A truly cloud-scale architecture that provides robust security in a simplified way
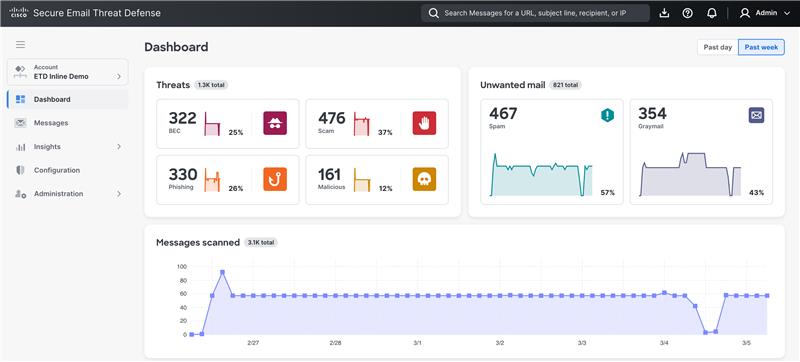
Expansive email security protects your employees and organization, while empowering your security response.
Cloud-scale, AI-driven gateway capabilities
Harness cloud-scale AI in our unified platform, eliminating traditional appliance-based limitations and reducing overhead.
Comprehensive, pre-delivery threat protection
Proactively stop email threats before they reach the mailbox, helping to ensure compliance and a safer, protected environment.
Unified and flexible platform
Gain flexible threat protection through a cohesive interface that unifies inline gateway and API-based deployment modes into a single console.
Simplified management and robust security
Streamline maintenance and accelerate your email security journey with cloud-scale AI and seamless platform integration.
Better together
Cisco Breach Protection Suite
Empower your security teams to respond to threats at speed with innovative XDR and global telemetry.
Cisco User Protection Suite
Enable seamless and secure access for trusted users to protect against identity-based attacks.
Cisco Secure Endpoint
Stop threats—before they cause compromise—with powerful detection and response capabilities.
Licensing made easy
Pricing
Pricing for Secure Email Threat Defense is on a per-user basis, which means it applies to a single-knowledge worker.
Terms
All subscriptions have flexible options, including 1-, 3-, and 5-year terms with significant savings on multiyear options. There is no extra charge for scheduled billing (monthly, quarterly, yearly, or full payment).
Financing
All subscriptions can be included in larger Cisco buying programs (Security Bundles, Enterprise Agreements) and can engage Cisco Capital for financing options.
Support
All subscriptions include Cisco Technical Assistance Center (TAC) support (24/7) and customer success for onboarding assistance.
Add value to security solutions
Cisco Security Enterprise Agreement
Instant savings
Experience security software buying flexibility with one easy-to-manage agreement.
Services for security
Let the experts secure your business
Get more from your investments and enable constant vigilance to protect your organization.