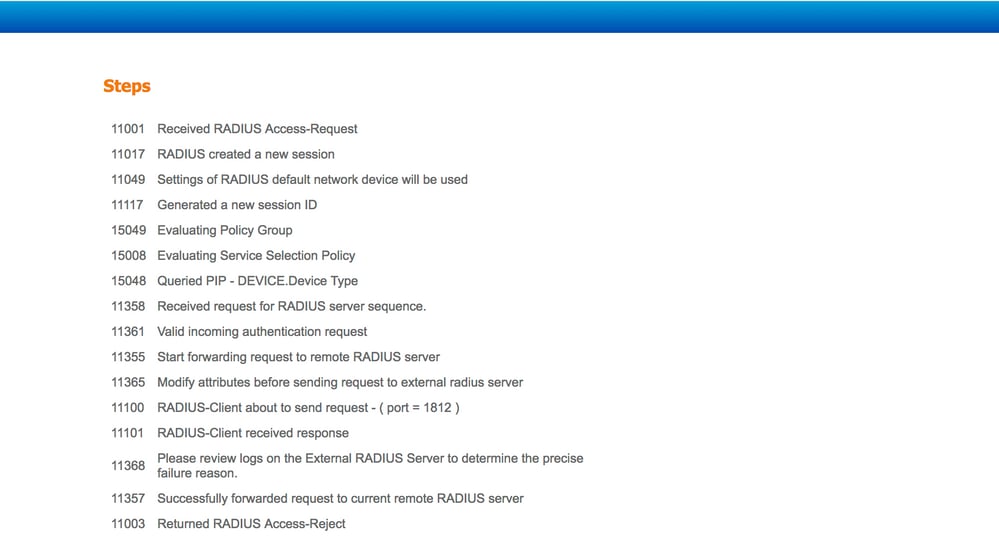
- If the steps say "15039 Rejected per authorization profile", it means that ISE received an Access-Accept from the external RADIUS server but ISE rejects the authorization based on the authorization policies configured.
- If the Failure Reason on the ISE is anything else apart from the ones mentioned here in case of an authentication failure, then it can mean a potential issue with the configuration or with the ISE itself. A TAC case is recommended to be opened at this point.



 Feedback
Feedback