Introduction
This document describes components configurable in the Advanced Malware Protection (AMP) for Endpoints Windows Policy.
Prerequisites
Requirements
Cisco recommends that you have knowledge of these topics:
- AMP for Endpoints user with Administrator privileges
Components Used
The information in this document is based on AMP for Endpoints Console.
The information in this document was created from the devices in a specific lab environment. All of the devices used in this document started with a cleared (default) configuration. If your network is live, make sure that you understand the potential impact of any command.
Configure
In order to create a new Windows policy, navigate to the management tab and select Policies. In the policy section, create a new Windows policy.
Modes and Engines
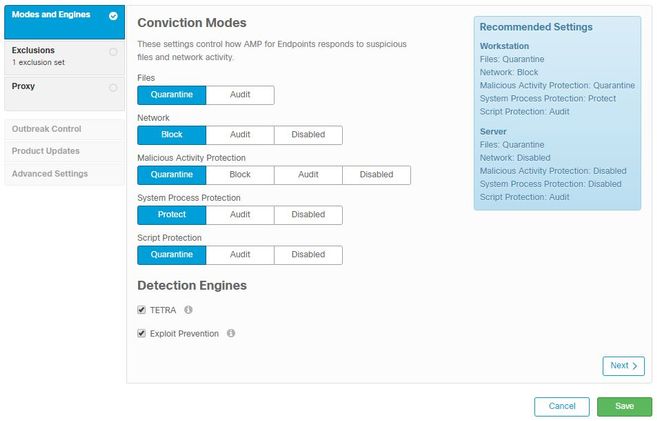
Files: The main SHA engine and core functionality of AMP. This option allows for file scans and quarantine.
Network: The Device Flow Correlation engine that monitors connections.
Malicious Activity Protection: Engine that protects the endpoint from ransomware attacks.
System Process Protection: Engine that protects critical Windows system processes from compromises through memory injection attacks.
Script protection: Provides visibility into script-based attacks.
Detection engines:
- Tetra: Offline antivirus that downloads definitions to protect the endpoint
- Exploit Prevention: Protects connectors from memory injection attacks
Note: A window of recommended settings for Workstations and Servers is displayed in the right section.
After the configuration of the Modes and Engine section, click Next, as shown in the image.
Exclusions
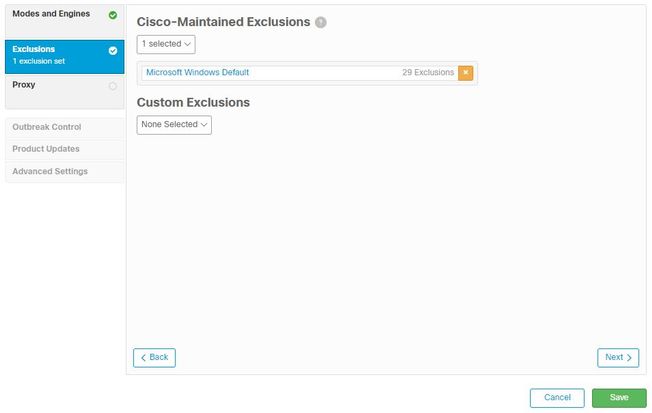
The exclusions section contains Cisco-Maintained Exclusions and Custom exclusions:
- Cisco-Maintained Exclusions are created and maintained by Cisco and allow you to exclude common applications from scans by AMP to avoid incompatibility issues
- Custom Exclusions are created and maintained by the user administrator
If you want to know more about exclusions, you can find more information in this video.
Once you finish your Exclusions configuration, click Next, as shown in the image.
Proxy
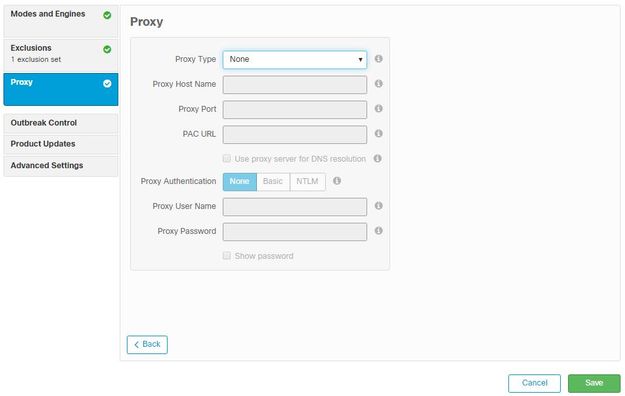
In this section, you can configure the proxy settings per your environment to allow the connector to query the AMP cloud.
After you configure your Proxy settings, click Save, as shown in the image.
Outbreak Control
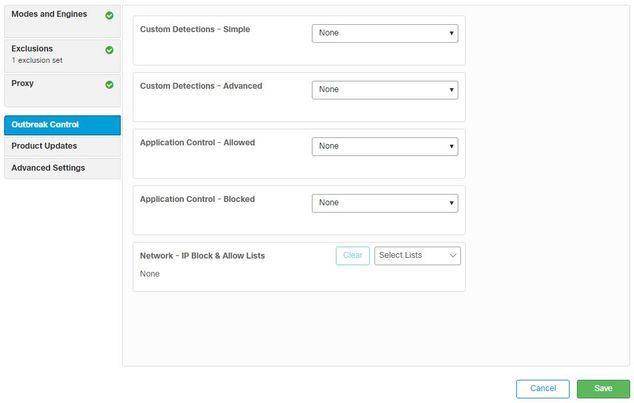
In the Outbreak Control section, you can configure custom detections:
- Custom detections - Simple: Allows you to block specific files based on their SHA
- Custom detections - Advanced: Blocks files based on signatures, for detections when a simple SHA is not sufficient
- Application Allowed and Blocked lists: Allows or blocks applications with SHAs
- Network - IP Block & Allow Lists: used with Device Flow Correlation (DFC) to define custom IP address detections
Product Updates
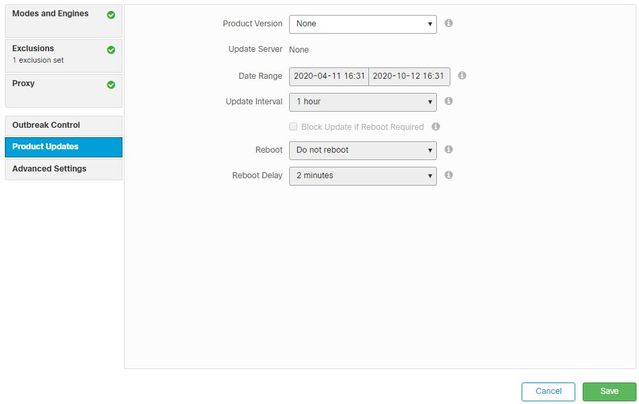
In the Product Update section, options for new updates are set. You can choose a version, date range to roll updates and options for a reboot.
Advanced Settings
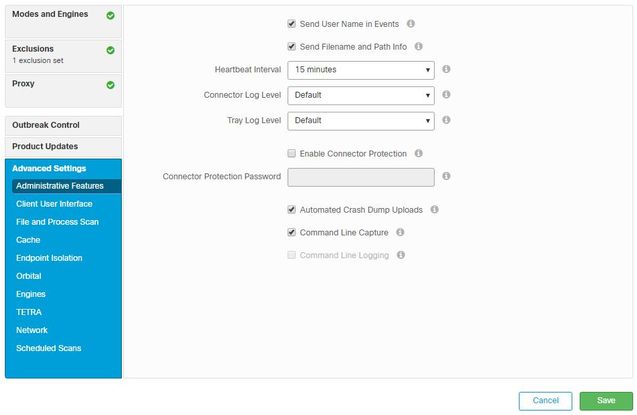
Administrative features: Configures how often the connector queries the cloud for changes to the policy.
Client User interface: Allows you to control the display of notifications in your devices where AMP is installed.
File and Process Scan: configures real-time protection options, how connectors check for file dispositions, and maximum file sizes allowed.
Cache: Time To Live configuration for cache.
Endpoint isolation allows you to enable and configure the feature to isolate devices with the AMP connector installed.
Orbital option enables the orbital advanced search.
Engines: Settings for ETHOS; a file grouping engine, and SPERO; a machine-based learning system.
TETRA configuration for the offline engine.
Network Enables the Device Flow Correlation options.
In the Scheduled Scans section you can configure the options for when and what type of scans you want to run in the connectors.
Save Changes
After you perform any changes, click Save to ensure that they are applied to the policy.
You can also find the information contained in this document in the Windows Policy Configuration in AMP for Endpoints video.
Related Information
