- Preface
- Chapter 1 - Introduction
- Chapter 2 - System Overview
- Chapter 3 - Initial Installation of Connected Lighting
- Chapter 4 - Lighting Migration to Campus Network Architecture
- Chapter 5 - Lighting Deployment without Campus Network Core
- Chapter 6 - Lighting Small Scale Deployment
- Chapter 7 - Lighting Control and Maintenance
- Chapter 8 - Caveats
- Appendix A - References
- Appendix B - Glossary
Lighting Deployment without Campus Network Core
This chapter, which covers the implementation details for migrating the lighting network to a Production Network without a Campus Network core architecture as described in Section 3.1, System Topologies of the Cisco Digital Building Cree Design Guide, includes the following major topics:
Network Topology
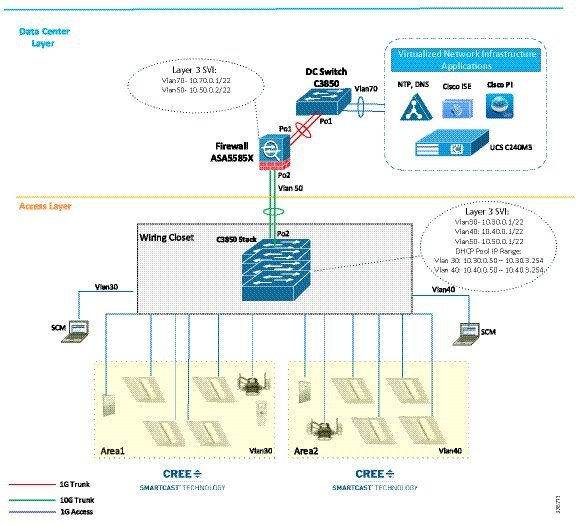
In this deployment, access switches are directly connected to data center via firewall as shown in Figure 5-1.
Figure 5-1 Cisco Digital Building Cree Solution Topology without Campus Network Core
Wiring Closet Access Switch (Cisco Catalyst 3850 Stack)
When migrating from initial lighting setup to a Production Network without network core, wiring closet switches (for example, Cisco Catalyst 3850 stack) are connected directly to the data center edge via the firewall in order to leverage data center application services for lighting network as discussed in Section 3.1, System Topologies of the Cisco Digital Building Cree Design Guide.
This section covers configuration required on Cisco Catalyst 3850 stack and ASA while connecting the switch stack to the firewall. The implementation of all other applications and devices is similar, as discussed in Chapter4, “Lighting Migration to Campus Network Architecture”
Configuring DHCP Server for Light Fixture IP Addressing
During migration, the DHCP server IP addressing pool for light fixtures/wall dimmers is configured on the Cisco Catalyst 3850 switch stack to assign IP addresses to Cree endpoints, as shown in Figure 5-1.
Do the following to configure DHCP server pool on Cisco Catalyst 3850 stack for lighting network:
Configure DHCP server pool for lighting fixtures’ IP addressing. For example:
Configuring Management VLAN Interface
Configure the management VLAN 50 interface for the management traffic to go through the ASA firewall to the data center:
Configuring Network Uplink to Firewall
In this deployment, follow the steps below to configure networking port channel on 3850 stack to connect the Cisco Catalyst 3850 switch stack to the ASA firewall, as shown in Figure 5-1.
Step 1 Configure the Port Channel interface to ASA:
Step 2 Configure the Port Channel as a trunk port:
Follow the configuration steps described in Wiring Closet Access Switch (Cisco Catalyst 3850 Stack), to complete the Cisco Catalyst 3850 stack switch configuration for this deployment model.
Provisioning Light Fixtures using SmartCast Manager
This section describes how to commission the light fixtures using the SCM. The light fixture can be commissioned by running the OneButton Setup, which groups the endpoints automatically.
The light fixtures can then be controlled via the SCM and the Wall Dimmer. Following are the steps to be performed to provision the light fixtures:
Step 1 Connect the SCM to an access port on the switch, in the same VLAN as the lighting network.
Step 2 Launch the SCM application.
Step 3 In the Network Interface selection, if prompted to select the network interface, choose the PoE network.
Step 5 If light fixtures are commissioned already from the initial installation, do a factory reset on them, and then allow them to be rediscovered for commissioning on a new area as per the requirement.
Step 6 Once the devices are listed on the SCM, perform OneButton Setup.
Step 8 Once OneButton Setup is complete, click All Devices under the Settings tab to verify that all devices in the lighting network are assigned to Occupancy Groups and Switch Groups.
Step 9 Click Controls and change the dim level to verify that the Switch Group brightness changes when controlling it via the control screen. This verifies light fixture is provisioned and controllable by SCM.
Implementing Data Center Applications
Configuring Firewall
In this deployment, follow the steps below to configure firewall networking to connect the Cisco Catalyst 3850 switch stack as shown in Figure 5-1. The configuration of the firewall is same as described in Configuring Firewall in this deployment.
Configuring Data Center Applications
Refer to Configuring Data Center Applications, for the configure data center application as shown Figure 5-1.
 Feedback
Feedback