What does whaling mean in cybersecurity?
Whaling attacks, often referred to as CEO fraud or executive phishing, are sophisticated cyberthreats targeting an organization's high-profile individuals. These attacks are carefully designed to deceive top executives, such as CEOs and CFOs, into giving away sensitive information. The term whaling reflects the high status of these targets, who have significant access to critical data and financial assets.
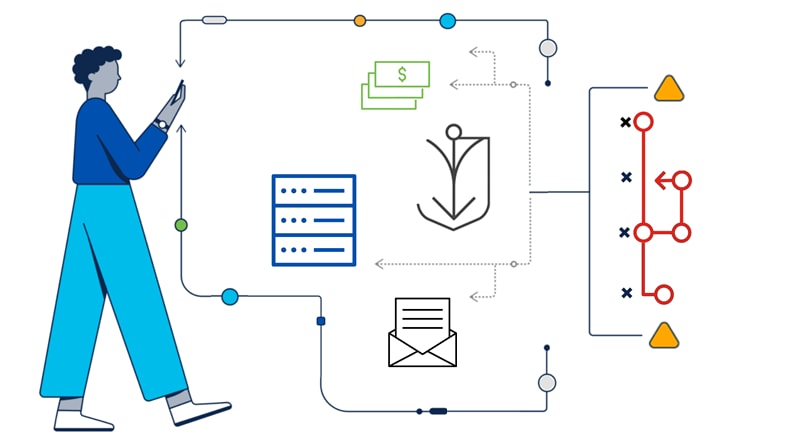
In these attacks, cybercriminals pretend to be trusted contacts. They use social engineering techniques to manipulate their victims into transferring funds or revealing confidential data.
To better understand whaling attacks, recognize their signs, and protect your organization's leaders and assets from phishing, continue reading.
What is the goal of a whaling attack?
The goal of a whaling attack is to deceive top personnel within an organization into taking actions that benefit the attacker for financial gain, data theft, or other malicious purposes. This can include:
- Transferring large sums of corporate money to the attacker's fraudulent accounts
- Divulging sensitive or confidential information, such as trade secrets, client data, or login credentials
- Granting access to secure systems, networks, or databases
- Executing unauthorized actions that can compromise the organization's security or operations, such as endorsing contracts or making policy changes
Who is vulnerable to whaling attacks?
Whaling attacks typically target high-ranking individuals within organizations. Executives like CEOs and CFOs are prime targets, given their broad decision-making power and access to sensitive information. Senior managers who control valuable company data and oversee financial transactions are also highly vulnerable.
But the attacks don't stop there. The risk also extends to personnel in human resources due to their handling of sensitive employee details. Employees in the finance and IT departments are at the forefront because they manage crucial financial data and system access, respectively. Even board members, equipped with insider knowledge and substantial influence, are often attractive targets for cybercriminals.
Personnel with significant authority or access to crucial data in an organization face the risk of whaling attacks. Without regular cyber-awareness training, an attack could cost your business millions, as global data breach costs averaged US$4.91 million in 2022.
What are the consequences of a whaling attack?
Successful whaling attacks can severely harm an organization's data, finances, operations, and reputation. These impacts can include:
- Data loss: The loss of critical data, intellectual property, or trade secrets can have enduring repercussions.
- Financial loss: Beyond immediate financial losses from a successful attack, the cost of recovery and upgrading measures to prevent future breaches can be substantial.
- Operational disruption: Whaling attacks can disrupt normal business operations that lead to downtime, reduced productivity, and potential loss of business opportunities.
- Reputation damage: Publicly disclosing a whaling attack can severely damage a company’s reputation and trust, especially if customer data is compromised.