How to protect your business from BEC
BEC phishing scams are becoming increasingly difficult to detect, but a multifaceted approach using best practices and security technologies can help minimize the frequency and impact of BEC attacks. Here's how you can fortify your defenses:
Enforce MFA on your accounts and workflows
Securing sensitive company data in today's threat landscape requires more than just a strong password. Multi-Factor Authentication (MFA) is no longer optional—it's a necessity. This secure access tool requires two or more verification factors, such as a fingerprint or token, to access resources. Adding an extra layer of verification can help keep attackers out who are armed with only a password.
To defend against BEC scams targeting critical employees, enforce MFA across your entire organization, especially for roles like senior executives, financial approvers, system administrators, and human resources personnel.
Invest in advanced email security solutions
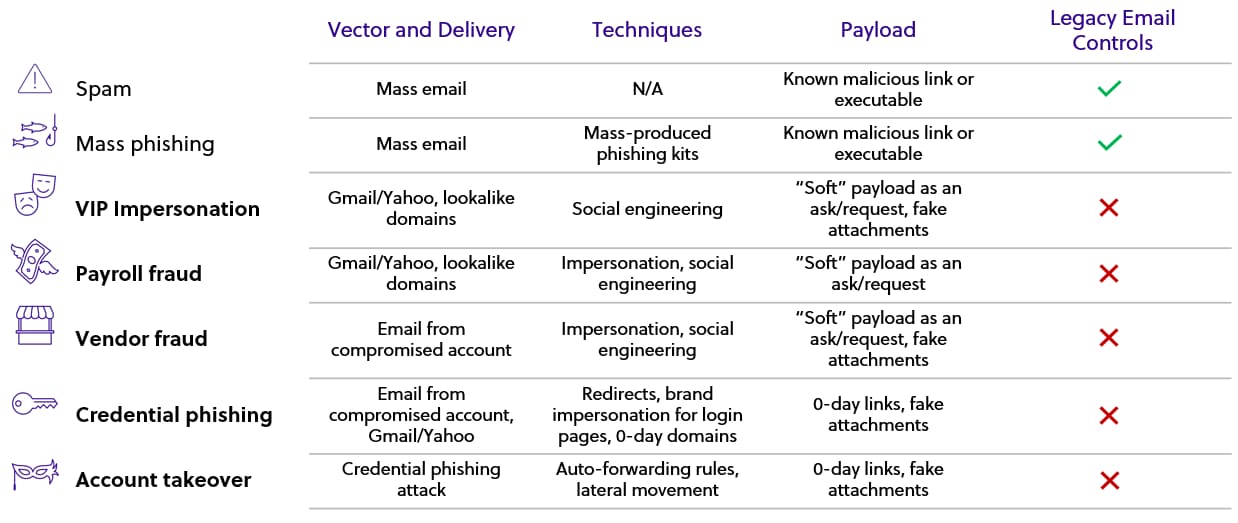
Today's increasing standard of hybrid work models often means relying more on digital communication, making email security more vital than ever. While email platforms offer fundamental, built-in protections, these measures aren't foolproof.
To defend against BEC, phishing, and malware attacks, look for a comprehensive email security solution like Cisco Secure Email Threat Defense that delivers:
- Global threat intelligence with real-time updates for proactive defense against emerging threats
- Forged email detection that blocks customized attacks exploiting executive accounts
- Advanced spam and phishing protection with a high accuracy rate in filtering harmful emails
- URL scanning and filtering to protect users from malicious links
- Domain-based message authentication, reporting, and conformance (DMARC) automated email authentication, which shields your company’s email domains from impersonation and potential abuse
- Dynamic malware defense tools with continuous threat analysis, file sandboxing, and automatic breach remediation
- Data loss prevention (DLP), complying with regulations to safeguard sensitive outbound information
- User-behavior training modules with threat simulations and education on best practices
Empower employees with continuous security education
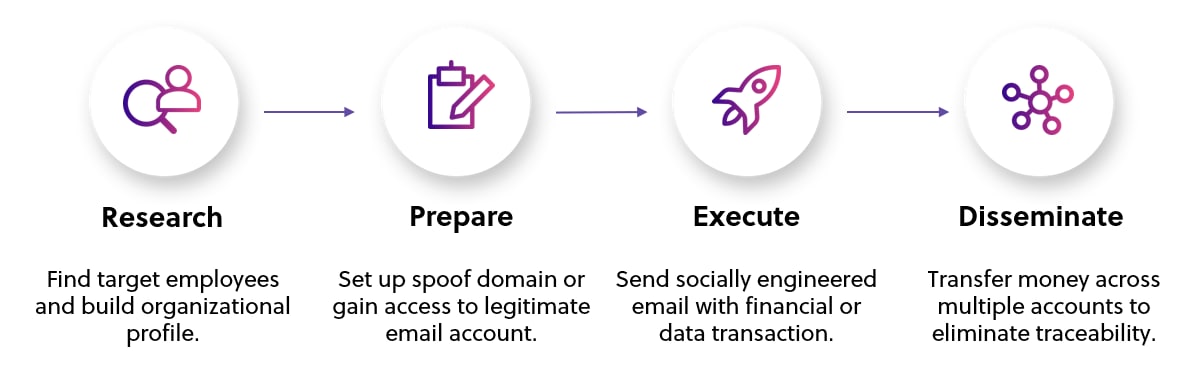
BEC attackers exploit busy routines, relying on employees overlooking deceptive emails during their busy workday. Though challenging, it's crucial to cultivate a culture of security mindfulness across all levels of your organization.
Train employees to look for these signs of a business email compromise scheme:
- Deadlines emailed at short notice that involve sending money or sensitive data
- Unusual purchase requests, even when they come from senior officials or trusted colleagues
- Emails from employees sharing new direct deposit details
- Requests to keep information confidential or bypass normal communication channels
- Requests for wire transfers that must be completed hastily or without proper authorization
- Misspellings, grammar, or language that is unusual for the sender
- Something that feels "off" or doesn't look right
Employees should trust their instincts and not be afraid to investigate. When in doubt, they should call the sender or send a separate email rather than replying to the one sent.
BEC fraud thrives on superficiality and haste. To stay head, foster a thoughtful, security-conscious culture and arm your staff with up-to-date knowledge and resources.
Establish escalation protocols and promote open communication
In the fight against BEC, quick, organized responses to threats are vital. Set clear escalation protocols so employees can immediately report unusual activities, helping to stop BEC attempts in their tracks. This structured approach is essential but works best when paired with an open company culture.
Encourage a workspace where everyone feels responsible for security and is comfortable raising suspicions, even if they're unsure. This open dialogue often catches inconsistencies that formal procedures might miss.
To reinforce this approach, encourage team members to:
- Speak up if something seems even slightly amiss, knowing it's better to be safe than sorry.
- Share insights or reservations about requests that deviate from the norm, as these could be invaluable in recognizing new scamming tactics.
- Understand that vigilance and questioning are signs of proactivity and responsibility, not distrust or paranoia.
Business email compromise attacks exploit human trust to steal data and millions of dollars from organizations. Though strong email protection is the first line of defense against BEC phishing, an educated, empowered, and confident workforce is crucial to identifying and stopping these attacks.