-
Cisco MDS 9000 Family Fabric Manager Configuration Guide, Release 1.3 (from Release 1.3(1) through Release 1.3(6))
-
Index
-
New and Changed Information
-
Preface
-
Product Overview
-
Getting Started with Cisco Fabric Manager
-
Overview of Fabric Manager Components
-
Before You Begin
-
Obtaining and Installing Licenses
-
Initial Configuration
-
Configuring High Availability
-
Software Images
-
Managing Modules
-
Managing System Hardware
-
Configuring and Managing VSANs
-
Configuring Interfaces
-
Configuring Trunking
-
Configuring PortChannels
-
Configuring and Managing Zones
-
Configuring Inter-VSAN Routing
-
Managing FLOGI, Name Server, FDMI, and RSCN Databases
-
Configuring Switch Security
-
Configuring Fabric Security
-
Configuring Port Security
-
Configuring Fibre Channel Routing Services and Protocols
-
Configuring IP Services
-
Configuring FICON
-
Configuring IP Storage
-
Configuring Call Home
-
Configuring Domain Parameters
-
Configuring Traffic Management
-
Configuring System Message Logging
-
Discovering SCSI Targets
-
Monitoring Network Traffic Using SPAN
-
Advanced Features and Concepts
-
Configuring Fabric Configuration Servers
-
Monitoring System Processes and Logs
-
Troubleshooting the Fabric
-
Troubleshooting Fabric Manager Issues
-
Table Of Contents
Configuring Gigabit Ethernet Interfaces
About Gigabit Ethernet Interfaces
Basic Gigabit Ethernet Configuration
About VLANs for Gigabit Ethernet
Verifying Gigabit Ethernet Connectivity
Gigabit Ethernet High Availability
Configuring Ethernet PortChannels
Creating FCIP Tunnels with Device Manager
Verifying Extended Link Protocols (ELP)
Creating FCIP Tunnels with Fabric Manager
Advanced FCIP Profile Configuration
Configuring TCP Listener Ports
Advanced FCIP Interface Configuration
Configuring the Number of TCP Connections
Configuring FCIP Write Acceleration
Ethernet PortChannels and Fibre Channel PortChannels
Routing iSCSI Requests and Responses
Presenting Fibre Channel Targets as iSCSI Targets
iSCSI Virtual Target Configuration Examples
Presenting iSCSI Hosts as Virtual Fibre Channel Hosts
Making the Dynamic Initiator WWN Mapping Static
Assigning VSAN Membership to iSCSI Hosts
Assigning VSANs to a iSCSI Interface
Configuring iSCSI Proxy Initiators
Configuring the iSCSI Proxy Initiator
Fibre Channel Zoning-Based Access Control
Configuring an Authentication Mechanism
Configuring an iSCSI RADIUS Server
Multiple IPS Ports Connected to the Same IP Network
Ethernet PortChannel-Based High Availability
iSCSI Authentication Setup Guidelines
Configuring Storage Name Services
Creating iSNS Profiles and Tagging Profiles
Associating IP Profiles to Interfaces
Configuring IP Storage
Cisco MDS 9000 Family IP storage (IPS) services modules extend the reach of Fibre Channel SANs by using open-standard, IP-based technology. The switch connects separated SAN islands using Fibre Channel over IP (FCIP), and allows IP hosts to access Fibre Channel storage using iSCSI protocol.
FCIP and iSCSI features are specific to the IPS module and can be implemented in Cisco MDS 9216 switches or Cisco MDS 9500 Directors running Cisco MDS SAN-OS Release 1.1(x) or above.
This chapter contains the following topics:
•
Configuring Gigabit Ethernet Interfaces
•
Configuring Storage Name Services
•
Adding IP Filters to Profiles
•
Associating IP Profiles to Interfaces
IP Storage Services Module
The IPS services module (IPS module) allows you to use FCIP and iSCSI features. It integrates seamlessly into the Cisco MDS 9000 Family, and supports the full range of features available on other switching modules, including VSANs, security, and traffic management.
The following types of IPS modules are currently available for use in any Cisco MDS 9216 switch or any switch in the Cisco MDS 9500 Series:
•
The 4-port, hot-swappable IPS module (IPS-4) has four Gigabit Ethernet ports.
•
The 8-port, hot-swappable IPS module (IPS-8) has eight Gigabit Ethernet ports.
Each port in either module can be configured to support FCIP protocol, iSCSI protocol, or both protocols simultaneously.
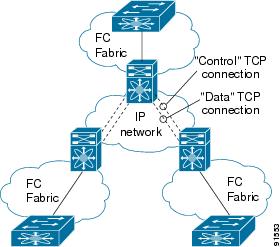
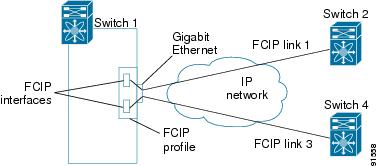
•
FCIP—FCIP transports Fibre Channel frames transparently over an IP network between two Cisco MDS 9000 Family switches or other FCIP standards-compliant devices. The figure below depicts the FCIP scenarios in which the IPS module is used.
Figure 24-1 FCIP Scenarios
•
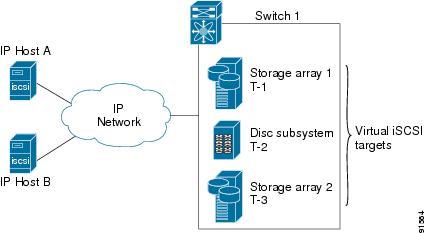
iSCSI—The IPS module provides IP hosts access to Fibre Channel storage devices. The IP host sends SCSI commands encapsulated in iSCSI protocol data units (PDUs) to a MDS 9000 IPS port over a Transmission Control Protocol (TCP)/Internet Protocol (IP) connection. At this point, the commands are routed from an IP network into a Fibre Channel network and forwarded to the intended target. Figure 24-2 depicts the iSCSI scenarios in which the IPS module is used.
Figure 24-2 iSCSI Scenarios
Configuring Gigabit Ethernet Interfaces
This section contains the following topics:
•
About Gigabit Ethernet Interfaces
•
Basic Gigabit Ethernet Configuration
•
About VLANs for Gigabit Ethernet
•
Verifying Gigabit Ethernet Connectivity
•
Gigabit Ethernet High Availability
About Gigabit Ethernet Interfaces
Both FCIP and iSCSI rely on TCP/IP for network connectivity. On the IPS module, connectivity is provided in the form of Gigabit Ethernet interfaces that are appropriately configured. This section covers the steps required to configure IP for subsequent use by FCIP and iSCSI.
A new port mode, called IPS, is defined for Gigabit Ethernet ports on the IPS module. IP storage ports are implicitly set to IPS mode, so they can only be used to perform iSCSI and FCIP storage functions. IP storage ports do not bridge Ethernet frames or route other IP packets.
Tip
Gigabit Ethernet ports on the IPS module should not be configured in the same Ethernet broadcast domain as the management Ethernet port—they should be configured in a different broadcast domain, either by using separate standalone hubs or switches or by using separate VLANs.
Basic Gigabit Ethernet Configuration
Figure 24-3 depicts a basic Gigabit Ethernet configuration.
Figure 24-3 Gigabit Ethernet Configuration
You can configure the switch to receive and transfer large (or jumbo) frames on a port. The default IP MTU frame size is 1500 bytes for all Ethernet ports. By configuring jumbo frames on a port, the MTU size can be increased to 9000 bytes. The following example sets the size to 3000 bytes. Independent of the MTU size, the IPS module does not pack multiple IP frames (converted to FCIP or to iSCSI).
The minimum MTU size for a port running iSCSI is 512 bytes.
About VLANs for Gigabit Ethernet
Virtual LANs (VLANs) create multiple virtual Layer 2 networks over a physical LAN network. VLANs provide traffic isolation, security, and broadcast control.
IPS gigabit ethernet ports automatically recognize Ethernet frames with IEEE 802.1Q VLAN encapsulation. If you need to have traffic from multiple VLANs terminated on one IPS port, configure subinterfaces—one for each VLAN. Use the VLAN ID as a subscription to the Gigabit Ethernet interface name to create the subinterface name <the slot-number>/<port-number>.<VLAN-ID>).
If the IPS module is connected to a Cisco Ethernet switch, and you need to have traffic from multiple VLANs coming to one IPS port, verify the following requirements on the Ethernet switch:
•
The Ethernet switch port connected to the IPS module is configured as a trunking port.
•
The encapsulation is set to 802.1Q and not ISL, which is the default.
Verifying Gigabit Ethernet Connectivity
The ping command sends echo request packets out to a remote device at an IP address that you specify.
Once the Gigabit Ethernet interfaces are connected with valid IP addresses, verify the interface connectivity on each switch using the ping command. Ping the IP host using the IP address of the host to verify that the static IP route is configured correctly.
If the connection fails, verify the following, and repeat the ping command:
•
The IP address for the destination (IP host) is correctly configured.
•
The host is active (powered on).
•
The IP route is configured correctly.
•
The IP host has a route to get to the Gigabit Ethernet interface subnet.
•
The Gigabit Ethernet interface is in the up state.
Gigabit Ethernet High Availability
Virtual Router Redundancy Protocol (VRRP) and Ethernet PortChannels are two Gigabit Ethernet features that provide high availability for iSCSI and FCIP services.
Configuring VRRP
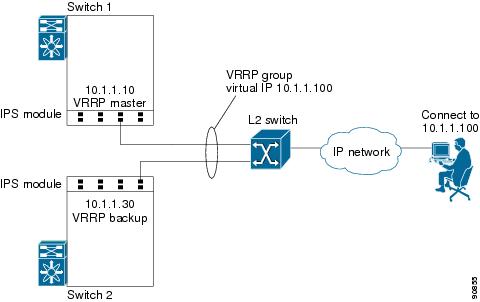
VRRP provides a redundant alternate path to the Gigabit Ethernet port for iSCSI and FCIP services.
VRRP provides IP address fail over protection to an alternate Gigabit Ethernet interface so the IP address is always available.
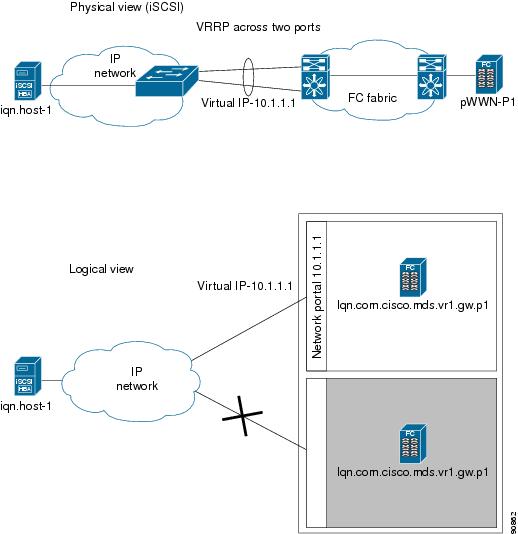
Figure 24-4 VRRP Scenario
In Figure 24-4, all members of the VRRP group must be IP storage Gigabit Ethernet ports. VRRP group members can be one or more of the following interfaces:
•
One or more interfaces in the same IPS module
•
Interfaces across IPS modules in one switch
•
Interfaces across IPS modules in different switches
•
Gigabit Ethernet subinterfaces
•
Ethernet PortChannels
•
Subinterfaces
The VRRP preempt option is not supported on IP storage Gigabit Ethernet interfaces. However, if the virtual IP address is also the IP address for the interface, then preemption is implicitly applied.
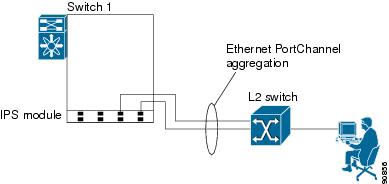
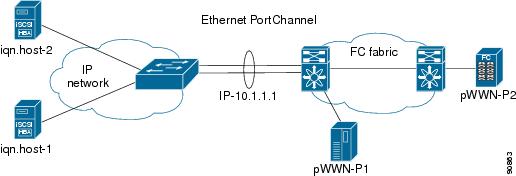
Configuring Ethernet PortChannels
Ethernet PortChannels refer to the aggregation of multiple physical Gigabit Ethernet interfaces into one logical Ethernet interface to provide link redundancy and, in some cases, higher aggregated bandwidth and load balancing.
The data traffic from one TCP connection always travels on the same physical links. An Ethernet switch connecting to the MDS Gigabit Ethernet port can implement load balancing based on its IP address, its source-destination MAC address, or its IP and port. In iSCSI scenarios if the Ethernet switch is not capable of load-balancing based on the IP address or the IP port, multiple iSCSI initiators are required to take advantage of the Ethernet PortChannel feature.
The Cisco Ethernet switch's PortChannel should be configured as a static PortChannel, and not the default 802.3aa protocol.
Ethernet PortChannels can only aggregate two physical interfaces that are adjacent to each other on a given IPS module.
PortChannel members must be one of these combinations: ports 1-2, ports 3-4, ports 5-6, or ports 7-8.
Figure 24-5 Ethernet PortChannel Scenario
In Figure 24-5, Gigabit Ethernet ports 3 and 4 in slot 9 are aggregated into an Ethernet PortChannel.
All FCIP data traffic for one FCIP link is carried on one TCP connection. Consequently, the aggregated bandwidth will be one Gbps for that FCIP link.
PortChannel configuration specified in also apply to Ethernet PortChannel configurations.
PortChannel interfaces provide configuration options for both Gigabit Ethernet and Fibre Channel. However, based on the PortChannel membership, only Gigabit Ethernet parameters or Fibre Channel parameters are applicable.
Gigabit Ethernet interfaces cannot be added to a
PortChannel if one of the following cases apply: - if the interface already has an IP address assigned, or - if subinterfaces are configured on that interface.
Configuring CDP
The Cisco Discovery Protocol (CDP) is supported on the management Ethernet interface on the supervisor module and the Gigabit Ethernet interface on the IPS module.
IPS Core Dumps
IPS core dumps are different from the system kernel core dumps for other modules. When the IPS module operating system (OS) unexpectedly resets, it is sometimes useful to obtain a copy of the memory image (called a IPS core dump) to identify the cause of the reset. Under that condition, the IPS module sends the core dump to the supervisor module for storage. Core dumps take up significant space and hence the level of what gets stored can be configured using one of the two options:
•
Partial core dumps (default)—Each partial core dump consists of four parts (four files).
•
Full core dumps—Each full core dump consists of 75 parts (75 files). This dump cannot be saved on the supervisor module due to its large space requirement.
Configuring FCIP
This section contains the following topics:
•
Creating FCIP Tunnels with Device Manager
•
Creating FCIP Tunnels with Fabric Manager
•
Advanced FCIP Profile Configuration
•
Advanced FCIP Interface Configuration
•
Ethernet PortChannels and Fibre Channel PortChannels
About FCIP
The Fibre Channel over IP Protocol (FCIP) is a tunneling protocol that connects geographically distributed Fibre Channel storage area networks (SAN islands) transparently over IP local area networks (LANs), metropolitan area networks (MANs), and wide area networks (WANs).
FCIP uses TCP as a network layer transport.
To configure the IPS module for FCIP, you should have a basic understanding of the following concepts:
•
FCIP and VE Ports
•
FCIP Links
•
FCIP Profiles
•
FCIP Interfaces
FCIP and VE Ports
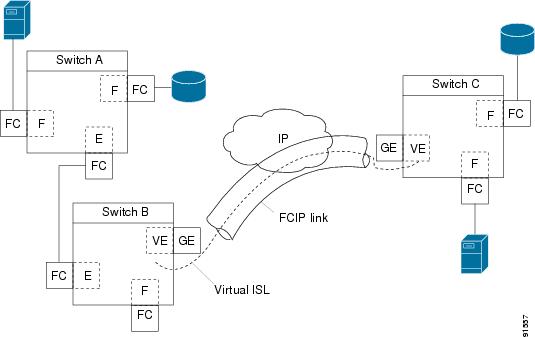
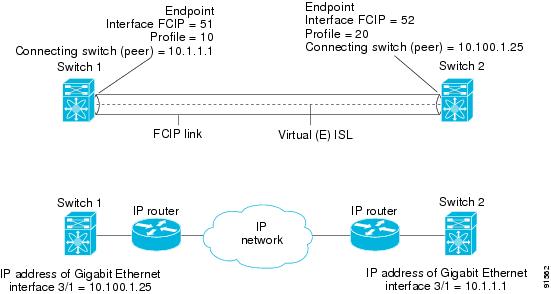
Figure 24-6 describes the internal model of FCIP with respect to Fibre Channel inter switch links (ISLs) and Cisco's enhanced ISLs (EISLs).
FCIP defines virtual E (VE) ports, which behave exactly like standard Fibre Channel E ports, except that the transport in this case is FCIP instead of Fibre Channel. The only requirement is for the other end of the VE port to be another VE port.
A virtual ISL is established over a FCIP link and transports Fibre Channel traffic. Each associated virtual ISL looks like a Fibre Channel ISL with either an E port or a TE port at each end.
Figure 24-6 FCIP Links and Virtual ISLs
FCIP Link
FCIP links consist of one or more TCP connections between two FCIP link end points. Each link carries encapsulated Fibre Channel frames.
When the FCIP link comes up, the VE ports at both ends of the FCIP link create a virtual Fibre Channel (E)ISL and initiate the E port protocol to bring up the (E)ISL.
By default, the FCIP feature on any Cisco MDS 9000 Family switch creates two TCP connections for each FCIP link.
•
One connection is used for data frames.
•
The second connection is used only for Fibre Channel control frames, i.e. switch-to-switch protocol frames (all Class F) frames. This arrangement is used to provide low latency for all control frames.
To enable FCIP on the IPS module, a FCIP profile and FCIP interface (interface FCIP) must be configured.
The FCIP link is established between two peers, the VE port initialization behavior is identical to a normal E port. This behavior is independent of the link being FCIP or pure Fibre Channel, and is based on the E port discovery process (ELP, ESC).
Once the FCIP link is established, the VE port behavior is identical to E port behavior for all inter-switch communication (including domain management, zones, and VSANs). At the Fibre Channel layer, all VE and E port operations are identical.
FCIP Profiles
The FCIP profile contains information about local IP address and TCP parameters. The profile defines the following information:
•
the local connection points (IP address and TCP port number)
•
the behavior of the underlying TCP connections for all FCIP links that use this profile
The FCIP profile's local IP address determines the Gigabit Ethernet port where the FCIP links terminates.
Figure 24-7 FCIP Profile and FCIP Links
FCIP Interface
The FCIP interface is the local end point of the FCIP link and a VE port interface. All the FCIP and E port parameters are configured in context to the FCIP interface.
The FCIP parameters consist of the following:
•
The FCIP profile determines which Gigabit Ethernet port initiates the FCIP links and defines the TCP connection behavior.
•
Peer information.
•
Number of TCP connections for the FCIP link.
•
E port parameters—Trunking mode and trunk allowed VSAN list.
Enabling FCIP
To begin configuring the FCIP feature, you must explicitly enable FCIP on the required switches in the fabric. By default, this feature is disabled in all switches in the Cisco MDS 9000 Family.
The configuration and verification commands for the F IP feature are only available when FCIP is enabled on a switch. When you disable this feature, all related configurations are automatically discarded.
Basic FCIP Configuration
To configure a FCIP link, follow these steps on both switches.
Step 1
Configure the Gigabit Ethernet interface.
Step 2
Create a FCIP profile, assign the Gigabit Ethernet interface's IP address to the profile.
Step 3
Create a FCIP interface, assign the profile to the interface.
Step 4
Configure the peer IP address for the FCIP interface.
Step 5
Enable the interface.
Creating FCIP Profiles
To create a FCIP profile, you must assign a local IP address of a Gigabit Ethernet interface or subinterface to the FCIP profile.
Figure 24-8 Assigning Profiles to Each Gigabit Ethernet Interface
Creating FCIP Links
When two FCIP link end points are created, a FCIP link is established between the two IPS modules. To create a FCIP link, assign a profile to the FCIP interface and configure the peer information. The peer IP switch information initiates (creates) a FCIP link to that peer switch.
Figure 24-9 Assigning Profiles to Each Gigabit Ethernet Interface
Creating FCIP Tunnels with Device Manager
To create and manage FCIP tunnels with Device Manager, first verify that the IPS module is inserted in the required Cisco MDS 9000 Family switches, and that the switches' Gigabit Ethernet interfaces are connected and the connectivity verified using the ping command. The steps in creating FCIP tunnels are:
Assigning FCIP Profiles
You can use Device Manager to configure FCIP tunnels between switches. First, you must create FCIP profiles, and then bind the interfaces to the profile. To bind an FCIP profile to an interface, use the IP address of the interface in the FCIP profile's IP address configuration. Profile numbers range from 1 to 255. The interface associated with a profile can be either of the following:
•
EtherChannel
•
Ethernet subinterface slot and port (or slot, port, and VLAN ID)
To create and bind profiles on a Gigabit Ethernet interface, follow these steps.
Step 1
Be sure you are connected to a switch that contains an IPS module.
Step 2
Open Device Manager.
Step 3
Choose IP > FCIP.
Step 4
Click the Profiles tab if it is not already selected. You see a list of any profiles that are already bound, along with their IP addresses, in the FCIP Profiles dialog box.
Step 5
To add a new profile, click Create. You see the Create FCIP Profiles dialog box.
Step 6
Enter the profile ID in the ID field.
Step 7
Select an IP address of the interface to which you want to bind the profile from the IP Address drop-down list.
Step 8
Enter all the optional information, if desired.
Step 9
Click Create to add this profile to the table. Click Close to close the Create FCIP Profiles dialog box without adding the profile.
Creating Tunnels
Each Gigabit Ethernet interface can have three active FCIP tunnels on it at one time.
To create these tunnels, follow these steps:
Step 1
Be sure you are connected to a switch that contains an IPS module.
Step 2
Open Device Manager.
Step 3
Choose IP > FCIP.
Step 4
Click the Tunnels tab if it is not already selected. The FCIP Tunnels dialog box lists the remote IP address of the interface together with optional attributes.
Step 5
Click the Create button. You see the Create FCIP Tunnels dialog box.
Step 6
Enter the entity ID in the ID field.
Step 7
Enter a remote IP address as the endpoint to which you want to link.
Step 8
Enter all the optional information, if desired.
Step 9
Click Create to add this tunnel to the table. Click Close to close the Create FCIP Tunnels dialog box without adding the tunnel.
Verifying Interfaces
To verify the interfaces, follow these steps:
Step 1
Be sure you are connected to a switch that contains an IPS module.
Step 2
Open Device Manager.
Step 3
Choose Interface > FCIP.
Step 4
Click the Interfaces tab (if it is not already selected) to see the FCIP Interfaces dialog box.
Verifying Extended Link Protocols (ELP)
To verify the extended link protocol, follow these steps:
Step 1
Be sure you are connected to a switch that contains an IPS module.
Step 2
Open Device Manager.
Step 3
Choose IP > FCIP.
Step 4
Click the ELP tab (if it is not already selected) to see the FCIP ELP dialogist.
Checking Trunk Status
To check the trunk status, follow these steps:
Step 1
Be sure you are connected to a switch that contains an IPS module.
Step 2
Open Device Manager.
Step 3
Choose IP > FCIP.
Step 4
Click the Trunk Status tab (if it is not already selected) to see the FCIP Trunk Status dialog box.
Checking for Interface Errors
To check for interface errors, follow these steps:
Step 1
Be sure you are connected to a switch that contains an IPS module.
Step 2
Open Device Manager.
Step 3
Choose IP > FCIP.
Step 4
Click the Interface Errors tab (if it is not already selected) to see a list of FCIP-specific end-point/interface errors in the FCIP Interface Errors dialog box.
Creating FCIP Tunnels with Fabric Manager
To create and manage FCIP tunnels with Fabric Manager, you use the FCIP Wizard. First verify that the IPS module is inserted in the required Cisco MDS 9000 Family switches, and that the switches' Gigabit Ethernet interfaces are connected and the connectivity verified. The steps in creating FCIP tunnels using the FCIP Wizard are:
•
Select the endpoints
•
Choose the interfaces' IP addresses
•
Specify link attributes
To create FCIP tunnels using the FCIP Wizard, follow these steps:
Step 1
Open the FCIP Tunnels Wizard by clicking on its icon in the Fabric Manager toolbar.
Figure 24-10 FCIP Tunnels Wizard
Step 2
Choose the endpoints.
Step 3
Choose the ports' IP addresses.
Step 4
Choose the link attributes.
Advanced FCIP Profile Configuration
A basic FCIP configuration uses the local IP address to configure the FCIP profile. In addition to the local IP address and the local port, you can specify other TCP parameters as part of the FCIP profile configuration.
FCIP configuration options can be accessed from the switch(config- profile)# submode prompt.
Configuring TCP Listener Ports
The default TCP port for FCIP is 3225. You can change this port using the port command.
Configuring TCP Parameters
This section provides details on the TCP parameters that can be configured to control TCP behavior in a switch. The following TCP parameters can be configured.
Minimum Retransmit Timeout
The tcp minimum-retransmit-time option controls the minimum amount of time TCP waits before retransmitting. By default, this value is 200 milliseconds.
Keepalive Timeout
The tcp keepalive-timeout option enables you to configure the interval between which the TCP connection verifies if the FCIP link is functioning. This ensures that a FCIP link failure is detected quickly even when there is no traffic.
If the TCP connection is idle for more than the specified time, then keepalive timeout packets are sent to ensure that the connection is active. This command can be used to tune the time taken to detect FCIP link failures.
The first interval during which the connection is idle is 60 seconds (default). When the connection is idle for 60 seconds, 8 keepalive probes are sent at 1-second intervals. If no response is received for these 8 probes and the connection remains idle throughout, that FCIP link is automatically closed.
Only the first interval (during which the connection is idle) can be changed from the default of 60 seconds. This interval is identified using the keepalive-timeout
option. The valid range is from 1 to 7200 seconds.
Maximum Retransmissions
The tcp max-retransmissions option specifies the maximum number of times a packet is retransmitted before TCP decides to close the connection.
Path MTU
Path MTU (PMTU) is the minimum MTU on the IP network between the two end points of the FCIP link. PMTU discovery is a mechanism by which TCP learns of the PMTU dynamically and adjusts the maximum TCP segment accordingly (RFC 1191).
By default, PMTU discovery is enabled on all switches with a default timeout of 3600 seconds. If TCP reduces the size of the max segment because of PMTU change, the reset-timeout specifies the time after which TCP tries the original MTU.
SACK
TCP may experience poor performance when multiple packets are lost within one window. With the limited information available from cumulative acknowledgments, a TCP sender can only learn about a single lost packet per round trip time. A selective acknowledgment (SACK) mechanism helps overcome the limitations of multiple lost packets during a TCP transmission.
The receiving TCP sends back SACK advertisements to the sender. The sender can then retransmit only the missing data segments. By default, SACK is enabled on Cisco MDS 9000 Family switches.
Window Management
The optimal TCP window size is computed using the max-bandwidth option, the min-available-bandwidth option, and the dynamically-measured round-trip-time (RTT). The interaction and the resulting TCP behavior is outlined below:
The configured round-trip-time option determines the window scaling factor of the TCP connection. This option is only an approximation. The measured RTT value overrides the round-trip-time option for window management. If the configured round-trip-time is too small compared to the measured RTT, then the link may not be fully utilized due to the window scaling factor being too small.
•
If the average rate of the fc traffic over the preceding RTT is less than the min-available-bandwidth * RTT, every FC burst is sent immediately at the min-available-bandwidth rate, provided no TCP drops occur.
•
If the average rate of the FC traffic is greater than min-available-bandwidth * RTT, but less than max-bandwidth * RTT, then if the FC traffic is transmitted in burst sizes smaller than the configured CWM value all the bursts are sent immediately by FCIP at the max-bandwidth rate.
•
If the average rate of the FC traffic is larger than the min-available-bandwidth * RTT and the burst size is greater than the CWM value, some traffic will not be sent immediately.
The maximum-bandwidth option and the measured round-trip-time together determine the maximum window size.
The min-available-bandwidth option and the measured round-trip-time together determine the threshold below which TCP aggressively maintains a window size sufficient to transmit at min-available-bandwidth. The software uses standard TCP rules to increase the window beyond the one required to maintain the min-available-bandwidth in order to reach the max-bandwidth. The defaults are max-bandwidth = 1G, min-available-bandwidth = 15 Mbps, and round-trip-time =1 ms.
Buffer Size
The send-buffer-size option defines the required additional buffering (beyond the normal send window size) that TCP allows before flow controlling the switch's egress path for the FCIP interface. The default buffer size is 0 KB.
Quality of Service
The Quality of Service (QoS) feature specifies the differentiated services code point (DSCP) value to mark all IP packets (type of service—STOS field in the IP header).
•
The control DSCP value applies to all FCIP frames in the control TCP connection.
•
The data DSCP value applies to all FCIP frames in the data connection.
If the FCIP link has only one TCP connection, that data DSCP value is applied to all packets in that connection.
Monitoring Window Congestion
The congestion window monitoring (CWM) option determines the maximum burst size allowed after an idle period.
•
If the FC traffic burst is smaller than the configured CWM value, every packet is sent immediately, provided that no TCP drops were detected in the previous RTT.
•
If FC traffic burst is larger than the configured CWM value, the excess packets will be sent during succeeding RTTs.
By default the tcpcwm option is enabled and the default burst size is 10 KB.
Tip
We recommend that this feature remain enabled to realize optimal performance. Increasing the CWM burst size can result in more packet drops in the IP network, impacting TCP performance. Only if the IP network has sufficient buffering, try increasing the CWM burst size beyond the default to achieve lower transmit latency.
Advanced FCIP Interface Configuration
You can establish connection to a peer by configuring one or more of the following options for the FCIP interface. To do so, you must first create the interface and enter the config-if submode.
Configuring Peers
To establish a FCIP link with the peer, you can use one of two options:
•
—Used to configure both ends of the FCIP link. Optionally, you can also use the peer TCP port along with the IP address.
•
—Used to configure one end of the FCIP link when security gateways are present in the IP network. Optionally, you can also use the port and profile ID along with the IP address.
Peer IP Address
The basic FCIP configuration uses the peer's IP address to configure the peer information. You can also specify the peer's port number to configure the peer information. If you do not specify a port, the default 3225 port number is used to establish connection.
Special Frames
You can alternatively establish a FCIP link with a peer using an optional protocol called special frames. You can enable or disable the special-frame option. On the peer side, the special-frame option must be enabled in order to establish the FCIP link. When the special-frame option is enabled, the peer IP address (and optionally the port or the profile ID) only needs to be configured on one end of the link. Once the connection is established, a special frame is exchanged to discover and authenticate the link.
By default, the special frame feature is disabled.
Refer to the Fibre Channel IP standards for further information on special frames.
Tip
Special frame negotiation provides an additional authentication security mechanism because the link validates the WWN of the peer switch.
Configuring Active Connection
Use the passive-mode option to configure the required mode for initiating an IP connection. By default, active mode is enabled to actively attempt an IP connection.
If you enable the passive mode, the switch does not initiate a TCP connection and merely waits for the peer to connect to it.
Ensure that both ends of the FCIP link are not configured as passive mode. If both ends are configured as passive, the connection will not be initiated.
Configuring the Number of TCP Connections
Use the tcp-connection option to specify the number of TCP connections from a FCIP link. By default, the switch tries two (2) TCP connections for each FCIP link. You can configure 1 or 2 TCP connections.
For example, the Cisco PA-FC-1G Fibre Channel port adapter which has only 1 (one) TCP connection interoperates with any switch in the Cisco MDS 9000 Family. One TCP connection is within the specified limit and you can change the configuration on the switch using the tcp-connection 1 command. If the peer initiates one TCP connection, and your MDS switch is configured for two TCP connections, the software handles it gracefully and moves on with just one connection.
Enabling Time Stamps
Use the time-stamp option to enable or disable FCIP time stamps on a packet. The time stamp option instructs the switch to discard packets that are outside the specified time. By default, the time-stamp option is disabled.
The acceptable-diff option specifies the time range within which packets can be accepted. If the packet arrived within the range specified by this option, the packet is accepted. Otherwise, it is dropped. By default if a packet arrives within a 1000 millisecond interval (+ or -1000 milliseconds), that packet is accepted.
If the time-stamp option is enabled, be sure to configure NTP on both switches.
B Port Interoperability Mode
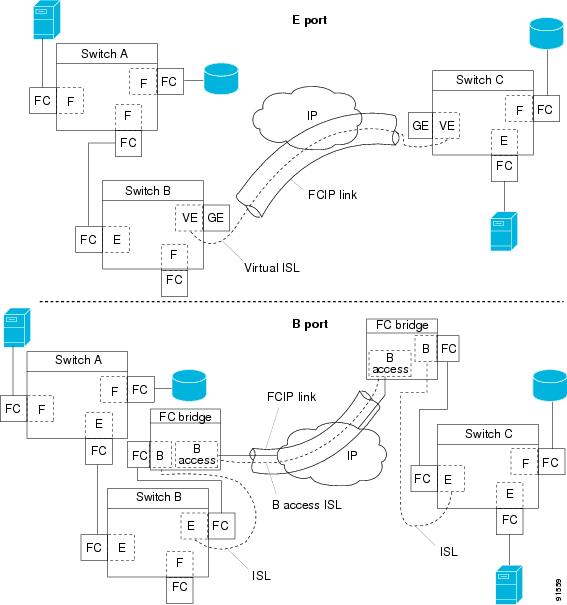
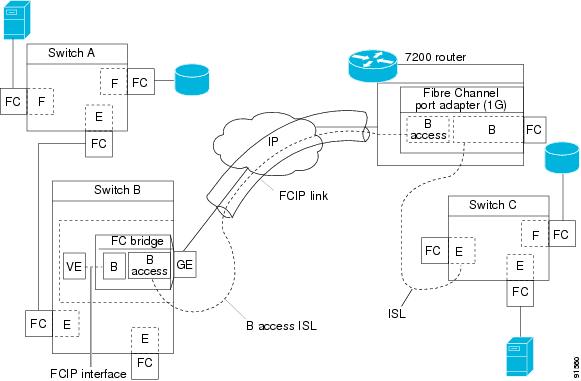
While E ports typically interconnect Fibre Channel switches, some SAN extender devices, such as Cisco's PA-FC-1G Fibre Channel port adapter and the SN 5428-2 storage router, implement a bridge port model to connect geographically dispersed fabrics. This model uses B port as described in the T11 Standard FC-BB-2. depicts a typical SAN extension over an IP network.
Figure 24-11 FCIP B Port and Fibre Channel E Port
B ports bridge Fibre Channel traffic from one E port to a remote E port without participating in fabric-related activities such as principal switch election, Domain ID assignment, and Fibre Channel routing (FSPF). For example, Class F traffic entering a SAN extender does not interact with the B port. The traffic is transparently propagated (bridged) over a WAN interface before exiting the remote B port. This bridge results in both E ports exchanging Class F information which ultimately leads to normal ISL behavior such as fabric merging and routing.
FCIP links between B port SAN extenders do not exchange the same information as FCIP links between E ports, and are therefore incompatible. This is reflected by the terminology used in FC-BB-2: while VE ports establish a virtual ISL over a FCIP link, B ports use a B access ISL.
The IPS module supports FCIP links that originate from a B port SAN extender device by implementing the B access ISL protocol on a Gigabit Ethernet interface. Internally, the corresponding virtual B port connects to an virtual E port which completes the end-to-end E port connectivity requirement.
Figure 24-12 FCIP Link Terminating in a B Port Mode
The B port feature in the IPS module allows remote B port SAN extenders to communicate directly with a Cisco MDS 9000 Family switch, therefore eliminating the need for local bridge devices.
Configuring B Ports
When a FCIP peer is a SAN extender device that only supports Fibre Channel B ports, you need to enable the B port mode for the FCIP link. When a B port is enabled, the E port functionality is also enabled and they coexist. If the B port is disabled, the E port functionality remains enabled.
E Port Configurations
All configuration commands that apply to E ports, also apply to FCIP interfaces. The following features are also available FCIP interfaces:
•
VSANs
–
FCIP interfaces can be a member of any VSAN.
–
Trunk mode
–
Trunk mode can be configured.
–
Trunk allowed VSANs can be configured
–
PortChannels
–
Multiple FCIP links can be bundled into a Fibre Channel PortChannel.
–
FCIP links and Fibre Channel links cannot be combined in one PortChannel.
–
FSPF
–
Fibre Channel domains
–
Zone merge
–
Importing the zone database from the adjacent switch.
–
Exporting the zone database from the adjacent switch.
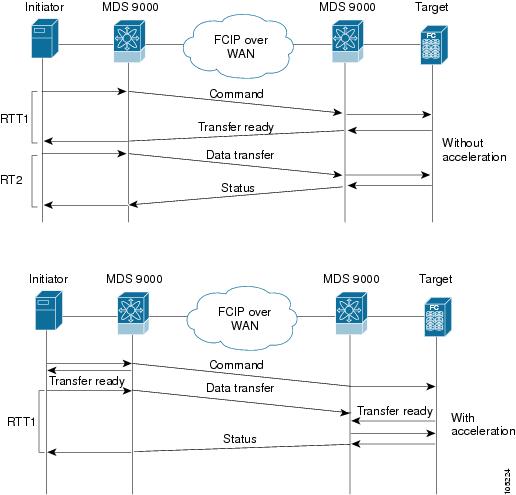
Configuring FCIP Write Acceleration
The FCIP Write Acceleration feature in SAN-OS 1.3(3) enables you to significantly improve application performance when storage traffic is routed over wide area networks using FCIP. When FCIP Write Acceleration is enabled, WAN throughput is maximized by minimizing the impact of WAN latency for the command to transfer ready acknowledgement.
The write acceleration feature is disabled by default and must be enabled on both sides of the FCIP link. If it is only enabled on one side of the FCIP tunnel, the tunnel will not initialize.
Figure 24-13 FCIP Link Write Acceleration
In Figure 24-13, some data sent by the host is queued on the target before the target issues a Transfer Ready. This way the actual write operation may be done in a less time than the write operation without the write acceleration feature being enabled.
Tip
FCIP write acceleration will not work if the FCIP port is part of a PortChannel or if there are multiple paths with equal weight between the initiator and the target port. Such a configuration might cause either SCSI discovery failure or broken write or read operations.
Enabling FCIP Compression
The FCIP compression feature introduced in Release 1.3(x) allows IP packets to be compressed on the FCIP link if this feature is enabled on that link. By default the FCIP compression is disabled.
This feature uses the Lempel-Zif-Stac (LZS) compression algorithm to compress packets.
The high-throughput mode allows faster compression but the compression ratio may be lower. The high-comp-ratio mode allows a higher compression ratio, but the throughput may be lower.
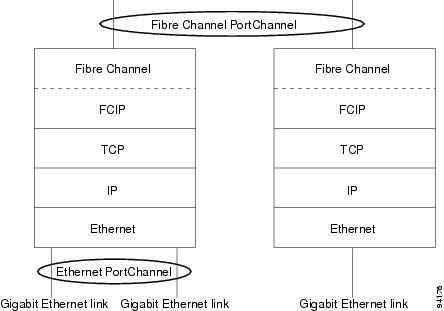
Fibre Channel PortChannels
Figure 24-14 provides an example of a PortChannel-based load balancing configuration. To perform this configuration, you need two IP addresses on each SAN island. This solution addresses link failures.
Figure 24-14 PortChannel Based Load Balancing
The following characteristics set Fibre Channel PortChannel solutions apart from other solutions:
•
The entire bundle is one logical (E)ISL link.
•
All FCIP links in the PortChannel should be across the same two switches.
•
The Fibre Channel traffic is load balanced across the FCIP links in the PortChannel.
FSPF
Figure 24-15 displays a FPSF-based load balancing configuration example. This configuration requires two IP addresses on each SAN island, and addresses IP and FCIP link failures.
Figure 24-15 FSPF-Based Load Balancing
The following characteristics set FSPF solutions apart from other solutions:
•
Each FCIP link is a separate (E)ISL.
•
The FCIP links can connect to different switches across two SAN islands.
•
The Fibre Channel traffic is load balanced across the FCIP link.
VRRP
displays a VRRP-based high availability FCIP configuration example. This configuration, requires at least two physical Gigabit Ethernet ports connected to the Ethernet switch on the island where you need to implement high availability using VRRP.
Figure 24-16 VRRP-Based High Availability
The following characteristics set VRRP solutions apart from other solutions:
•
If the active VRRP port fails, the standby VRRP port takes over the VRRP IP address.
•
When the VRRP switchover happens, the FCIP link automatically disconnects and reconnects.
•
This configuration has only one FCIP (E)ISL link.
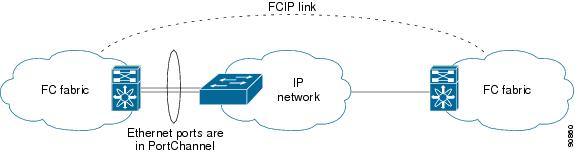
Ethernet PortChannels
Figure 24-17 displays a Ethernet PortChannel-based high availability FCIP example. This solution addresses the problem caused by individual Gigabit Ethernet link failures.
Figure 24-17 Ethernet PortChannel-Based High Availability
The following characteristics set Ethernet PortChannel solutions apart from other solutions:
•
The Gigabit Ethernet link level redundancy ensures a transparent failover if one of the Gigabit Ethernet links fails.
•
Two Gigabit Ethernet ports in one Ethernet PortChannel appears like one logical Gigabit Ethernet link.
•
The FCIP link stays up during the failover.
Ethernet PortChannels and Fibre Channel PortChannels
Ethernet PortChannels offer Ethernet-level redundancy, Fibre Channel PortChannels offer (E)ISL-level redundancy. FCIP is unaware of any Ethernet PortChannels or Fibre Channel PortChannels. Fibre Channel PortChannels are unaware of any Ethernet PortChannels, and there is no mapping between the two.
Figure 24-18 PortChannels at the Fibre Channel and Ethernet Levels
Configuring iSCSI
This section contains the following topics:
•
Routing iSCSI Requests and Responses
•
Presenting Fibre Channel Targets as iSCSI Targets
•
Presenting iSCSI Hosts as Virtual Fibre Channel Hosts
•
Configuring iSCSI Proxy Initiators
•
iSCSI Authentication Setup Guidelines
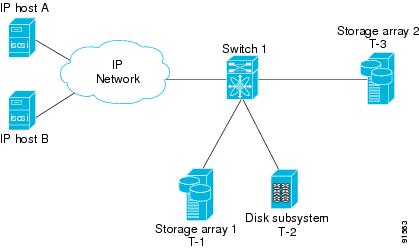
About iSCSI
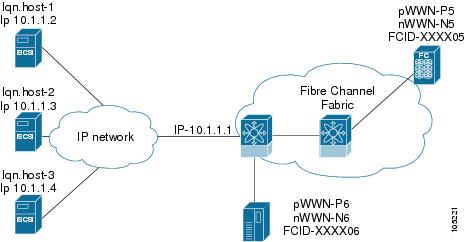
The IPS module provides transparent SCSI routing by default. IP hosts using iSCSI protocol can transparently access targets on the Fibre Channel network. provides an example of a typical configuration of iSCSI hosts with access to a Fibre Channel SAN.
Figure 24-19 Typical IP to Fibre Channel SAN Configuration
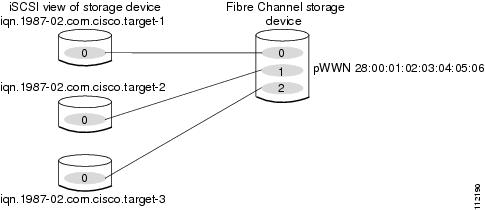
The IPS module enables you to create virtual iSCSI targets and maps them to physical Fibre Channel targets available in the Fibre Channel SAN. They present the Fibre Channel targets to IP hosts as if the physical targets were attached to the IP network.
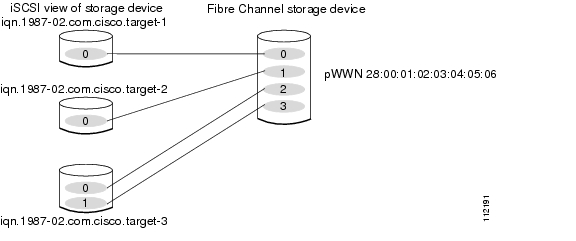
Figure 24-20 iSCSI View
In conjunction with presenting Fibre Channel targets to iSCSI hosts, the IPS module presents each iSCSI host as a Fibre Channel host (in transparent mode), i.e. Host Bus Adaptor (HBA) to the Fibre Channel storage device. The storage device responds to each IP host as if it were a Fibre Channel host connected to the Fibre Channel network.
Figure 24-21 Fibre Channel SAN View
Refer to the IETF standards for IP storage at http://www.ietf.org, for information on the iSCSI protocol.
Enabling iSCSI
To begin configuring the iSCSI feature, you must explicitly enable iSCSI on the required switches in the fabric. By default, this feature is disabled in all switches in the Cisco MDS 9000 Family.
The configuration and verification commands for the iSCSI feature are only available when iSCSI is enabled on a switch. When you disable this feature, all related configurations are automatically discarded.
To enable iSCSI on a switch using Fabric Manager, follow these steps:
Step 1
Choose End Devices > ISCSI from the Physical Attributes pane. The ISCSI tables display in the Information pane.
Step 2
Click the Control tab if it is not already displayed. This shows the iSCSI enable status for all switches in the fabric that contain IPS ports
Step 3
Choose Enable from the Command column for each switch that you want to enable iSCSI on.
Step 4
Click the Apply Changes icon to save these changes or click the Undo Changes icon to remove all changes without saving them.
Using the iSCSI Wizard
To use the iSCSI wizard in Fabric Manager, follow these steps:
Step 1
Click the iSCSI Setup Wizard icon.
Step 2
Choose an existing iSCSI initiator or add the iSCSI node name or IP address for a new iSCSI initiator.
Step 3
Choose the switch for this iSCSI initiator if you are adding a new iSCSI initiator and click Next.
Step 4
Choose the VSAN and targets to associate with this iSCSI initiator and click Next.
Step 5
Set the zone name for this new iSCSI zone and optionally check the Read Only check box.
Step 6
Click Finish to create this iSCSI initiator, or click Cancel to close the wizard without creating the iSCSI initiator.
Routing iSCSI Requests and Responses
The iSCSI feature consists of routing iSCSI requests and responses between hosts in an IP network and Fibre Channel storage devices in the Fibre Channel SAN that are accessible from any Fibre Channel interface of the Cisco MDS 9000 Family switch.
Each iSCSI host that requires access to storage via the IPS module needs to have a compatible iSCSI driver installed. (The CCO website at provides a list of compatible drivers). Using iSCSI protocol, the iSCSI driver allows an iSCSI host to transport SCSI requests and responses over an IP network. From the host operating system perspective, the iSCSI driver appears to be a SCSI transport driver similar to a Fibre Channel driver for a peripheral channel in the host. From the storage device perspective, each IP host appears as a Fibre Channel host.
Routing SCSI from the IP host to the Fibre Channel storage device consists of the following main actions.
•
Transporting iSCSI requests and responses over an IP network between hosts and the IPS module.
•
Routing SCSI requests and responses between hosts on an IP network and the Fibre Channel storage device (converting iSCSI to FCP and vice versa). This routing is performed by the IPS module.
•
Transporting FCP requests or responses between the IPS module and Fibre Channel storage devices.
FCP (the Fibre Channel equivalent of iSCSI) carries SCSI commands over a Fibre Channel SAN.
Presenting Fibre Channel Targets as iSCSI Targets
The IPS module presents physical Fibre Channel targets as iSCSI targets allowing them to be accessed by iSCSI hosts. It does this in one of two ways:
•
—Used if all logical units (LUs) in all Fibre Channel storage targets are made available to iSCSI hosts (subject to VSAN and zoning).
•
—Used if iSCSI hosts are restricted to subsets of LUs in the Fibre Channel targets and additional iSCSI access control is needed. Also, static import allows automatic failover if the Fibre Channel target LU is reached by redundant Fibre Channel ports.
The IPS module does not import Fibre Channel targets to iSCSI by default. Either dynamic or static mapping must be configured before the IPS module makes Fibre Channel targets available to iSCSI initiators. When both are configured, statically mapped Fibre Channel targets have a configured name. Targets that are not statically imported are advertised with the name created by the conventions explained in this section.
Dynamic Importing
To enable dynamic importing of Fibre Channel targets into iSCSI, use the iscsi import target fc command.
The IPS module maps each physical Fibre Channel target port as one iSCSI target. That is, all LU accessible via the physical storage target port are available as iSCSI LUs with the same LU number (LUN) as in the storage target.
For example, if an iSCSI target was created for Fibre Channel target port with pWWN 31:00:11:22:33:44:55:66 and that pWWN contains LUN 0 through 2, those LUNs would become available to an IP host as LUNs 0 through 2 as well.
If you have configured a switch name, then the switch name will be used instead of the management IP address. If you have not configured a switch name, the management IP address will be used.
The iSCSI target node name is created automatically using the iSCSI qualified name (IQN) format. The iSCSI qualified name is restricted to a maximum name length of 223 alphanumeric characters and a minimum length of 16 characters.
The IPS module creates an IQN formatted iSCSI node name using the following conventions:
•
IPS ports that are not part of a VRRP group use this format:
iqn.1987-05.com.cisco:05.<mgmt-ip-address>.<slot#>-<port#>-<sub-intf#>.<Target-pWWN>•
IPS ports that are part of a VRRP group use this format:
iqn.1987-05.com.cisco:05.vrrp-<vrrp-ID#>-<vrrp-IP-addr>.<Target-pWWN>•
Ports that are part of a PortChannel use this format:
iqn.1987-02.com.cisco:05.<mgmt-ip-address>.pc-<port-ch-sub-intf#>.<Target-pWWN>With this format, each IPS port in a Cisco MDS 9000 Family switch creates a different iSCSI target node name for the same Fibre Channel target.
Configuring Dynamic Importing with Device Manager
To dynamically import Fibre Channel targets as iSCSI targets, follow these steps:
Step 1
Choose IP > iSCSI from Device Manager. You see the iSCSI dialog box.
Step 2
Choose the Targets tab to display a list of existing iSCSI targets.
Step 3
Check the Dynamically Import FC Targets check box.
Step 4
Click Apply to save this change or click Cancel to close the dialog box without saving any changes.
Static Importing
You can manually (statically) create an iSCSI target and assign a node name to it. A statically-mapped iSCSI target can either contain the whole FC target port, or it can contain one or more LUs from a Fibre Channel target port.
To create a static iSCSI virtual target for the Fibre Channel target port, follow these steps
Step 1
Choose IP > iSCSI from Device Manager. You see the iSCSI dialog box.
Step 2
Choose the Targets tab to display a list of existing iSCSI targets.
Step 3
Click Create to create a new iSCSI target. You see the Create iSCSI Targets dialog box.
Step 4
Set the iSCSI target node name in the iSCSI Name field, in IQN format.
Step 5
Set the port WWN for the Fibre Channel target port you are mapping.
Step 6
Click the List radio button and set the iSCSI initiator node names or IP Addresses that you want this virtual iSCSI target to access, or click the All radio button to let the iSCSI target access all iSCSI initiators. See the "Access Control in iSCSI" section.
Step 7
Click the Selected from List radio button and check each interface you want to advertise the iSCSI targets on or choose the All radio button to advertise all interfaces.
Step 8
Click Apply to save this change or click Cancel to close the dialog box without saving any changes.
For multiple interfaces configured with iSNS, a different static virtual target name has to be created for each interface tagged to an iSNS profile and each static virtual target must be advertised only from one interface.
Advertising iSCSI Targets
You can limit the Gigabit Ethernet interfaces over which static iSCSI targets are advertised. By default iSCSI targets are advertised on all Gigabit Ethernet interfaces, subinterfaces, PortChannel interfaces, and PortChannel subinterfaces.
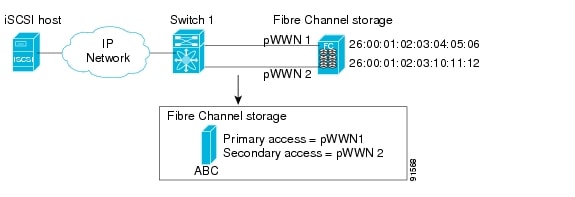
High Availability Static Target Importing
Statically imported iSCSI targets have an additional option to provide a secondary pWWN for the Fibre Channel target. This can be used when the physical Fibre Channel target is configured to have an LU visible across redundant ports. When the active port fails, the secondary port becomes active and the iSCSI session switches to use the new active port (see Figure 24-22).
Figure 24-22 Static Target Importing Through Two Fibre Channel Ports
In Figure 24-22, you can create a virtual iSCSI target that is mapped to both pWWN1 and pWWN2 to provide redundant access to the Fibre Channel targets.
The failover to secondary port is done transparently by the IPS port without impacting the iSCSI session from the host. All outstanding I/O are terminated with a check condition status when the primary port fails. New I/O received while the failover has not completed will receive a busy status.
Tip
If you use LUN mapping, you can define a different secondary Fibre Channel LUN if the LU number is different.
Refer to the Cisco MDS 9000 Family Configuration Guide for details on setting the secondary pWWN.
Enable the revert to primary port option to direct the IPS port to switch back to the primary port when the primary port is up again. If this option is disabled (default) and the primary port is up again after a switchover, the old sessions will remain with the secondary port and does not switch back to the primary port. However, any new session will use the primary port. This is the only situation when both the primary and secondary ports are used at the same time.
To enable the revert to primary port option, follow these steps:
Step 1
Choose End Devices > iSCSI from the Physical Attributes pane in Fabric Manager, or choose IP > iSCSI from Device Manager. You see the iSCSI tables in the Fabric Manager Information pane, or the Device Manager iSCSI dialog box.
Step 2
Click the Targets tab to display a list of existing iSCSI targets.
Step 3
Check the RevertToPrimaryPort check box to enable this option.
Step 4
Set the iSCSI target node name in the iSCSI Name field, in IQN format.
Step 5
Click the Apply Changes icon in Fabric Manager (or click Apply in Device Manager) to save this change, or click Cancel to close the dialog box without saving any changes.
Configuring the Trespass Feature
In addition to the high availability of statically imported iSCSI targets, the trespass feature is available (effective Release 1.3(x)) to enable the export of LUs, on an active port failure, from the active to the passive port of a statically imported iSCSI target.
In physical Fibre Channel targets, which are configured to have LUs visible over two Fibre Channel N-ports, when the active port fails, the passive port takes over. Some physical Fibre Channel targets require that the trespass command be issued, to export the LUs from the active port to the passive port. A statically imported iSCSI target's secondary pWWN option and an additional option of enabling the trespass feature is available for a physical Fibre Channel target with redundant ports. When the active port fails, the passive port becomes active, and if the trespass feature is enabled, the MDS issues a trespass command to the target to export the LUs on the new active port. The iSCSI session switches to use the new active port and the exported LUs are accessed over the new active port.
Figure 24-23 Virtual Target with an Active Primary Port
To configure the trespass feature, follow these steps:
Step 1
Choose End Devices > iSCSI from the Physical Attributes pane in Fabric Manager, or choose IP > iSCSI from Device Manager. You see the iSCSI tables in the Fabric Manager Information pane, or the Device Manager iSCSI dialog box.
Step 2
Click the Targets tab to display a list of existing iSCSI targets.
Step 3
Check the Trespass Mode check box to enable this option.
Step 4
Click the Apply Changes icon in Fabric Manager (or click Apply in Device Manager) to save this change, or click Cancel to close the dialog box without saving any changes.
iSCSI Virtual Target Configuration Examples
This section provides three examples of virtual target configurations.
Example 1
This example assigns the whole Fibre Channel target as a virtual iSCSI target. All LUNs that are part of the Fibre Channel target are available as part of the iSCSI target.
Figure 24-24 Assigning iSCSI Node Names
Example 2
This example maps a subset of LUNs of a Fibre Channel target to three iSCSI virtual targets. Each iSCSI target only has one LUN.
Figure 24-25 Mapping LUNs to iSCSI a Node Name
Example 3
This example maps three subsets of Fibre Channel LUN targets to three iSCSI virtual targets. Two iSCSI targets have one LUN and the third iSCSI target has two LUNs.
Figure 24-26 Mapping LUNs to Multiple iSCSI Node Names
Presenting iSCSI Hosts as Virtual Fibre Channel Hosts
The iSCSI hosts are mapped to virtual Fibre Channel hosts in one of two ways:
•
(default)—Used if no access control is done on the Fibre Channel target. An iSCSI host may use different pWWNs each time it connects to a Fibre Channel target.
•
—Used if an iSCSI host should always have the same pWWN or nWWN each time it connects to a Fibre Channel target.
Dynamic Mapping
When an iSCSI host connects to the IPS module using the iSCSI protocol, a virtual N port is created for the host. The nWWNs and pWWNs are dynamically allocated from the switch Fibre Channel WWN pool. The IPS module registers this N port in the Fibre Channel SAN. The IPS module continues using that nWWN and pWWN to represent this iSCSI host until it no longer has a connection to any iSCSI target via that IP storage port.
At that point, the virtual Fibre Channel host is taken offline from the Fibre Channel SAN and the nWWNs and pWWNs are released back to the switch's Fibre Channel WWN pool. These addresses becomes available for assignment to other iSCSI hosts requiring access to Fibre Channel SANs.
When a dynamically mapped iSCSI initiator has multiple sessions to multiple Fibre Channel targets, each session can use the same pWWN and nWWN as long as it uses the same node name in the iSCSI login message.
Identifying Initiators
An iSCSI initiator is identified in one of two ways:
•
By iSCSI node name—An initiator with multiple IP addresses (multiple interface cards--NICs or multiple network interfaces) has one virtual N port, assuming it uses the same iSCSI initiator name to iSCSI targets from all interfaces.
•
By IP address—A virtual N port is created for each IP address it uses to login to iSCSI targets.
By default, the switch uses the iSCSI node name to identify the initiator.
Static Mapping
With dynamic mapping, each time the iSCSI host connects to the IPS module a new Fibre Channel N port is created and the nWWNs and pWWNs allocated for this N port may be different. Use the static mapping method to obtain the same nWWN and pWWNs for the iSCSI host each time it connects to the IPS module.
You can implement static mapping in one of two ways: system assignment or manual assignment.
•
System assignment—When a static mapping configuration is created, one nWWN and/or one or more pWWNs are allocated from the switch's Fibre Channel WWN pool and the mapping is kept permanent.
•
Manual assignment—You can specify your own unique WWN by providing them during the configuration process.
Tip
We recommend using the system assignment option. If you manually assign a WWN, you must ensure its uniqueness.
Static mapping can be used on the IPS module to access intelligent Fibre Channel storage arrays that have access control and LUN mapping/masking configuration based on the initiator's pWWNs and/or nWWNs.
If an iSCSI host connects to multiple IPS ports, each port independently creates one virtual N port for the host. If static mapping is used, enough pWWNs should be configured for as many IPS ports to which a host connects.
If a system assignment option is used to configure WWNs for an iSCSI initiator, when the configuration is backed up to an ASCII file the system-assigned WWNs are also saved. Subsequently if you issue a CLI write erase command, you must manually delete the WWN configuration from the ASCII file.
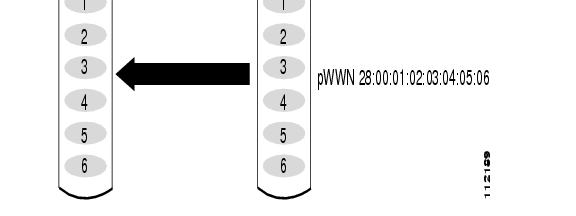
Making the Dynamic Initiator WWN Mapping Static
After a dynamic initiator has already logged in, you may decide to permanently keep the automatically-assigned nWWN/pWWN mapping, so this initiator uses the same mapping the next time it logs in.
Assigning VSAN Membership to iSCSI Hosts
By default, a host is only in VSAN 1 (default VSAN). You can configure an iSCSI host to be a member of one or more VSANs. The IPS module creates one Fibre Channel virtual N port in each VSAN to which the host belongs.
When an initiator is configured in any other VSAN (other than VSAN 1), for example VSAN 2, the initiator is automatically removed from VSAN 1. If you also want it to be present in VSAN 1, you must explicitly configure the initiator in VSAN 1.
Assigning VSANs to a iSCSI Interface
All dynamic iSCSI initiators are members of VSAN 1. The port VSAN of an iSCSI interface is the default VSAN for all dynamic iSCSI initiators. The default port VSAN of an iSCSI interface is VSAN 1, but can be changed. All dynamic iSCSI initiators are member of the port VSAN of the iSCSI interface.
Tip
This is a 1.3(x) feature. If you downgrade to an earlier release, be sure to delete any assigned VSAN before performing the downgrade procedure.
To modify the VSANs assigned to an iSCSI interface using Device Manager, follow these steps:
Step 1
Choose Interfaces > Ethernet or iSCSI. You see the interfaces dialog box.
Step 2
Click the iSCSI tab. You see the iSCSI interface configuration table.
Step 3
Double-click on the PortVSAN column to modify the default port VSAN.
Step 4
Click Apply to save these changes, or click Cancel to discard changes.
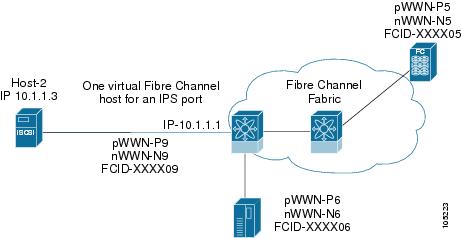
Configuring iSCSI Proxy Initiators
When an interface is in the proxy initiator mode, you can only configure Fibre Channel access control (zoning) based on the Fibre Channel interface attributes--the WWN pair and available FCIDs. You cannot configure zoning using iSCSI attributes such as the IP address or the iQN name of the iSCSI initiator. To enforce initiator-based access control, use iSCSI based access control.
By default, each iSCSI initiator appears as one Fibre Channel initiator in transparent mode in the Fibre Channel fabric. For some storage arrays, this appearance requires the initiator's pWWN to be manually configured for access control purposes. This process can be quite cumbersome. The Proxy initiator feature allows all iSCSI initiators to connect through one IPS port making it appear as one Fibre Channel port per VSAN. It simplifies the task of configuring the pWWN for each new initiator on the storage array, and Fibre Channel access control such as zoning. This feature along with static target importing (using LUN mapping) results in the configuration being performed only on the switch when a new iSCSI host is added. On the storage array, all LUNs that will be used by iSCSI initiators are configured to allow access by the proxy initiator's pWWN. From the iSCSI perspective, this configuration is no different from the default mode.
Figure 24-27 The iSCSI View of a Proxy Initiator
From the Fibre Channel perspective, only one Fibre Channel initiator is visible per VSAN.
Figure 24-28 The FC View with a Proxy Initiator
Configuring the iSCSI Proxy Initiator
To configure the proxy initiator, follow these steps:
Step 1
Choose Interfaces > FC Logical from the Fabric Manager Physical Attributes pane, or choose Interfaces > Ethernet or iSCSI from Device Manager. You see the Interface tables in the Fabric Manager Information pane or the Device Manager Interfaces dialog box.
Step 2
Click the iSCSI tab. You see the iSCSI interface configuration table.
Step 3
In the Initiator Proxy Mode section, check the Enable check box.
Step 4
Click the Apply Changes icon in Fabric Manager or click Apply in Device Manager to save these changes, or click Undo Changes in Fabric Manager or click Cancel in Device Manager to discard changes.
Access Control in iSCSI
You can control access to each statically-mapped iSCSI target by specifying a list of IPS ports on which it will be advertised and specifying a list of iSCSI initiator node names allowed to access it. Fibre Channel zoning-based access control and iSCSI-based access control are the two mechanisms by which access control can be provided for iSCSI. Both methods can be used simultaneously.
This access control is in addition to the existing Fibre Channel access control. The iSCSI initiator has to be in the same VSAN and zone as the physical Fibre Channel target.
Fibre Channel Zoning-Based Access Control
Zoning is an access control mechanism within a VSAN. The switch zoning implementation extends the VSAN and zoning concepts from the Fibre Channel domain to also cover the iSCSI domain. This extension includes both iSCSI and Fibre Channel features and provides a uniform, flexible access control across a SAN. Static and dynamic are the two Fibre Channel zoning access control mechanisms.
•
Static—Statically map the iSCSI host to Fibre Channel virtual N port(s). This creates a permanent nWWNs and pWWNs. Next, configure the assigned pWWN into zones, similar to adding a regular Fibre Channel host pWWN to a zone.
•
Dynamic—Add the iSCSI host's initiator node name as a member of a zone. When the IP host's Fibre Channel virtual N port is created and the Fibre Channel address (nWWNs and pWWNs) is assigned, Fibre Channel zoning is enforced.
To register an iSCSI host initiator as a member of a zone using Fabric Manager, follow these steps:
Step 1
Choose Zone > Edit Local Full Zone Database.
Step 2
Choose the VSAN and zone to which you want to add the iSCSI host initiator.
Step 3
From the list of available devices including iSCSI host initiators, click on the initiators that you want to add to the zone and click Add to Zone or Alias.
Step 4
Click Close to close the dialog box.
iSCSI-Based Access Control
For static iSCSI targets, you can manually configure a list of iSCSI initiators that are allowed to access it. The iSCSI initiator is identified by the iSCSI node name or the IP address of the iSCSI host.
By default, static virtual iSCSI targets are not accessible to any iSCSI host. You must explicitly configure accessibility to allow a virtual iSCSI target to be accessed by all hosts. The initiator access list can contain one or more initiators. Each initiator is identified by one of the following:
•
iSCSI node names
•
IP addresses
•
IP subnets
Enforcing Access Control
IPS modules use both iSCSI node name-based and Fibre Channel zoning-based access control lists to enforce access control during iSCSI discovery and iSCSI session creation.
•
iSCSI discovery--When an iSCSI host creates an iSCSI discovery session and queries for all iSCSI targets, the IPS module returns only the list of iSCSI targets this iSCSI host is allowed to access based on the access control policies discussed in the previous section.
•
iSCSI session creation--When an IP host initiates an iSCSI session, the IPS module verifies if the specified iSCSI target (in the session login request) is a static mapped target, and if true, verifies if the IP host's iSCSI node name is allowed to access the target. If the IP host does not have access, its login is rejected.
The IPS module, then creates a Fibre Channel virtual N port (the N port may already exist) for this IP host and does a Fibre Channel name server query for the FCID of the Fibre Channel target pWWN that is being accessed by the IP host. It uses the IP host virtual N port's pWWN as the requester of the name server query. Thus, the name server does a zone-enforced query for the pWWN and responds to the query.
If the FCID is returned by the name server, then the iSCSI session is accepted. Otherwise, the login request is rejected.
iSCSI User Authentication
The IPS module supports the iSCSI authentication mechanism to authenticate iSCSI hosts that request access to storage. When iSCSI authentication is enabled, the iSCSI hosts must provide user name and password information each time an iSCSI session is established.
Only the Challenge Handshake Authentication Protocol (CHAP) authentication method is supported.If no authentication is configured, local authentication is used. You can use RADIUS authentication or TACACS+ authentication.
Configuring an Authentication Mechanism
During an iSCSI login, both the iSCSI initiator and target have the option to authenticate each other. By default, the IPS module allows either CHAP authentication or no authentication from iSCSI hosts.
Note
The authentication for a Gigabit Ethernet interface or subinterface configuration overrides the authentication for the global interface configuration.
To configure an authentication method for iSCSI, follow these steps:
Step 1
Choose End Devices > iSCSI from the Fabric Manager Physical Attributes pane, or choose IP > iSCSI from Device Manager. You see the iSCSI tables in the Fabric Manager Information pane, or the Device Manager iSCSI dialog box.
Step 2
Click the Global tab. You see the iSCSI authentication configuration table.
Step 3
From Fabric Manager, choose chap or none from the authMethod column.
From Device manager, check the Chap check box to configure DH-CHAP authentication, or check the none check box for no authentication.
Step 4
Click the Apply Changes icon in Fabric Manager (or click Apply in Device Manager) to save these changes, or click Undo Changes in Fabric Manager (or click Cancel in Device Manager) to discard changes.
Configuring an iSCSI RADIUS Server
To configure an iSCSI RADIUS server, follow these steps:
Step 1
Configure the RADIUS server to allow access from the Cisco MDS switch's management Ethernet IP address.
Step 2
Configure the shared secret for the RADIUS server to authenticate the Cisco MDS switch.
Step 3
Configure the iSCSI users and passwords on the RADIUS server.
Advanced iSCSI Configuration
Advanced configuration options are available for iSCSI interfaces on a per-IPS port basis. These configurations are similar to the advanced FCIP configurations and are already explained in that section.
Cisco MDS switches support the following advanced features for iSCSI interfaces:
•
iSCSI listener port—Configure the TCP port number for the iSCSI interface which listens for new TCP connections. The default port number is 3260. Following that, the iSCSI port only accepts TCP connections on the newly configured port
•
TCP tuning parameters—The following TCP parameters can be configured.
–
SACK is enabled by default for iSCSI TCP configurations.
–
QoS configurations differ for iSCSI and FCIP interfaces.
•
Identification of dynamic iSCSI initiator—iSCSI initiators are identified based on their IQN name or their IP address. In the absence of any configuration for the initiator (WWN or VSAN membership), the identifier key is the default connection. By default, the key is the IQN name but can be changed to IP address by toggling this mode.
•
Proxy or transparent Initiator—For each iSCSI initiator with iSCSI target sessions, the switch creates a virtual FC initiator with a distinct pair of WWNs per VSAN. Targets that have access control per LUN, the WWN pair of each FC initiator must be configured in the target. The proxy initiator mode can be enabled to facilitate this configuration, in which case, all iSCSI initiators which connect to this iSCSI interface inherit the same WWN pair and create only one virtual FC initiator in each VSAN.
Setting the QOS Values
To set the QoS values, follow these steps:
Step 1
Choose Interfaces > FC Logical from the Fabric Manager Physical Attributes pane, or choose Interfaces > Ethernet or iSCSI from Device Manager. You see the Interface tables in the Fabric Manager Information pane, or the Device Manager Interfaces dialog box.
Step 2
Click the iSCSI TCP tab. You see the iSCSI TCP configuration table.
Step 3
Set the QoS field from 1 to 6.
Step 4
Click the Apply Changes icon in Fabric Manager (or click Apply in Device Manager) to save these changes, or click Undo Changes in Fabric Manager (or click Cancel in Device Manager) to discard changes.
iSCSI Forwarding Mode
The iSCSI gateway on the IPS module has two modes of forwarding operation
•
The pass-thru mode (default)—In this mode, the IPS port converts an iSCSI PDU into an FCP frame or vice versa and then forwards it one frame or PDU at a time. The absence of buffering PDUs or frames keeps the operation latency low. To operate in this mode, the IPS port has to negotiate with its peers a suitable maximum size of the data payload in each frame/PDU. This is done during iSCSI login and FC PLOGI and the value is restricted by the TCP connection's Maximum Segment Size (MSS) and the maximum Fibre Channel data payload size specified by the FC target. This usually results in a smaller maximum payload size than most hosts expect, thus comes the second mode of forwarding.
•
The store-and-forward mode—This mode allows the iSCSI client to send and receive an iSCSI data payload at the size it desires. This sometimes results in better performance for the client. The IPS port stores each TCP segment it receives until one full iSCSI PDU is received before converting and forwarding it as Fibre Channel frames to the FC target. In the opposite direction, the IPS port assembles all FC data frames of an exchange to build one iSCSI data-in PDU before forwarding it to the iSCSI client. The limitation on this mode is iSCSI CRC data digest cannot be used.
iSCSI High Availability
The following high availability features are available for iSCSI configurations:
•
Multiple IPS Ports Connected to the Same IP Network
•
VRRP-Based High Availability
•
Ethernet PortChannel-Based High Availability
Multiple IPS Ports Connected to the Same IP Network
Figure 24-29 provides an example of a configuration with multiple Gigabit Ethernet interfaces in the same IP network.
Figure 24-29 Multiple Gigabit Ethernet Interfaces in the Same IP Network
In Figure 24-29, each iSCSI host discovers two iSCSI targets for every physical Fibre Channel target (with different names). The multi-pathing software on the host provides load-balancing over both paths. If one Gigabit Ethernet interface fails, the host multi-pathing software is not affected because it can use the second path.
VRRP-Based High Availability
Figure 24-30 provides an example of a VRRP-based high availability iSCSI configuration.
Figure 24-30 VRRP-Based iSCSI High Availability
In Figure 24-30, each iSCSI host discovers one iSCSI target for every physical Fibre Channel target. When the Gigabit Ethernet interface of the VRRP master fails, the iSCSI session is terminated. The host then reconnects to the target and the session comes up because the second Gigabit Ethernet interface has taken over the virtual IP address as the new master.
Tip
Ports that act as VRRP master and backup can be on different switches. If you have a static WWN configuration for iSCSI initiators, configure a different WWN for the iSCSI initiator for each switch. If you use a proxy-initiator, be sure to configure a different pWWN on each iSCSI interface for each VRRP port used.
Ethernet PortChannel-Based High Availability
All iSCSI data traffic for one iSCSI link is carried on one TCP connection. Consequently, the aggregated bandwidth will be one Gbps for that iSCSI link.
Figure 24-31 provides a sample Ethernet PortChannel-based high availability iSCSI configuration.
Figure 24-31 Ethernet PortChannel-Based iSCSI High Availability
In Figure 24-31, each iSCSI host discovers one iSCSI target for every physical Fibre Channel target. The iSCSI session from the iSCSI host to the virtual iSCSI target (on the IPS port) uses one of the two physical interfaces (because an iSCSI session uses one TCP connection). When the Gigabit Ethernet interface fails, the IPS module and the Ethernet switch transparently forwards all the frames on to the second Gigabit Ethernet interface.
iSCSI Authentication Setup Guidelines
This section provides guidelines on iSCSI authentication possibilities, setup requirements, and sample scenarios.
This section does not specify the steps to enter or exit EXEC mode, configuration mode, or any submode. Be sure to verify the prompt before issuing any command.
Configuring Storage Name Services
Effective Release 1.3(1), the Internet Storage Name Service (iSNS) client feature is available in all switches in the Cisco MDS 9000 Family with IPS modules installed.
iSNS services allow your existing TCP/IP networks to function more effectively as storage area networks by automating the discover and management of iSCSI devices. To facilitate these functions, the iSNS client functionality registers iSCSI portals and all targets accessible through a particular interface with an external iSNS server.
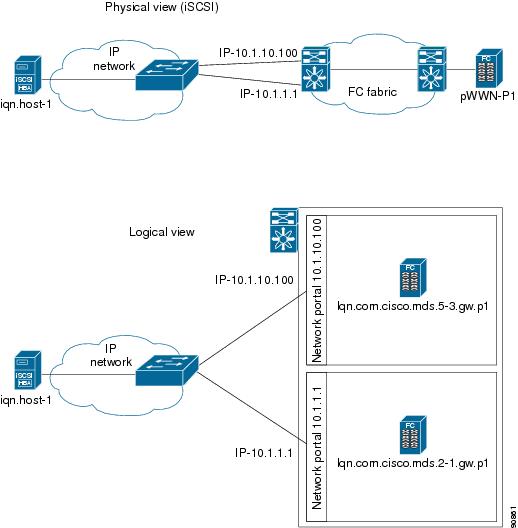
Creating iSNS Profiles and Tagging Profiles
The iSNS client functionality on each interface (Gigabit Ethernet interface or subinterface or PortChannel) registers information with its configured iSNS server using an iSNS profile. This process is referred to as tagging an iSNS profile to an interface. Each iSNS profile keeps information about an iSNS server IP address. One profile can be tagged to one or more interfaces.
Once a profile is tagged to an interface, the MDS switch opens a TCP connection to the iSNS server IP address (using a well-known iSNS port number 3205) in the profile and registers network entity and portal objects. It goes through the FC name server database and configuration to find storage nodes to register with the server.
Statically-mapped virtual target is registered if the associated Fibre channel pWWN is present in the FC name server database and no access control configuration prevents it. A dynamically-mapped target is registered if the dynamic target importing is enabled.
A storage node is deregistered from the iSNS server when it becomes unavailable either because of configuration change (such as access control change or dynamic import disabling) or when the Fibre Channel storage port goes off-line. It will be registered again when the node is online.
When the iSNS client is unable to register/deregister objects with the iSNS server (e.g. as in unable to make a tcp connection to the iSNS server) it retries every minute to re-registers all iSNS objects for the affected interface(s) with the iSNS server.
Untagging a profile causes the network entity and portal to deregister from that interface.
Creating an iSNS Profile
To create an iSNS profile, follow these steps:
Step 1
Choose End Devices > iSCSI from the Fabric Manager Physical Attributes pane, or choose IP > iSCSI from Device Manager. You see the iSCSI tables in the Fabric Manager Information pane, or the Device Manager iSCSI dialog box.
Step 2
Click the iSNS Profiles tab. You see the iSCSI authentication configuration table.
Step 3
Set the Name and IP address of the iSNS server.
Step 4
Click the Fabric Manager Apply Changes icon (or click Create in Device Manager) to save these changes, or click Undo Changes in Fabric Manager (or click Cancel in Device Manager) to discard changes.
Modifying an iSNS Profile
To modify (tag) the iSNS profile for an interface, untag the interface from currently tagged iSNS profile and then tag to a new iSNS profile.
To tag an interface to a profile using Device Manager, follow these steps:
Step 1
Choose Interfaces > Ethernet or iSCSI. You see the Interfaces dialog box.
Step 2
Click the General tab. You see the General interface configuration table.
Step 3
Choose the iSNS ProfileName.
Step 4
Click Apply to save these changes, or click Cancel to discard changes.
Default IP Storage Settings
Table 24-1 lists the default settings for Gigabit Ethernet parameters.
Table 24-1 Default Gigabit Ethernet Parameters
IP MTU frame size
1500 bytes for all Ethernet ports
Table 24-2 lists the default settings for FCIP parameters.
Table 24-3 lists the default settings for iSCSI parameters.
Using the IP Filter Wizard
Use the IP Filter Wizard to manage IP filters.
Step 1
From the Fabric Manager, click the IP Filter icon on the Fabric Manager toolbar.
Figure 24-32 IP Filter Wizard
The IP Filter Wizard is displayed.
Step 2
Follow the prompts in the wizard to manage IP filters.
Creating IP Profiles
To create an IP profile, perform the following steps.
Step 1
From the Fabric Manager, choose Security > IP Filter from the menu tree. You see IP filter information on the Fabric Manager Information pane.
Step 2
Click the Profiles tab to see a list of profiles.
Step 3
Click the Create Row icon. You see the Create Profile dialog box.
Step 4
Choose the switches you want to include in the profile by checking the check box next to the switch's address.
Step 5
Enter a profile name in the Name field.
Step 6
Click Create to create the profile, or click Close to close the Create Profile dialog box without creating a profile.
You see the newly created profile in the list of profiles.
Step 7
To create additional profiles, repeat Steps 4 through 6. Otherwise, click Close to close the Create Profile dialog box.
Adding IP Filters to Profiles
To add an IP filter to a profile, perform the following steps.
Step 1
Choose Security > IP Filter from the Fabric Manager menu tree. You see IP Filter information on the Information pane.
Step 2
Click the Profiles tab to see a list of switches and associated profiles.
Step 3
Click on the IP address of the switch to which you want to add a filter. The Rules button becomes available.
Step 4
Click Rules. You see the IP Filter Edit dialog box.
Step 5
Click Create Row. You see the Create IP Filter dialog box.
Step 6
Complete the fields in the Create IP Filter dialog box.
Step 7
Click Create to create the filter, or click Close to close the Create IP Filter dialog box without creating a filter.
You see the newly created filter in the list of filters.
Step 8
Repeat Steps 6 and 7 to create additional filters, or click Close to close the Create IP Filter dialog box.
Step 9
Click Apply Changes to add the newly created filters to the profile.
Associating IP Profiles to Interfaces
To associate the profile to an interface, perform the following steps.
Step 1
Choose Security > IP Filter from the Fabric Manager menu tree. You see the IP Filter information in the Information pane.
Step 2
Click the Interfaces tab to see a list of interfaces and associated profiles.
Step 3
Click the Create Row icon. You see the Create Interface dialog box.
Step 4
Select the switches you want to include in the profile, by checking the check boxes next to the switch's address.
Step 5
Enter an interface name in the Name field.
Step 6
Choose the profile direction (either inbound or outbound).
Step 7
Enter the profile name in the Profile Name field. (This profile name must already have been created using the Create Profiles dialog. If not, no filters will be enabled until you to go to the Create Profiles dialog and create the profile.)
Step 8
Click Create to associate the profile, or click Close to close the Create Interfaces dialog box without associating a profile.
You see the newly associated profile in the list of profiles.
Step 9
Repeat Steps 4 through 8 to create additional associations, or click Close to close the Create Interfaces dialog box.
Deleting IP Profiles
To delete an IP profile, perform the following steps.
Step 1
Choose Security > IP Filter from the Fabric Manager menu tree. You see IP Filter information in the Information pane.
Step 2
Click the Profiles tab to see a list of switches, profile names and profile types.
Step 3
Click the row you want to delete. If you want to delete multiple rows, hold down the Shift key while clicking rows.
Step 4
Click the Delete Row icon to delete the profile.
Deleting IP Filters
To delete an IP filter, perform the following steps.
Step 1
Choose Security > IP Filter from the Fabric Manager menu tree. You see IP Filter information in the Information pane.
Step 2
Click the Interfaces tab to see a list of switches, filters and profile names.
Step 3
Click the row you want to delete. If you want to delete multiple rows, hold down the Shift key while clicking rows.
Step 4
Click the Delete Row icon to delete the filter from the profile

 Feedback
Feedback