Here is the difference between these three phishing methods:
- Vishing: Phone call scams that pressure victims to share sensitive information verbally
- Phishing: Email scams that lure victims into clicking links leading to deceptive websites or malware downloads
- Smishing: Text message scams that also prompt victims to click malicious links or visit fake websites
How do vishing emails avoid detection?
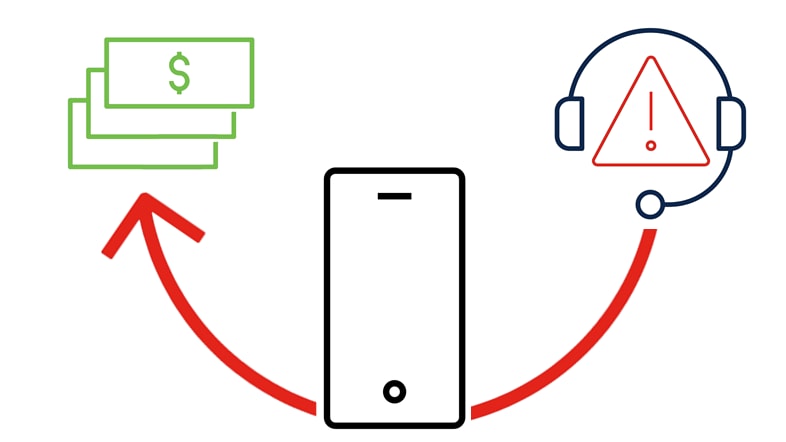
Not all vishing attacks start with a phone call. Many attackers start their scam with a well-crafted email, posing as an authoritative or trusted entity. They persuade the recipient to follow up to their demands through a phone call. When a vishing attack begins with a phishing email, how does it get through email security filters? There are three possible reasons for this:
- No links in email: Security systems easily flag emails with malicious links. However, a vishing email typically prompts the recipient to make a phone call, avoiding the need for links that standard security tools can identify. The content emphasizes initiating a call, sidelining traditional clickable links or buttons that are standard in phishing attempts.
- Email from a so-called authentic sender: Impersonated email accounts can pass authentication screenings such as Domain Based Message Authentication Reporting (DMARC), Sender Policy Framework (SPF), or DomainKeys Identified Mail (DKIM), if sent from a personal email address, such as a Gmail account.
- Ineffective email security tools: If an email successfully passes the first two filters, it may be categorized as low risk by basic email security systems and delivered to recipients' inboxes. This common problem can be mitigated with sophisticated email security software designed to detect and remediate phishing attempts, business email compromise, and ransomware.
Phone numbers, unlike URLs, aren't routinely tracked and shared as indicators of compromise (IOC) in the cybersecurity community. This lack of structure around phone numbers increases the likelihood of vishing campaigns evading conventional email security checks.
Vishing examples
Advances in technology have evolved common vishing scams into incredibly convincing attacks. Capitalizing on human trust and urgency, these scams mimic real businesses and scenarios, resulting in serious consequences for organizations.
Here are a few examples of common vishing attacks:
IRS tax scam
IRS vishing scams often feature a prerecorded voice message alerting you to a problem with your tax return, urging you to contact the IRS directly through a provided number. These messages are usually spoken in a threatening tone, warning that failure to respond could lead to a warrant for your arrest.
Impersonating the IRS is a common tactic among cybercriminals, both in email and voice scams. The IRS's name creates immediate trust and a sense of panic, compelling victims to act swiftly without questioning the legitimacy of the request.
Tech-support attacks
In tech-support vishing scams, fraudsters act as representatives from tech companies like Apple, Microsoft, and Google, alerting you to suspicious activity on your online account. They often request your email to send vital software updates, which turn out to be malware-infected downloads.
Tech-support scams exploit the victim's potential lack of technical knowledge. These scammers employ scare tactics, suggesting severe security threats or technical problems to instill fear and a sense of urgency. They might offer immediate solutions that grant them remote access to the victim's computer. If granted access, attackers can steal personal or corporate data, install malicious software, or cause systemwide damage.
Bank-impersonation scams
Bank-impersonation scams involve scammers impersonating credit card companies, banks, and other financial institutions to gain unauthorized access to your accounts. Claiming there is unusual or suspicious activity, they ask you to verify your account details and login credentials under the guise of resolving the issue.
If you call your financial institution directly, you may be asked to verify your identity with confidential information. However, legitimate financial institutions will never call you to ask for your passwords or security codes.
Social Security or Medicare scams
Older adults are often targets for cybercriminals as they may be less familiar with modern phishing scam tactics. In these scams, criminals pose as Social Security or Medicare officials to extract sensitive account details, allegedly to issue a new Social Security number or discuss benefits. The older adult demographic tends to favor phone communication over email or text messages, exposing themselves more to vishing schemes than to phishing or smishing attacks.
Inform friends or family members whom you think are susceptible to these types of scams that the IRS, Social Security Administration, or Medicare will never call them demanding personal information or issuing threats. Legitimate federal agencies do not contact citizens by phone, email, text, or social media to request personal or financial information.
Delivery scams
The prevalence of online shopping has made it challenging for many individuals and businesses to keep track of their purchases, and cybercriminals are capitalizing on this oversight. Scammers, masquerading as Amazon or UPS representatives, notify customers about alleged shipping issues and provide a contact number for queries about these fictitious orders.
When unsuspecting customers dial in, they are greeted by scammers posing as customer service, ready to pry personal details from the callers. As events like Amazon Prime Day surge in popularity and online shopping becomes even more routine, consumers need to be aware of these delivery scams.
Loan and investment scams
Extreme caution is crucial when approached with any investment opportunity offering high returns with little risk, or loans that claim to pay off debt unusually quickly. If the offer sounds too good to be true, it usually is.
Here are some essential tips to protect yourself from these loan and investment scams:
- Ask about risks and associated costs
- Resist high-pressure pitches or aggressive sales tactics
- Insist on receiving specifics in writing and follow up with your own research
- Don't commit solely because of the caller's title or trustworthiness
- Verify the registration of the investment and the promoter
- Dismiss any claims of completely risk-free investments or guaranteed returns; these are red flags, as genuine investments always carry some level of risk
Voice-cloning vishing scams
Voice-cloning technology uses artificial intelligence to craft alarmingly realistic fake audio or video clips. Cybercriminals are now using these AI tools to fabricate voice recordings that mimic those of a target's family member or trusted figure. For instance, a CEO's voice can be replicated to request a significant financial transfer. A lower-ranking employee might believe the call is genuine due to the accurate voice imitation and comply due to a sense of urgency and respect for the authoritative request.
As voice-cloning tools become more sophisticated and available, the risk of such scams grows, underscoring the need for strong security protocols and heightened vigilance—even when the caller sounds familiar.