BPA User Guide RBAC Permissions v5.1
Available Languages
Introduction
Role Based Access Control (RBAC) is a method of restricting access based on the roles of users within an enterprise. Default roles are available, and new roles can be created by selecting preferred permissions and mapping these roles to user groups. Mapping roles to user groups allows all users in that user group to perform the operations associated with the role.
New Permissions
This section describes how a microservice can define its own set of RBAC permissions.
Define Static Permissions
To define static permissions:
- Create a JSON file listing all permissions in the microservice/src/config/device-permissions-spec.json path.
- Run the following JSON code to list a permission:
{
"service":"service-name",
"permissions": [
{
"group": "group-name",
"actions": [
{"name":"action-name","displayName":"Display name to be shown in roles page"}
]
}
]
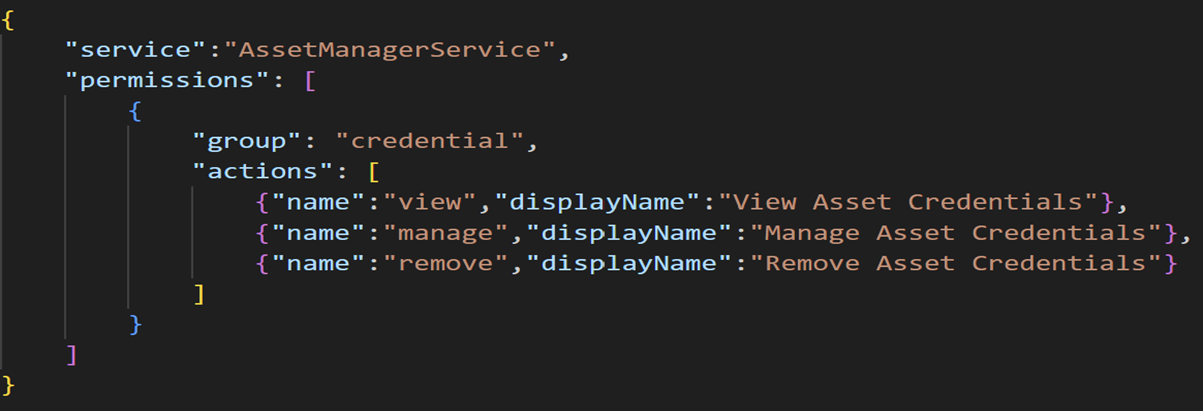
}Refer to the following example to create view, manage, and remove permissions within a credential group.
Registering Permissions in BPA
To register permissions:
- Import rbacSpecProcessorHelper from @cisco-bpa-platform/mw-util-common-app.
const { rbacHelper, rbacSpecProcessorHelper } = require('@cisco-bpa-platform/mw-util-common-app');- Run the following command to use rbacSpecProcessorHelper to process the permissions listed in the JSON file.
let resources = require('./config/asset-manager-permissions-spec');
let rbacSpecProcessorObj = rbacSpecProcessorHelper.getRbacSpecProcessorUtil();
rbacSpecProcessorObj.setSpec(resources);
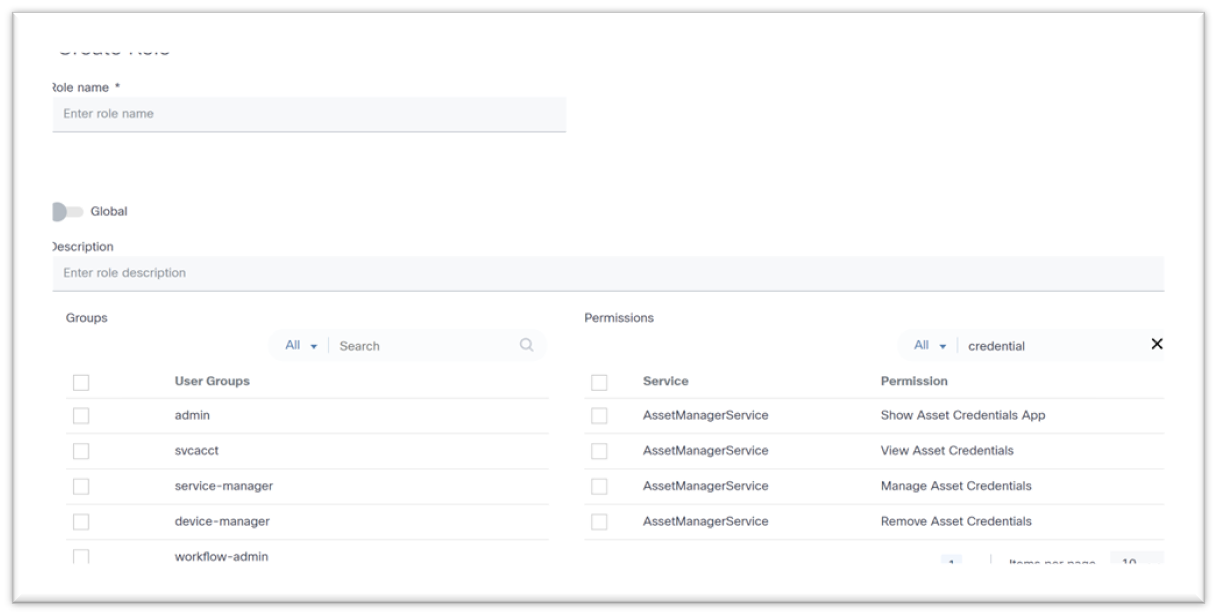
await rbacSpecProcessorObj.process();Users can view registered permissions in the Create Role and Edit Role pages.
Mapping Permissions
Permissions created in the previous section can be mapped to roles by default or by defining mapping with roles.
Defining Permissions Mapping
To map defined permissions to default roles, create a new JSON file in the microservice/src/config/device-role-permissions-mapping-spec.json path.
In the example below, three (3) permissions are mapped to the BPA Super Admin role, two (2) are mapped to the Tenant Admin role, and one (1) is mapped to the Network Operator role.
{
"service": "AssetManagerService",
"roles": [
{
"name": "BPA Super Admin",
"permissions": [
{"name":"view","displayName":"View Asset Credentials","group": "credential"},
{"name":"remove","displayName":"Remove Asset Credentials","group": "credential"},
{"name":"manage","displayName":"Manage Asset Credentials Add, Update and Delete Asset Credentials","group": "credential"}
]
},
{
"name": "Tenant Admin",
"permissions": [
{"name":"view","displayName":"View Asset Credentials","group": "credential"},
{"name":"remove","displayName":"Remove Asset Credentials","group": "credential"}
]
},
{
"name": "Network Operator",
"permissions": [
{"name":"view","displayName”:"View Asset Credentials","group": "credential"}
]
}
]
}
Updating Permission Mapping
To update permission mapping:
- Import rbacHelper, rbacPermissionMappingHelper from @cisco-bpa-platform/mw-util-common-app.
const { rbacHelper, rbacPermissionMappingHelper } = require('@cisco-bpa-platform/mw-util-common-app');- Run the following command to update permissions mapping with roles:
let rbacUtilObj = rbacHelper.getRbacUtilObj();
let registryDetails = await rbacUtilObj getRegistryByName({}, 'device-role-permissions-mapping-spec');
if (Array.isArray(registryDetails) && registryDetails.length === 0) {
let rbacPermissionMappingSpecProcessorObj = rbacPermissionMappingHelper.getRbacSpecProcessorUtil() ;
let rolePermissions = require('./config/device-role-permissions-mapping-spec');
rbacPermissionMappingSpecProcessorObj.setSpec(rolePermissions);
await rbacPermissionMappingSpecProcessorObj.process();
let rbacUtilObjRegister = rbacHelper.getRbacUtilObj();
await rbacUtilObjRegister addRegistry({}, 'device-role-permissions-mapping-spec');
}- Run the following command to process the files, create a permissions list, and map permissions with roles:
async function permissionsSpecProcessor() {
let resources = require('./config/device-permissions-spec');
let rbacSpecProcessorObj = rbacSpecProcessorHelper.getRbacSpecProcessorlltil();
rbacSpecProcessorObj.setSpec(resources);
await rbacSpecProcessorObj.process();
let rbacUtilObj = rbacHelper.getRbacUtilObj();
let registryDetails = await rbacUtilObj.getRegistryByName({} 'device-role-permissions-mapping-spec');
if (Array.isArray(registryDetails) && registryDetails.length === 0) {
let rbacPermissionMappingSpecProcessorObj = rbacPermissionMappingHelper.getRbacSpecProcessorUtil();
let rolePermissions = require('./config/device-role-permissions-mapping-spec');
rbacPermissionMappingSpecProcessorObj.setSpec(rolePermissions);
await rbacPermissionMappingSpecProcessorObj.process();
let rbacUtilObjRegister = rbacHelper.getRbacUtilObj();
await rbacUtilObjRegister.addRegistry({}, 'device-role-permissions-mapping-spec');
}
}Revision History
| Revision | Publish Date | Comments |
|---|---|---|
1.0 |
23-Sep-2025
|
Initial Release |
 Feedback
Feedback